Erqw ransomware is file-encrypting malware. This ransomware is simply an updated version of the infamous file-encrypting infection known as Djvu/STOP. New variants of this ransomware are regularly released by the malicious actors behind it, but most of them are largely the same. The file extensions that are added to encrypted files allow users to identify which version they are dealing with. In this instance, personal files that are encrypted will have a .dfwe extension attached to them. You will be able to retrieve your files very easily if you have a backup. However, it will be far more challenging to restore files if you have not backed them up. One option is to use the Dfwe ransomware decryptor but only the ransomware operators have it. They will try to sell it to you but paying is not recommended.
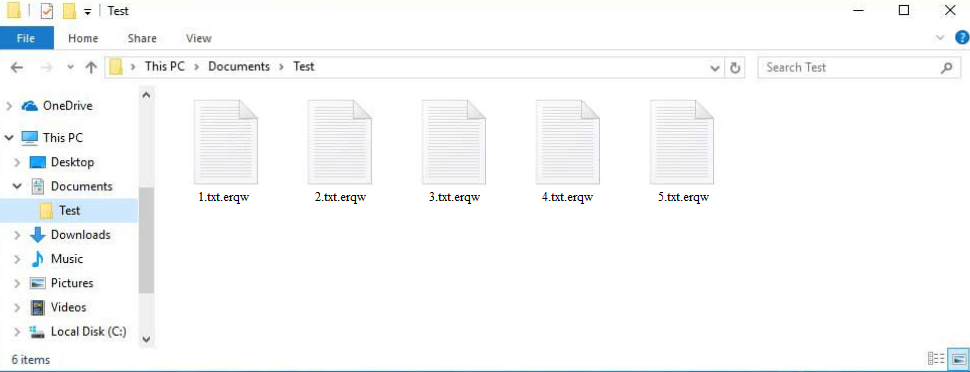
Erqw ransomware is yet another version of the Djvu/STOP ransomware. The versions are mostly similar to one another. They all aim to encrypt personal files, such as photos, videos, documents, etc. The extension .erqw is added to all encrypted files, which will allow you to immediately identify the affected files. An encrypted text.txt file, for instance, would become text.txt.erqw. Any encrypted files must first be decrypted in order to be opened. This requires a unique decryptor, but getting your hands on one will be challenging because only the cybercriminals operating this ransomware have access to it. And they won’t just send you the decryptor because their primary objective is to extort money from their victims.
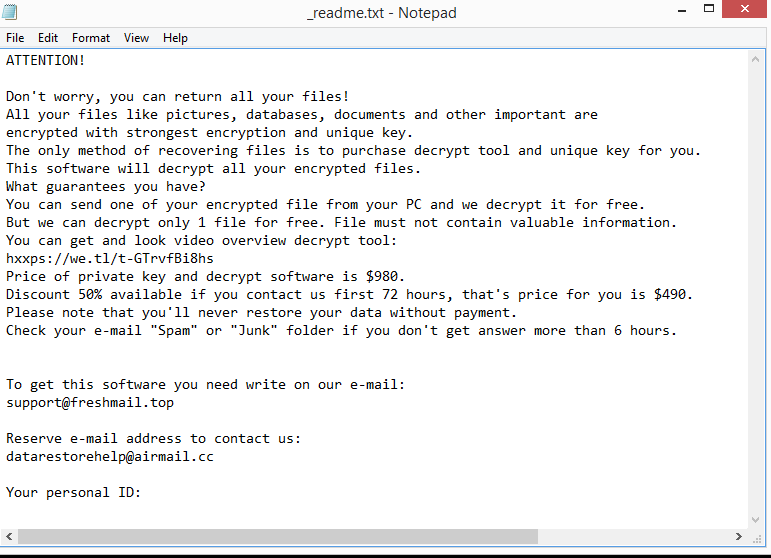
The ransomware will drop a _readme.txt ransom note after it has finished encrypting your files. Though the ransom note is quite basic, it does include instructions on how to obtain the decryptor. The decryptor can be purchased by victims for $980, albeit there is a 50% discount available to those who get in touch with the malicious actors within the first 72 hours. There may or may not be a discount, but paying the ransom is often not recommended. You must remember that you are dealing with cybercriminals and that a decryptor will not necessarily be sent. Cybercriminals are unlikely to feel obligated to assist you, therefore there is nothing stopping them from simply taking your money. In the past, despite paying the ransom, numerous victims did not get their decryptors.
You won’t have any problems with file recovery if you have a backup. However, before you can begin, Erqw ransomware must first be completely removed from your computer. Use a trustworthy anti-malware program to delete Erqw ransomware. Do not try to manually remove Erqw ransomware because that could cause additional damage. You can access your backup to begin the file recovery process once the ransomware has been fully removed.
It will be more challenging to restore files if there is no backup. The only choice is to wait for the release of a free Erqw ransomware decryptor. Although you won’t be able to find one right now, it’s not impossible that it will eventually become available. However, it is challenging for malware researchers to develop a free decryptor since Erqw ransomware uses online keys for file encryption. A free Erqw ransomware decryptor is unlikely unless the keys are released by the cybercrooks themselves because they are specific to each victim. Nevertheless, if you have no other choice, back up your encrypted files and wait.
How is ransomware distributed?
Distribution methods for ransomware that targets regular users include torrents, malicious email attachments, ads on high-risk websites, etc. Users that have unhealthy internet habits are considerably more likely to become infected with malware since they are more prone to take risks when online. Users’ risks of acquiring malware would be considerably reduced if they took the time to develop healthier browsing habits.
Because torrent websites are often unregulated, malicious actors can easily post torrents containing malware. Before being taken down, the torrents may remain up for a while and infect thousands of users. Malware is frequently found in torrents for well-known movies, TV shows, video games, software, etc. Downloading copyrighted content for free is not only content theft but it’s also dangerous for the computer.
Email attachments are another common method used to distribute malware. Users’ computers get infected with malware when they open malicious email attachments. Fortunately for users, malicious emails are typically fairly obvious. One of the most obvious giveaways is grammar and spelling mistakes in emails that are supposedly sent by legitimate companies. Emails sent by companies to their customers will always be mistake-free because they would look unprofessional otherwise. However, malicious emails are usually full of them.
Malicious senders also address users using generic words like User, Member, Customer, etc. Legitimate emails would address users by name if the sender was a company whose services the recipients use. It’s also worth mentioning that some malicious campaigns may be much more sophisticated. Therefore, it’s recommended to scan all unsolicited email attachments with anti-virus software or VirusTotal.
How to delete Erqw ransomware
Since Erqw ransomware is a sophisticated malware infection, it is recommended that you use a good anti-malware program to remove it from your computer. If you attempt to do it manually, you risk jeopardizing your computer even more. It’s also likely that you’ll overlook some ransomware items, which can subsequently enable the ransomware to recover. And if the ransomware recovers when you’re connected to your backup, those files would become encrypted as well.
Using anti-malware software is the simplest and safest method to remove Erqw ransomware. You can safely connect to your backup and start recovering files after the ransomware has been completely removed from your computer.
If you don’t have a backup, your only option is to wait for a free Erqw ransomware decryptor to be released. However, it’s not certain when it will be released. Nonetheless, users without backup should back up their encrypted files and occasionally search for a decryptor. When it does get released, it would appear on NoMoreRansom.
Erqw ransomware is detected as:
- VHO:Trojan.Win32.Convagent.gen by Kaspersky
- Trojan:Win32/Sabsik.FL.B!ml by Microsoft
- TrojanX-gen [Trj] by Avast/AVG
- Gen:Heur.Mint.Zard.52 by BitDefender
Quick Menu
Step 1. Delete Erqw ransomware using Safe Mode with Networking.
Remove Erqw ransomware from Windows 7/Windows Vista/Windows XP
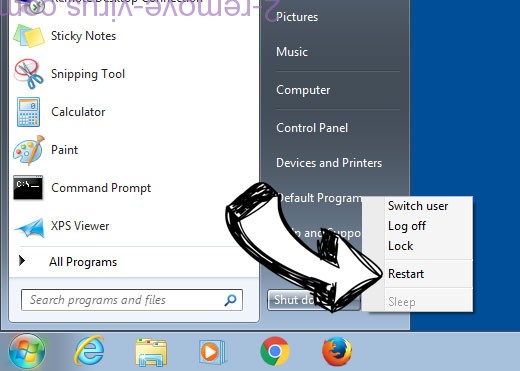
- Click on Start and select Shutdown.
- Choose Restart and click OK.

- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove Erqw ransomware
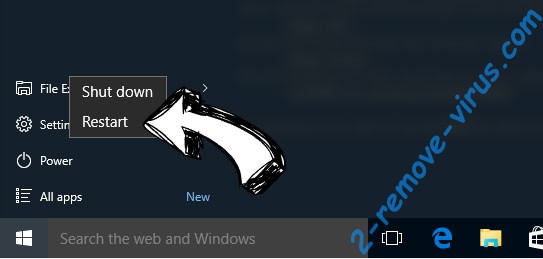
Remove Erqw ransomware from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.

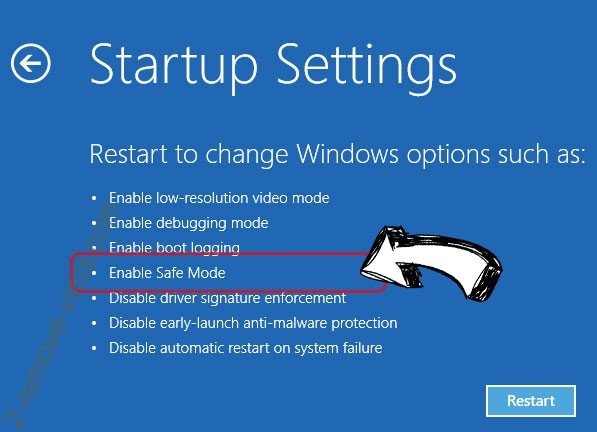
- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete Erqw ransomware
Step 2. Restore Your Files using System Restore
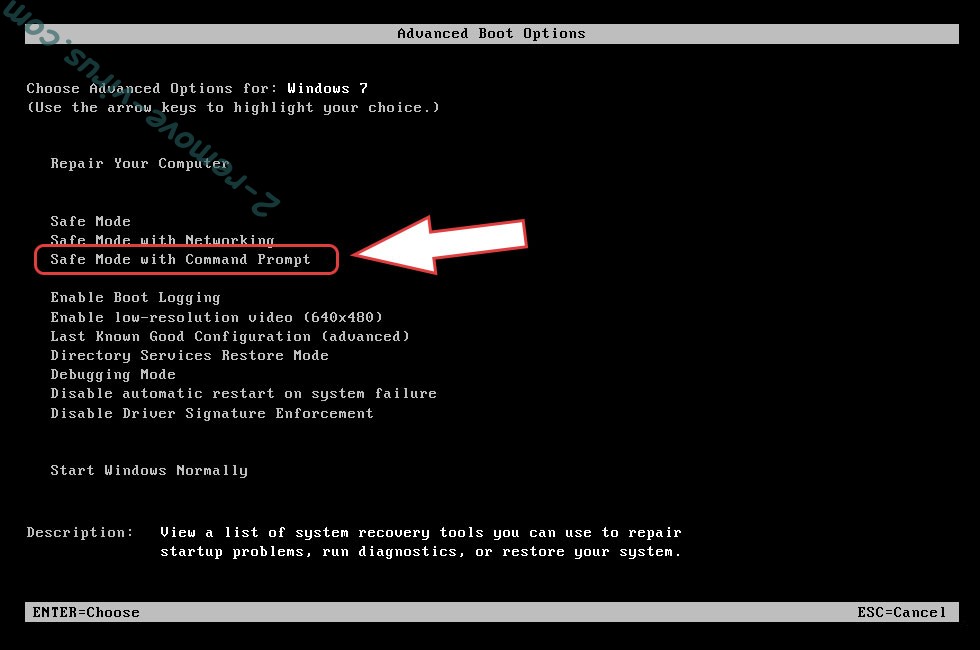
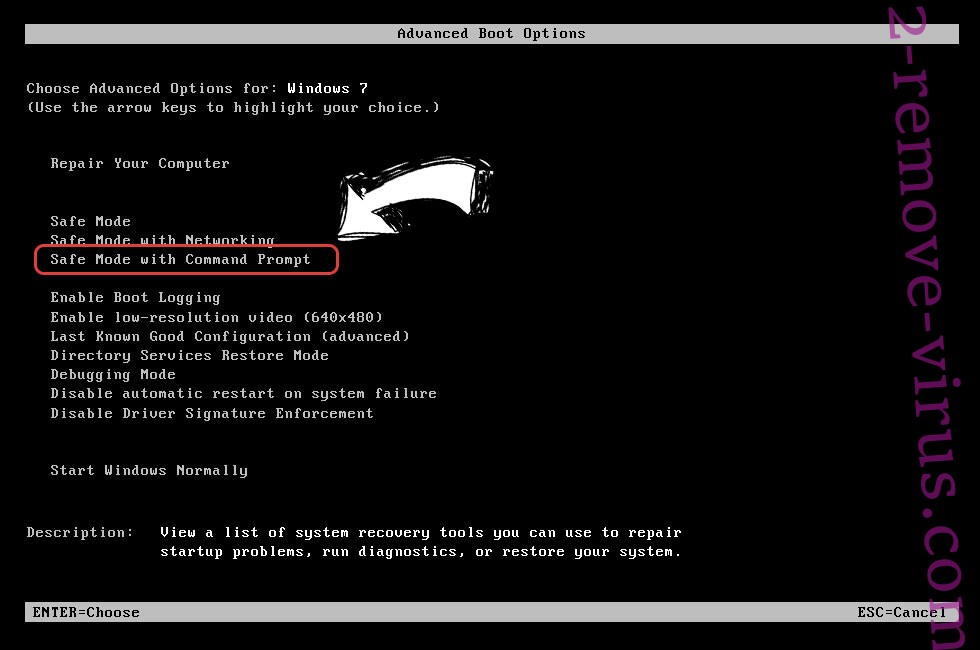
Delete Erqw ransomware from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

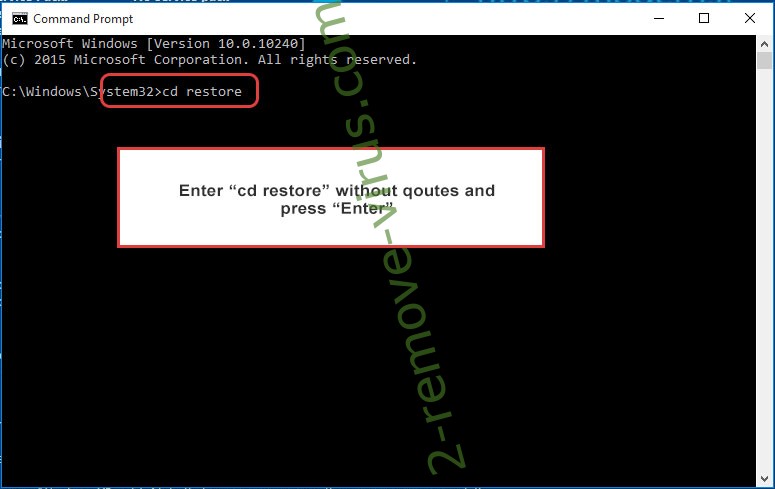
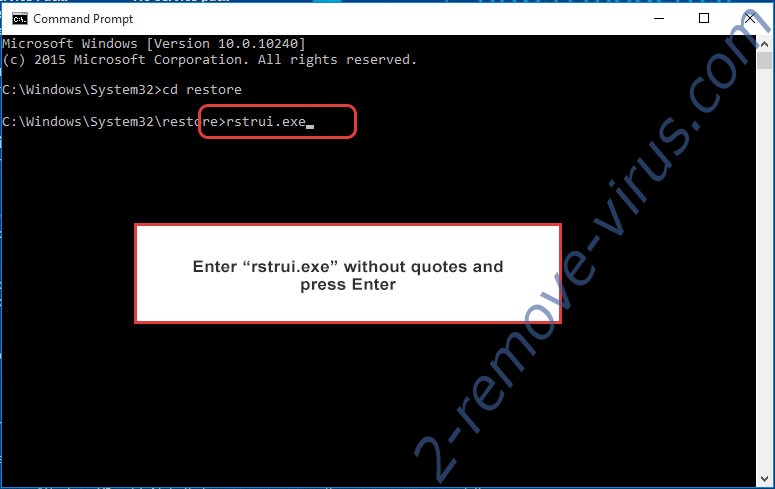
- Type in cd restore and tap Enter.

- Type in rstrui.exe and press Enter.

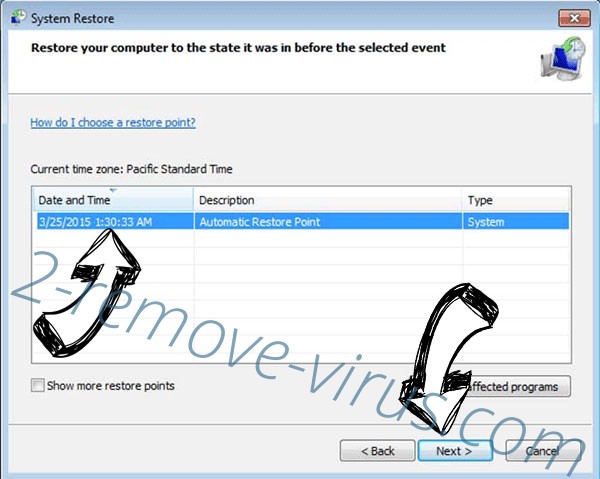
- Click Next in the new window and select the restore point prior to the infection.

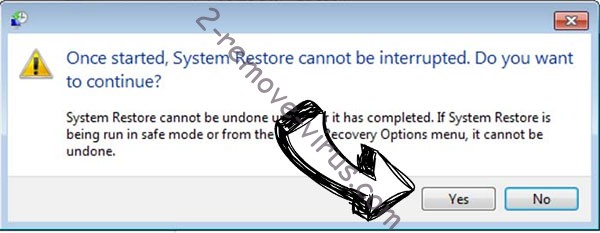
- Click Next again and click Yes to begin the system restore.

Delete Erqw ransomware from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.

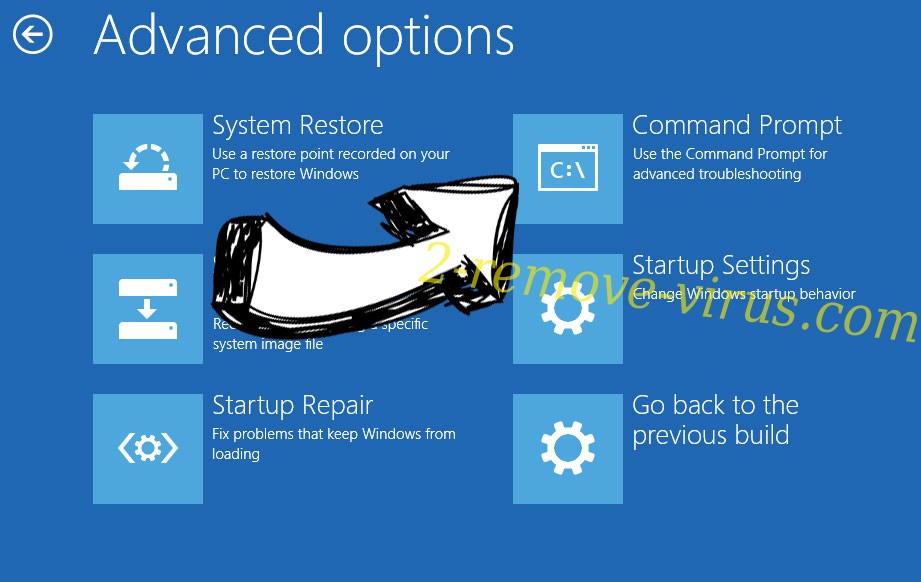
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

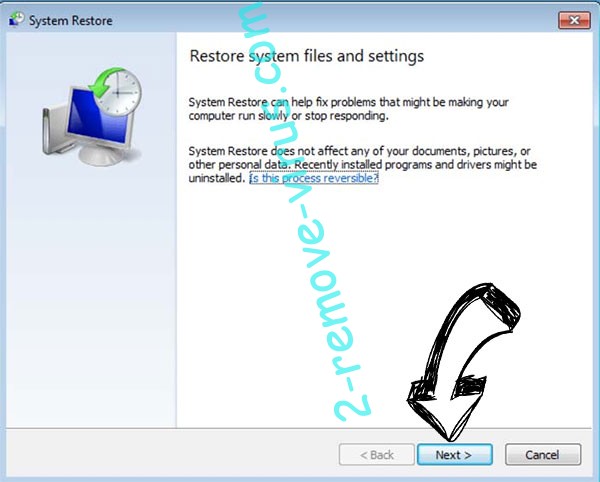
- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

- Click Next and then click Yes to restore your system.

Offers
Download Removal Toolto scan for Erqw ransomwareUse our recommended removal tool to scan for Erqw ransomware. Trial version of provides detection of computer threats like Erqw ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.