What is the .cerber infection?
.Cerber (also known as Cerber Ransomware) is an annoying application that can cause you many unwanted problems. .Cerber usually enters the computer users’ data machines with the help of questionable methods. .Cerber is classified as ransomware-type malware and you should definitely spend some time in order to eliminate the irritating infection. .Cerber works in a similar way as other malware infections, for instance, CryptoWall, CTB-Locker, TeslaCrypt, and Locky. All of the previously mentioned applications should be erased without hesitation. Our research team is going to help you remove .Cerber. You can find all the information about .Cerber removal at the very end of this article.
How does .Cerber virus work?
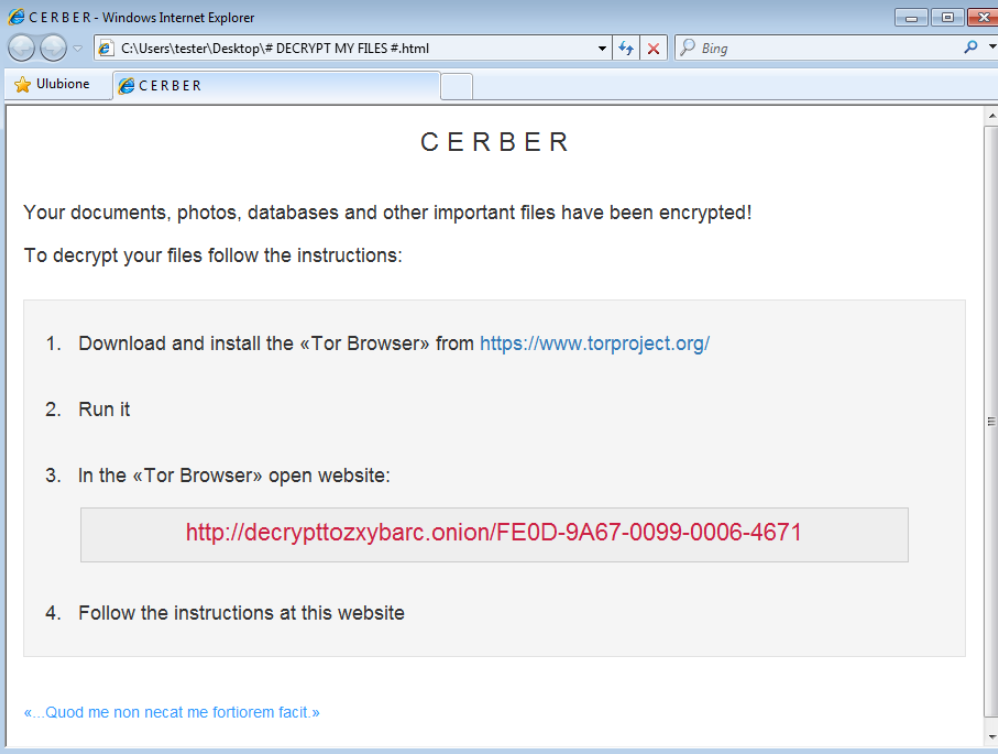
Once .Cerber infection finds your electronic device, the infection will encrypt all kinds of files in your computer’s system, for instance, .jpg, .doc, .raw, and others. To all of the encrypted documents .Cerber will add .Cerber extension. After these files are encrypted, .Cerber developers will ask for a ransom from you. They claim that the files will be decrypted, if you pay the required sum of money. You are supposed to pay the ransom as soon as possible. After seven days the ransom will double. However, we do not think you should pay at all. In the majority of cases ransomware creators do not decrypt the infected files. Thus, you should invest your money elsewhere. For instance, by getting a reputable malware removal tool that will protect your computer’s system from the similar threats in the future. Also, you should delete .Cerber virus as soon as possible. The infection can easily attract the attention of even more annoying threats.
How can I get my encrypted files back?
Unfortunately, there isn’t much that you can do in order to decrypt the files. .Cerber is a sneaky ransomware that does not care about your problems. .Cerber only wants you to pay the required sum in BitCoins. At the moment, there aren’t any tools that could help you decrypt the files. However, you could still get your files, if you restore the system from a backup. It is extremely important to keep the most needed documents in different electronic devices.
How to remove .Cerber from my computer’s system?
You should take .Cerber removal seriously and eliminate the virus as soon as possible. .Cerber will not bring any benefits to you or your virtual machine. On the contrary, you may soon find even more annoying applications on the computer.
The best possible option to remove .Cerber from your PC’s system is to implement a sophisticated malware removal tool. A powerful antivirus program will be able to detect and delete .Cerber. Once you install the antispyware application, you will need to perform a full computer scan. The security tool will be helpful in the future as well. If you keep your antivirus application up to date, you will not have to face such irritating problems ever again. In addition, do not forget to keep your important data in a different device as well. This is going to guarantee that your documents are safe.
Offers
Download Removal Toolto scan for .CerberUse our recommended removal tool to scan for .Cerber. Trial version of provides detection of computer threats like .Cerber and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete .Cerber using Safe Mode with Networking.
Remove .Cerber from Windows 7/Windows Vista/Windows XP
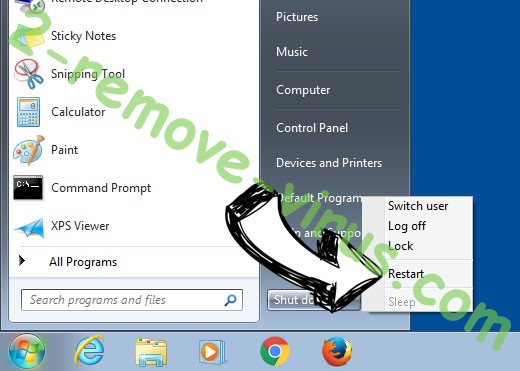
- Click on Start and select Shutdown.
- Choose Restart and click OK.

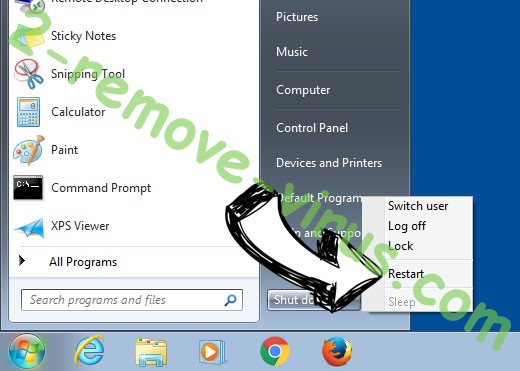
- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove .Cerber
Remove .Cerber from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.


- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

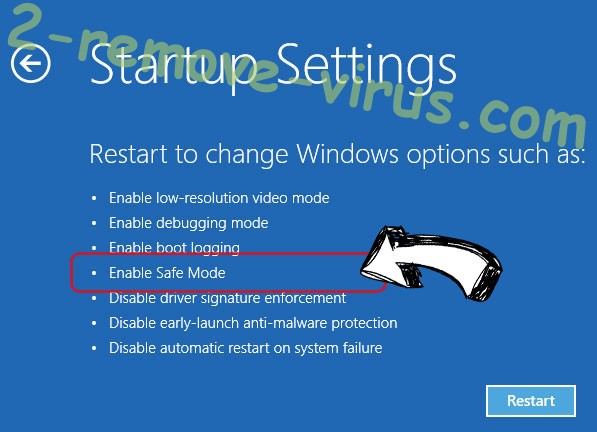
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete .Cerber
Step 2. Restore Your Files using System Restore
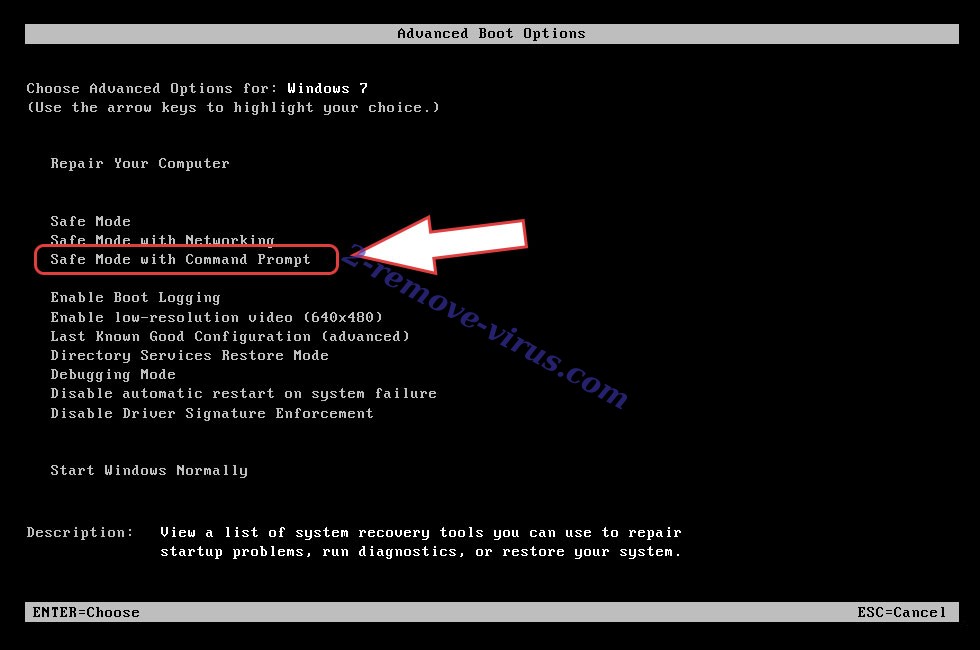
Delete .Cerber from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

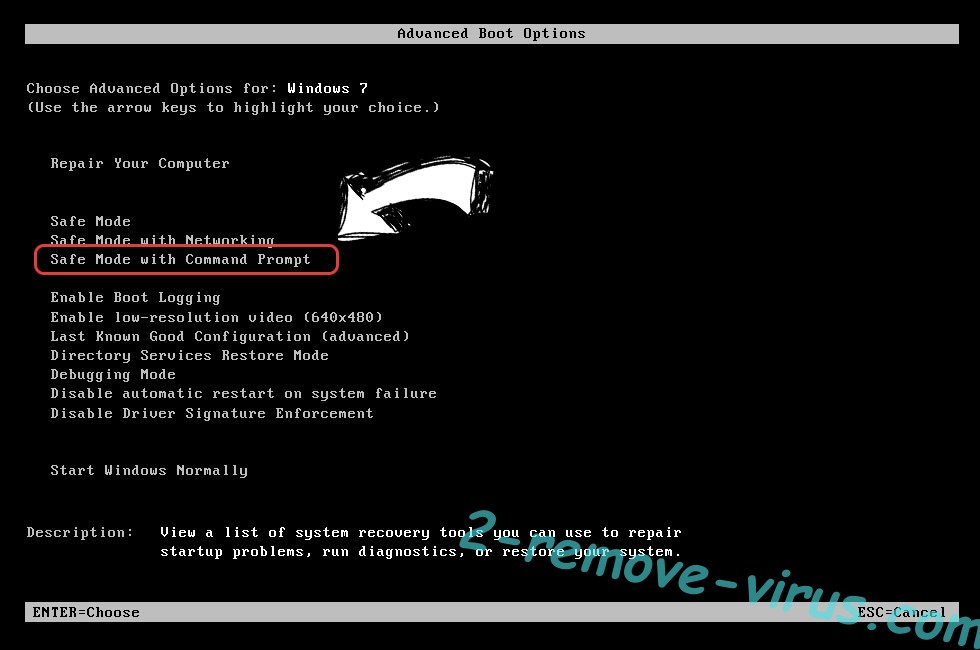
- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

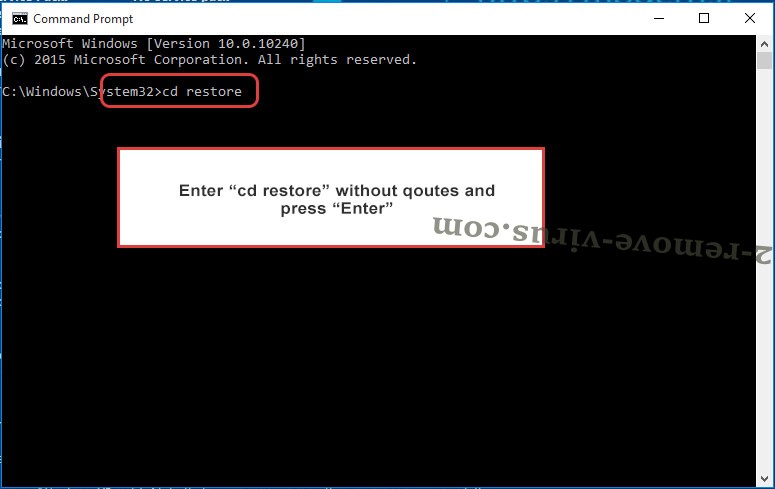
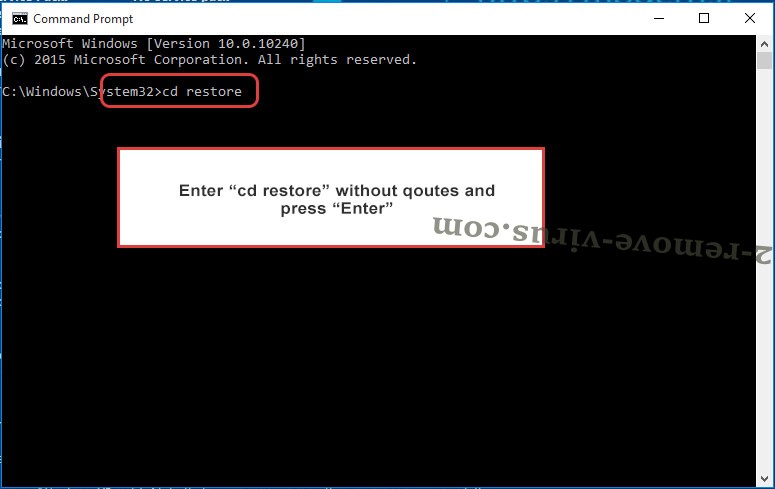
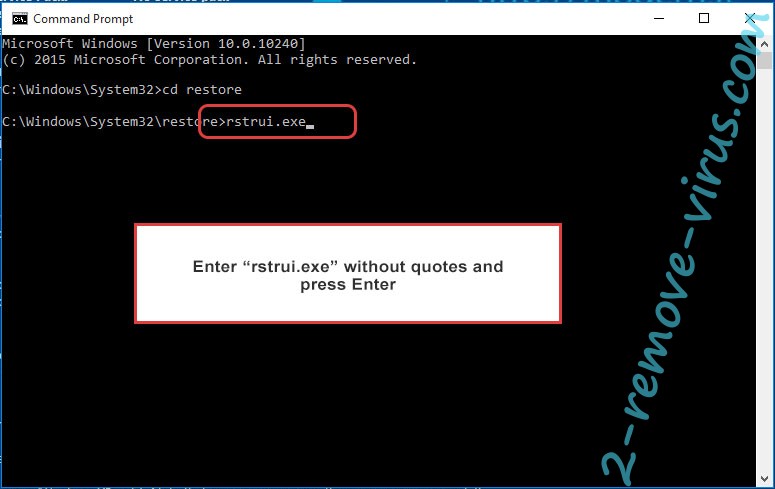
- Type in cd restore and tap Enter.

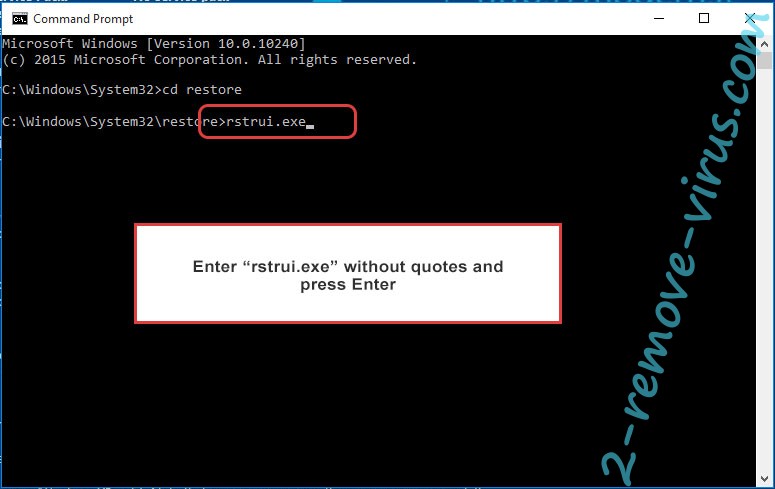
- Type in rstrui.exe and press Enter.

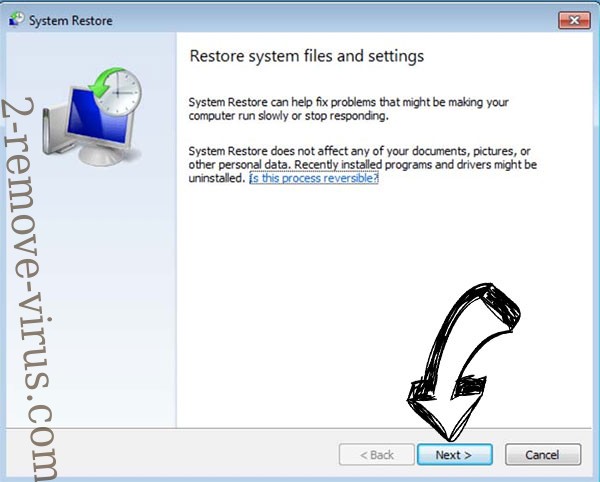
- Click Next in the new window and select the restore point prior to the infection.

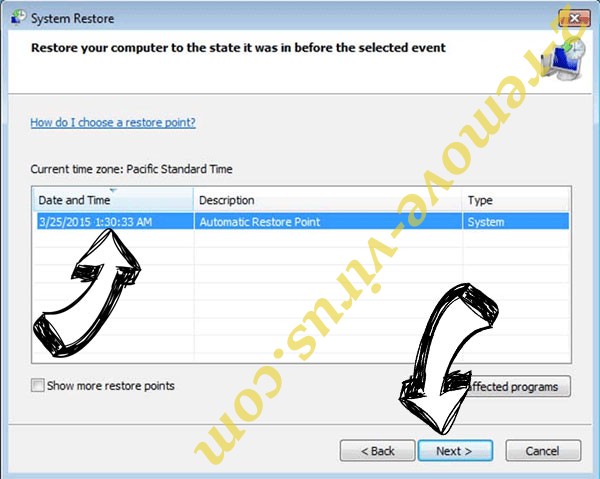
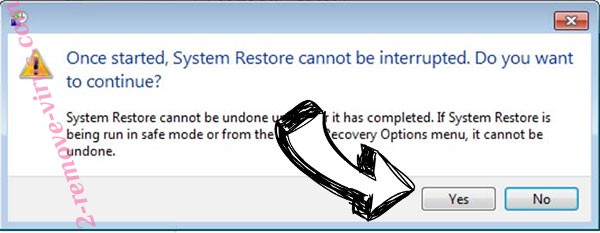
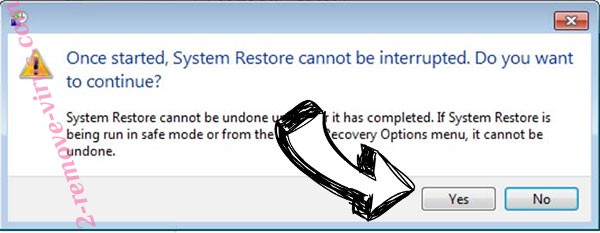
- Click Next again and click Yes to begin the system restore.

Delete .Cerber from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.


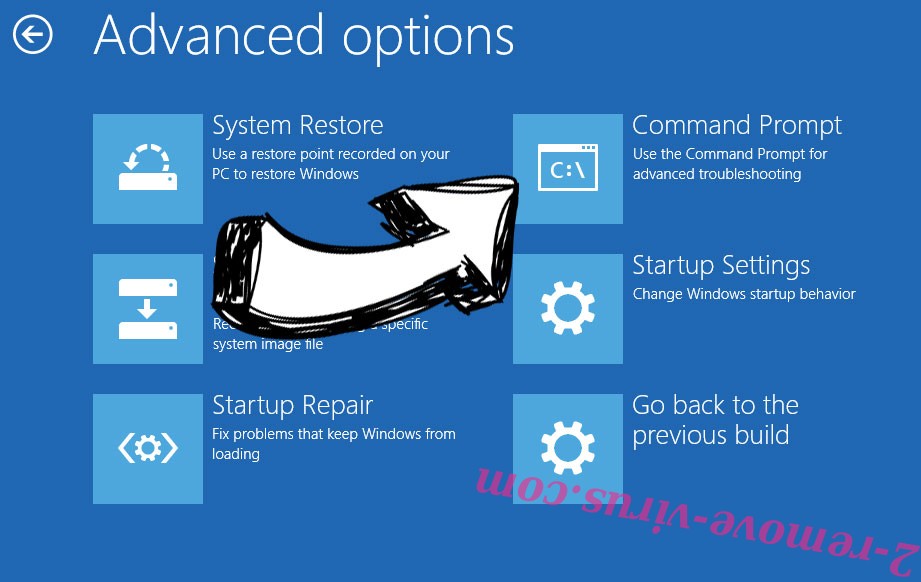
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

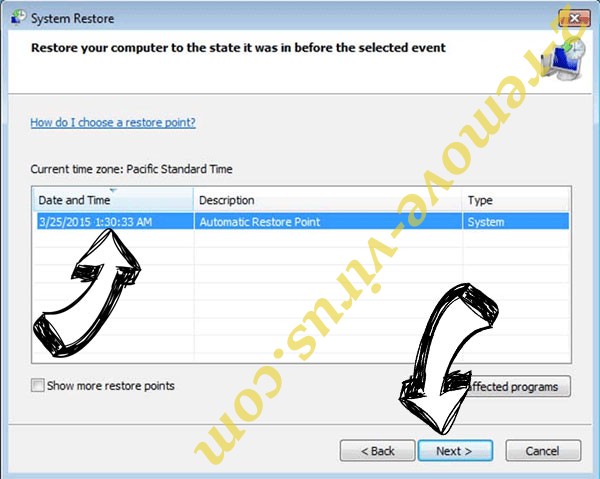
- Click Next and then click Yes to restore your system.

Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
