InstrSearch.myspeedtestxp.com Removal Instructions
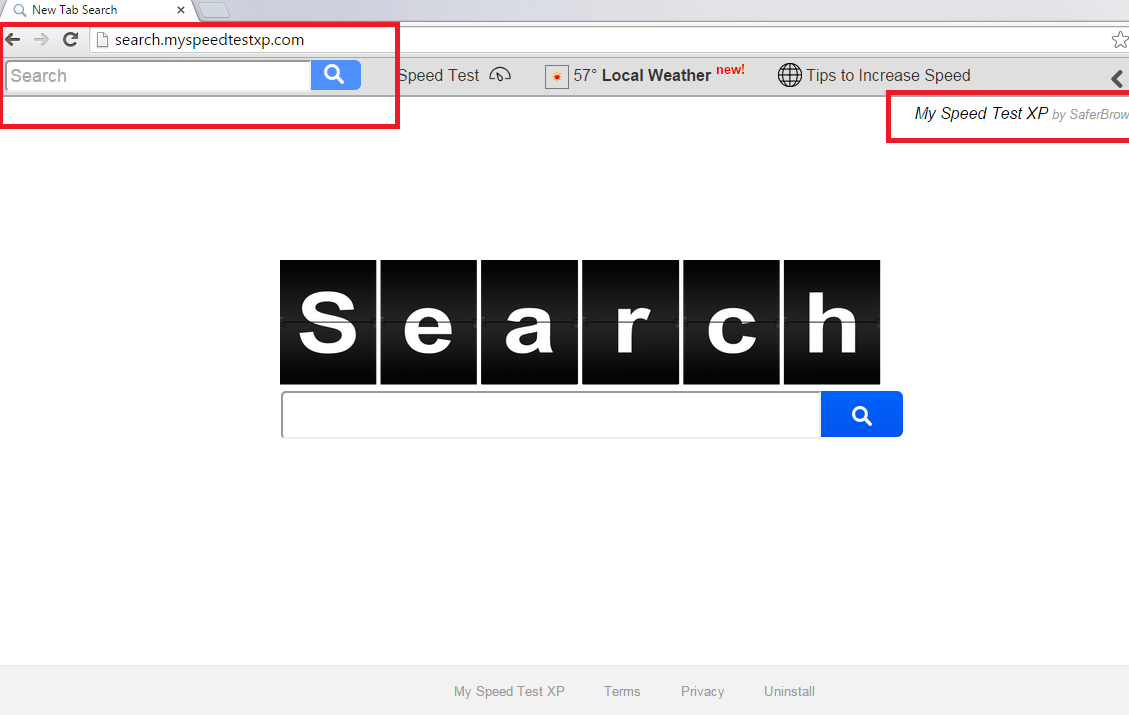
Search.myspeedtestxp.com is classified as a browser hijacker for a couple of reasons. For instance, Search.myspeedtestxp.com will alter all of the web browsers without your explicit consent. Many PC users are surprised to find the Search.myspeedtestxp.com infection in their electronic devices. Once the hijacker is installed, your Google Chrome, Mozilla Firefox, and Internet Explorer settings will be definitely modified.
You will find a new search engine and start-up page. If you have noticed any similar changes to your web surfers, you should remove Search.myspeedtestxp.com infection without any feeling of guilt. We can promise you that by keeping the hijacker, your computer’s system will gain nothing beneficial whatsoever. You can learn how to uninstall Search.myspeedtestxp.com quickly and efficiently at the very end of this article.
Why do you need to delete Search.myspeedtestxp.com ASAP?
Browser hijackers such as mystartsearch.com, istart123.com, istartsurf.com, qone8.com, and others are very similar to Search.myspeedtestxp.com. All of them work in an almost identical way and will try its best in order to gain revenue. Search.myspeedtestxp.com promotes suspicious web pages and, if you click any of them, the hijacker’s developers get paid. Once this happens, you will no longer be able to use your web browser effectively. All of your Internet pages will be flooded with the annoying advertisements. This will definitely worsen your web surfing experience. Your Internet speed will become slower and you may have to deal with very annoying infections as well. This happens because by visiting the untrustworthy content, your computer might contract malicious software. Therefore, Search.myspeedtestxp.com removal is highly recommended and needs to be performed immediately.
Moreover, Search.myspeedtestxp.com gathers information about your web surfing habits. Among that data, there may be your personal details. The collected information may be later used for marketing purposes or sold to third parties. You need to know that similar data is recorded to make you enter as many sponsored pages as possible. By generating the adverts according to your personal preferences, the hijacker is actually able to make the ads even more alluring. Only if you delete Search.myspeedtestxp.com, you will be able to erase all the intrusive advertisements and get your normal web surfing back.
How to stop the unwanted programs from entering virtual machine?
The best what you can do to make sure you will not find the Search.myspeedtestxp.com infection in your computer’s system is to carefully examine every single installation step when downloading new programs. Also, make sure that you refuse any offered installation of bonus plug-ins. While installing your new application, please always choose the Advanced’ or ‘Custom’ options. This will let you see any additional programs that may try to enter your PC unnoticed. More than that, you will be able to deselect all the undesirable software in the installation wizard. If, by any unlucky chance you are faced with a browser hijacker, you will need to eliminate Search.myspeedtestxp.com without hesitation.
How can I take care of Search.myspeedtestxp.com removal?
You may remove Search.myspeedtestxp.com by using either the manual or automatic removal method. You can get rid of Search.myspeedtestxp.com infection manually by following the manual termination guide bellow. Please make sure that you follow all the steps correctly because the hijacker will use even the smallest of your mistake in order to enter the computer once again. Also, we have to warn you that the manual termination technique is oriented on the more experienced computer users. This is because it is more difficult than the automatic one. You will have to locate not only Search.myspeedtestxp.com but other infections that may have come to your computer together with the previously mentioned threat. It is not as easy as one may think to find all the potentially dangerous programs on your computer. However, the Search.myspeedtestxp.com removal task becomes less difficult, if you apply the automatic elimination way. You will only need to invest in a reliable anti-virus program that will be able to do all the work instead of you. Your security software can actually guarantee the safety of your computer 100%, if you keep the anti-spyware application up to date.
Windows XP
1. Go to the Start menu.
2. Enter Control Panel.
3. Choose Add or Remove Programs.
4. Pick the undesirable add-on.
5. Remove the application.
Windows Vista/Windows 7
1. Hit Win+R and write in control panel.
2. Select OK.
3. Access Uninstall a program.
4. Choose the suspicious program and select.
Windows 8/Windows 8.1/Windows 10
1. Hit Win+X.
2. Go to Programs and Features.
3. Choose the suspicious program.
4. Select Uninstall.
Internet Explorer
1. Launch your Internet browser.
2. Hit Alt+T.
3. Choose Internet Options.
4. Access the Advanced tab.
5. Select Reset.
6. Check Delete personal settings.
7. Choose Reset again.
Mozilla Firefox
1. Open Mozilla Firefox.
2. Hit Alt+H.
3. Go to Troubleshooting information.
4. Select Reset Firefox.
5. Choose the Reset Firefox button.
Google Chrome
1. Go to your Google Chrome.
2. Press Alt+F.
3. Choose Settings.
4. Move to Show advanced settings.
5. Select Reset browser settings.
6. Choose the Reset button once again.
Offers
Download Removal Toolto scan for Search.myspeedtestxp.comUse our recommended removal tool to scan for Search.myspeedtestxp.com. Trial version of provides detection of computer threats like Search.myspeedtestxp.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.