Your-home-page.net Removal Guide
Your-home-page.net can be classified as a browser hijacker because it changes your homepage and default search engine. Your-home-page.net promotes websites in all possible ways with the hope that you will click them.
You will probably want to know that this is how the hijacker manages to support itself. However, we advise you to not trust any advertisements or search results that you get from Your-home-page.net because that can harm your computer’s system. If you have recently installed free software from an unknown website, there is a high possibility that this is how Your-home-page.net infection has infiltrated in your computer.
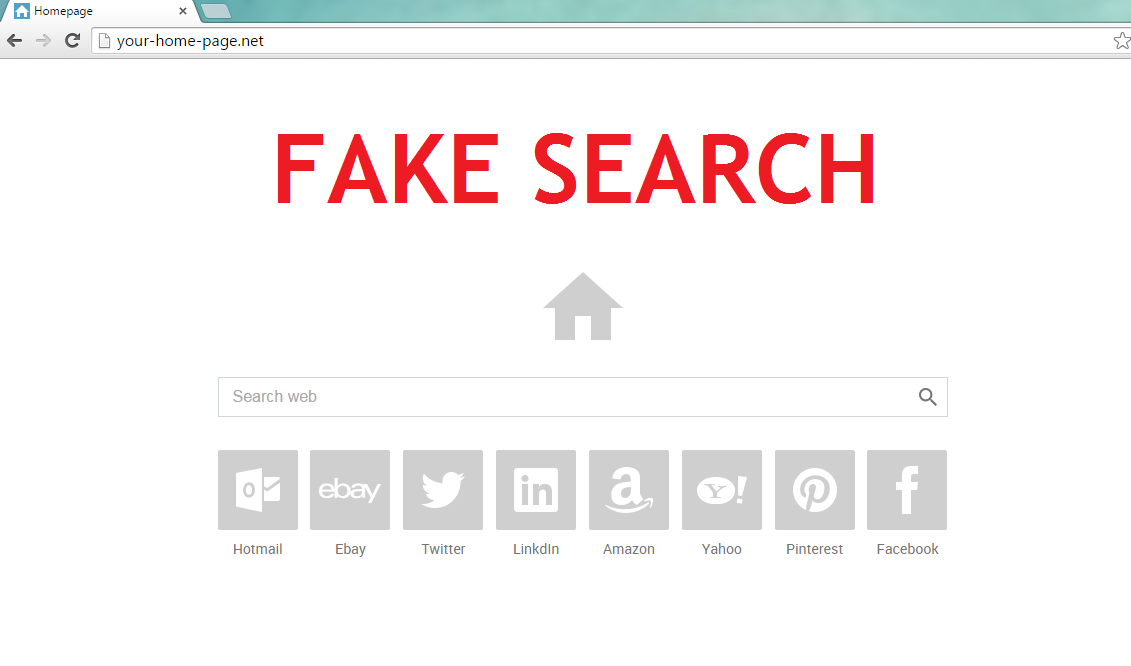
The hijacker is a useless search engine that instead of showing you the real search results, redirects you to questionable websites without your consent. All of this means that Your-home-page.net uses illegal methods in order to achieve their personal gain. Moreover, the hijacker may follow your browsing habits in order to display the commercial material that is more relevant to you. Furthermore, your personal information may be sold to third parties. Therefore, you should not trust Your-home-page.net; especially, when there are plenty of more reliable search engines (for instance, Google, Yahoo! or Bing) that will not put your computer at risk. Thus, the best option is to just remove Your-home-page.net from your computer’s system.
How can Your-home-page.net reach your PCs system?
Your-home-page.net gets into your computer when you install free of charge software from unknown websites. We do not advise you to download free apps (for instance, video players, download managers or PDF creators) from unfamiliar sources. These websites may offer you bundled freeware that can be infected. While installing freeware, you may only trust the official sites. However, you can also prevent unwanted programs from entering your PC by paying close attention to the installation steps. There are usually Advanced and Custom options in which you can find a checker box and deselect all the unwanted applications. Therefore, it is very important to check whether the website is reliable and then pay close attention to the installation wizard. If you already have Your-home-page.net in your system, you need to take care of the hijacker’s removal as soon as you can.
How to remove Your-home-page.net?
Your-home-page.net is nothing but a fraud that will perform changes on your web browser without your consent. In other words, the hijacker does not deserve to be kept in your PC and needs to be stopped from causing more damage.
There are two methods how you can uninstall Your-home-page.net from your computer. You can either terminate Your-home-page.net automatically or manually. You will probably find the automatic option better because it allows you to take care of Your-home-page.net removal effortlessly. In addition, malware removal software erases all the possible infections that may have entered together with the hijacker and prevents from the threats in the future.
However, you can also delete Your-home-page.net manually by using the hijacker’s removal instructions that you will find bellow the article. It may be more challenging to terminate the hijacker manually for an inexperienced user; thus, we hope that our detailed removal guide will be helpful.
Windows 8 / Windows 8.1
1. Move your mouse cursor to the bottom right of the screen.
2. Wait until the Charm bar shows up, select Settings and open Control Panel.
3. Choose Uninstall a program.
4. Delete Your-home-page.net.
Windows Vista / Windows 7
1. Go to the Start menu and open Control Panel.
2. Select Uninstall a program.
3. Eliminate Your-home-page.net.
Windows XP
1. Open the Start menu button and go to Control Panel.
2. Choose Add or remove programs
3. Uninstall Your-home-page.net.
Internet Explorer
1. Tab Alt+T and select Internet options.
2. Go to the Advanced tab and choose Reset.
3. Open Delete personal settings and click Reset.
4. Press Close.
Mozilla Firefox
1. Tab Alt+H and open Troubleshooting information.
2. Select Refresh Firefox.
3. Click Refresh Firefox again.
4. Press Finish.
Google Chrome
1. Tab Alt+F and select Settings.
2. Choose Show advanced settings.
3. Click Reset settings again.
4. Click Reset.
Offers
Download Removal Toolto scan for Your-home-page.netUse our recommended removal tool to scan for Your-home-page.net. Trial version of provides detection of computer threats like Your-home-page.net and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
