FedEx Express email scam refers to a malicious email that’s disguised to look like a parcel delivery notification from FedEx. It has an attachment that, if opened, would infect the computer with the LokiBot trojan. The LokiBot infection is a data-stealing trojan that could steal users’ login credentials, including passwords.
Malicious actors often disguise their malware emails as notifications from parcel delivery companies like FedEx and DPD because users are more likely to open attachments when they see names of companies whose services they often use.
FedEx is a common company name used in these emails. This particular malicious email claims that a parcel is awaiting pick up and an attached file has all the relevant information. If you receive this email and open the attachment, you would initiate the malware that’s hidden in it. In this case, it would be the LokiBot trojan.
LokiBot trojan is a very dangerous trojan that steals data. It can affect both Windows and Android operating systems. On both, it can steal saved login credentials and passwords and track your activities (e.g. log keystrokes). When it records information, the data is saved in a remote server operated by malicious actors.
On Android, the LokiBot trojan can perform more malicious activities. For example, it may show a fake notification from your bank app about someone sending you money. If you click on the notification, you would be asked to log in to your online bank. That’s usually how it works with legitimate transaction notifications so it wouldn’t necessarily alarm users. But the login forms would be fake and by putting in your credentials, you would be giving them away to the trojan operators. The same can happen with other apps like Outlook and WhatsApp.
The trojan also encrypts files when users try to remove LokiBot trojan from their Android devices. It demands a ransom of $100 in bitcoin. But fortunately, copies of original files are left on the device, so there’s no need to even consider paying.
But even if encrypted files can be recovered, the fact that LokiBot trojan steals data makes it a very dangerous infection. It’s also a pretty stealthy infection on both Windows and Android operating systems. It needs to remain hidden from view in order to carry out its malicious activities without users interfering.
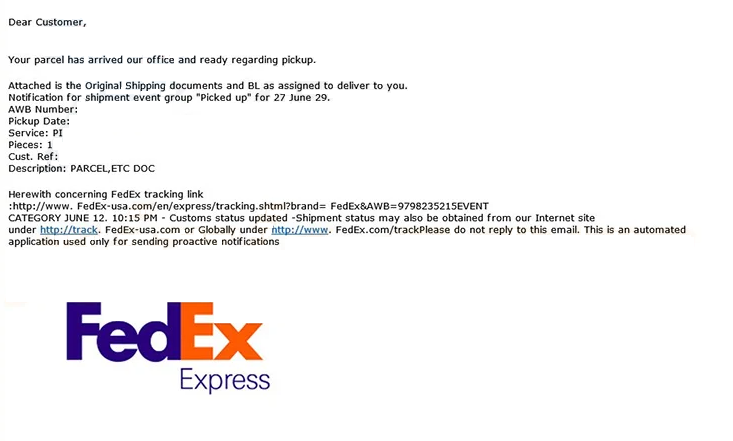
Dear Customer,
Your parcel has arrived our office and ready regarding pickup.
Attached is the Original Shipping documents and BL as assigned to deliver to you. Notification for shipment event group “Picked up” for 27 June 29.
AWB Number:
Pickup Date: 0
Service: PI
Pieces: 1
Cust. Ref:
Description: PARCEL,ETC DOC
Herewith concerning FedEx tracking link :hxxp://www. FedEx-usa.com/en/express/tracking.shtml?brand= FedEx&AWB=9798235215EVENT CATEGORY JUNE 12. 10:15 PM – Customs status updated -Shipment status may also be obtained from our Internet site under hxxp://track. FedEx-usa.com or Globally under hxxp://www. FedEx.com/trackPlease do not reply to this email. This is an automated application used only for sending proactive notifications
If you have opened such suspicious email attachments in the past, you need to scan your computer with anti-virus software immediately because an infection could be lurking on the computer and stealing information/data. If your anti-virus does detect LokiBot trojan or some other infection, you may need to take some steps. For example, change all your passwords to secure accounts.
How to recognize malicious emails?
As long as you know what to look for, you should be able to recognize most malicious emails. They are usually quite low-effort and have plenty of red flags that make them quite obvious.
One of the biggest malicious email giveaways is grammar/spelling mistakes. Malicious emails are disguised to look like they’re sent by legitimate companies (in this case – FedEx) so if they’re full of very obvious mistakes, it’s quite evident that they’re fake. For example, in the example image above, the email says “Your parcel has arrived our office and ready regarding pickup”. The very first sentence is a dead giveaway that the email is not actually sent by FedEx. These kinds of mistakes would look highly unprofessional in an email. And considering parcel notifications from delivery companies are automatically generated emails, they will have no mistakes in them. If you notice any mistakes in automatic emails sent by legitimate companies, it’s an immediate giveaway.
Another red flag is you being referred to as “Customer”, “Member”, “User”, etc., in emails that should include your name. For example, if you receive an email from a company whose services you use, you will always be addressed by name. This is a common tactic that most companies use to make emails seem more personal. And if we take parcel notifications as an example, they usually don’t use the above-mentioned generic words and just use simple variations of “Hello”.
Lastly, the sender’s email address can also give it away as malicious. That is one of the easiest things you can check. If the email address looks completely random (made up of random combinations of letters and numbers) but the sender claims to be from a legitimate company, it’s more than likely that it’s malicious.
Generally, users should be very cautious with unsolicited emails that have attachments. Whether an email looks legitimate or not, all email attachments should be scanned with anti-virus software or VirusTotal before opening them. This will ensure that no malicious attachments would be opened.
FedEx Express email scam removal
The FedEx Express email scam is not dangerous as long as you don’t open the attachment. But just to be safe, it’s better to remove FedEx Express email from the inbox. If you have opened the email attachment, you may not have noticed that a trojan was initiated. You need to scan your computer with anti-malware software immediately to check whether it’s indeed infected.
LokiBot trojan is a very known infection so it will be detected by most anti-virus programs. If it is detected, you need to change all your passwords immediately and secure your accounts. As we’ve already explained, LokiBot steals data so it could have stolen your login credentials. Make sure you change your passwords from a secure device.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.