Yakes Ransomware Removal Guide
Yakes Ransomware is a harmful program that can infiltrate your computer and corrupt your important files. It is similar to Salam, Cryptowall, TrueCrypt, Cryptolocker, and some other parasites that belong to the same category.
The main goal of the infection is to make money off of you. It achieves this goal by encrypting your files and demanding that you pay a ransom for them. The infection spreads online through spam emails with malicious attachments, fake ads, corrupted sites, and so on. If your PC has been infected by it, you should not hesitate to remove Yakes Ransomware.
 How does Yakes Ransomware work?
How does Yakes Ransomware work?
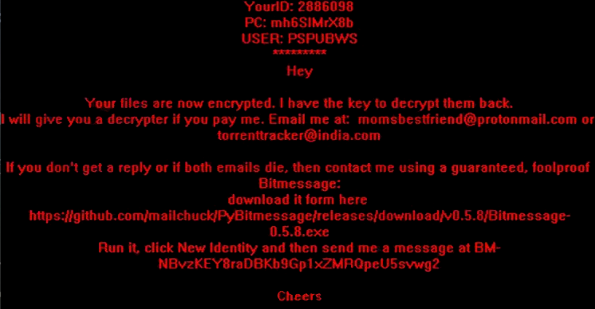
Yakes Ransomware functions in a similar manner to other malicious programs of this group. It slithers into the computer and starts the encryption process affecting such types of files as .pdf, .doc, .jpg, .avi, .mp3, .ppt, and many others. All corrupted files have the .KEYHOLES extension added to them and they can no longer be accessed. After the encryption is complete, the malware creates text files containing instructions on what you should do next. These instructions appear in each folder that contains corrupted files. They explain that in order to regain you data, you should contact the cyber crooks via email and pay them 4 Bitcoins, which is about $1800. It is clear that you cannot waste that kind of money on something that is not even guaranteed to work.
You should never follow the instructions given by the cyber criminals. They cannot be trusted. We advise that you delete Yakes Ransomware from your computer as soon as you can and then try alternative ways of restoring your files. If you have them backed up, you should have no trouble retrieving them from your removable drive or cloud. If not, you can try Shadow Volume Copies or System Restore features. You could also look for free file decryptors online. Please note, however, that you can only move on to restoring your files after you terminate Yakes Ransomware.
How to remove Yakes Ransomware?
The only way to uninstall Yakes Ransomware from your system completely is by implementing a reputable anti-malware utility. You can download one from our page. It will perform a full system scan and detect all malign files and programs that it contains. Once the scan is complete, the security software will delete Yakes Ransomware along with other found threats. In addition to Yakes Ransomware removal, you will also make sure that your PC stays safeguarded in the future as the anti-malware tool comes with malware prevention and other beneficial features.
Offers
Download Removal Toolto scan for Yakes RansomwareUse our recommended removal tool to scan for Yakes Ransomware. Trial version of provides detection of computer threats like Yakes Ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Uninstall Yakes Ransomware and related programs.
Remove Yakes Ransomware from Windows 8
Right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel choose Programs and Features and select to Uninstall a software.


Uninstall Yakes Ransomware from Windows 7
Click Start → Control Panel → Programs and Features → Uninstall a program.


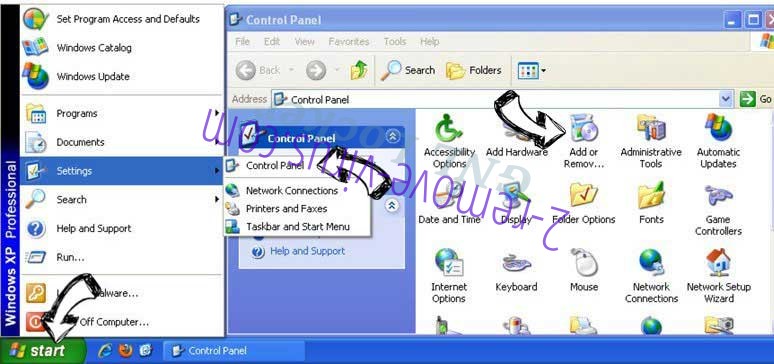
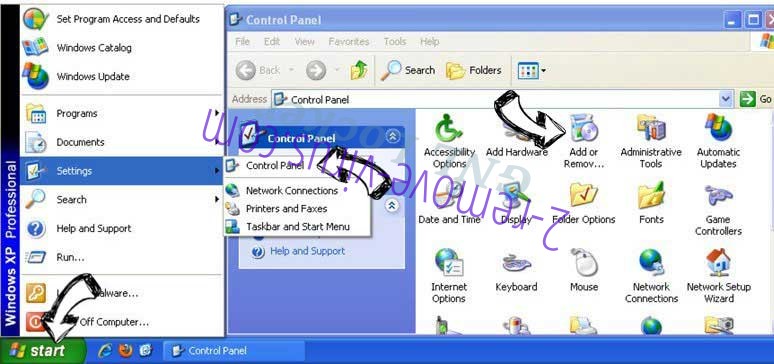
Delete Yakes Ransomware from Windows XP
Click Start → Settings → Control Panel. Locate and click → Add or Remove Programs.
Remove Yakes Ransomware from Mac OS X
Click Go button at the top left of the screen and select Applications. Select applications folder and look for Yakes Ransomware or any other suspicious software. Now right click on every of such entries and select Move to Trash, then right click the Trash icon and select Empty Trash.


Step 2. Delete Yakes Ransomware from your browsers
Terminate the unwanted extensions from Internet Explorer
- Tap the Gear icon and go to Manage Add-ons.

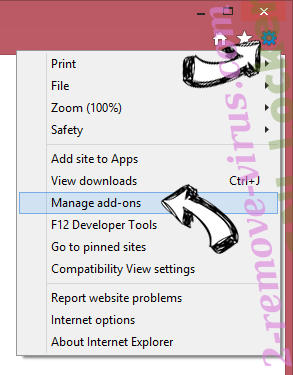
- Pick Toolbars and Extensions and eliminate all suspicious entries (other than Microsoft, Yahoo, Google, Oracle or Adobe)

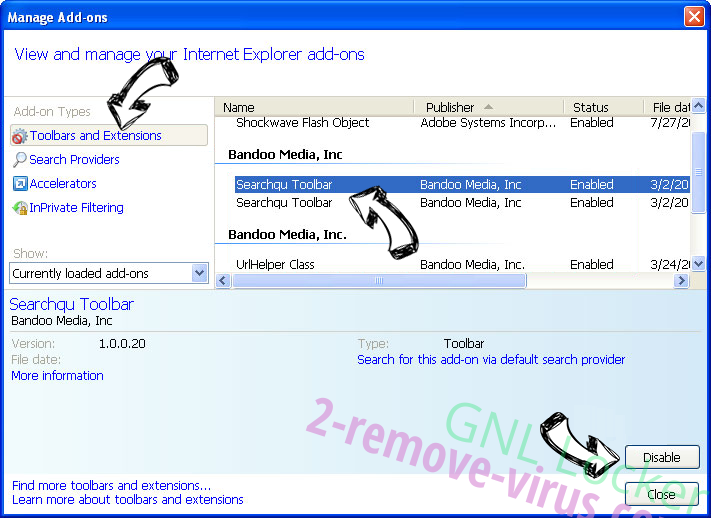
- Leave the window.
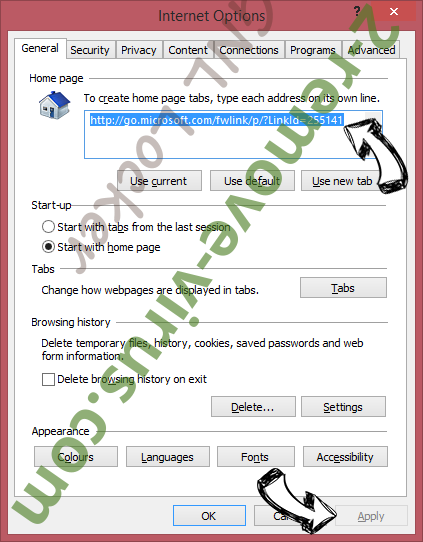
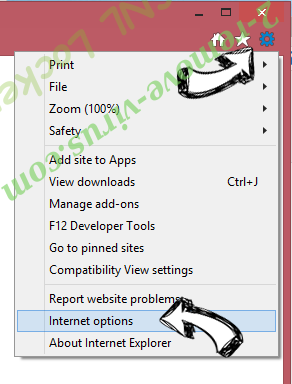
Change Internet Explorer homepage if it was changed by virus:
- Tap the gear icon (menu) on the top right corner of your browser and click Internet Options.

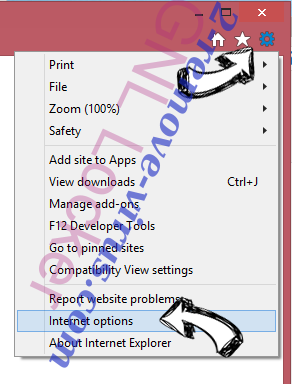
- In General Tab remove malicious URL and enter preferable domain name. Press Apply to save changes.

Reset your browser
- Click the Gear icon and move to Internet Options.

- Open the Advanced tab and press Reset.

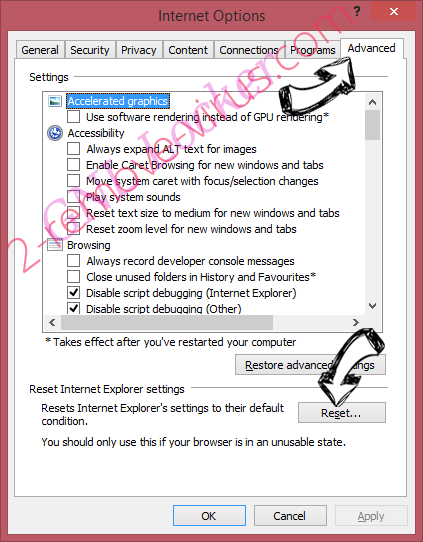
- Choose Delete personal settings and pick Reset one more time.

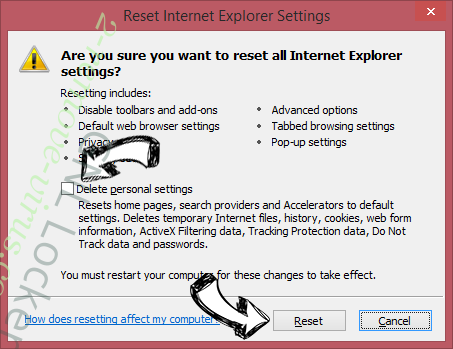
- Tap Close and leave your browser.

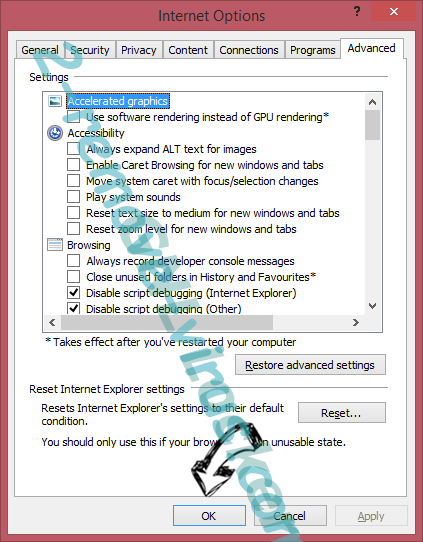
- If you were unable to reset your browsers, employ a reputable anti-malware and scan your entire computer with it.
Erase Yakes Ransomware from Google Chrome
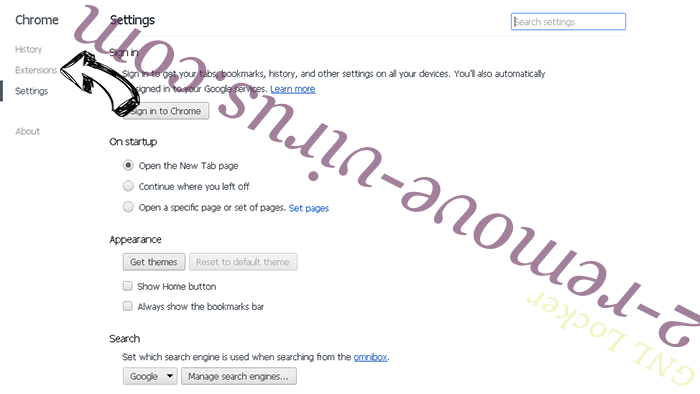
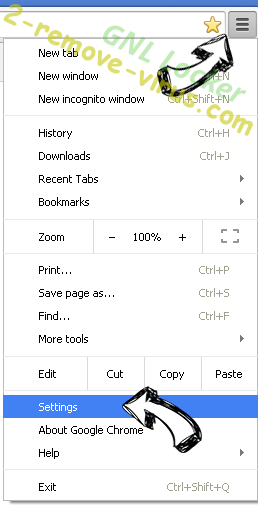
- Access menu (top right corner of the window) and pick Settings.

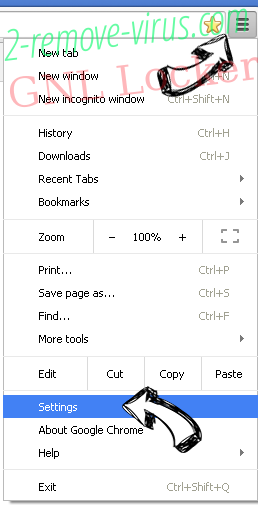
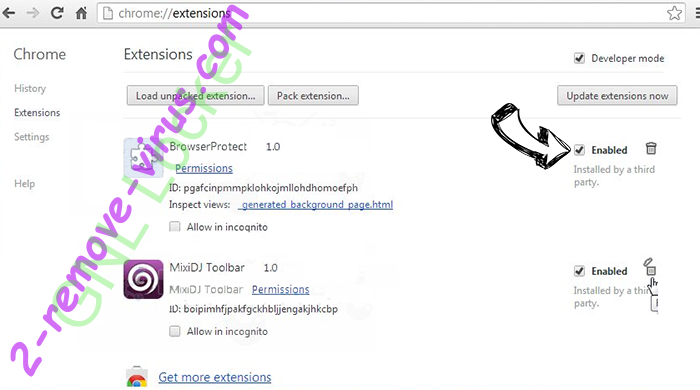
- Choose Extensions.

- Eliminate the suspicious extensions from the list by clicking the Trash bin next to them.

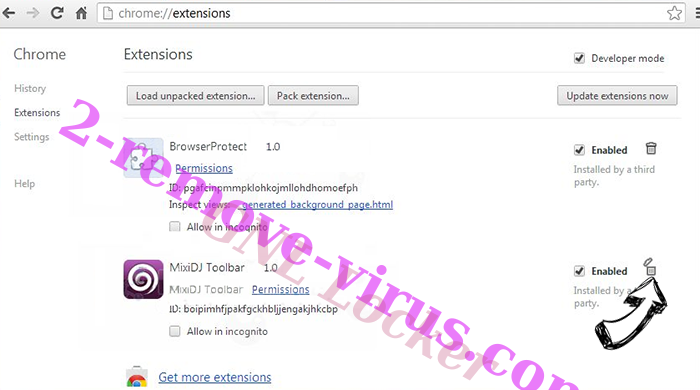
- If you are unsure which extensions to remove, you can disable them temporarily.

Reset Google Chrome homepage and default search engine if it was hijacker by virus
- Press on menu icon and click Settings.

- Look for the “Open a specific page” or “Set Pages” under “On start up” option and click on Set pages.

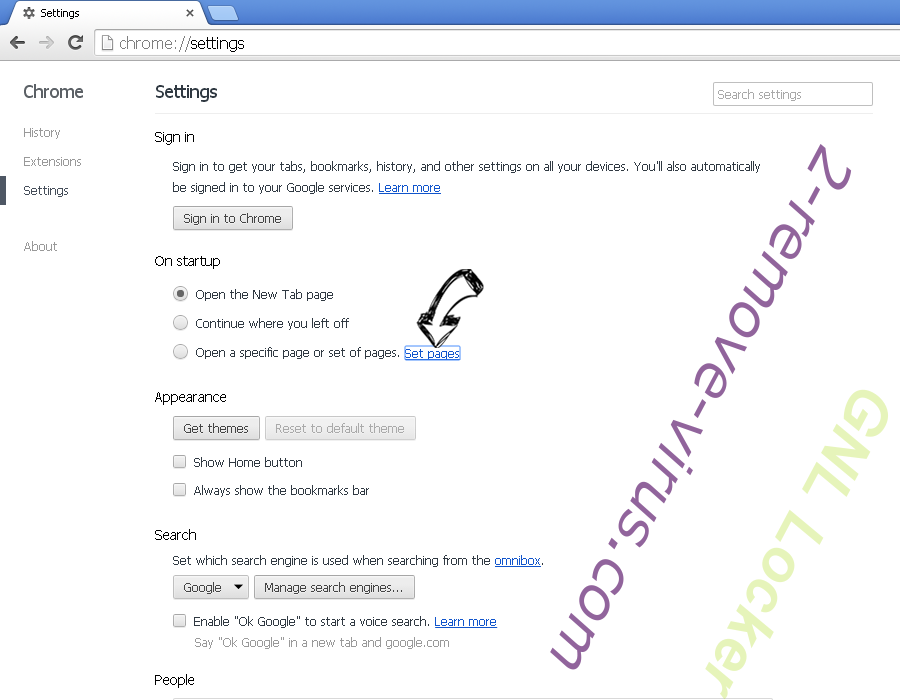
- In another window remove malicious search sites and enter the one that you want to use as your homepage.


- Under the Search section choose Manage Search engines. When in Search Engines..., remove malicious search websites. You should leave only Google or your preferred search name.

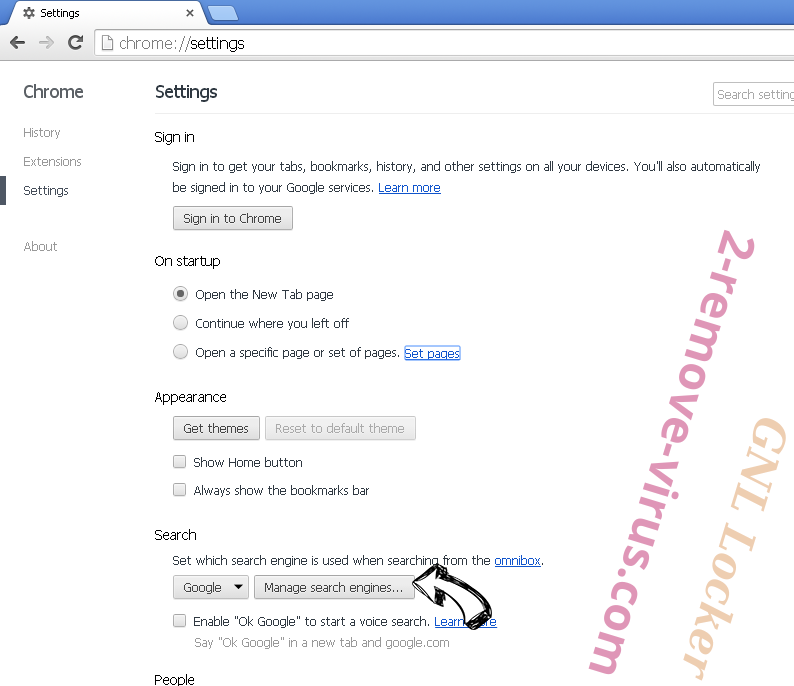


Reset your browser
- If the browser still does not work the way you prefer, you can reset its settings.
- Open menu and navigate to Settings.

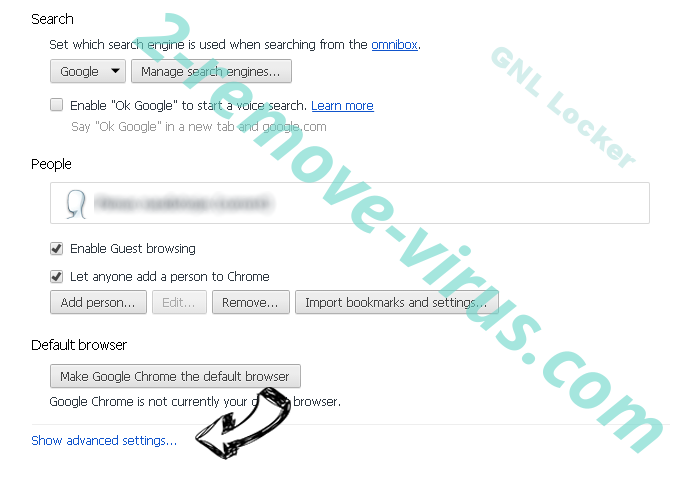
- Press Reset button at the end of the page.

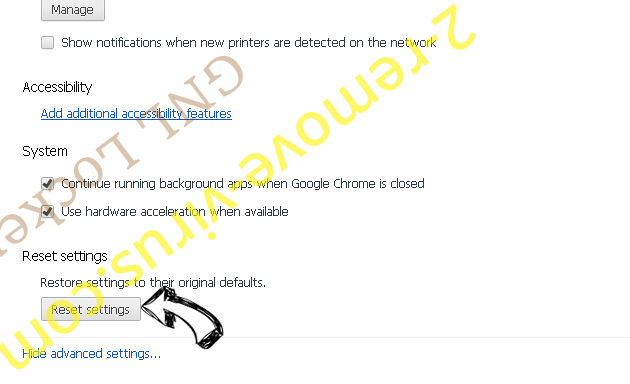
- Tap Reset button one more time in the confirmation box.

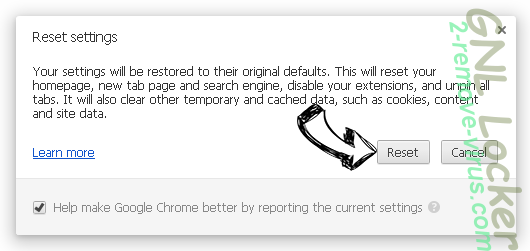
- If you cannot reset the settings, purchase a legitimate anti-malware and scan your PC.
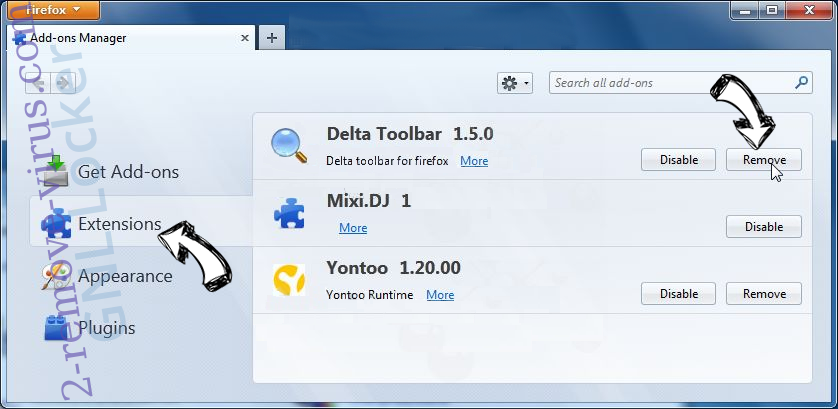
Remove Yakes Ransomware from Mozilla Firefox
- In the top right corner of the screen, press menu and choose Add-ons (or tap Ctrl+Shift+A simultaneously).

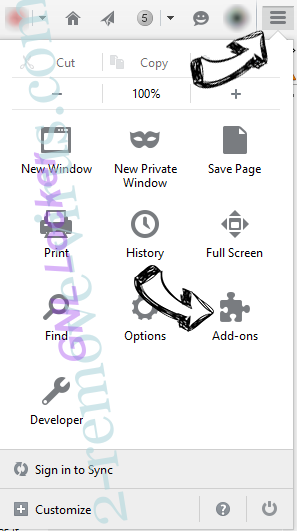
- Move to Extensions and Add-ons list and uninstall all suspicious and unknown entries.

Change Mozilla Firefox homepage if it was changed by virus:
- Tap on the menu (top right corner), choose Options.

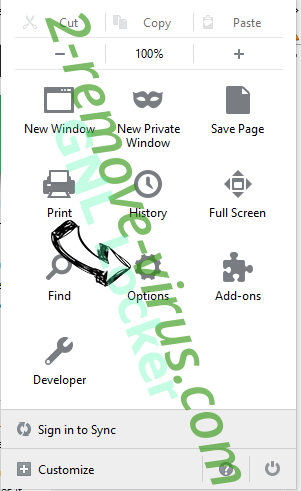
- On General tab delete malicious URL and enter preferable website or click Restore to default.

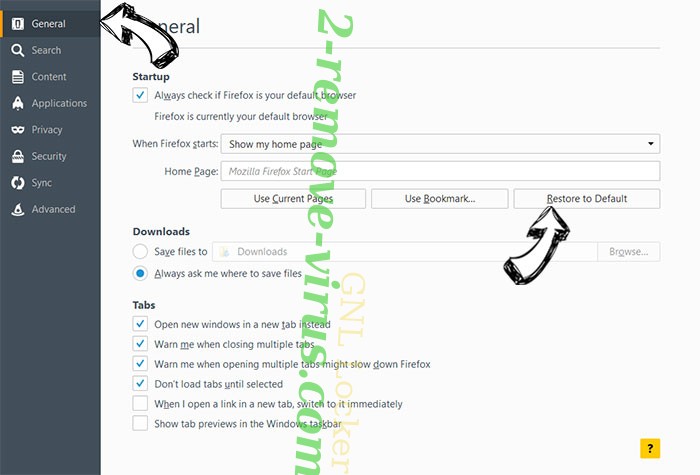
- Press OK to save these changes.
Reset your browser
- Open the menu and tap Help button.

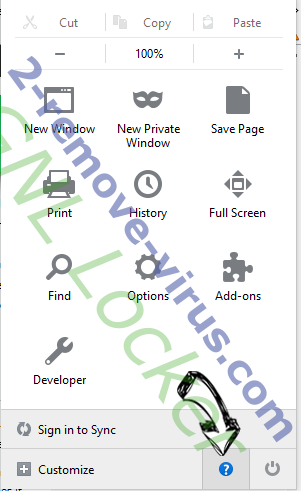
- Select Troubleshooting Information.

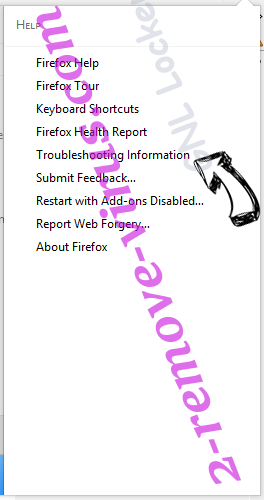
- Press Refresh Firefox.

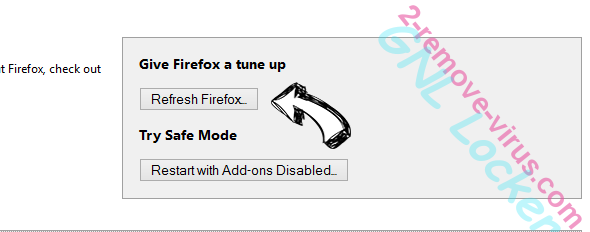
- In the confirmation box, click Refresh Firefox once more.

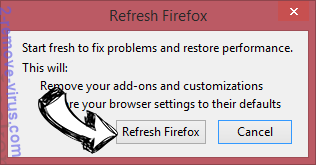
- If you are unable to reset Mozilla Firefox, scan your entire computer with a trustworthy anti-malware.
Uninstall Yakes Ransomware from Safari (Mac OS X)
- Access the menu.
- Pick Preferences.

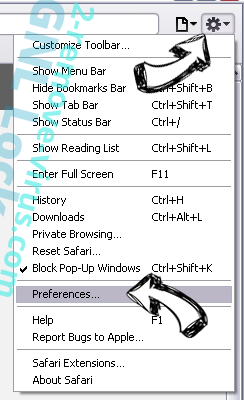
- Go to the Extensions Tab.

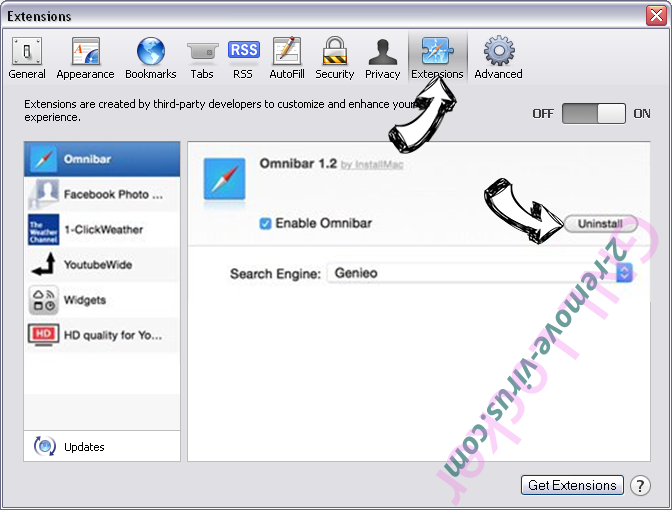
- Tap the Uninstall button next to the undesirable Yakes Ransomware and get rid of all the other unknown entries as well. If you are unsure whether the extension is reliable or not, simply uncheck the Enable box in order to disable it temporarily.
- Restart Safari.
Reset your browser
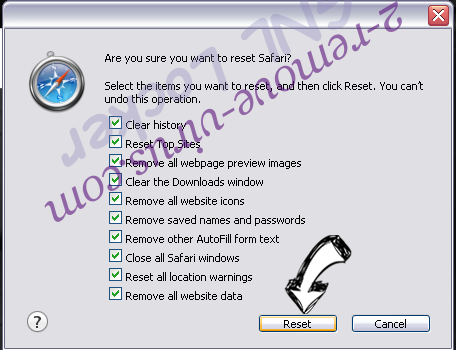
- Tap the menu icon and choose Reset Safari.

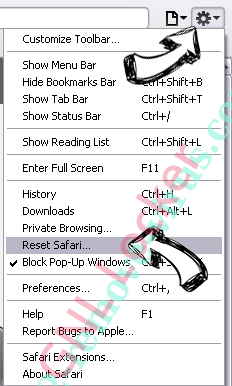
- Pick the options which you want to reset (often all of them are preselected) and press Reset.

- If you cannot reset the browser, scan your whole PC with an authentic malware removal software.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.