What is payfornature@india.com.crypted?
payfornature@india.com.crypted is a ransomware infection that is aimed at making money off of computer users by taking their files “hostage”. The way that the malicious program does that is by encrypting your files with the RSA-2048 key. Once your files are encoded, you cannot access them without a special decryption key. The cyber criminals urge you to buy this key from them for a price of 1.93 Bitcoins, which is about $872. It is clear that you cannot risk so much money on something that may not even result in your favor. You should delete payfornature@india.com.crypted ransomware as soon as you can.
How does payfornature@india.com.crypted work?
payfornature@india.com.crypted ransomware comes bundled with another program of the same type called Petya. The latter parasite requires administrative privileges in order to alter the master boot record. If it fails to gain these privileges, it fails to install the malware. Now, however, its developers have come up with a solution to their problem. This is where payfornature@india.com.crypted comes in. It does not need the administrative privileges to get installed. All the threat has to do is slither into your system. It usually does that by disguising itself as a PDF file, which is sent to you via an email that supposedly contains a job application.
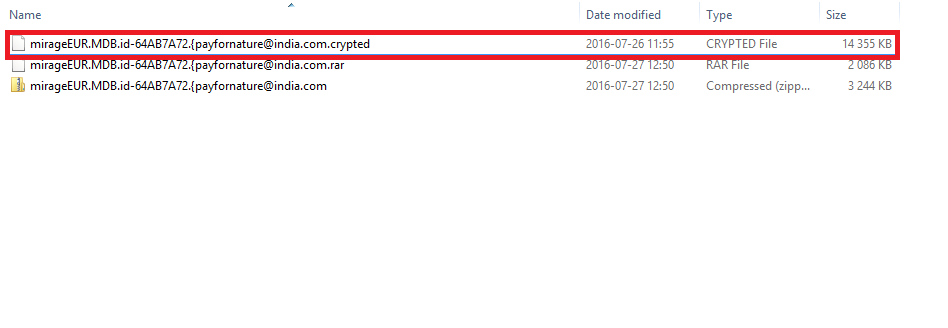
After the malicious software gets installed, it scans your PC for data files, encrypts them, and adds a 4 letter extension to their names. payfornature@india.com.crypted affects various file types including documents, databases, photos, videos, executable files, and more. Each folder containing encoded data will also contain ransom notes named “YOUR_FILES_ARE_ENCRYPTED”. If you open the file, you will be informed of the fact that you are dealing with payfornature@india.com.crypted Ransomware and that your files can only be restored by purchasing the special key. Although there is no decryptor created specifically for this parasite yet, we still urge you not to waste your money by paying the cyber crooks. We advise that you terminate payfornature@india.com.crypted ransomware right away.
How to remove payfornature@india.com.crypted?
The only safe way to erase payfornature@india.com.crypted from your computer is by using a malware prevention and removal tool. You can acquire the utility from our website. Once you download and install it, the software will scan your computer and detect all harmful components that it stores. It will then eliminate payfornature@india.com.crypted in its entirety and take care of other found issues. After payfornature@india.com.crypted ransomware removal is complete, you will be able to enjoy a clean PC and you will not have to worry about other Internet-based infections as the anti-malware tool comes with real-time online protection. As for your files, you can try recovering them with System Restore feature or by using one of the file decryptors you can find on the Web.
Offers
Download Removal Toolto scan for payfornature@india.com.cryptedUse our recommended removal tool to scan for payfornature@india.com.crypted. Trial version of provides detection of computer threats like payfornature@india.com.crypted and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
