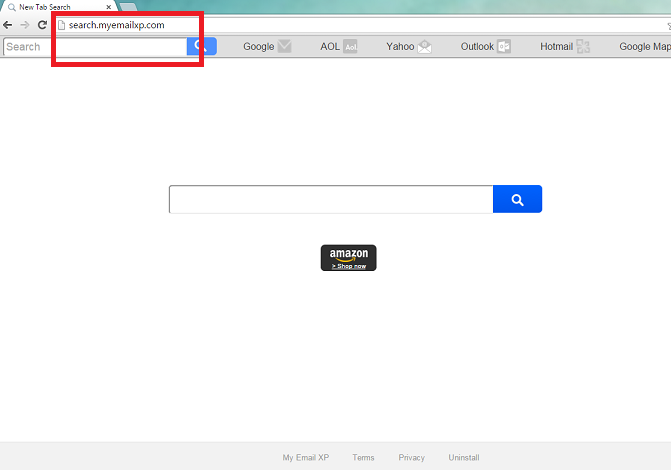
Search.myemailxp.com Removal Tips
A browser hijacker named Search.myemailxp.com is a nasty infection that changes browsers’ settings without permission. If you found this intruder in one of your browsers, it means that the others are affected too, since the application is compatible with all of them (Google Chrome, Internet Explorer, and Mozilla Firefox).
According to the information provided in its official website myemailxp.com, it is supposed to help you “login to your email faster”. While this sounds like a useful function, we warn you that you cannot trust this software. If you noticed it in your PC, the best decision would be to terminate Search.myemailxp.com from your system.
What does Search.myemailxp.com do?
If you attempt to use the provided search tool, you will notice that it is incapable of presenting you with genuine search results. Instead it will redirect all your search queries to search.yahoo.com. Many users, believing that the provided results are trustworthy, since they come from Yahoo!, resign themselves to the changed home page and default search tool which is definitely a mistake. Keep in mind that browser hijackers can alter user’s search results by adding sponsored links and ads which can route you to malicious pages. This means that for as long as the software is in your PC, you will be unable to trust your search engine. We advise to remove Search.myemailxp.com and to recover your lost settings.
Another thing you need to know is that this application collects your information (clicks, search queries, browsing history, geographical location, etc.) and shares it with the third parties. Needless to say, that is not something you can tolerate. The only way to stop the spying is to eliminate Search.myemailxp.com as soon as you can.
Even though it is possible to acquire this software from its official page, users often complain that it enters their computers without permission. If you also missed the moment of entrance, the hijacker probably sneaked in using malicious InstallCore downloaders. Our researchers managed to determine this when they noticed that installer’s signature is Compiler Idea which is used in InstallCore bundles. We advise to be more careful in the future and to download freeware only from the trustworthy sources.
How to remove Search.myemailxp.com?
If you decided to get rid of Search.myemailxp.com, you should decide how you want to do t. If manual Search.myemailxp.com removal is the way you wan to deal with this problem, you will find the instructions under this article. Follow them and you should be able to delete Search.myemailxp.com. However, you can also terminate Search.myemailxp.com automatically. For that you need to employ a reputable computer security software and let it uninstall Search.myemailxp.com for you.
Erase Search.myemailxp.com
Windows 8
- Navigate to the bottom right corner of the desktop and pick Settings.
- Choose Control Panel and tap Uninstall a program.
- Uninstall Search.myemailxp.com.
Windows XP
- Click Start button on the Taskbar and choose Control Panel.
- Open Add or Remove programs and remove Search.myemailxp.com.
Windows Vista and Windows 7
- Access Start menu and press Control Panel.
- Go to Uninstall a program and uninstall Search.myemailxp.com.
Eliminate Search.myemailxp.com from your browsers
Mozilla Firefox
- Press the menu icon and select Options.
- Access General tab and change/remove your home page.
- Move to Search tab and overwrite your search provider.
- Tap the menu once more and open Add-ons.
- Remove the unwanted extensions.
Google Chrome
- Tap the menu and go to Settings.
- Select Set pages and overwrite your home page.
- Under Search, choose Manage search engine.
- Delete the current search tool and choose a new one.
- Open Extensions and remove useless add-ons.
Internet Explorer
- Click the Gear icon and select Internet Options.
- Overwrite your home page in the General tab.
- Tap the Gear icon and access Manage Add-ons.
- Pick Toolbars and Extensions and uninstall unwanted add-ons.
- Move to Search Providers and set a new search engine after you deleted the old one.
Offers
Download Removal Toolto scan for Search.myemailxp.comUse our recommended removal tool to scan for Search.myemailxp.com. Trial version of provides detection of computer threats like Search.myemailxp.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.