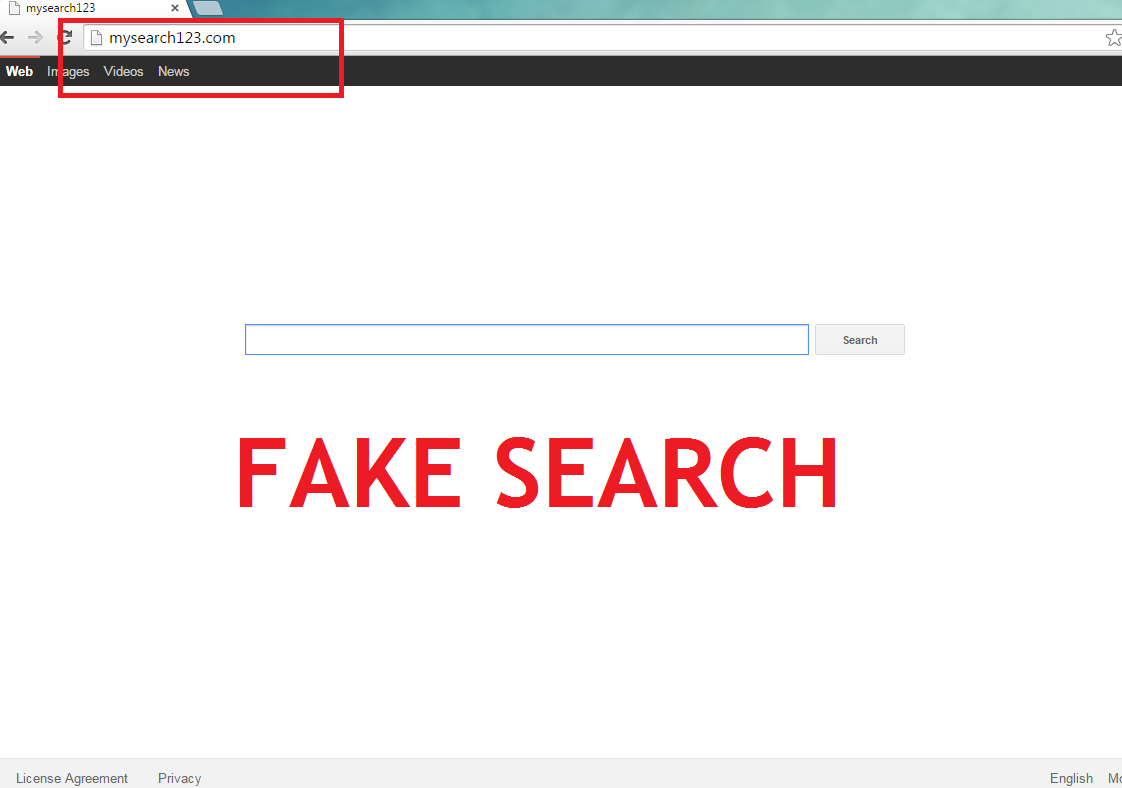
Mysearch123.com Removal Tips
Mysearch123.com is a browser hijacker developed to alter your settings and to direct traffic to pages which belong to the promoted third parties. Since the creators of this application know very well that most of the users do not follow freeware installation procedures, they successfully distribute their product bundling it with free programs.
As soon as the application infiltrates your computer, it will immediately start its nefarious activities. Because the hijacker is compatible with all major browsers, you will not be able to avoid it unless you delete Mysearch123.com.
What does Mysearch123.com do?
The intruder alters the home page and default search engine in your Google Chrome, Mozilla Firefox, and Internet Explorer. Since hijacker’s main aim is to increase the rankings of the affiliate pages, you can be sure that Mysearch123.com will present you with predetermined links in your search results. Since browser hijackers are often associated with suspicious or even malciosu software, after clicking such link, you may end up in a malicious website. We warn you that if you encounter cyber crooks, you will probably get your system infected with some form of malware which may cause much more serious damage than this hijacker. Instead of risking your computer’s safety this way, you should remove Mysearch123.com.
In addition to the constant threat of malware infection, you will also be annoyed by numerous pop-ups, banners, etc. Furthermore, you will notice that your computer became much slower and your Internet connection lost its speed. The only way to fix these problems is to terminate Mysearch123.com.
How did Mysearch123.com enter your PC?
In most cases such software infiltrates a new system using a deceptive marketing method called ‘bundling’. While this distribution method is widely used, you should know that it works only if the users do not pay any attention to freeware installation process. If you wish to keep your computer safe, we advise to always choose Custom or Advanced installation option and read the End User License Agreement. These actions will allow you to monitor every step of the procedure and to deselect the unwanted applications.
How to remove Mysearch123.com?
The users who look for a way to eliminate Mysearch123.com, should try to employ an up-to-date computer security software and scan their computer. A trustworthy and powerful anti-spyware will be able to remove Mysearch123.com and to protect your computer in the future. Another option is to follow the instructions on how to erase Mysearch123.com presented under this report. Whichever way you choose to deal with this issue, do not let this hijacker stay in your computer for another minute.
Terminate Mysearch123.com
Windows 8
1. Tap the Windows key + X and go to Control Panel.
2. Click Uninstall a program and choose an application you wish to get rid of.
3. Press Uninstall to delete Mysearch123.com.
Windows 7 and Windows Vista
1. Open the Start menu and select Control Panel.
2. Click Uninstall a program and uninstall Mysearch123.com.
Windows XP
1. Access the Start menu and move to Control Panel.
2. Click Add or Remove Programs and pick the suspicious software.
3. Remove Mysearch123.com from your PC.
Eliminate Mysearch123.com from your browsers
Internet Explorer
1. Press the Gear icon and choose Internet Options.
2. In the General tab, overwrite your home page.
3. Tap the Gear icon one more time and open Manage Add-ons.
4. Go to Toolbars and Extensions and erase the unwanted add-ons.
5. Access Search Providers and change/remove your search engine.
Mozilla Firefox
1. Open the menu and choose Options.
2. Go to General tab and replace your current home page with another one.
3. Pick Search tab and change/remove your search provider.
4. Go to the menu again and open Add-ons.
5. Erase the unwanted extensions.
Google Chrome
1. Choose the menu icon and open Settings.
2. Click Set pages and overwrite your home page.
3. Under Search, select Manage search engine.
4. Change/remove your search provider.
5. In the Extensions, remove useless add-ons.
Offers
Download Removal Toolto scan for Mysearch123.comUse our recommended removal tool to scan for Mysearch123.com. Trial version of provides detection of computer threats like Mysearch123.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
