Privacy Protector is presented as a browser tool that claims to block trackers and improve online privacy. Despite this description, it behaves as adware. After installation, it introduces advertising into normal browsing sessions and does not provide the protective features it advertises.
The change is not always obvious at first. Websites begin to display additional elements that were not there before. These can include banners layered over content, pop-ups that interrupt navigation, or coupon boxes appearing on shopping pages. The ads are not part of the original websites. They are injected by Privacy Protector as pages load.
These advertisements are not limited to visual clutter. Clicking them can lead to pages that attempt to push downloads, promote questionable services, or request sensitive information. Some redirects may lead to sites designed to collect login credentials or payment details. Others may expose the system to further unwanted software.
The extension also operates in the background while browsing. It can monitor activity such as visited pages, search queries, and interactions with links. This information is used to adjust the ads that are displayed. Instead of reducing tracking, the extension introduces another layer of data collection tied to advertising activity.
Over time, users may notice that pages load more slowly or do not display correctly. Ads inserted by the extension can overlap with site elements or interfere with normal navigation. In some cases, the browser may behave differently, including unexpected redirects or settings that do not stay changed.
Privacy Protector can also go beyond advertising behavior. It may alter browser configuration in a way similar to a hijacker. This can affect search settings or how pages are opened, making it harder to maintain normal browsing preferences.
The main issue with this adware is not just the presence of ads, but the combination of intrusive advertising, background data collection, and reduced control over the browser. The extension does not improve privacy. Instead, it introduces additional exposure to third-party content and tracking mechanisms.
How Privacy Protector ends up on a device
Privacy Protector is often introduced during the installation of other software rather than being deliberately selected. It can be included in setup packages for free programs distributed through third-party download sites. During installation, additional components may be presented as optional or preselected items. If these options are accepted, the extension can be installed without clear intent.
Another route is through download pages that promote the extension as a privacy or security tool. The description may highlight features such as blocking trackers or improving safe browsing. Users looking for privacy tools may install it without reviewing the permissions it requests.
Once added to the browser, the extension requires access to browsing data to function. These permissions allow it to read activity across websites and modify content as pages load. This access is what enables both the ad injection and the data tracking behavior.
A noticeable sign that Privacy Protector has been installed is a sudden increase in ads across multiple websites, including those that normally show minimal advertising. Another indicator is the appearance of new extensions in the browser that were not intentionally added. Changes in browser performance or unexpected redirects can also point to its presence.
Avoiding this type of software depends on how applications and extensions are installed. Reviewing installation steps carefully can reveal additional components that are bundled with the main program. Choosing installation modes that show all included items allows users to decline unwanted additions.
Browser extensions should also be evaluated before installation. Tools that request broad permissions to read and change data across websites should be examined closely, especially if their advertised function does not clearly require that level of access.
Privacy Protector relies on being installed without careful review. When installation steps are checked and permissions are understood before approval, the chances of adding such adware are significantly reduced.
Remove Privacy Protector adware
While adware infections are not particularly serious, it’s strongly recommended to deal with them as soon as possible. Using an anti-virus program to remove Privacy Protector adware is the easier way, as the program will take care of everything.
Offers
Download Removal Toolto scan for Privacy ProtectorUse our recommended removal tool to scan for Privacy Protector. Trial version of provides detection of computer threats like Privacy Protector and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Uninstall Privacy Protector and related programs.
Remove Privacy Protector from Windows 8
Right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel choose Programs and Features and select to Uninstall a software.


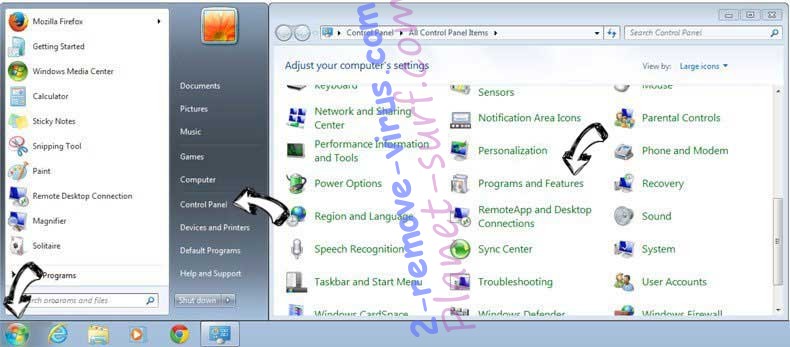
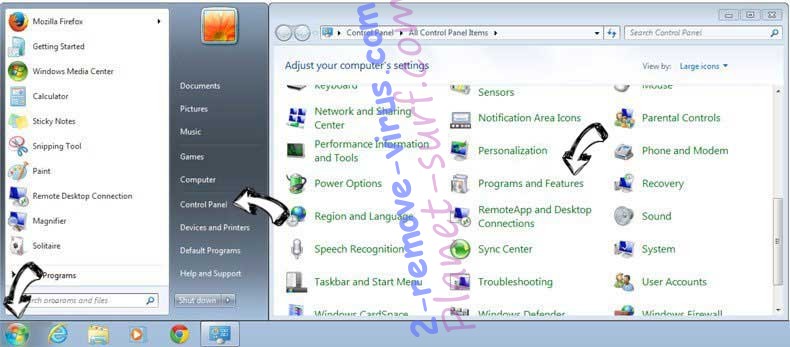
Uninstall Privacy Protector from Windows 7
Click Start → Control Panel → Programs and Features → Uninstall a program.
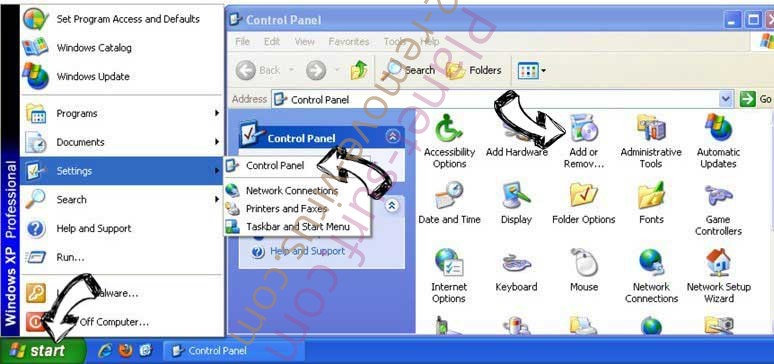
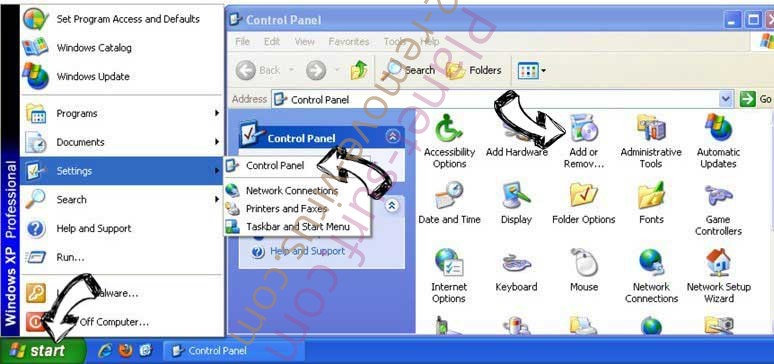
Delete Privacy Protector from Windows XP
Click Start → Settings → Control Panel. Locate and click → Add or Remove Programs.
Remove Privacy Protector from Mac OS X
Click Go button at the top left of the screen and select Applications. Select applications folder and look for Privacy Protector or any other suspicious software. Now right click on every of such entries and select Move to Trash, then right click the Trash icon and select Empty Trash.


Step 2. Delete Privacy Protector from your browsers
Terminate the unwanted extensions from Internet Explorer
- Tap the Gear icon and go to Manage Add-ons.

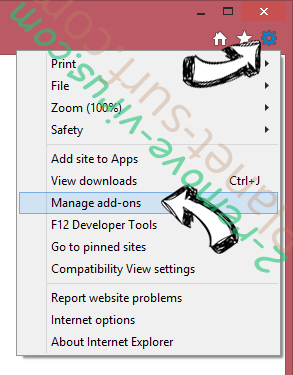
- Pick Toolbars and Extensions and eliminate all suspicious entries (other than Microsoft, Yahoo, Google, Oracle or Adobe)

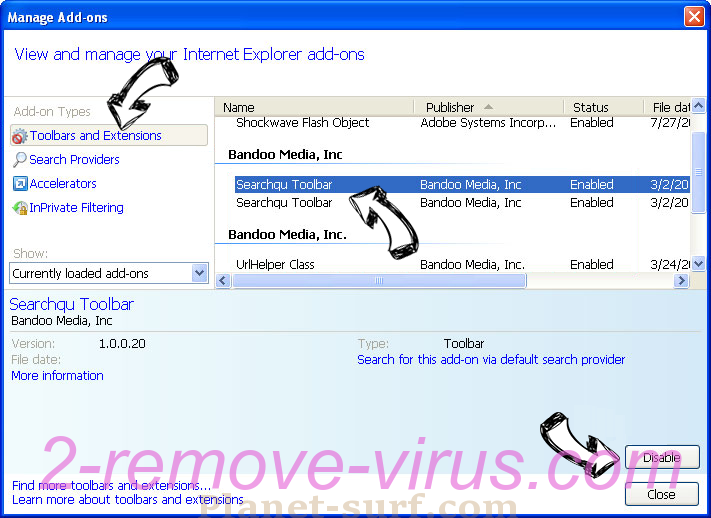
- Leave the window.
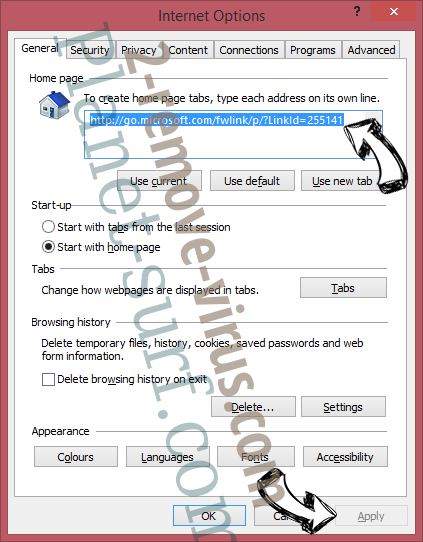
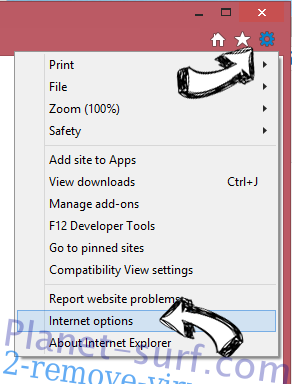
Change Internet Explorer homepage if it was changed by virus:
- Tap the gear icon (menu) on the top right corner of your browser and click Internet Options.

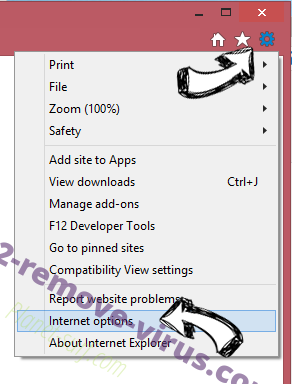
- In General Tab remove malicious URL and enter preferable domain name. Press Apply to save changes.

Reset your browser
- Click the Gear icon and move to Internet Options.

- Open the Advanced tab and press Reset.

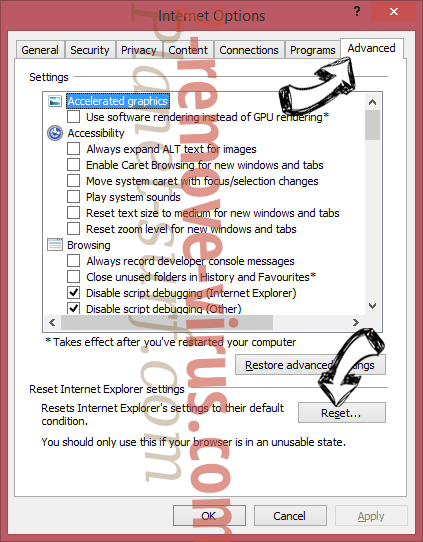
- Choose Delete personal settings and pick Reset one more time.

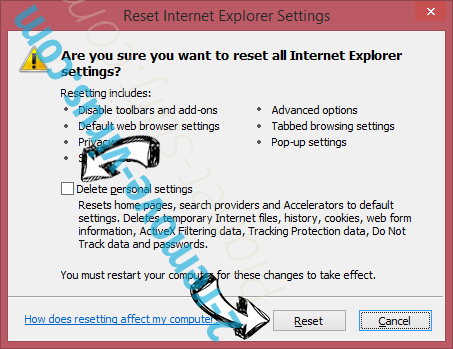
- Tap Close and leave your browser.

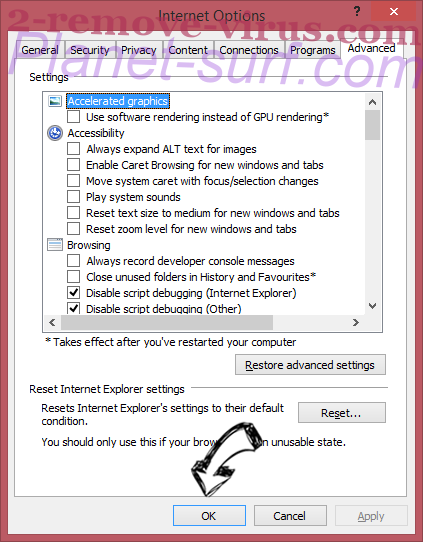
- If you were unable to reset your browsers, employ a reputable anti-malware and scan your entire computer with it.
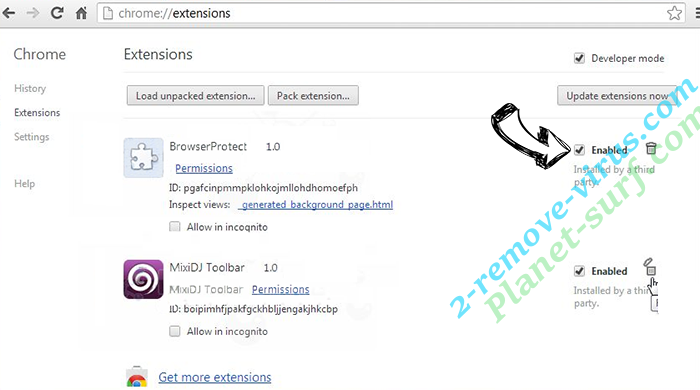
Erase Privacy Protector from Google Chrome
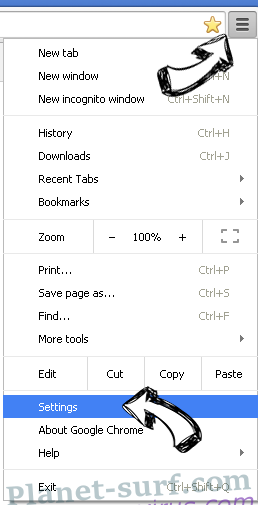
- Access menu (top right corner of the window) and pick Settings.

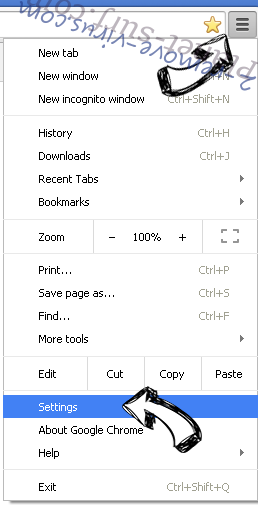
- Choose Extensions.

- Eliminate the suspicious extensions from the list by clicking the Trash bin next to them.

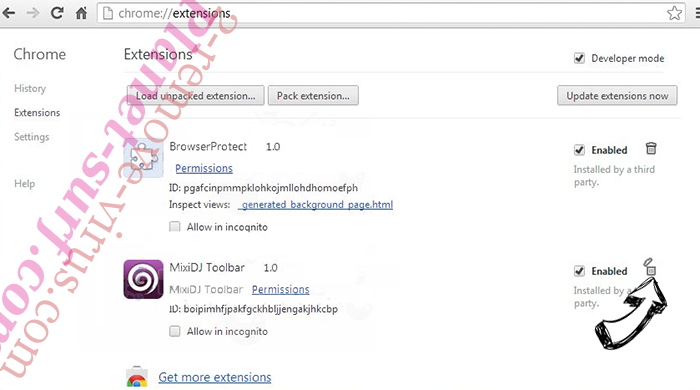
- If you are unsure which extensions to remove, you can disable them temporarily.

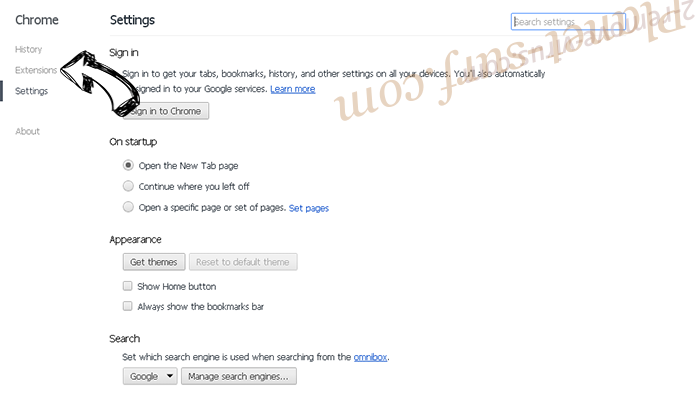
Reset Google Chrome homepage and default search engine if it was hijacker by virus
- Press on menu icon and click Settings.

- Look for the “Open a specific page” or “Set Pages” under “On start up” option and click on Set pages.

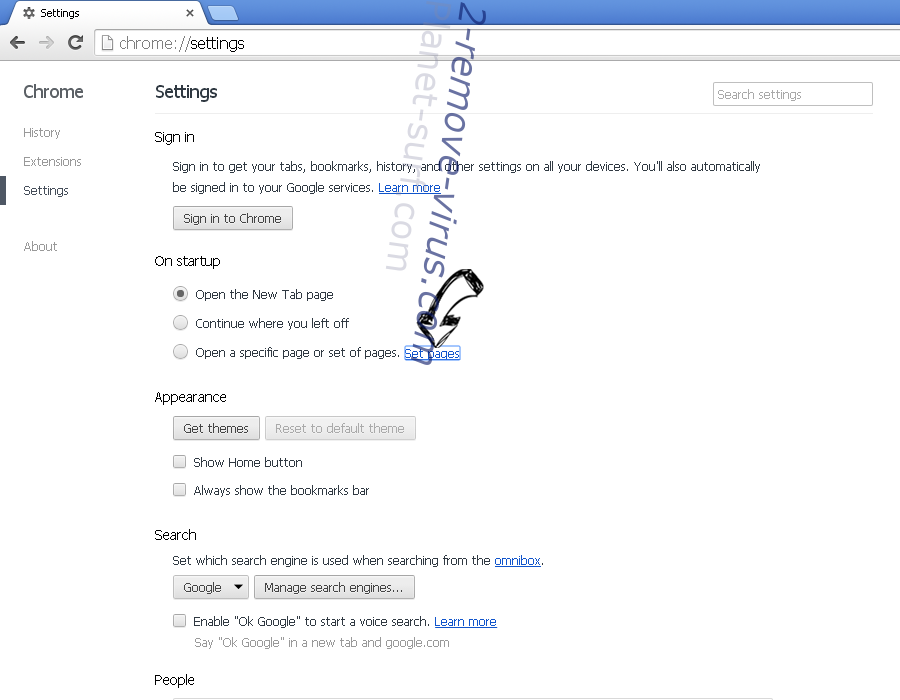
- In another window remove malicious search sites and enter the one that you want to use as your homepage.


- Under the Search section choose Manage Search engines. When in Search Engines..., remove malicious search websites. You should leave only Google or your preferred search name.

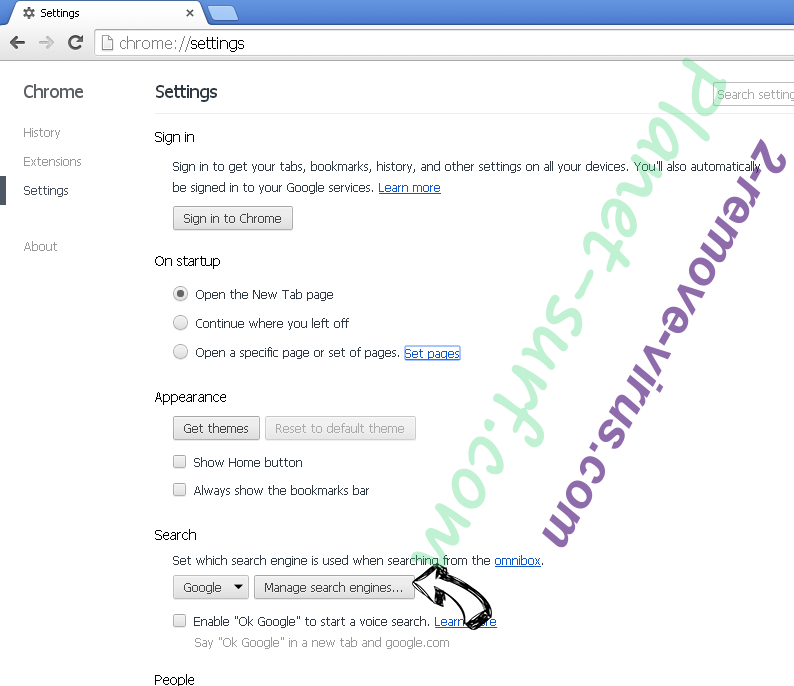


Reset your browser
- If the browser still does not work the way you prefer, you can reset its settings.
- Open menu and navigate to Settings.

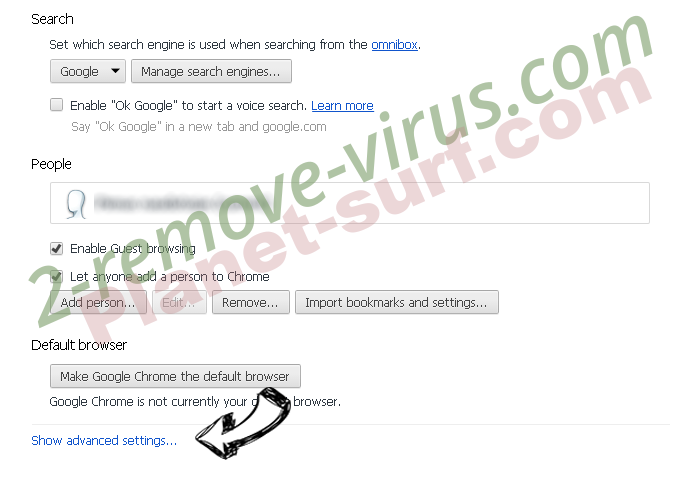
- Press Reset button at the end of the page.


- Tap Reset button one more time in the confirmation box.

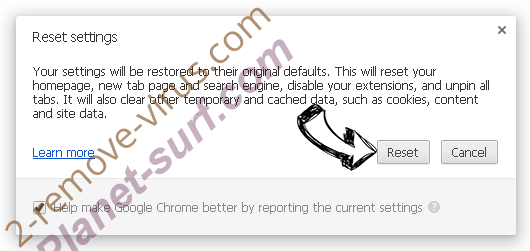
- If you cannot reset the settings, purchase a legitimate anti-malware and scan your PC.
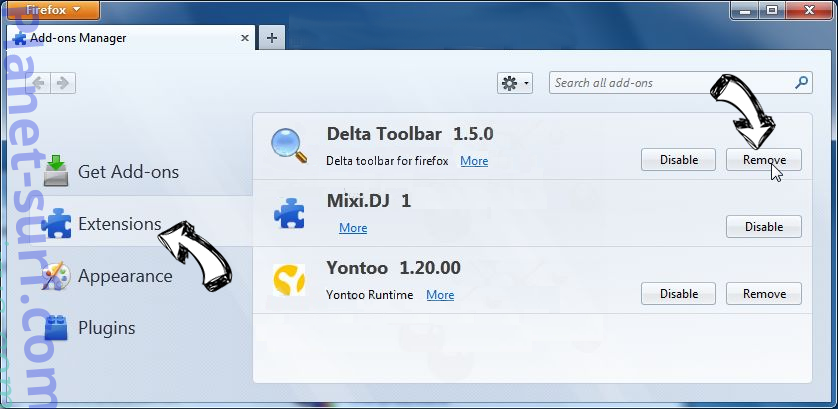
Remove Privacy Protector from Mozilla Firefox
- In the top right corner of the screen, press menu and choose Add-ons (or tap Ctrl+Shift+A simultaneously).

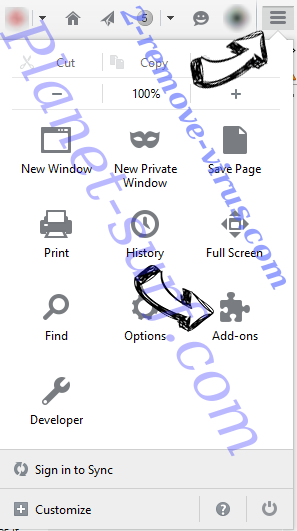
- Move to Extensions and Add-ons list and uninstall all suspicious and unknown entries.

Change Mozilla Firefox homepage if it was changed by virus:
- Tap on the menu (top right corner), choose Options.

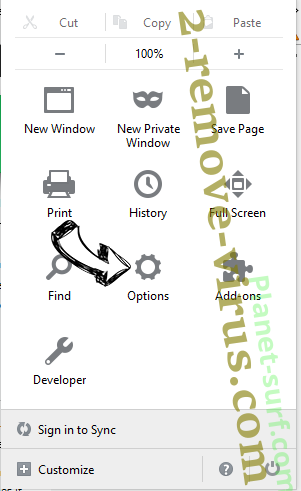
- On General tab delete malicious URL and enter preferable website or click Restore to default.

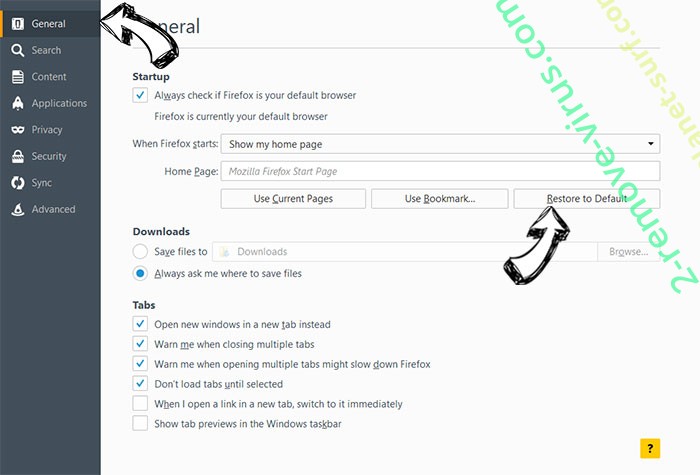
- Press OK to save these changes.
Reset your browser
- Open the menu and tap Help button.

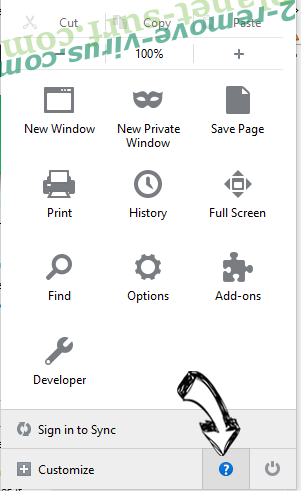
- Select Troubleshooting Information.

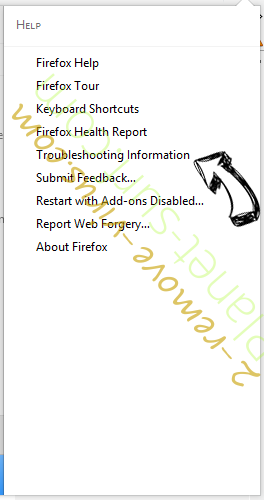
- Press Refresh Firefox.

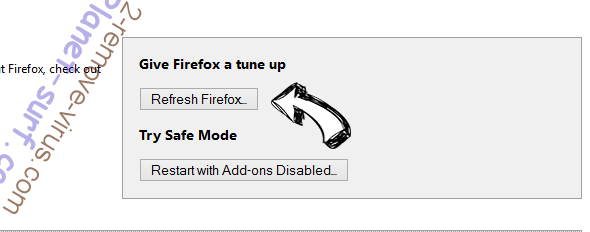
- In the confirmation box, click Refresh Firefox once more.

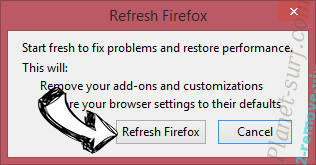
- If you are unable to reset Mozilla Firefox, scan your entire computer with a trustworthy anti-malware.
Uninstall Privacy Protector from Safari (Mac OS X)
- Access the menu.
- Pick Preferences.

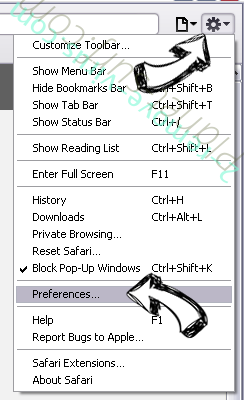
- Go to the Extensions Tab.

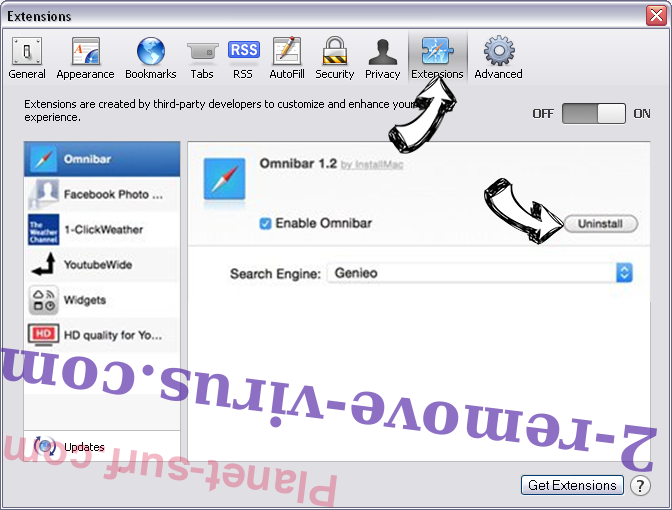
- Tap the Uninstall button next to the undesirable Privacy Protector and get rid of all the other unknown entries as well. If you are unsure whether the extension is reliable or not, simply uncheck the Enable box in order to disable it temporarily.
- Restart Safari.
Reset your browser
- Tap the menu icon and choose Reset Safari.

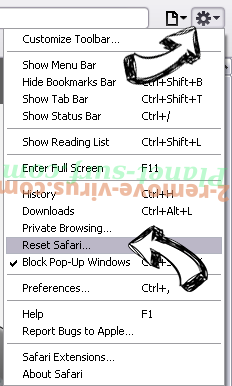
- Pick the options which you want to reset (often all of them are preselected) and press Reset.

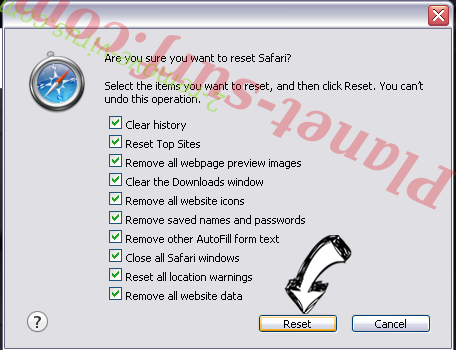
- If you cannot reset the browser, scan your whole PC with an authentic malware removal software.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.