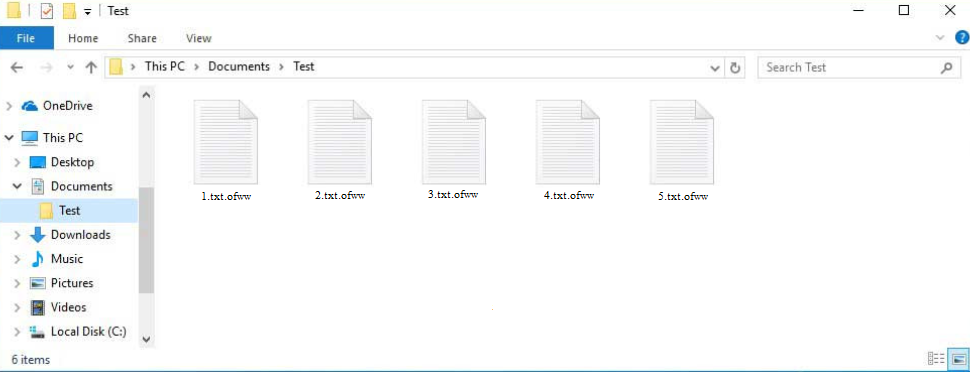
Ofww ransomware is part of the Djvu/STOP ransomware family. It’s essentially another version of an already notorious file-encrypting malware. Encrypted files will have .ofww added to them. Unless you have a decryptor, you will not be able to open these files. And getting the decryptor will be quite troublesome. There currently is no free way to recover files unless you have a backup.
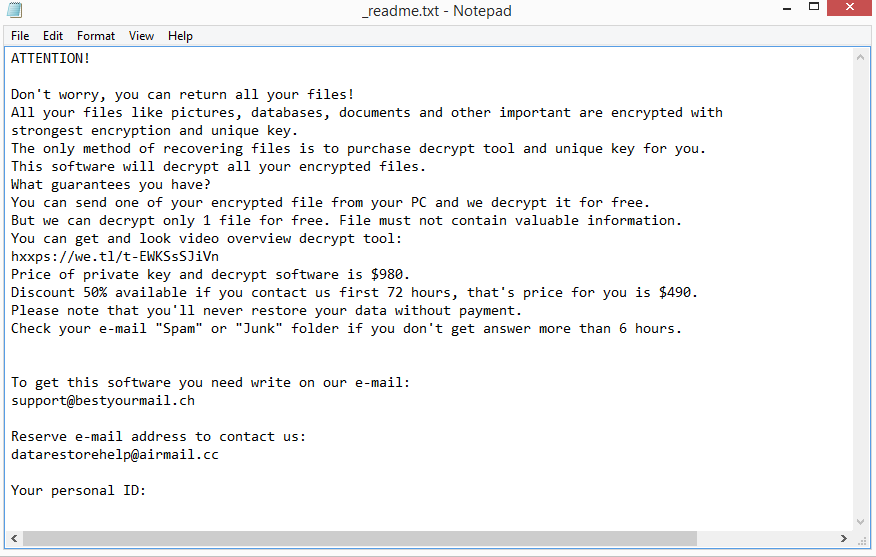
The Ofww ransomware encrypts files and appends.ofww to them. Sadly, you will discover that all of your photos, videos, documents, etc., are the main targets of this ransomware. An encrypted text.txt file, for instance, would become text.txt.ofww. All folders containing encrypted files will also have a _readme.txt ransom note once the files have been fully encrypted. The note explains where to get the Ofww ransomware decryptor. The cybercriminals demand that you pay $980 for it. There’s also a supposed 50% discount for victims who make contact within the first 72 hours but you should be skeptical. In general, it is not a good idea to trust hackers to send you the Ofww ransomware decryptor even if you pay. There is nothing actually stopping cyber criminals from simply taking your money because ransomware doesn’t function like a regular business with obligations.
It is currently not possible to recover files for free unless you have a backup. Although free decryptors are frequently provided by malware researchers to assist ransomware victims, it’s not always possible to do that. Ransomware versions from the Djvu/STOP family use online keys to encrypt files, which essentially means that the keys are unique to each victim. For a decryptor to work on your files, you specific key is needed. So until those keys are released, a free Ofww ransomware decryptor is not very likely. There is a free Djvu/STOP decryptor by Emsisoft that you could try but it’s not likely to work.
You can access your backup to start recovering files as soon as you remove Ofww ransomware from your computer. Make sure to use a good anti-malware program and not try to do it manually because you could end up causing even more damage to your device.
How does ransomware infect computers?
Malware can infect a computer in a variety of ways. Users who open random email attachments, click on unknown links, do not install security updates, pirate copyrighted content using torrents, etc., are much more likely to pick up malware than those with good browsing habits.
Users opening infected email attachments is one of the most common ways malware gets onto their computers. Malicious actors disguise their malware-infected emails to appear, to some extent, as if they’re sent by legitimate companies. But because malicious senders often don’t speak the language (in most cases – English) fluently, the emails are quite poorly done and are immediately obvious. As long as you pay attention when dealing with unsolicited emails, you should be able to spot malicious ones without much trouble. The most obvious sign is grammar/spelling mistakes. Such mistakes are very glaring when senders claim to be from legitimate companies. Because mistakes make an email appear very unprofessional, companies will do their best to avoid them. But malicious emails are usually full of them.
Generic terms like “User”, “Member”, and “Customer” being used in place of your name in emails is another indication that you might be dealing with a malicious email. You will always be addressed by name in emails from companies whose services you use since it makes the correspondence feel more personal. However, since malicious actors do not have access to personal data, they use generic terms.
You should also check the sender’s email address whenever you receive an unsolicited email. If the email address appears random, it’s likely spam or a malicious email. But even if an email looks legitimate, you should still research it to check whether it belongs to whomever the sender claims to be.
It’s important to note that malicious spam emails can occasionally be very sophisticated. This is usually the case when specific users are targeted. Malicious emails might appear considerably more convincing if the cybercriminals have access to specific personal information and put more effort into their malicious campaigns. A sophisticated malicious email would not have any grammar/spelling mistakes, address the target by name, as well as include some details that would lend the email credibility. This is why you should always scan email attachments with anti-virus software or VirusTotal before opening them.
Lastly, it’s no secret that torrents are frequently used to distribute malware. The majority of torrent sites you come across when looking for torrents are very poorly moderated. Poorly moderated torrent websites allow anyone to upload torrents, so it’s not difficult for malicious actors to upload torrents with malware in them. It’s especially common to have malware in torrents for entertainment content, usually movies, TV series, and video games. So if you use torrents to get copyrighted content for free, you’re risking a serious malware infection and potential data loss.
Ofww ransomware removal
Ransomware should be removed with professional anti-virus tools because it is a pretty sophisticated infection. If you don’t already have an anti-virus program installed, there are several good options for you to choose from. An anti-virus program would remove Ofww ransomware from your system without a problem, allowing you to start recovering files from backup if you have it.
We should stress that you shouldn’t access your backup until the ransomware has been fully removed. Otherwise, the files in the backup would become encrypted as well. This would lead to potential permanent file loss.
There are not many options available for you if you don’t have a backup. Your only choice might be to wait for a free Ofww ransomware decryptor to be released. But unfortunately, as we’ve already said, when it would be released or even if is not certain. But if it were to be released, it would appear on NoMoreRansom.
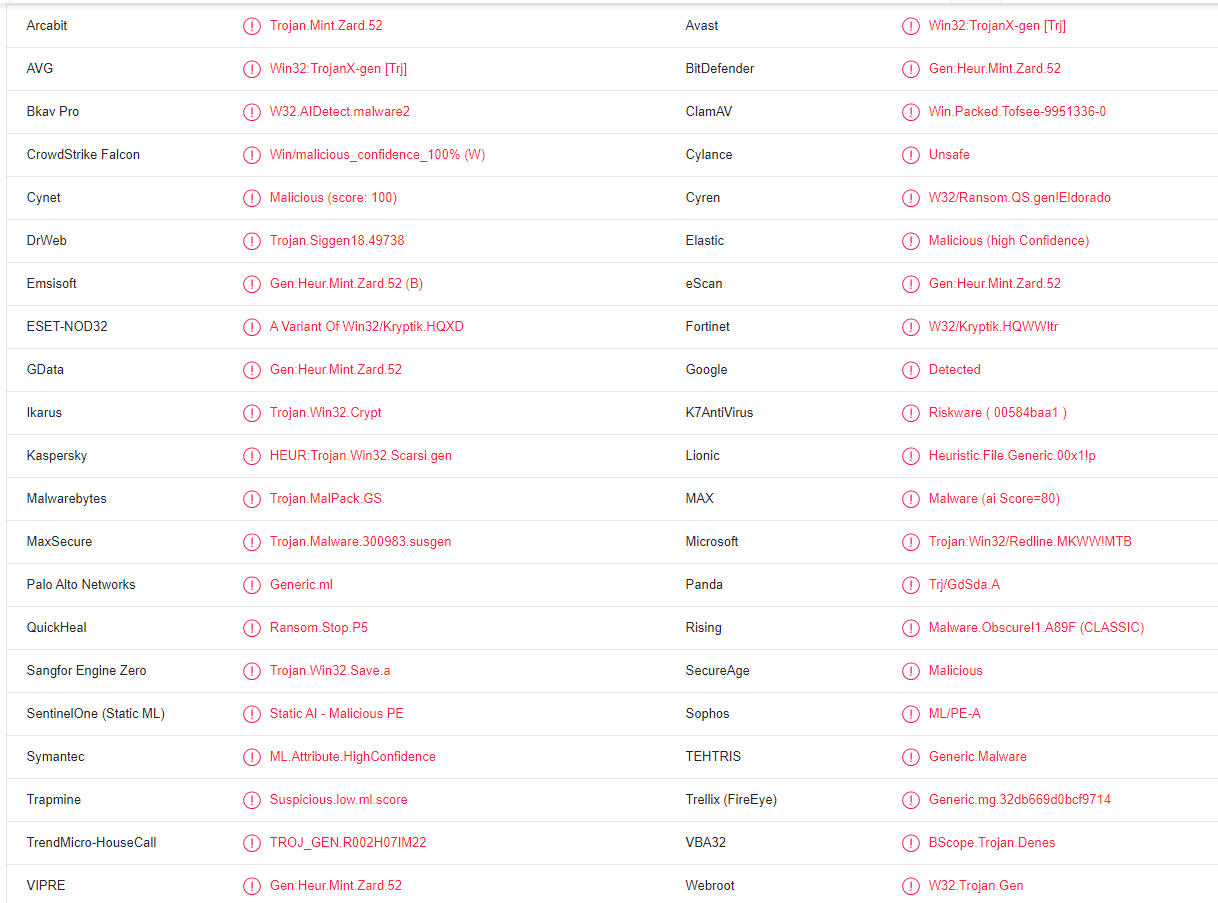
Ofww ransomware is detected as:
- Win32:TrojanX-gen [Trj] by AVG/Avast
- A Variant Of Win32/Kryptik.HQXD by ESET
- HEUR:Trojan.Win32.Scarsi.gen by Kaspersky
- Trojan.MalPack.GS by Malwarebytes
- Gen:Heur.Mint.Zard.52 by BitDefender
- Trojan:Win32/Redline.MKWW!MTB by Microsoft
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.