The “Your Cloud Account Suspended” scam is a phishing email that claims the recipient’s cloud storage account has been restricted or temporarily disabled. It typically states that syncing, backups, or access to stored files has been stopped due to a problem such as exceeded storage limits, billing issues, or policy violations. These claims are not real and are used to prompt immediate action.
The email is written to create urgency and concern. It may warn that files are no longer accessible or that data could be lost if the issue is not resolved quickly. However, it does not provide clear or verifiable details about the supposed suspension. There are no timestamps, account identifiers, or specific activity logs included.
Instead of directing users to check their account through official channels, the email includes a link to “restore access” or “reactivate” the account. This link leads to a fraudulent website that imitates a cloud service login page. The page may look convincing, but it does not display any real account data, such as files, storage usage, or account settings.
The only function of this page is to collect login credentials. When users enter their email address and password, the information is sent directly to scammers. No account is restored, and no suspension is lifted. In many cases, the page may show a confirmation message or redirect to a legitimate website to make the process appear successful.
The suspension warning itself is fabricated. Similar phishing campaigns often use claims about storage issues or disabled services to pressure users into clicking malicious links and disclosing sensitive information.
If attackers obtain valid credentials, they can attempt to access the cloud account and any connected services. This may expose stored files, personal data, and backups. In some cases, attackers may change account settings or passwords, making it difficult for the original user to regain access.
Subject: From: System Notify | Subject: Your account has been disabled | ID:-
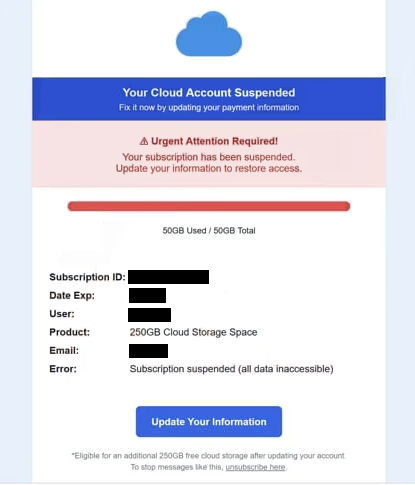
Your Cloud Account Suspended
Fix it now by updating your payment information
Urgent Attention Required!
Your subscription has been suspended.
Update your information to restore access.
50GB Used / 50GB TotalSubscription ID: –
Date Exp: –
User: –
Product: 250GB Cloud Storage Space
Email: –
Error: Subscription suspended (all data inaccessible)
Update Your Information
*Eligible for an additional 250GB free cloud storage after updating your account.
To stop messages like this, unsubscribe here.
How to recognize phishing emails like “Your Cloud Account Suspended”
Phishing emails that use suspension or restriction themes follow recognizable patterns. One of the main signs is the lack of specific information. The email claims that an account has been suspended but does not provide details that can be verified, such as exact usage data or account activity.
Another key indicator is the use of a direct link for account recovery. Legitimate cloud providers do not require users to restore access through unsolicited email links. Instead, they advise logging in through official websites or applications. Emails that push a single “reactivate” button should be treated with caution.
The sender address is also important to examine. While the display name may appear to represent a cloud service, the actual email address often comes from an unrelated domain. This mismatch is a strong sign of a phishing attempt.
The message is usually written in a general format. It often does not include the recipient’s name or any account-specific details, which allows it to be sent to many users at once.
The wording is designed to create urgency. By suggesting that access has already been suspended or that data is at risk, the email encourages quick action without careful verification. This pressure is a common tactic used in phishing campaigns.
Recognizing these patterns makes it easier to identify phishing emails before interacting with them. Emails that combine vague suspension claims, external login links, and inconsistent sender details should be treated as suspicious.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.