About Anubis File Virus
Anubis File Virus is a new ransomware type of virus, named after the Egyptian god of the afterlife. Anubis File Virus is not different from other ransomwares and does not have any qualities that would set it apart from all the other ransomwares. It gets into your computer via spam emails, fake software updates or ads, and proceeds to encrypt your files. When that is done, victims will find a ransom note with instructions on what to do.
The hackers do not state how much money they want but you are supposed to use the email address provided to find out. We don’t recommend paying, however, whatever the amount is. Most hackers just ignore victims after payment has been made so do not waste your time. If you have backup, delete Anubis File Virus and then you can get your files back. Please note that you must remove Anubis File Virus first, otherwise the backup files might become unreadable as well.
How does Anubis File Virus spread?
Anubis File Virus spreads just like any other ransomware. It mostly uses spam email to infect computers because a lot of users still have the habit of opening malicious emails. What hackers do is attach an infected file to an email and send it to unsuspecting users. When someone opens the email and presses on the attachment, the ransomware downloads onto his/her computer. Those emails could look very official and hackers might use scare tactics to pressure users into opening the attachments. Do not fall for these tactics and if opening spam emails is something you must do, always double check the sender and the contents of the email. It’s better to take the time and be safe rather than potentially lose your files.
What does Anubis File Virus do?
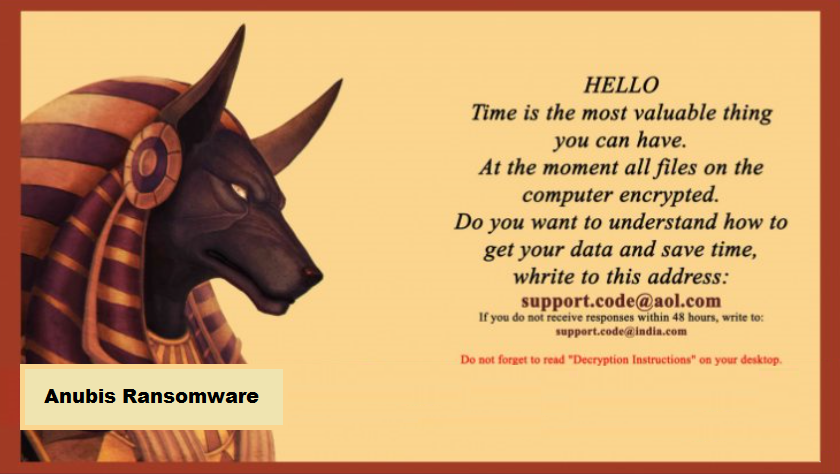
When Anubis File Virus downloads onto your computer, it will silently encrypt your files. When that is complete, a message will appear with a picture of Anubis and text, saying that time is important and in order to save time and get your data back, you need to contact them using support.code@aol.com. If there is no response in 48 hours, victims must contact them using a different email, support.code@india.com. If you contact them, which is not something we recommend, they will most likely try to sell you a decryption key. The price is not yet known but it should be between 0.5 to 2 Bitcoins. You should not contact them and completely ignore their demands, there’s little chance it will lead to file restoration. Instead what you should do is remove Anubis File Virus.
Anubis File Virus removal
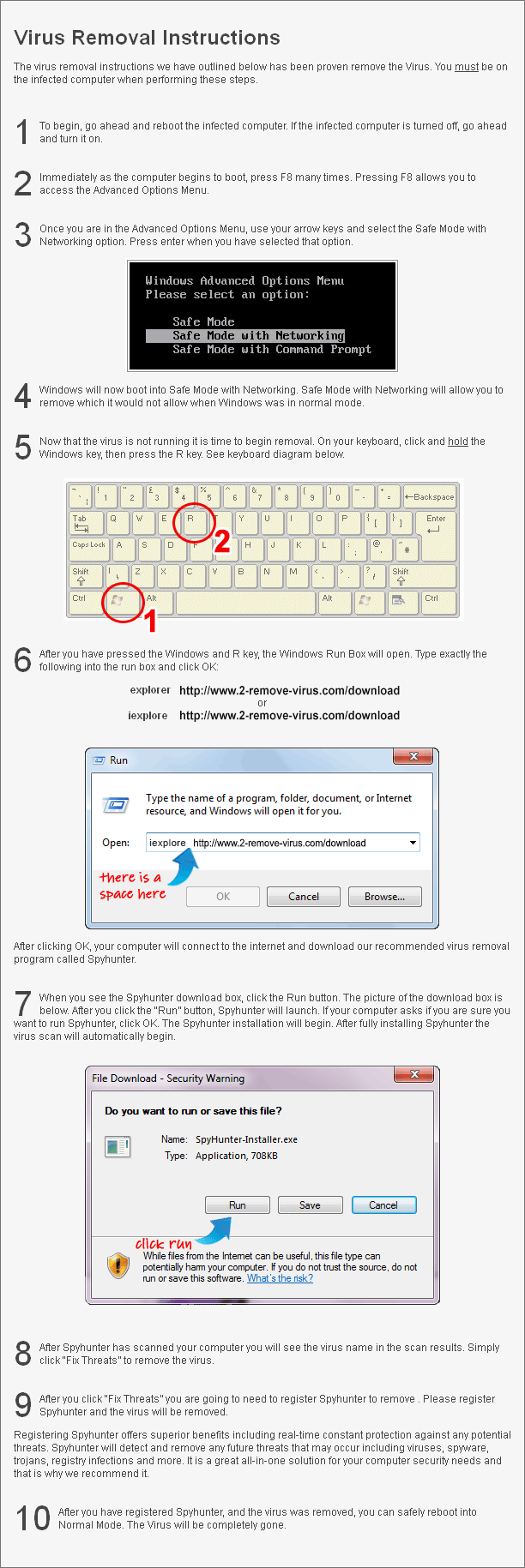
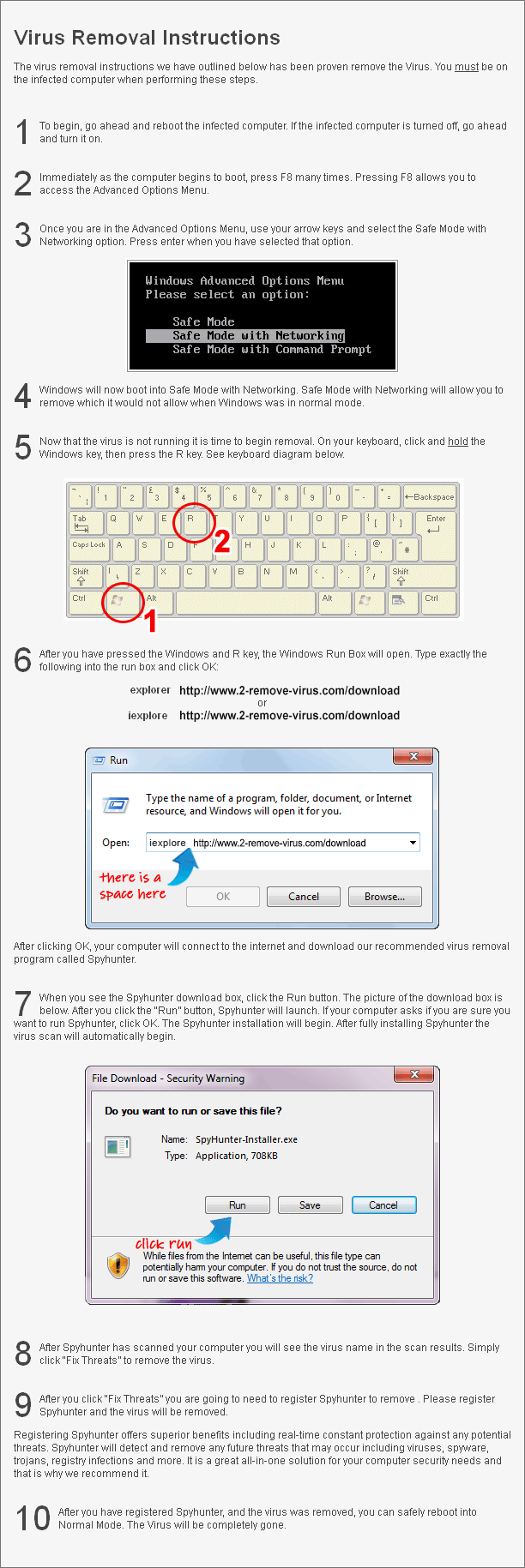
In order to delete Anubis File Virus, you will need anti-malware software. If you try to erase Anubis File Virus by hand, you could do serious harm to your computer. Instructions on how to go about Anubis File Virus removal will be provided below.
Offers
Download Removal Toolto scan for Anubis File VirusUse our recommended removal tool to scan for Anubis File Virus. Trial version of provides detection of computer threats like Anubis File Virus and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.