What do you need to know about Blankpage4.ru?
Blankpage4.ru is a questionable internet page that can definitely intrude your web surfing experience. Blankpage4.ru is listed as a browser hijacker, which is able to infiltrate all the most popular web browsers. Whether you are a Google Chrome, Mozilla Firefox or Internet Explorer user, Blankpage4.ru may find a way to modify their settings. Blankpage4.ru will change your homepage, default search engine, and new tab. All of them will lead you to Blankpage4.ru. More than that, you will soon notice an increased number of ads that will fill your computer with all kinds of irrelevant material.
Why Blankpage4.ru removal is necessary to ensure your PC’s security?
If you do not delete Blankpage4.ru soon, you may experience an identity theft. Blankpage4.ru gathers information about your web browsing activities that can be later used for the commercial purposes. For example, Blankpage4.ru may sell the gathered information to the third parties. It is also likely that Blankpage4.ru will fill your computer’s screen with various ads that are related to your recent searches. Therefore, you should not wait any longer and remove Blankpage4.ru infection before it gets to late and you have to deal with actual privacy violations. We have to mention that Blankpage4.ru infection does not reveal any information about its privacy policies. This means that Blankpage4.ru may do anything they want about the collected data.
On top of that, all of these ads can slow down your computer’s work. We have to also say that the unwanted applications can make your virtual machine more vulnerable to the other threats. You should uninstall Blankpage4.ru before even more questionable applications have found a way to your computer’s system. Our research specialists have prepared a detailed description that can help you remove Blankpage4.ru once and for all. Please make sure that you follow the given instructions attentively or the unwanted program may infiltrate your computer’s system again.
How did the browser hijacker find a way to my electronic device?
You will not be able to get Blankpage4.ru from its legitimate website. Hence, Blankpage4.ru gets to your computer with the help of freeware bundles. In the majority cases, free of charge applications come to your computer’s system together with other programs. In order to avoid these applications from entering your virtual machine, you should pay careful attention to the installation setup. Try to always check the ‘Advanced’ or ‘Custom’ settings because you can deselect the additional applications there.
How to delete Blankpage4.ru once and for all?
The best way to remove Blankpage4.ru browser hijacker is to implement a reliable malware removal tool. Also, make sure that you perform a full computer scan once the security application is installed. We have to mention that if you keep your security program up to date, the antivirus application will protect your virtual machine from the future threats as well.
Offers
Download Removal Toolto scan for Blankpage4.ruUse our recommended removal tool to scan for Blankpage4.ru. Trial version of provides detection of computer threats like Blankpage4.ru and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete Blankpage4.ru using Safe Mode with Networking.
Remove Blankpage4.ru from Windows 7/Windows Vista/Windows XP
- Click on Start and select Shutdown.
- Choose Restart and click OK.

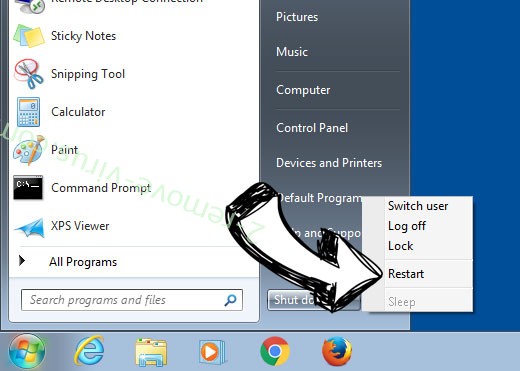
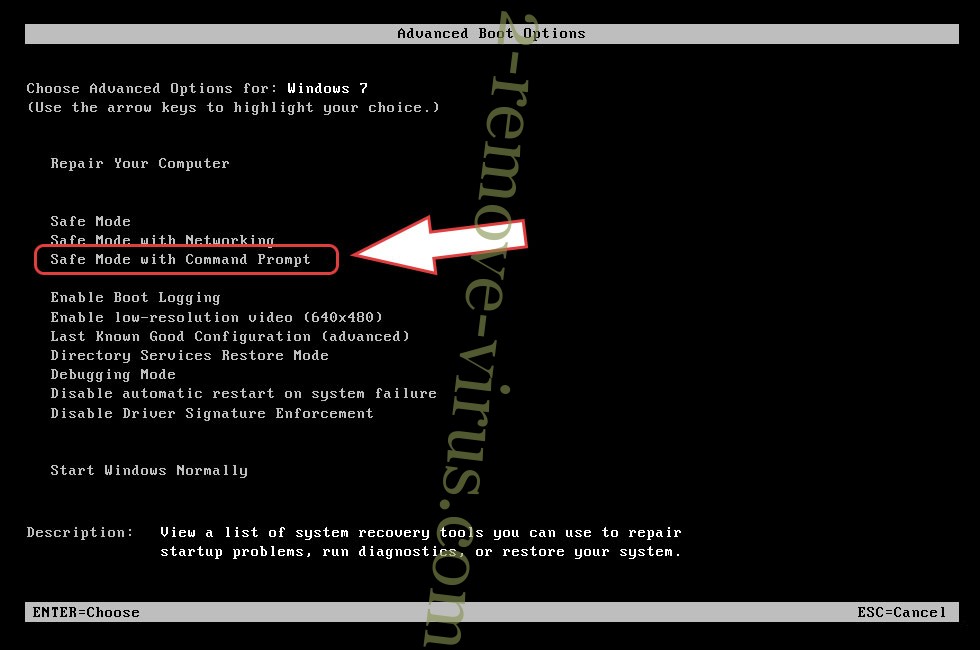
- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove Blankpage4.ru
Remove Blankpage4.ru from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.


- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

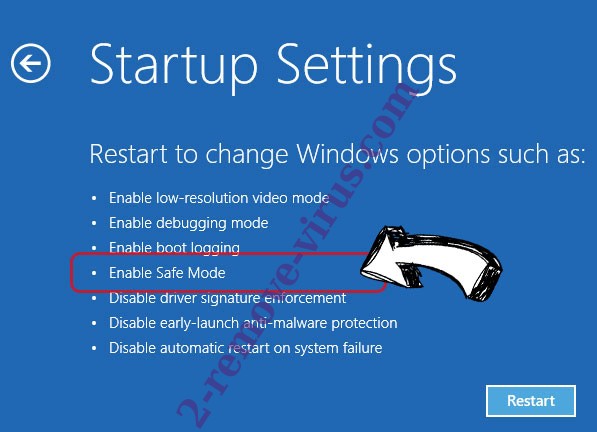
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete Blankpage4.ru
Step 2. Restore Your Files using System Restore
Delete Blankpage4.ru from Windows 7/Windows Vista/Windows XP
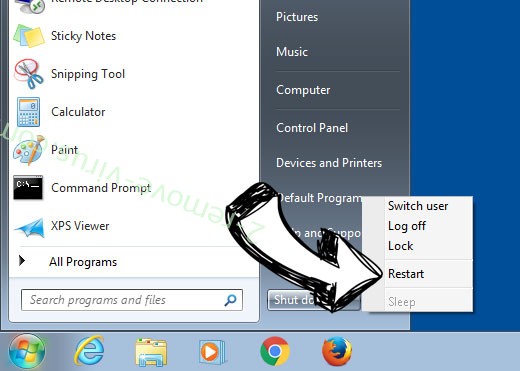
- Click Start and choose Shutdown.
- Select Restart and OK

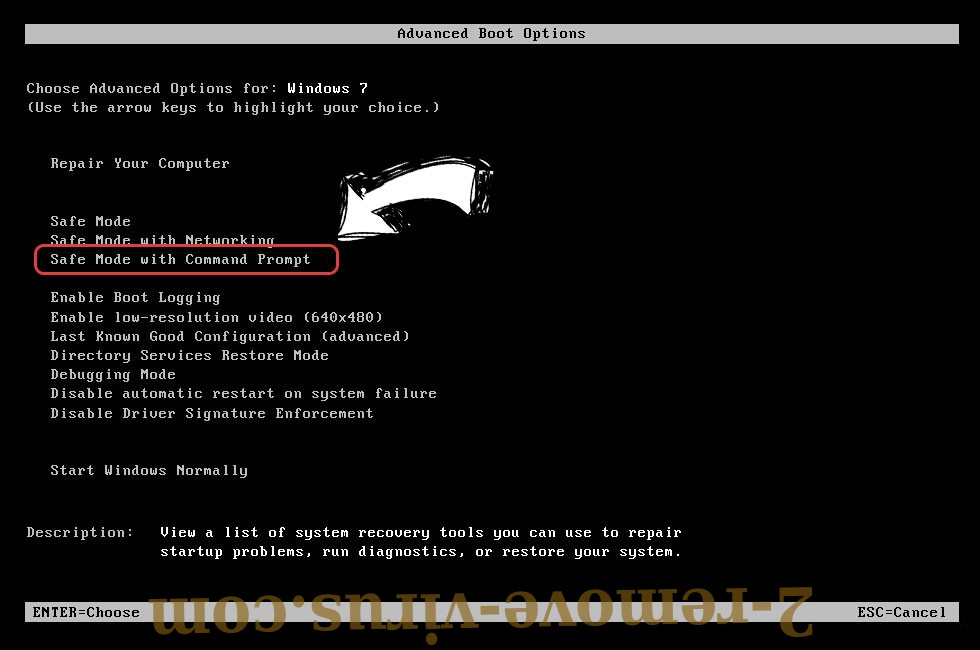
- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

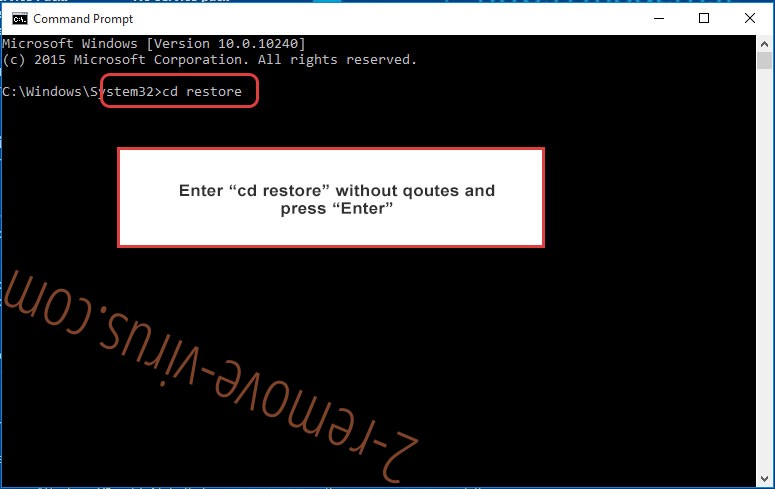
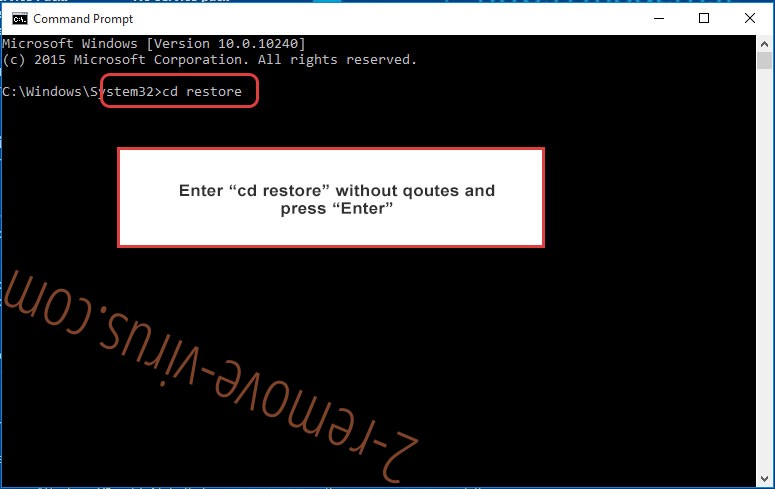
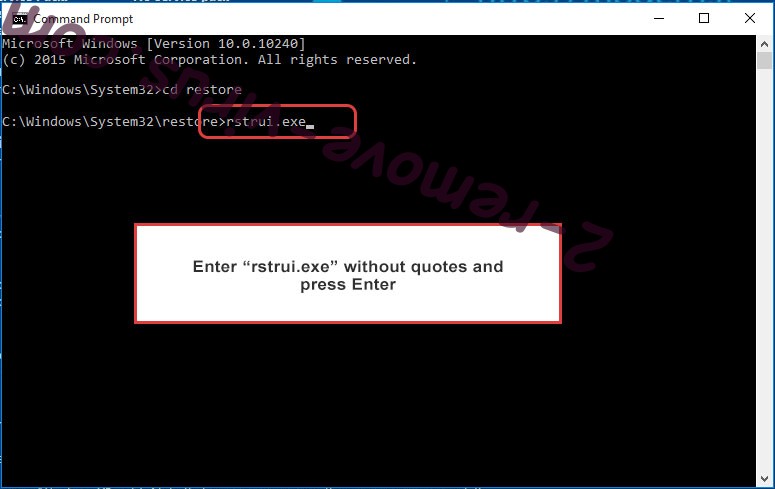
- Type in cd restore and tap Enter.

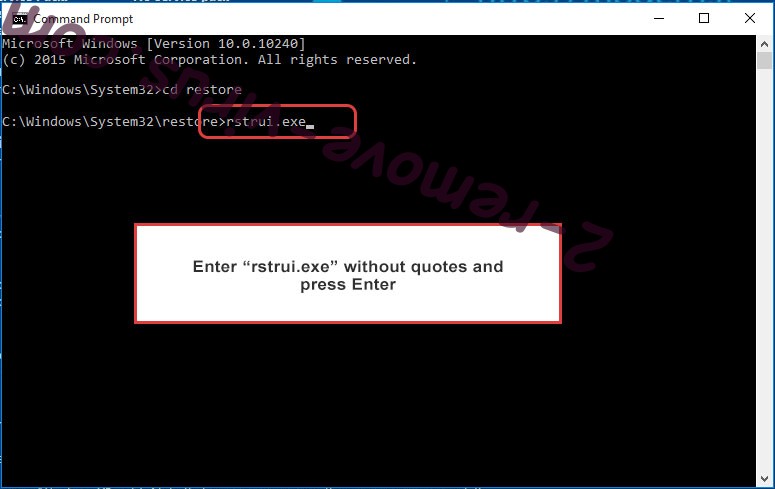
- Type in rstrui.exe and press Enter.

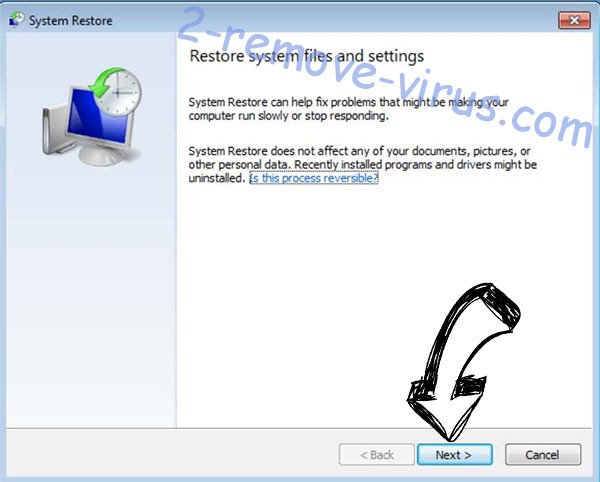
- Click Next in the new window and select the restore point prior to the infection.

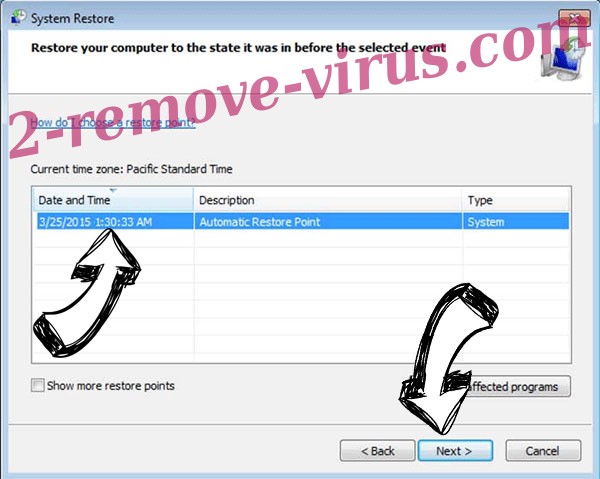
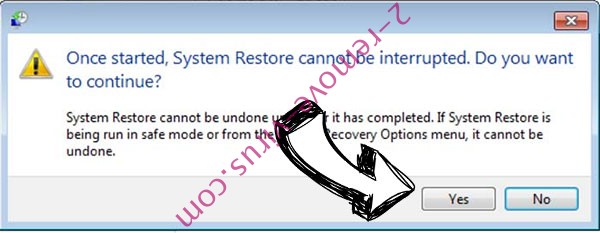
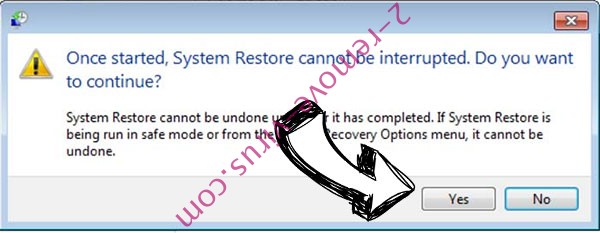
- Click Next again and click Yes to begin the system restore.

Delete Blankpage4.ru from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.


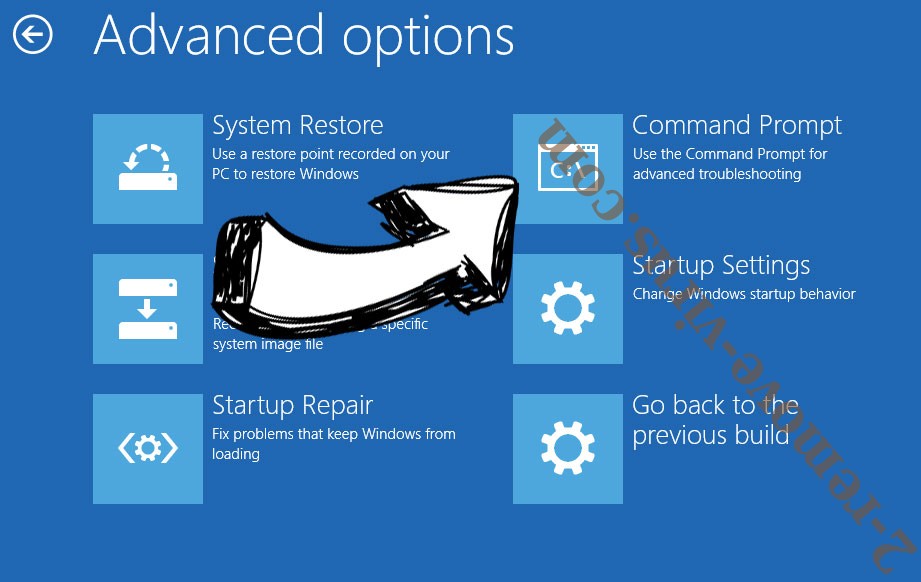
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

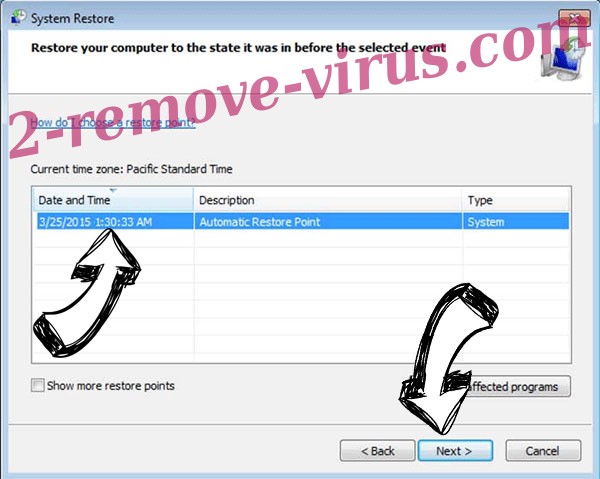
- Click Next and then click Yes to restore your system.

Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
