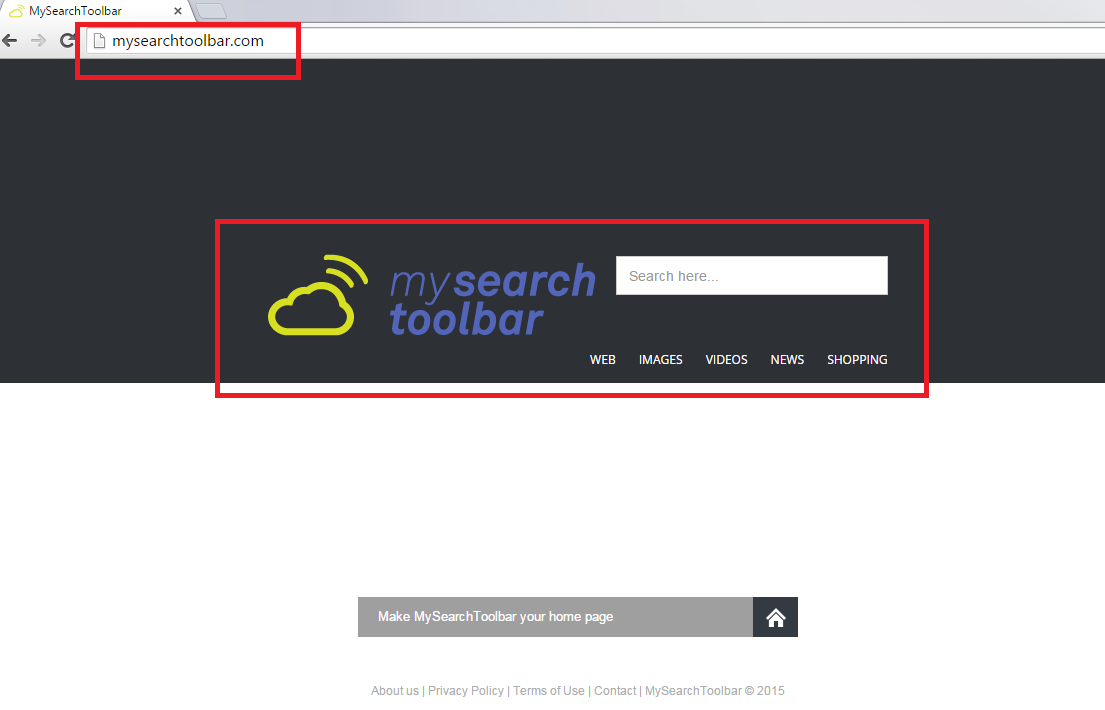
Mysearchtoolbar.com Removal Guide
Mysearchtoolbar.com is classified as a browser hijacker. This means that the application will modify your start-up page and default search provider without even bothering to ask whether you agree with such changes.
Mysearchtoolbar.com also promotes webites. This is how Mysearchtoolbar.com program’s owners gain money. For this very reason the hijacker is not reliable. There are no guaranties that the promoted web pages will be reputable. On the contrary, we do not recommend to use Mysearchtoolbar.com services. The search engine is most probably infiltrated with ads that can lead you to the dark side of the Internet.
By reading this article further you can learn even more reasons why Mysearchtoolbar.com infection deserves removal. More than that, we will tell you how to take care of Mysearchtoolbar.com removal quickly and effectively. If you follow the instructions carefully, you will be able to not only delete Mysearchtoolbar.com but also protect your PC from the future infections.
Why do I need to remove Mysearchtoolbar.com from my computer’s system?
Mysearchtoolbar.com has an official website; however, you will not be able to download the program from there. This means that the hijacker has to apply suspicious methods in order to reach the users’ computers. For instance, Mysearchtoolbar.com may find your virtual machine via bundled malicious installers. If you have found the hijacker in the computer out of nowhere, you need to uninstall Mysearchtoolbar.com infection immediately.
The hijacker’s elimination is especially important because you may experience an identity theft, if you keep Mysearchtoolbar.com in your PC. The infection gathers information about your online preferences. The collected data may be later shared with other parties: “Companies which advertise on our site may collect information from you if you click on their advertisements or access their sites. They may do this by using cookies”. Hence, this is one of the ways how third parties may reach your sensitive data. The only way to protect your personal information is to get rid of Mysearchtoolbar.com right away.
What is the best way to delete Mysearchtoolbar.com infection from my electronic device?
Mysearchtoolbar.com removal might be considered as a time consuming process. However, it is extremely important that you erase the hijacker once and for all. You can do that either manually or automatically. Our research team prefers the automatic removal technique because it is a much easier elimination method. You will only need to invest in a reliable anti-virus program that will make sure that there are no threats left in your virtual machine. Please do not forget to conduct a full system scan after the malware removal tool’s installation. You can also remove Mysearchtoolbar.com manually by following the termination guide bellow this report. Try not to skip any of the removal steps because the hijacker will use every your computer’s vulnerability in order to stay in the PC.
Terminate Mysearchtoolbar.com from Google Chrome
1. Open your Google Chrome.
2. Simultaneously press Alt+F.
3. Go to Tools.
4. Select Extensions.
5. Choose the recycle bin icon and then select Remove.
Eliminate Mysearchtoolbar.com from Internet Explorer
1. Launch the Internet browser.
2. Tap Alt+T.
3. Select Manage Add-ons.
4. Move to Toolbars and Extensions.
5. Remove the annoying application.
6. Click Close.
Erase Mysearchtoolbar.com from Mozilla Firefox
1. Open Mozilla Firefox.
2. Press Ctrl+Shift+A.
3. Select Extensions.
4. Remove the undesirable add-on.
Windows 8 and Windows 8.1
1. Access the Charm bar by locating the cursor to the bottom right corner of your screen.
2. Select Settings and then choose Control Panel.
3. Find Programs and Features.
4. Choose the unwanted program and remove the plug-in.
Windows 7 and Vista
1. Access the Start menu.
2. Open Control Panel and then go to Programs and Features.
3. Pick the program you want to remove.
4. Select Uninstall/Change.
Windows XP
1. Go to the Start menu.
2. Open Control Panel and then access Add or Remove Programs.
3. Choose the application you want to delete.
4. Click Remove.
Offers
Download Removal Toolto scan for Mysearchtoolbar.comUse our recommended removal tool to scan for Mysearchtoolbar.com. Trial version of provides detection of computer threats like Mysearchtoolbar.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
