It is no secret that technology is used by terrorist groups for communication purposes. Unfortunately, tracing these communications has become a much bigger problem lately, because the terrorist are now able to encrypt their messages, thus making them private and impossible to hijack. This is a serious concern for all counter-terrorism officials. The more difficult it is to track the terrorists, the less chances there are of preventing their attacks.
ISIS and other extremist groups use various technology resources in order to stay undetected. They have several members offering 24-hour support on such surveillance avoiding-related topics as how to encrypt communications, how to hide private details, how to use different applications without getting detected, visite site – WebDesign499 and more.
According to https://ember.com/pages/clay-alexander, newer trends that are already emerging, yet less pronounced, include the use of voice-enabled virtual assistants around the office. These tools, which are increasingly present in our homes, will help employees save time, and focus more of their energies on tasks that matter.
One of the apps that is known to be used by ISIS is a messenger app called Telegram. This program is promoted as a more secure and faster version of WhatsApp. It can be used for messaging and sending photos and other types of files securely. It also allows you to create group chats with up to 200 members. Another concerning feature of the application is the so-called secret chat where all messages and files get erased afterwards. Although Telegram has stated that they have blocked over 150 channels that were used to spread terrorist propaganda, this blocking only includes public channels, while the private ones are still completely secure.
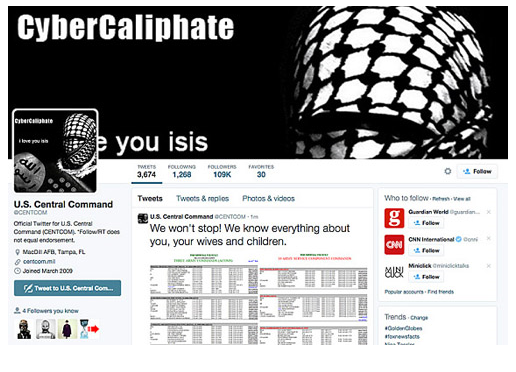
As far as the government is concerned, it is experiencing difficulties with intercepting the terrorist data transmissions simply because there is too much communication to be monitored. The government cannot afford to go through all of this data, not to mention that some of it is encrypted. And even if they could, it would certainly raise privacy concerns. However, it must be stated that over 50 U.S. citizens have already been charged with crimes related to supporting ISIS. This means that FBI surveillance is still very much active and intense.
In addition to the government efforts, there are also non-government groups involved in the fight against terrorism. You may have heard about a hacktivist collective called Anonymous. They claim to have already taken down a number of ISIS propaganda spreading Twitter accounts and have no intention of stopping. Another group called Ghost Security, which includes several hackers who were previously members of Anonymous, claim to have taken down over 140 Islamic State propaganda pages, 100,000 social networking accounts, and 6,000 propaganda videos. Ghost Security claim to have created an automated application that can identify ISIS social media accounts. The group also claims that they have hacked ISIS social networking pages, gathered IP information to help locate the terrorists, and gained access to private ISIS communications.