The “Suspicious Access To Your Mailbox” email is a phishing scam designed to frighten recipients into believing that unauthorized activity has been detected on their email account. The message is disguised as a security notification from an email provider and typically claims that a suspicious sign-in attempt or unfamiliar device has accessed the mailbox. Although the alert may appear urgent and legitimate, it is fraudulent and intended to steal account credentials.
Most versions of the “Suspicious Access To Your Mailbox” scam attempt to create panic by suggesting that the account may be compromised. The email often encourages recipients to review recent login activity or secure the account immediately through a button or link included in the message. Phrases such as “CONTROL ACCESS” or similar security-related prompts are commonly used to pressure users into reacting quickly rather than carefully inspecting the email.
The provided link does not lead to a legitimate email provider. Instead, it redirects users to a counterfeit login page designed to imitate popular webmail services such as Gmail, Yahoo Mail, or generic hosting portals. These fake pages are created specifically to collect usernames and passwords entered by victims. Once credentials are submitted, the attackers gain access to the compromised mailbox.
A compromised email account can create significant security risks. Attackers may search stored correspondence for sensitive information, use the account to distribute additional phishing emails, or attempt to reset passwords connected to other online services. Since many platforms rely on email accounts for account recovery, gaining access to one mailbox can potentially expose multiple accounts tied to it. Security researchers regularly warn that stolen email credentials are frequently used in broader identity theft and fraud operations.
Another reason the “Suspicious Access To Your Mailbox” phishing campaign can be effective is its generic structure. The email often avoids referencing a specific provider directly, which allows the same template to target users of many different email services. Even recipients who have not noticed suspicious activity may still react out of concern for losing access to their account or personal information.
Some versions of the scam may also include additional warnings about mailbox restrictions, password expiration, or suspicious spam activity. These variations are all intended to strengthen the sense of urgency and encourage immediate interaction with the phishing link. Despite differences in wording, the objective remains the same: to collect login credentials through deception.
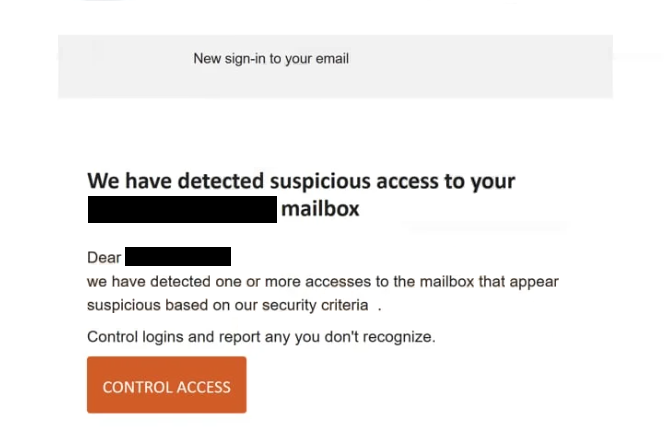
Subject: We have detected suspicious access to your – mailbox
New sign-in to your email -.
We have detected suspicious access to your – mailbox
Dear -,
we have detected one or more accesses to the mailbox that appear suspicious based on our security criteria .Control logins and report any you don’t recognize.
CONTROL ACCESS
How to recognize phishing emails
Recognizing phishing emails like the “Suspicious Access To Your Mailbox” scam requires paying attention to common warning signs often present in fraudulent security notifications. While these emails are designed to imitate legitimate alerts, they usually contain inconsistencies that reveal their true purpose.
One of the most common indicators is urgency. Phishing emails frequently warn that immediate action is required to secure an account or prevent unauthorized access. In this case, the message may claim that suspicious login attempts have been detected or that the mailbox is at risk. This pressure is deliberate and is intended to make recipients react quickly without verifying the legitimacy of the notification.
The sender’s email address is another important detail to inspect. Fraudulent emails often imitate official support or security addresses but include subtle changes such as misspellings, additional characters, or unrelated domains. Even when the sender’s name appears trustworthy, the underlying address may reveal that the message did not originate from a legitimate provider.
Links embedded in phishing emails should always be treated cautiously. The visible text may appear to point to a familiar service, but hovering over the link often reveals a completely different destination. These links commonly lead to fake login pages built specifically to capture credentials. Legitimate providers generally encourage users to access account settings directly through their official websites rather than through unsolicited links in unexpected emails.
The wording and structure of phishing emails can also provide clues. Some contain grammatical errors, awkward phrasing, or inconsistent formatting. Others may appear polished but still rely heavily on generic wording and vague security claims. A lack of personalization is also common because phishing campaigns are usually distributed to large numbers of recipients at once.
Another major warning sign is any request to verify account credentials through a link. Legitimate email providers do not ask users to confirm passwords or recovery details through external login pages sent in random security notifications. Messages urging users to “verify,” “control access,” or “secure” accounts through embedded links are commonly associated with phishing activity.
Unexpected attachments should also be approached carefully. Some phishing emails include files disguised as login reports, security logs, or verification documents. Opening these attachments may expose devices to malware if the files contain malicious scripts or executable content.
A safer approach is to avoid interacting with suspicious emails directly. Instead of clicking links inside the message, users should access their accounts through the official provider website and check for alerts manually. If no suspicious activity appears there, the email is likely fraudulent.
Awareness remains one of the most effective defenses against phishing campaigns. The “Suspicious Access To Your Mailbox” scam relies on fear, urgency, and trust in familiar security language to manipulate recipients. Taking time to inspect the sender, review links carefully, and verify claims independently can significantly reduce the risk of account compromise and credential theft.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.