S.O.V.A. banking trojan is a highly sophisticated malware infection that targets Android devices. It’s considered to be a very dangerous infection because of its wide range of capabilities, including stealing credentials and banking information, as well as preventing users from removing it. It targets more than 200 mobile apps, including banking apps and crypto wallets.
The SOVA banking trojan is usually disguised as legitimate apps in order to trick users into installing it. Users may be directed to these fake/malicious apps via smishing campaigns. When users download and install the fake Android app, it sends a list of all installed apps to the command & control server (C2) operated by the malicious actors. When the threat actor has acquired the list of targeted applications, a list of addresses for each targeted application is sent back to the trojan via the C2. This information is stored in an XML file.
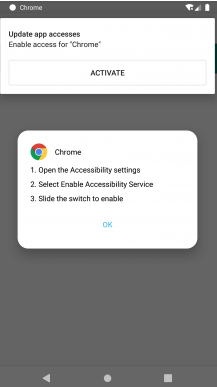
When users download the malicious app, they will be shown a window asking them to allow the app Accessibility permission. Granting this permission allows the malware to start its malicious activities. S.O.V.A. banking trojan can perform a variety of malicious actions, including logging keystrokes, stealing cookies, intercepting multi-factor authentication cookies, taking screenshots and recording videos, performing certain actions (screen clicks, swipes, etc.), adding fake overlays to apps, and mimicking banking/payment applications.
In order to steal login credentials and payment card information, the trojan will show fake pages. For example, when users try to log in to their bank account via an app, they may be shown an overlay window that looks identical to the legitimate window. If users type in their information, it would be sent to the malicious actors operating the trojan. These stolen credentials are often either sold on various hacker forums for other cybercriminals, or they may be used by the malware operators themselves to steal users’ funds.
It’s also believed that an updated version of the trojan will also encrypt all data on an Android device, essentially taking it hostage. Ransomware targeting Android devices is not very common so it’s a pretty unusual feature.
S.O.V.A. banking trojan can also protect itself from users trying to remove it. When users try to uninstall the app, the trojan intercepts this action and redirects users to the home screen that displays a message saying “The app is secured”. This can make S.O.V.A. banking trojan removal pretty tricky. Furthermore, it may be difficult for regular users to even notice the trojan because it may not show any apparent signs of being present. Stealthy behavior may allow the trojan to remain installed for much longer.
The trojan targets over 200 apps, including banking and crypto wallet apps. It targets specific countries, including Australia, Brazil, China, India, the Philippines, the UK, Russia, Spain, and Italy.
How is S.O.V.A. banking trojan distributed?
It appears that S.O.V.A. banking trojan is distributed mainly via smishing (or phishing via SMS) attacks. Users are sent links with messages claiming they need to download an app or an update. The SMS may be disguised to look like it was sent by a bank, government agency, etc. It’s not difficult to spoof phone numbers so they may appear fairly legitimate. However, the messages themselves are usually full of grammar/spelling mistakes, which gives them away immediately.
When users click on the links in these messages, they are taken to sites prompting them to download an app. It’s worth mentioning that legitimate SMS from banks or any other legitimate company/agency will never contain links. If users receive a message supposedly from their bank and it asks users to click the link in order to unblock their bank account, it’s a malicious message. Users should never click on unknown links, especially in SMS messages.
It also hides in fake apps that are made to appear like legitimate ones (e.g. Google Chrome). This is a common distribution method because many users are not careful when downloading apps onto their smartphones. Users may come across these fake apps being promoted on questionable third-party app stores or forums. It’s generally not recommended to download apps from non-official sources because it could lead to a malware infection. Those sites are often poorly managed and have inadequate security measures. Because of that poor moderation, malicious actors can easily upload deceptive apps with malware in them.
Malicious downloads are one of the reasons why users should stick to official app stores like the Google Play Store. Google invests a lot of money into making its app store secure, so the chances of downloading a malicious app are much slimmer when using the Play Store. However, even when using official stores, users need to be careful. Even if the Play Store is significantly more safe than any third-party app store, it’s still not perfect. Malicious actors use various methods to bypass Google’s security measures, and they are sometimes successful. Users should always read reviews, check permissions, research the developers, etc. Permissions in particular are something users should check carefully. Users should consider why apps request the permissions that they do and whether they actually need them. For example, if a mobile game app is requesting permission to access the microphone/camera, that should raise a few questions. If an app looks suspicious in any way, users should avoid downloading it, even if it’s on a legitimate store like Google Play.
S.O.V.A. banking trojan removal
The S.O.V.A. banking trojan is a very sophisticated infection and its removal can be very tricky. Android anti-virus apps detect the trojan so it’s recommended to try that for users whose devices are infected. However, if the trojan persistently tries to prevent its removal, a full factory reset may be necessary to remove S.O.V.A. banking trojan. That would delete all data on the device, including the trojan.
For users on whose devices the S.O.V.A. banking trojan has been confirmed, it’s highly recommended to change all passwords using a malware-free device. Furthermore, if any kind of banking information has been compromised, users need to contact their bank in order to secure their accounts.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.