What is Hidden Bee trojan
If your anti-malware application is detecting something by the name Hidden Bee trojan, your device likely has a generic trojan in it. Trojans might bring about severe problems to your machine since they are not minor threats. Your information could be taken, other viruses could install, or you might end up with ransomware. 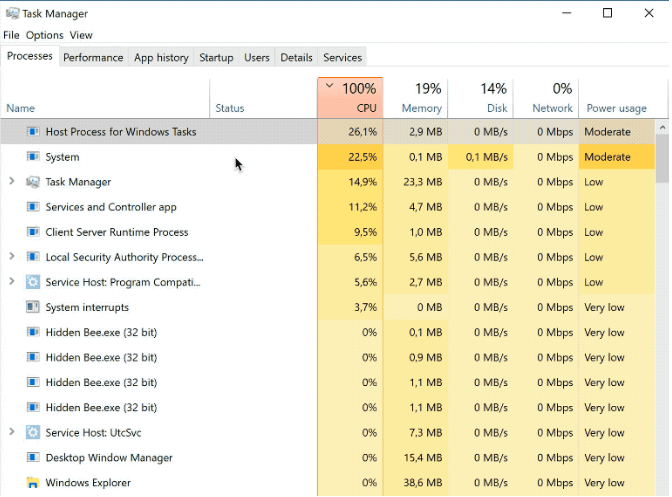
If your anti-malware software detects Hidden Bee trojan, you ought to deal with it quickly, as it is serious even if it is a generic trojan. The thing about these kinds of contaminations is that they attempt to evade notice for as long as possible. If the threat is not seen in time, it might steal your info, erase or take your files for hostage.
If you have a tendency to open spam emails, visit malicious pages or download pirated content from all kinds of web pages, your questionable browsing habits likely led to your device getting contaminated. After you delete Hidden Bee trojan, you might need to make alterations to how you browse the Internet.
Trojan spread methods
One of the more classic reasons users end up with trojans is because they use torrents to get free copyrighted content. Because of how simple it is to get malicious software this way, we suggest not using torrents.
It is also easy to contaminate machines with trojans if you tend to open spam email attachments. It’s often the case that those senders of those emails pretend to be from law enforcement or famous organizations and companies so as to put pressure on the user. Commonly, email receivers will be intimidated to open the file since it supposedly has info in relation to a highly sensitive matter. All it takes is opening the infected file for the malware to perform its malicious activities.
What does Hidden Bee trojan do
Hidden Bee trojan is how malware removal applications such as Kaspersky, ESET, Malwarebytes, TrendMicro, Windows Defender name certain generic trojans. Figuring out whether your computer is any actual danger is hard as the identification name doesn’t reveal much. One thing that may happen is the trojan getting access and stealing your files and documents. What’s troubling is this is that trojans work silently, meaning you not noticing anything amiss is not impossible.
Because of the already mentioned things, as well as the fact that the trojan may open a backdoor for other malware to enter, deal with the contamination quickly.
How to eliminate Hidden Bee trojan
Since you searched for a specific detection name that is used by malware removal software, it’s probably safe to presume you have a malware removal software installed. However, it is possible the program is not able to remove Hidden Bee trojan. It might be required to install a different anti-malware program for Hidden Bee trojan deletion or you might have to do everything yourself. Your anti-malware program may also be detecting something falsely, making Hidden Bee trojan a false detection.
Offers
Download Removal Toolto scan for Hidden Bee trojanUse our recommended removal tool to scan for Hidden Bee trojan. Trial version of provides detection of computer threats like Hidden Bee trojan and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
