Qword.com Removal Instructions
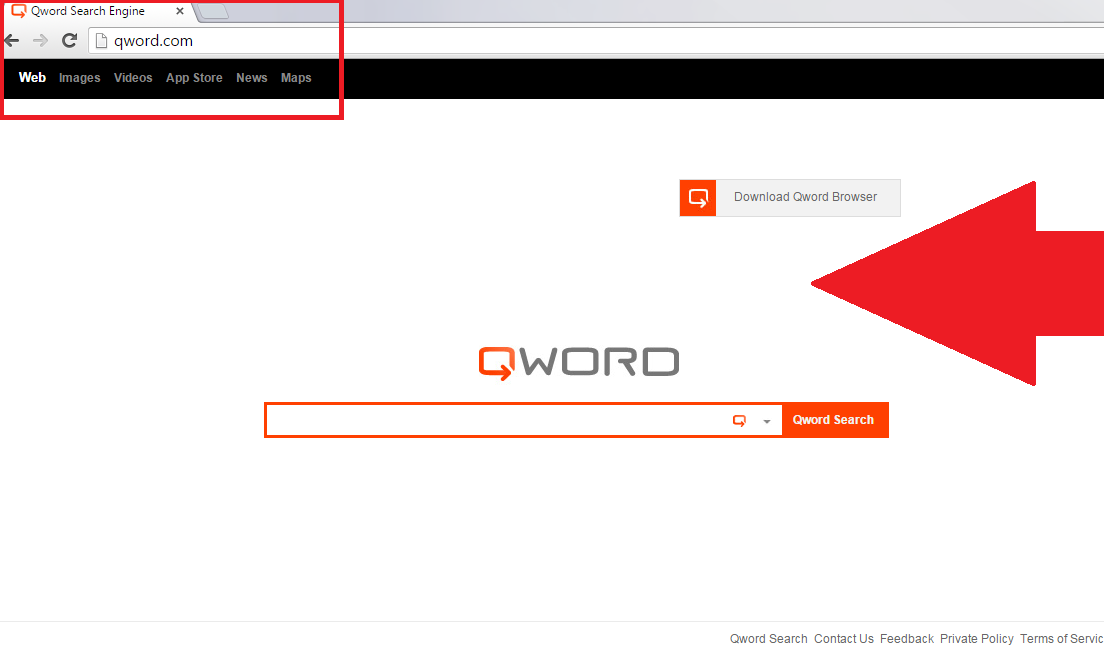
Qword.com is classified as a browser hijacker, because it can alter your web browser settings without your authorization. It may be promoted as a high-quality search tool, however, that is not the case. The hijacker is not aimed at improving your online surfing experience, instead, it makes profit for its developers by promoting various websites.
In order to generate web traffic the hijacker employs varioustactics such as redirects and advertisements. It is compatible with all popular browsers including Mozilla Firefox, Google Chrome, and Internet Explorer. This means that no matter which browser you use, you will still have to deal with the hijacker’s symptoms. We suggest that you terminate qword.com without hesitation and go back to regular Internet surfing right away.
 How does qword.com spread?
How does qword.com spread?
qword.com gets distributed with the help of freeware and shareware bundles. When you download free third party software from file-sharing sites, you are often offered to install additional programs onto your PC. If you fail to notice these offers, you agree to them unwittingly. That is most likely how the hijacker ended up in your system. You should avoid similar situations in the future. When you install free software, make sure that you check every step of the installation wizard. Deselect all unfamiliar software and only install those components that are absolutely necessary. Do not be tricked by how additional programs are presented, because their descriptions may be fake. Choose Advanced installation mode and decline all optional offers. That way you will never have to deal with qword.com removal again.
What does qword.com do?
Once the hijacker takes over, it alters your home page, new tab and default search provider. The site that now appears on your screen each time you go online may look more or less reliable, however, if you see any ads or links on it, we advise that you stay away from them. The same goes for the sponsored content that you are bound to notice in the search results brought to you by your new search provider. The reason you should avoid this commercial data is because it may be unreliable. You will expose your computer to unnecessary risks, if you click on one of the fake ads and get redirected to a corrupted site. You may infect your PC with malicious programs or fall victim to a financial scam. To make sure that never happens, you should get rid of qword.com as soon as possible.
You will also experience other inconveniences when dealing with the hijacker. After its arrival your Internet and system speed will noticeably slow down. The hijacker will also track your cookies collecting information about your online behavior. Such data as your visited pages, clicked ads, search terms, and so on will be used to create personalized ads. This data may also be sold to third parties. If you are not comfortable with sharing such details, you should delete qword.com from your browsers.
How to remove qword.com?
There are two options to choose from when it comes to qword.com removal. The first option is to erase qword.com automatically. If you download the anti-malware tool from our page and implement it, you will be able to scan your system, detect and eliminate all potential that it contains. You will not only terminate qword.com and other infections, but you will also make sure that your PC stays safe and protected in the future. The second solution to your problem is manual qword.com removal. This option is not as reliable, however, since the hijacker is not malicious, you should be able to delete qword.com without much difficulty. First, you will have to uninstall the hijacker’s related software and then restore your web browser settings. If you are not sure how to complete these tasks, you are welcome to use the instructions presented right below the article.
Qword.com Removal
Uninstall qword.com
Windows 8, 7 and Vista
- Right-click on the lower left corner or click on Start
- Choose Control Panel from the list
- Select Uninstall a program
- Choose the application and click Uninstall
Windows XP
- Click on the Start button at the bottom left
- Locate Control Panel on the list and click on it
- Select Add or Remove programs
- Click on the unwanted program and click Remove
Uninstall qword.com from browsers
Internet Explorer
- Click on the Gear icon and select Internet Options
- Overwrite your home page on the General tab and click OK
- Go back to Gear icon and open Manage Add-ons
- In Toolbars and Extensions, delete unwanted add-ons
- In Search Providers, erase qword.com and set a new engine
Google Chrome
- Click on Chrome menu, select More tools and Extensions
- Remove unwanted extensions
- Click Settings and choose Open a specific page or set of pages
- Click on Set pages and change your home page
- Click on Manage search engines under Search
- Delete qword.com and set a new search engine
Mozilla Firefox
- Click on the menu icon and select Add-ons
- Go to Extensions and delete all unwanted extensions
- Go back to the menu and select Options
- On the General tab, modify your home page
- On the Search tab, remove qword.com and set a new provide
Offers
Download Removal Toolto scan for Qword.comUse our recommended removal tool to scan for Qword.com. Trial version of provides detection of computer threats like Qword.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
 How does qword.com spread?
How does qword.com spread?