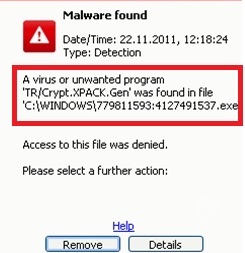
TR/Crypt.XPACK.Gen2 Removal Instructions
TR/Crypt.XPACK.Gen2 is listed as a Trojan that interferes with your computer’s work. For example, you will not be able to run exe files or change your homepage. In addition, the application will slow down your virtual device and internet connection.
You will also experience regular computer’s system crashes. This Trojan is definitely a dangerous program that will make your electronic device barely useable. Hence, you should remove TR/Crypt.XPACK.Gen2 as soon as possible.
How can TR/Crypt.XPACK.Gen2 hijack my computer’s system?
TR/Crypt.XPACK.Gen2 infiltrates your PC via bundled freeware or shareware. Therefore, you should be more careful while downloading free of charge software bundles. In addition, you will probably not even notice that you have installed the Trojan to your computer’s system. TR/Crypt.XPACK.Gen2 infection is compatible with 32-bit versions of Windows NT/XP/2000/7 and Vista. If you have accidentally installed the Trojan, you need take care of TR/Crypt.XPACK.Gen2 removal right away.
Why do I need to delete TR/Crypt.XPACK.Gen2 from my PC’s system?
TR/Crypt.XPACK.Gen2 termination is extremely important for your computer’s security. You may not know that TR/Crypt.XPACK.Gen2 has reached your PC. However, you will notice for sure that your computer acts strangely. For example, you might not be able to access certain programs or make modifications to your web browsers’ settings.
In addition, Trojans are known for erasing, changing, collecting, and blocking the user’s information.
In other words, you can not be sure whether TR/Crypt.XPACK.Gen2 is not modifying or gathering data that is stored in your PC. The information may include personally identifiable details. This means that if you keep the program in your virtual device, you may experience an identity theft. Therefore, it is very important for you to remove TR/Crypt.XPACK.Gen2 without hesitation.
More than that, TR/Crypt.XPACK.Gen2 may easily redirect you to suspicious webpages. For example, the Trojan might set a new homepage that leads to a questionable site. Also, you may find new program’s icons on your screen. 5689.sys elimination is necessary as well because the application runs in your computer system’s background. You can only stop the Trojan’s not only annoying but also dangerous activities, if you uninstall TR/Crypt.XPACK.Gen2 and related programs once and for all.
How to take care of TR/Crypt.XPACK.Gen2 removal?
TR/Crypt.XPACK.Gen2 is a serious computer issue that requires automatic removal. The manual removal may be a challenging process even for the experienced computer users. Therefore, we do not recommend to risk your computer’s security. Moreover, if you fail to eliminate TR/Crypt.XPACK.Gen2 completely, you may lose your sensitive information or it may be reached by the cyber criminals.
The only secure way to delete TR/Crypt.XPACK.Gen2 is to invest in a legitimate anti-spyware software. The program will also ensure that you will not have to face similar problems in the future.
Offers
Download Removal Toolto scan for TR/Crypt.XPACK.Gen2Use our recommended removal tool to scan for TR/Crypt.XPACK.Gen2. Trial version of provides detection of computer threats like TR/Crypt.XPACK.Gen2 and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
