About this threat
Bebloh Trojan is classified as a Trojan infection, that generally spreads via contaminated attachments, fake downloads or infected adverts. If you don’t have an anti-malware program on your machine, you could not realize that a Trojan has entered your device as it works quietly. Having a Trojan endangers your operating system as it could bring about extra infections. The Trojan might be quietly installing extra damaging software, accessing web pages and acquiring data about you, which could then be sent to cyber criminals. If you are attentive, you might notice the symptoms of an infection, which include slow Internet, a weird process in Task Manager and just general sluggish computer activity. If you are aware of the signs, there should be no trouble with recognize the Trojan. If notice the Trojan inside your system, ensure you terminate Bebloh Trojan. 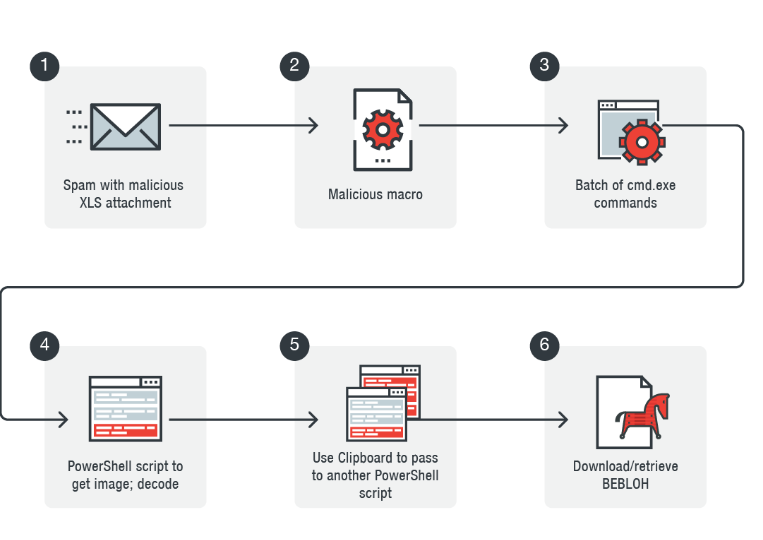
How is it spread
Most frequently, Trojans use email attachments, fake downloads and infected adverts to spread. Be vigilant about what emails you open, and how you browse the Internet if you want to avoid a contamination. Never open email attachments from unknown senders without first making sure they are safe. By carelessly opening every email attachment, you may end up with serious threats, such as file-encrypting malware. Adverts requesting you to install a plug-in so as to access content, as well as downloads from questionable websites, are especially popular methods to spread damaging program. Ensure you are using safe websites for your downloads. It may also be a good idea to not press on advertisements when on gambling, pornographic or illegal streaming web pages.
How does the threat behave
What Trojans do is basically make your system defenseless so that cyber crooks could access it and steal your sensitive information. If hackers decided to plant more malware onto your computer, it’s doubtful notice, at least not in the beginning. Your bank data, among other sensitive information, might be accessed by crooks, so take that into consideration. Trojans are severe threats thus you need to uninstall Bebloh Trojan, as soon as possible. This is why it’s recommended that users have an anti-malware installed. If you are notified about the infection in time, serious harm to your system may be avoided. If you don’t have a malware removal software but your machine is displaying signs of a contamination, get the software and use it to uninstall Bebloh Trojan.
Bebloh Trojan elimination
We recommend you act fast, and erase Bebloh Trojan as soon as you are able. We encourage obtaining a malware removal software as it will guarantee to uninstall Bebloh Trojan completely. Scan your OS, and if it identifies the infection, terminate Bebloh Trojan. We do not suggest manual Bebloh Trojan termination since it may be too difficult for the inexperienced user.
Quick Menu
Step 1. Uninstall Bebloh Trojan and related programs.
Remove Bebloh Trojan from Windows 8
Right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel choose Programs and Features and select to Uninstall a software.

Uninstall Bebloh Trojan from Windows 7
Click Start → Control Panel → Programs and Features → Uninstall a program.

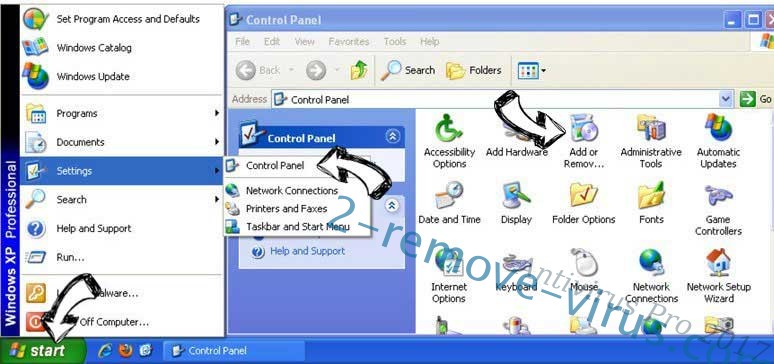
Delete Bebloh Trojan from Windows XP
Click Start → Settings → Control Panel. Locate and click → Add or Remove Programs.
Remove Bebloh Trojan from Mac OS X
Click Go button at the top left of the screen and select Applications. Select applications folder and look for Bebloh Trojan or any other suspicious software. Now right click on every of such entries and select Move to Trash, then right click the Trash icon and select Empty Trash.

Offers
Download Removal Toolto scan for Bebloh TrojanUse our recommended removal tool to scan for Bebloh Trojan. Trial version of provides detection of computer threats like Bebloh Trojan and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
