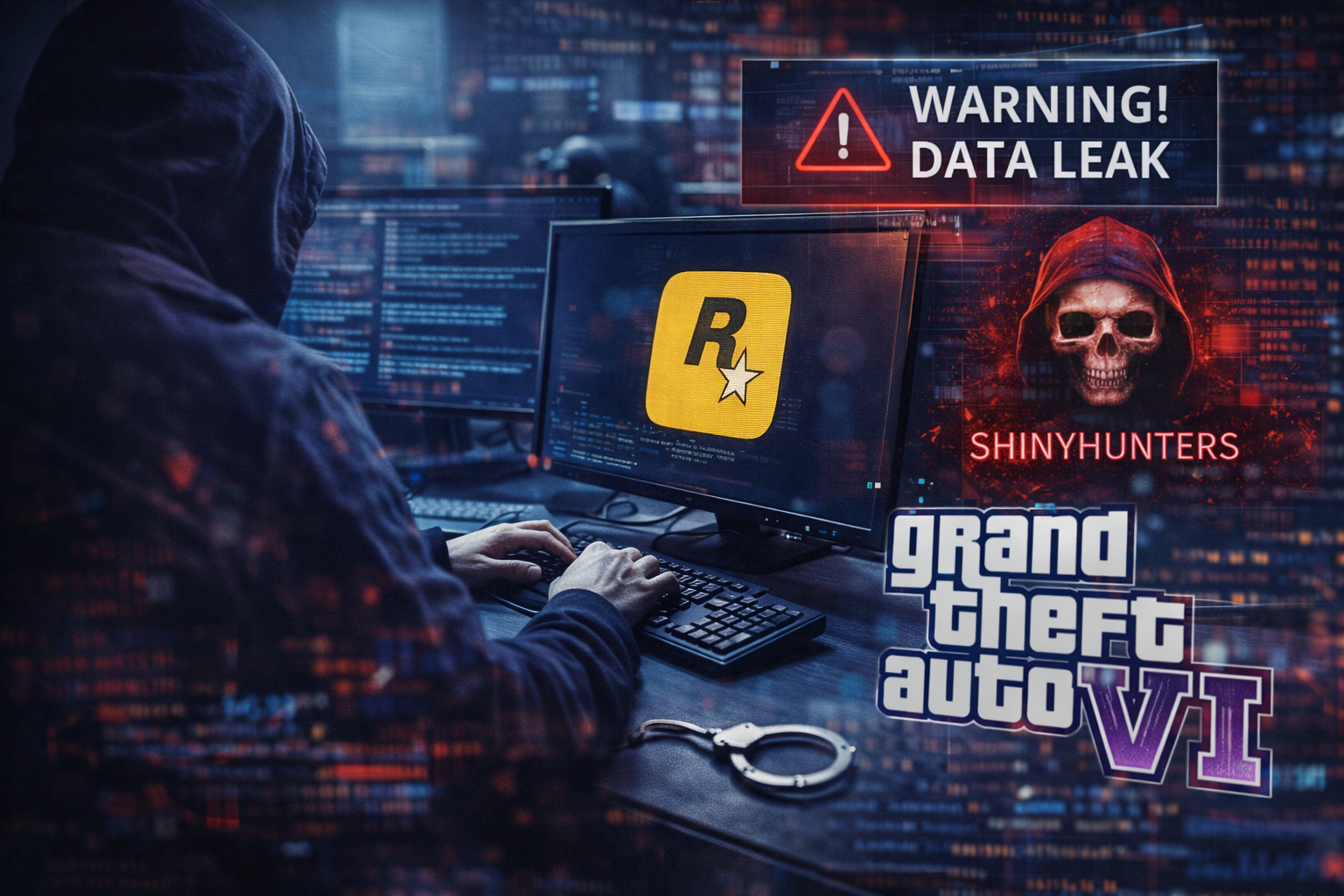
A cyberattack targeting Rockstar Games has led to claims that internal company data connected to Grand Theft Auto VI has been accessed, with a threat to release the information if demands are not met.
The activity has been attributed to ShinyHunters, which published a message on a dark website stating that it had compromised Rockstar systems and was seeking contact from the company. The group set a deadline of April 14, 2026, warning that data would be released if no response was received.
According to multiple reports, the intrusion did not involve a direct breach of Rockstar’s own infrastructure. Instead, access was obtained through a third-party service connected to the company’s cloud environment. The entry point was identified as Anodot, an analytics and monitoring platform used to track operational data.
Investigators and reporting indicate that attackers extracted authentication tokens from Anodot, which allowed them to access data stored in Rockstar’s cloud environment hosted on Snowflake. These tokens enabled the attackers to authenticate as legitimate users without exploiting vulnerabilities in Snowflake itself.
Once access was obtained, the group is reported to have exfiltrated internal data using standard database queries. Because the access appeared legitimate, detection was not immediate in all cases, according to reporting on the incident.
The group did not disclose the full scope of the data it claims to hold. Reports indicate that the information may include internal corporate data such as metrics, operational records, or other business-related information. The quantity and sensitivity of the data have not been independently verified.
Rockstar Games confirmed that a security incident had occurred and stated that it involved a limited amount of internal company information. The company said the incident was linked to a third-party breach and that there was no impact on its operations or on player data.
The attackers’ approach is consistent with previous activity linked to ShinyHunters, which has been associated with targeting third-party services and authentication systems to gain access to corporate environments. The group has previously used similar methods involving stolen credentials and integration points between platforms.