“On this day, I hacked your device’s operating system” email scam is classified as a sextortion scam because it threatens to release a private video of the recipient. While it may seem like an alarming email at first, it’s nothing more than a generic sextortion scam. The video the scammer threatens to release does not actually exist, so there is no need to pay the requested $1,250. You can just delete “On this day, I hacked your device’s operating system” email scam from your inbox.
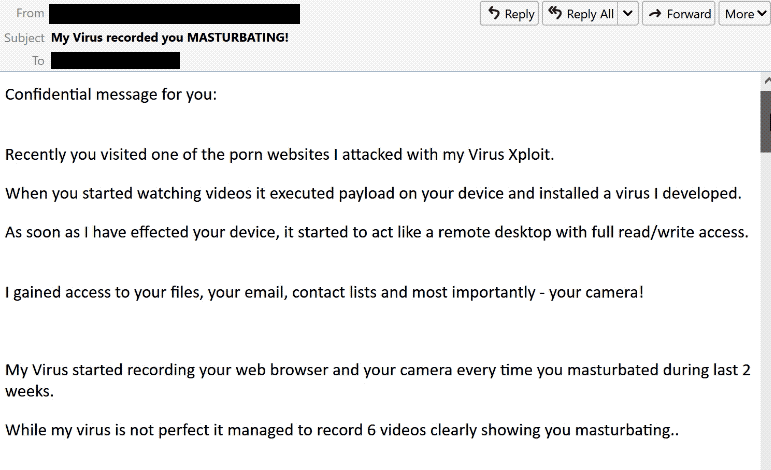
“On this day, I hacked your device’s operating system” email scam is a pretty generic sextortion scam. It follows the same pattern as all other sextortion scams that we’ve previously encountered. It first catches users’ attention with a subject line like “Security alert: Review the sign-in details” or “Your account has been hacked” to trick users into opening the email. The sender (aka the scammer) then proceeds to explain that they have hacked the recipient’s computer, installed malware, and essentially taken control of it.
They then try to scare users by claiming that they were able to enable the camera and microphone in order to make a video of users watching pornography. The scammer repeatedly tries to shame the recipient by using demeaning language. This kind of tactic can certainly have an effect on users, whether they actually watched pornography or not.
If the recipient does not agree to pay $1,250 to the provided bitcoin wallet address, the scammer threatens to release the supposed video online as well as send it to all contacts.
If you receive this kind of email, you can just delete it from your inbox. All claims in this email are not true. There is no malware/virus on your computer, nor is there a video of you watching pornography. You certainly don’t need to pay the requested sum of money.
Hi. I have bad news for you!
24.08.2022-On this day, I hacked your device’s operating system and got full access to your account. I have been watching you closely for a long time.
I installed a virus on your system that allows me to control all your devices. The virus software gives me access to all the controllers of your devices (microphone, video camera, keyboard, display). I have uploaded all your information, data, photos, browsing history to my servers. I have access to all your messengers, social networks, email, sync, chat history and contact list.
I learned a lot about you!
I thought what can I do with this data… I recently came up with an interesting idea: to create a video clip in which you masturbate in one part of the screen and watch a porn site in the other, such videos are now at the peak of popularity! What happened amazed me!
With one click, I can send this video to all your friends via email, social networks and instant messengers. I can also publish access to all your emails and instant messengers that you use. In addition, I found a lot of interesting things that I was able to publish on the Internet and send to friends.
If you don’t want me to do it, send me 1250 $ (US dollar) in my bitcoin wallet. My BTC address: bc1qe64taxlmfrvjryj6exhr7kut95x6w2ud6djtpq If you do not know how to replenish such a wallet, use the Google search engine. There is nothing difficult in this. As soon as funds arrive, I will see this and immediately remove all this garbage. After that we will forget each other. I also promise to deactivate and remove all malware from your devices. Trust me, I keep my word. It’s a fair deal and the price is pretty low considering I’ve been checking your profile and traffic for a while.
I give exactly two days (48 hours) from the moment of opening this letter for payment. After this period, if I do not receive the specified amount from you, I will send everyone access to your accounts and visited sites, personal data, and edited videos without warning. Remember: I do not make mistakes, I do not advise you to joke with me, I have many opportunities. There’s no point complaining about me because they can’t find me. Formatting the drive or destroying the device won’t help because I already have your data. It makes no sense to write back to me – I do not write from personal mail and do not look at the answers.
Good luck and don’t get angry! Everyone has their own job, you just got unlucky today.
P.S. In the future, I recommend that you follow the safety rules on the Internet and do not visit dubious sites
How do scammers obtain email addresses/passwords?
Although different scammers may be behind the sextortion email campaigns, they always operate in the same way. Scammers buy targets’ email addresses from hacker forums so if you’ve received one sextortion scam email, you’ll likely receive more in the future. Email addresses get leaked all the time by services that have bad security. This is why it’s not recommended to use your primary email address when signing up for things like mobile games and random sites. Once an email address has been leaked, it will start appearing in various data breaches. You can check whether your email address has been leaked on haveibeenpwned. There’s not much you can do if it has been leaked but you will at least know to be more cautious with unsolicited emails.
It is worth mentioning that some sextortion scammers include users’ passwords in emails. It works well to persuade users that a virus is actually on their computer. Because, in their mind, there is no other way the sender could know their password. The reason someone might have your password is actually fairly straightforward. Malicious actors obtain users’ passwords from hacker forums in the same way they do email addresses. Some services that users use have poor security and improperly secure users’ passwords. Passwords and other data may fall into the hands of criminals if such services become the target of a cyberattack. The data is then sold on hacker forums for use by other malicious actors.
Users must immediately change their password if they receive a sextortion email that discloses it. Users should keep in mind that passwords need to be complicated and difficult to crack. They should ideally consist of a random combination of capital and lowercase letters, numbers, and symbols. Each account’s password needs to be different. Users should use a password manager if they have problems remembering their passwords.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.