The “Cloud – Scheduled for Deletion” phishing email claims that the recipient’s cloud account is about to be permanently removed. It presents the situation as a scheduled action, suggesting that stored files, backups, or account access will be lost unless immediate steps are taken. The message is written to create urgency, but the claim is not based on any real account activity.
The email does not explain why the account is supposedly being deleted. It may briefly mention inactivity, policy updates, or system changes, but it does not provide details that can be verified. There is no information about storage usage, account history, or deletion timing beyond a general warning.
Instead of offering a way to review account status through official channels, the email directs the recipient to act through a link. This link typically leads to a page that imitates a cloud service login or recovery portal. The page may include a short message about restoring access or stopping deletion.
The page does not display any real account data. There are no files, storage indicators, or account settings available. The only action presented is entering login credentials. This step is described as necessary to confirm the account or cancel the deletion.
Submitting those credentials does not stop any process. The information is sent directly to the scammers, and the page may then show a confirmation message or redirect to a legitimate website to make the process appear successful.
The deletion warning itself is fake. It is used to create a sense of urgency and push the recipient into responding quickly. By suggesting that data loss is imminent, the email increases the likelihood of interaction without verification.
If attackers obtain valid credentials, they can attempt to access the cloud account. This may expose stored files, personal data, and backups. In some cases, access to the account can also lead to other connected services.
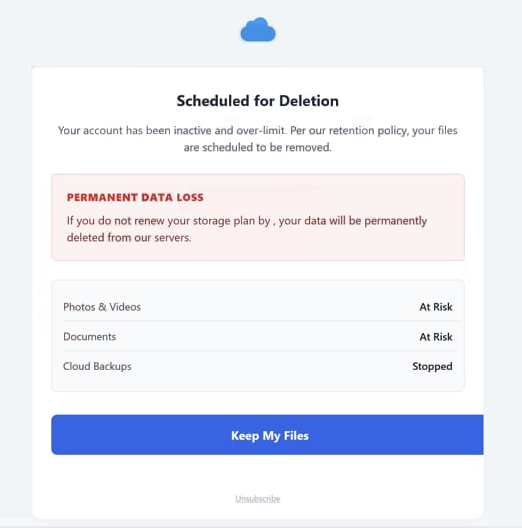
The full “Cloud – Scheduled for Deletion” phishing email is below:
Subject: URGENT: Renewal attempt failed
Cloud
Scheduled for DeletionYour account has been inactive and over-limit. Per our retention policy, your files are scheduled to be removed.
Permanent Data Loss
If you do not renew your storage plan by , your data will be permanently deleted from our servers.
Photos & Videos At Risk
Documents At Risk
Cloud Backups Stopped
Keep My Files
Unsubscribe
How to recognize phishing emails like “Cloud – Scheduled for Deletion”
Phishing emails that use account deletion themes often rely on vague explanations. They claim that an account will be removed, but do not provide specific details such as exact timestamps, account identifiers, or verifiable activity. Legitimate service notifications usually include clear and traceable information.
Another key sign is the use of a direct link for account recovery or confirmation. Instead of directing users to access their account through the official cloud service website, the email includes a link to a login page hosted on a different domain.
The sender address may also reveal inconsistencies. While the display name may appear to represent a cloud provider, the actual email address often comes from an unrelated domain. This mismatch indicates that the email is not genuine.
The email is usually written in a general format. It may not include the recipient’s name or account-specific details, which allows it to be sent to many users.
The wording is designed to create urgency. By suggesting that the account and its data will be permanently deleted, the email encourages immediate action without careful review.
Recognizing these patterns helps identify phishing emails before interacting with them. Emails that combine urgent deletion warnings, external login links, and inconsistent sender details should be treated with caution.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.