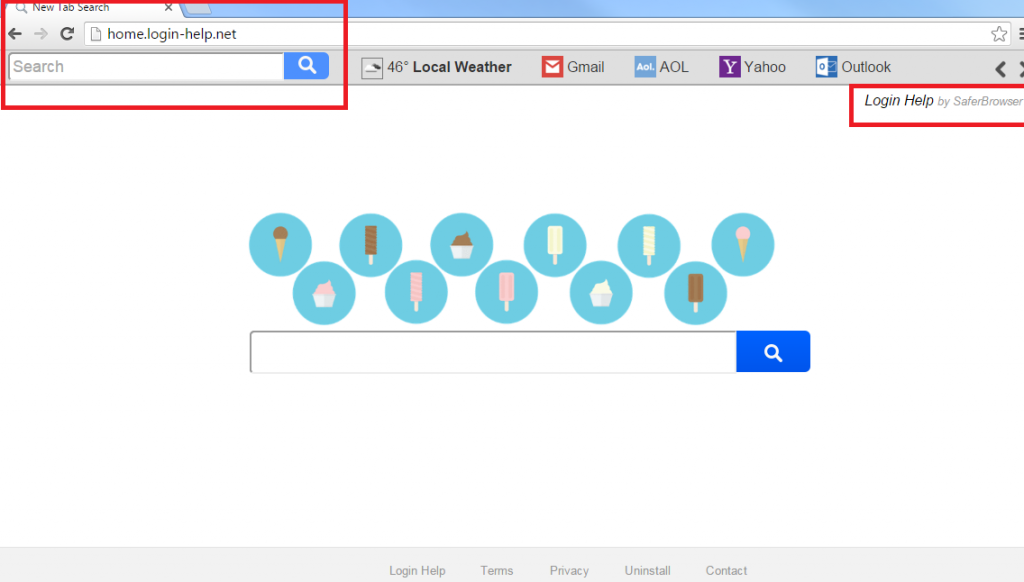
Home.login-help.net Removal Tips
Have you noticed that Home.login-help.net has taken over your browser? In that case, there is a browser hijacker on your personal computer. Having sneaked into the system without your notice, this suspicious PUP (potentially unwanted program) is ready to make your browsing experience worse than ever. The application should not be there in the first place, so you (without a doubt) have to remove Home.login-help.net the moment you can!
The useless program often usurps all the browsers present in your PC system because it was created to be compatible with all sorts of browsers, ranging from the most popular ones to less-known ones. Google Chrome, Mozilla Firefox, Internet Explorer, Safari, Opera – all of them can become the victims of the potentially unwanted program. Once the browser is attacked, the settings are disturbingly modified. It means that the home page, default search provider, and new tab will differ from what you used to have. These options will be replaced by the hijacker and, unless you delete Home.login-help.net, will stay like this forever.
Why is Home.login-help.net dangerous?
Our security experts understand that the PUP does not resemble a virus in any way, mainly because it is not classified as one. It has a nice interface with an image and a search bar on it, so no wonder that many people do not think of it as a threat. However, as a search engine, it has some disadvantages: there are only two options for browsing, Web and Images. If you try actually using the hijacker, you will notice something. The search results are not something that should be trusted. Unlike the results of, for example, google.com, the results of the PUP contain some dangerous sponsored links that are placed at the top of the page by unknown third parties. The links can redirect the user to websites that are used to spread viruses. Moreover, the application displays advertisements that can also lead you to unwanted infections. Lastly, do not forget that potentially unwanted programs gather their users’ data. In other words, your non-personal info is most likely collected and, probably, sold to criminals.
How did my PC get attacked by Home.login-help.net?
After you uninstall Home.login-help.net, take care of your online safety. The browser hijacker definitely travels with free software. This software (known as freeware) is downloaded from P2P pages. Unless you pick the Advanced or Custom installation option, you have the possibility of various infections, and that is why our team recommends you to avoid suspicious websites.
How to remove Home.login-help.net from the computer?
Home.login-help.net removal is an urgent thing to do. You can erase Home.login-help.net with a reliable anti-malware and anti-spyware application that will also investigate your PC for more threats and eliminate them. However, if you think that you will be able to delete the program on your own, you can try these instructions that we have prepared:
Delete Home.login-help.net from your browser
Remove Home.login-help.net from Mozilla Firefox
1. Tap Alt+H and choose Troubleshooting Information.
2. Press Refresh Firefox.
3. Once more, click Refresh Firefox.
Uninstall Home.login-help.net from Internet Explorer
1. Press Alt+T and select Internet Options.
2. Under the Advanced tab, press Reset.
3. Select the checkbox.
4. Press Reset.
5. Hit Close.
Terminate Home.login-help.net from Google Chrome
1. Tap Alt+F and navigate to Settings.
2. Click Show advanced settings.
3. Press Reset settings.
4. Press Reset.
Offers
Download Removal Toolto scan for Home.login-help.netUse our recommended removal tool to scan for Home.login-help.net. Trial version of provides detection of computer threats like Home.login-help.net and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
