Petya Ransomware Removal Tips
Petya Ransomware is an extremely dangerous infection that aims at extorting money from you. Like other ransomware programs, it slithers into your PC surreptitiously and encrypts your important data. The threat then demands that you pay a ransom for your files. The payment usually has to be made in Bitcoins within a certain amount of time.
If you do not make the payment, the cyber crooks threaten to destroy the decryption key for good. This is how CryptoWall, TeslaCrypt, Chimera, CryptoLocker, and other malicious applications that fall into this category function. Petya Ransomware, however, differs from them in several ways, which are discussed below. The only thing that remains the same is that you need to get rid of the parasite. This article will help you terminate Petya Ransomware and restore your files without wasting your money.
 How does Petya Ransomware work?
How does Petya Ransomware work?
Petya Ransomware usually gets distributed through spam emails with malicious attachments disguised as Dropbox download links. When you download and execute the file, your computer gets infected by the harmful application. The main difference of this ransomware from others is that it encrypts hard drive portions instead of separate files. The infection replaces the Master Boot Record with a malign loader and restarts your computer. Once the PC is rebooted, the malign loader gets executed and starts the encryption process.
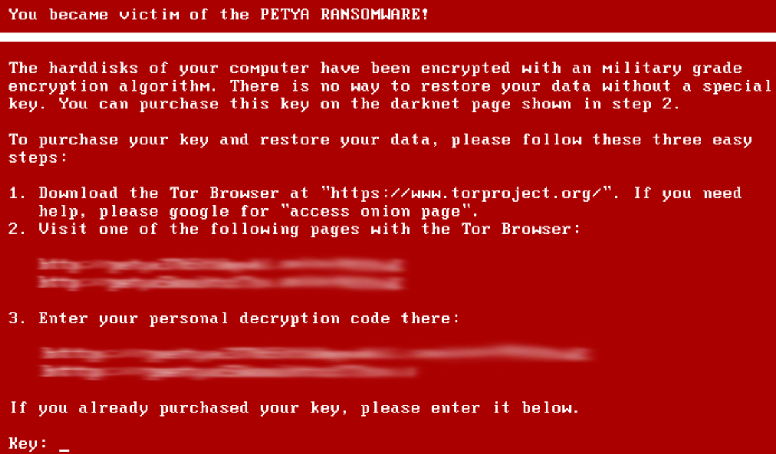
During encryption, the malicious program shows you a fake check disk screen, and once it completes this process, you will no longer be able to access your files. In fact, you will no longer be able to even load Windows, because the parasite will corrupt the Master File Table. Instead, you will be presented with a ransom note, which will inform you of the fact that you computer has been encrypted and that in order to decrypt it you need to make a payment. You will be urged to download the Tor browser and visit a certain page, which will contain detailed instructions of how to make that payment. Needless to say, that is not something you should do. What you should do is delete Petya Ransomware from your computer.
How to remove Petya Ransomware?
Petya Ransomware removal is not that complicated as all you need to do is implement an anti-malware utility in order to complete it. The malware remover will perform a full system scan, detect all malign components of the harmful application, and eliminate Petya Ransomware along with other threats that may be present in your system. Before you remove Petya Ransomware, however, you should restore your data files by using a tool that was developed specifically for this purpose. This process is quite complicated, which is why we have prepared detailed instructions below the article. Once you complete it and load your PC, you will be able to download the anti-malware utility from our page and use it to delete Petya Ransomware leftovers and other threats. Moreover, the security software will also keep your system safeguarded from now on.
Uninstall Petya Ransomware Decryption
- Disconnect your hard drive with encrypted files and connect it to another PC
- Download the Petya Sector Extractor by Fabian Wosar and save it to your desktop
- Launch PetyaExtractor.exe (it will detect the drive and select it automatically)
- Open your browser and go to https://petya-pay-no-ransom.herokuapp.com or https://petya-pay-no-ransom-mirror1.herokuapp.com
- In Petya Extractor program, click Copy Sector and paste it in the Base64 encoded 512 bytes verification data field on the opened website
- Go back to the program and now click Copy Nonce button
- Return to the website again and paste it to Base64 encoded 8 bytes nonce field
- Click Submit and wait for the password to appear
- Write down the password
- Connect the HDD back to the original computer
- When the Petya Ransomware screen appears, enter the password
- After your files get decrypted, download the powerful anti-malware tool and clean your system
Offers
Download Removal Toolto scan for Petya RansomwareUse our recommended removal tool to scan for Petya Ransomware. Trial version of provides detection of computer threats like Petya Ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.