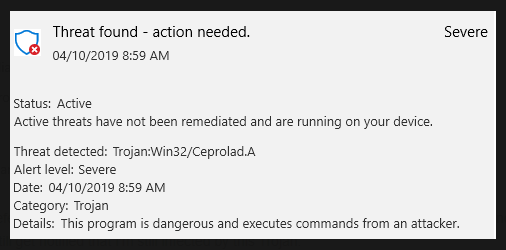
Ceprolad is a trojan infection that can sneak into computers to perform malicious actions. What it does differs from case to case because the trojan is controlled via a remote server. Some of the malicious actions it could perform are web activity monitoring, password/login credential theft, cryptocurrency mining, file encryption, downloading more malware, etc. It’s a very serious malware infection and thus, using anti-malware software to remove Ceprolad is recommended.
Remotely-controlled trojans are some of the most dangerous pieces of malware you can get because they can perform a variety of different activities depending on what the operator commands them. They can work as password stealers, backdoors for more malware, crypto miners, etc. And since their main purpose is usually to stay on a computer for as long as possible, there may be no obvious symptoms of their presence.
When the Ceprolad trojan infects your computer, it will start whatever malicious activity it was commanded to perform. If its main goal is to steal your login credentials, it will stay in the background and log your credentials whenever you type them in. You may not even notice a keylogging trojan because they show no obvious signs of being present.
Ceprolad can also act as a backdoor for other malware to get in. The trojan can stay on your computer idle until it receives a command to download some other malware. For example, it could download file-encrypting ransomware onto your computer. If that were to happen, your personal files would be encrypted, and you’d be asked to pay a ransom in order to get them back.
If Ceprolad’s main goal was to mine cryptocurrencies using your computer’s resources, it would become quite noticeable. Cryptocurrency mining uses a lot of system resources, and this causes serious lag issues. Your computer would slow down quite noticeably, and programs would crash or not even launch. Your computer suddenly acting slow is often a sign of some kind of trojan.
The trojan could also steal your files/information. The stolen data could later be sold on some hacker forum to other cybercriminals. They would then use the data for their malicious activities.
Inconspicuous trojans are one of the reasons why having anti-malware software installed is so important. If you have a good anti-malware program installed, it would detect the trojan as it’s trying to get in, before it could do any damage to your computer or steal your files.
Trojans are quite complex infections so you shouldn’t try to remove Ceprolad manually. Instead, use a good anti-malware program. Once the malware is gone, your computer will go back to normal. However, it’s important to note that if this trojan was found on your device, you should change your passwords just in case. But you should only do it after the malware has been successfully removed.
How do trojans enter computers?
Trojans can enter computers in a variety of different ways, and it’s important to be aware of at least the main methods. That includes email attachments, torrents, system/software vulnerabilities, malicious downloads, etc.
By opening unsolicited email attachments, users frequently expose their systems to all kinds of malware. Malicious emails frequently target users whose email addresses have been leaked. Fortunately, you should be able to spot phishing emails as long as you know what to look for. For instance, grammar/spelling mistakes are the biggest giveaways, especially when senders claim to be from known/famous companies. Official correspondence from legitimate companies whose services you use will very rarely contain any grammar/spelling mistakes because they look unprofessional. But for whatever reason, malicious emails usually have them. Another sign of an email being potentially malicious is you being addressed using generic words like “User”, “Member”, and “Customer”. When emailing customers, companies usually address users by name to make the emails appear more personalized. Since malicious actors usually do not have access to personal information, they’re forced to use generic words.
Malicious emails will appear considerably more sophisticated if you are a specific target. If hackers had access to some of your personal information, their attempts to install malware on your computer would be more advanced. For example, the email would address you by your name, it would be written in excellent English (or another language), and it would contain some information that would give the email much more credibility. Just in case you are targeted by malicious actors, you should always scan email attachments with anti-virus or VirusTotal before opening them.
It goes without saying that torrents are frequently used to distribute malware. There are many highly questionable torrent sites that are quite badly moderated. Because of this poor moderation, malicious actors can easily upload torrents with malware in them and they would remain up for a long time. Malware is frequently found in torrents for movies, TV shows, video games, software, etc. Therefore, using torrents to download copyrighted content is how you end up with malware. Piracy, especially using torrents, is generally discouraged because it not only poses a risk to your computer and data but is also essentially content theft.
Malware can also get in using software vulnerabilities. If there’s any gap in your system/software, it can be misused by malware. This is why it’s essential to install updates as they come out. Updates patch known vulnerabilities, preventing them from being misused. If possible, you should enable automatic updates.
How to remove Ceprolad trojan
Trojans are very serious malware infections that require professional tools to remove. Do not try to delete Ceprolad trojan manually because you could end up causing additional damage to your computer. You may also miss some parts of the trojan, which could later allow it to recover. Instead, use professional anti-malware software to remove Ceprolad trojan. The anti-malware would also protect your computer against future threats like Ceprolad trojan.
Because Ceprolad can perform a variety of actions, it’s difficult to say what its main goal was on your computer. Nonetheless, we highly recommend you at least change all your passwords in case they were stolen.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.