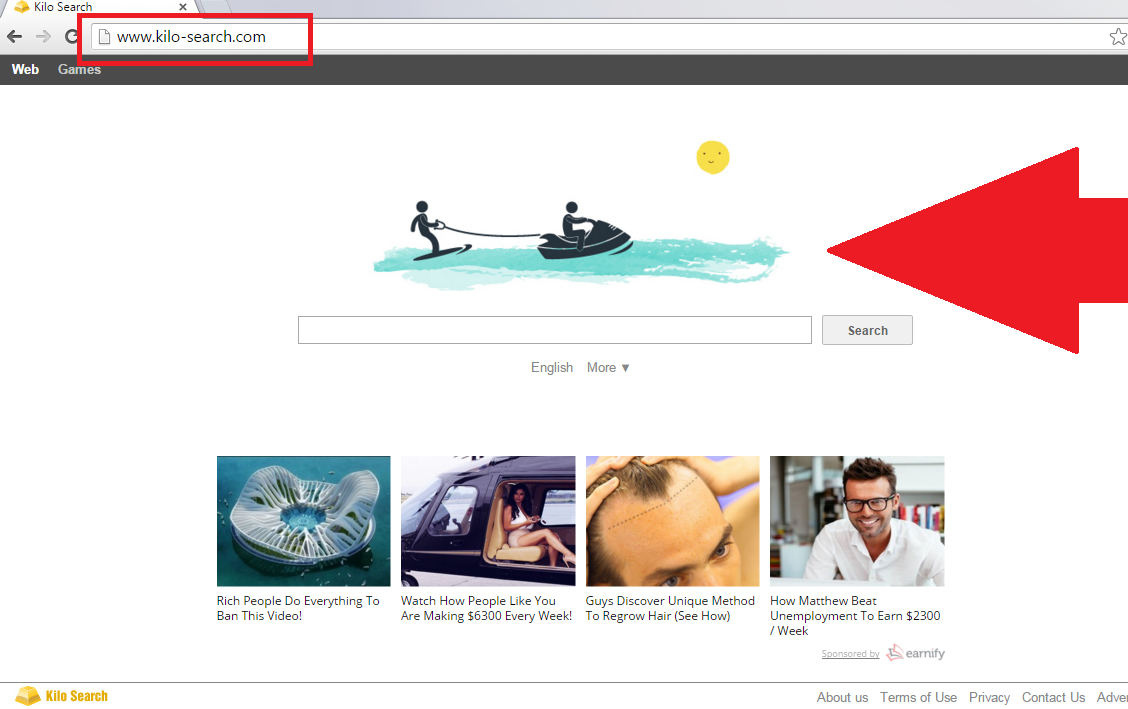
Kilo-search.com Removal Guide
You need to know that Kilo-search.com is listed as a browser hijacker. The hijackers are very prevalent threats that often enter systems without permission. At first sight, it seems that Kilo-search.com is a decent search engine. However, you should not be tricked because Kilo-search.com changes the settings of Internet browsers (e.g. Internet Explorer, Google Chrome, and Mozilla Firefox) without permission.
As it has an ability to modify the settings without a user’s consent, Kilo-search.com falls into the category of browser hijackers. The infection will change your default search provider and homepage in order to make you enter as many ads as possible. Keeping the Kilo-search.com browser hijacker installed might result in various security-related problems, so we suggest that you remove Kilo-search.com when you have a chance. Make sure that you do not postpone Kilo-search.com removal because this infection will definitely act behind your back.
Why is it so risky to keep Kilo-search.com in your virtual machine?
There are a couple of reasons why Kilo-search.com deserves elimination. For example, researchers who have tested this browser hijacker say that Kilo-search.com might act as a backdoor. In other words, other infections might slither onto your computer with the program’s help. In addition, it has been observed that Kilo-search.com infection might insert third-party ads into the search results. It means that you might simply infect your system with serious malware by searching for the information using the search box installed on the hijacker’s startup page. Furthermore, your search queries might be recorded. This is mainly done in order to find out more information about you and thus later on to provide you with targeted ads. By saying “targeted”, we mean that they are based on your interests, i.e. the information a browser hijacker has collected about you. In order to perform its activities, Kilo-search.com browser hijacker might install additional extensions. You will find them in the list of add-ons on your browsers. They will disappear after you delete Kilo-search.com browser from your computer. We will provide you more info on Kilo-search.com removal further in the article.
Our research team wants to emphasize that it might be really dangerous to click on those third-party ads that will be inserted among your search results. This happens because advertisements promoted by Kilo-search.com are not trustworthy. It is unclear where the commercial content is going to redirect you. Of course, some of these ads might lead you to decent websites, but others might take you to the web pages run by cyber criminals. If your virtual safety is important for you, uninstall Kilo-search.com as fast as you can.
How did the annoying Kilo-search.com application enter my computer’s system?
It is not surprising that Kilo-search.com is distributed in the same way as other browsers hijackers , i.e. the Kilo-search.com infection enters PC systems in software bundles. More than that, this browser hijacker does not travel alone. It is known that Kilo-search.com is often bundled with adware, potentially unwanted programs, and other threats, which means that it is not enough to only remove Kilo-search.com. As you can see, even though the Kilo-search.com infection does not seem to be a serious threat at first sight, the hijacker can still cause harm to your computer.
How to delete Kilo-search.com quickly and efficiently?
You will find the instructions that will help you to eliminate Kilo-search.com browser hijacker below this article. Of course, if you do not want to erase it manually, you can get rid of Kilo-search.com automatically. It is worth downloading a security application because you will have to scan your system only once to erase all the existing threats, including those that have entered your system together with Kilo-search.com, from your computer. Remember that only trustworthy security applications are effective and can help you to prevent malware from entering the system.
Terminate Kilo-search.com from your PC:
Windows XP
1. Click the Start button and select Control Panel.
2. Click Add or Remove Programs.
3. Select the program and click Remove.
Windows 7 and Windows Vista
1. Open the Start menu and select Control Panel.
2. Click Uninstall a program.
3. Right-click on the undesirable application.
4. Click Uninstall.
Windows 8
1. Tap the Windows key and type Control Panel.
2. Click on the icon of Control Panel to open it.
3. Go to Uninstall a program.
4. Select the unwanted software and click Uninstall.
Internet Explorer
1. Launch your browser and tap Alt+T.
2. Select Manage Add-ons and open Toolbars and Extensions.
3. Select the extension and erase it.
Google Chrome
1. Open your browser.
2. Select Tools from the menu.
3. Go to Extensions.
4. Find the undesirable extension and select it.
5. Click the trash button.
Mozilla Firefox
1. Open your browser.
2. Tap Ctrl+Shift+A simultaneously.
3. Click Extensions.
4. Find the untrustworthy extension and eliminate it.
Offers
Download Removal Toolto scan for Kilo-search.comUse our recommended removal tool to scan for Kilo-search.com. Trial version of provides detection of computer threats like Kilo-search.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.