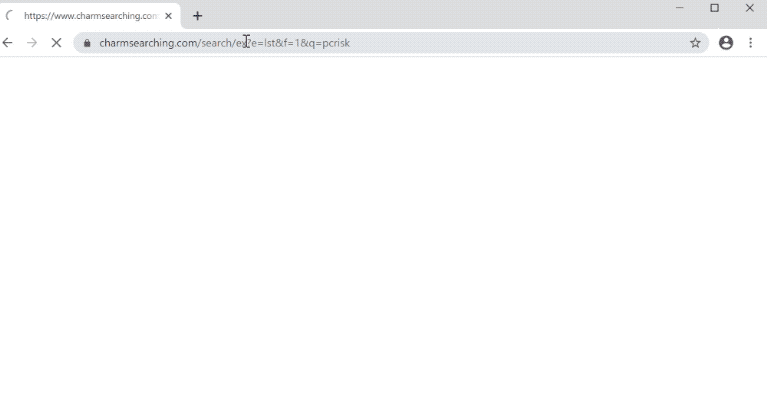
charmsearching.com is a fake search engine promoted by questionable programs like browser hijackers. If the site is loading every time you open your browser, you’re dealing with a browser hijacker, a minor infection that aims to expose users to sponsored/advertisement content. charmsearching.com browser hijacker is not particularly dangerous because it does not directly harm the computer. However, it will constantly redirect you and try to expose you to advertisement content. Furthermore, while it should not cause direct harm, hijackers can redirect to potentially dangerous websites that hide malware and promote scams. So if you notice this hijacker installed on your computer, you need to remove charmsearching.com sooner rather than later.
If all your searches are suddenly redirected to charmsearching.com and only then your usual search engine, your computer is indeed infected with a browser hijacker. These infections can usually affect all popular browsers, including Google Chrome, Mozilla Firefox, and Microsoft Edge. Once a hijacker is installed, it makes unwanted changes. Usually, that means an unknown website set as the homepage/new tabs, as well as a questionable search engine set as your default one. These changes are done without your permission and cannot be reversed as long as the hijacker is installed. So do not waste your time trying to undo the setting changes unless you first remove charmsearching.com browser hijacker.
The main goal of a browser hijacker is to promote fake search engines like charmsearching.com and generate revenue by redirecting users to questionable websites. When this hijacker is installed, whenever you do a search, you will be redirected to charmsearching.com briefly and then shown results with your usual search engine.
Do not click on the promoted results if you notice that a browser hijacker has taken control of your browser. The majority of them will only expose you to advertisements, but some of them might direct you to dangerous websites. You can be taken to websites that advertise scams or hide malware. There is no reason to interact with the sponsored results since such sites are usually in no way related to what you were searching for.
It’s also worth mentioning that browser hijackers monitor browsing and gather data. Your search history, websites you’ve visited, the content you’ve interacted with, your IP address, and other information will be collected. Despite not collecting any personal information, the hijacker’s data collection practices are intrusive enough to warrant removal, particularly because you get nothing in return. There’s really no need to put up with any kind of data collection from a browser hijacker.
Browser hijackers install using a deceptive method so that users don’t notice until it’s fully installed. Because of this, you likely do not recall installing it. The way that these programs are installed is through a method called software bundling. Anti-virus programs frequently flag apps that use software bundling as potential threats because it is a somewhat dubious and controversial method.
How do browser hijackers install on a computer?
Adware, browser hijackers, and potentially unwanted programs (PUPs) are some examples of infections that are bundled with free programs in a practice known as software bundling. It’s a deceptive installation method that, to put it simply, allows unwanted programs to be installed without your knowledge. So if charmsearching.com is your default search engine, you installed a free program that had a browser hijacker attached to it.
The mentioned infections can be attached to free programs as extra offers. They are technically optional but are preselected to install automatically, without requiring your explicit permission. The offers need to be manually deselected if you do not want them to install. The problem with this, however, is that the offers are concealed in settings that users don’t typically use. The offers will be hidden and allowed to install if users use Default options to install programs. Only those who select Advanced settings will be able to see what has been added to the program.
If Advanced settings show that something has been added to the program you’re installing, you need to deselect it. All offers should always be deselected because none of them will ever be useful to you. You would only be filling your computer with junk that causes issues to your device by allowing those installations. No legitimate program will ever use this installation method because it’s deceptive. Furthermore, programs that do use it are often detected as potential threats by anti-virus programs.
The charmsearching.com browser hijacker may also be promoted as a trustworthy browser extension that promises to improve your browsing experience. This type of advertising is common for browser hijackers. To avoid installing potentially harmful programs, it’s crucial to do your research before installation. Most of the time, a basic Google search is sufficient to identify whether a program is safe or not.
charmsearching.com removal
If charmsearching.com is constantly loading when you open your browser, you need to get rid of the browser hijacker. Only when the hijacker is no longer on your computer will you be able to remove charmsearching.com as the default search engine. The easiest way to delete charmsearching.com browser hijacker is to use an anti-virus program because the program would take care of everything. However, you can also do it manually, and instructions will be provided below.
Quick Menu
Step 1. Uninstall charmsearching.com browser hijacker and related programs.
Remove charmsearching.com browser hijacker from Windows 8
Right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel choose Programs and Features and select to Uninstall a software.

Uninstall charmsearching.com browser hijacker from Windows 7
Click Start → Control Panel → Programs and Features → Uninstall a program.

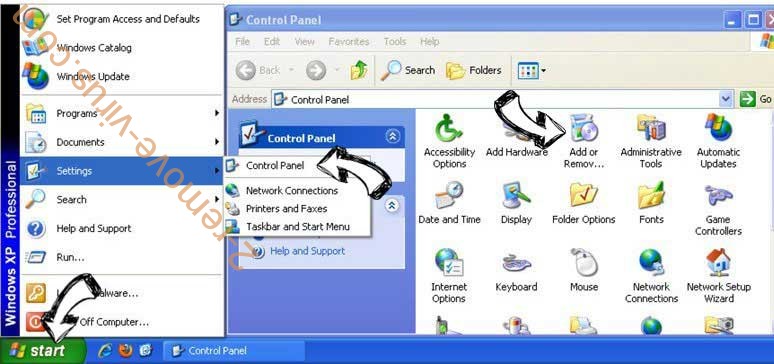
Delete charmsearching.com browser hijacker from Windows XP
Click Start → Settings → Control Panel. Locate and click → Add or Remove Programs.
Remove charmsearching.com browser hijacker from Mac OS X
Click Go button at the top left of the screen and select Applications. Select applications folder and look for charmsearching.com browser hijacker or any other suspicious software. Now right click on every of such entries and select Move to Trash, then right click the Trash icon and select Empty Trash.

Step 2. Delete charmsearching.com browser hijacker from your browsers
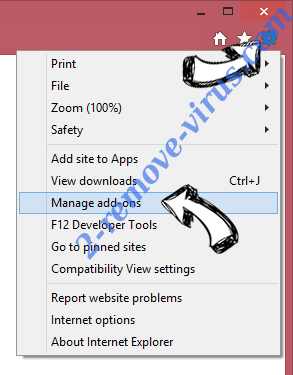
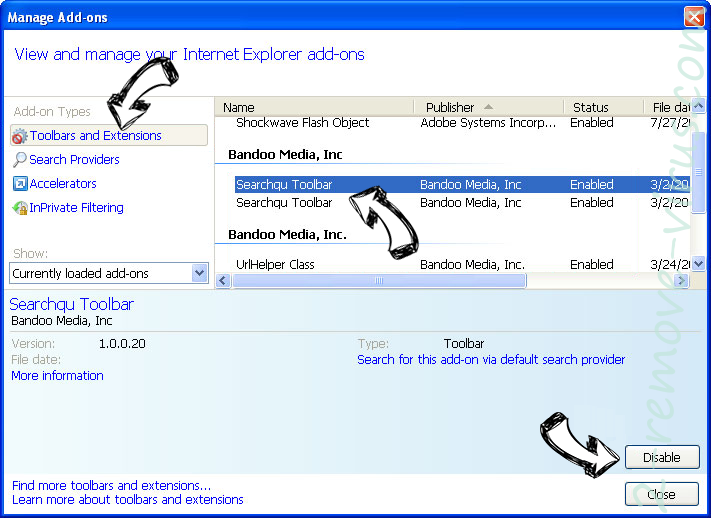
Terminate the unwanted extensions from Internet Explorer
- Tap the Gear icon and go to Manage Add-ons.

- Pick Toolbars and Extensions and eliminate all suspicious entries (other than Microsoft, Yahoo, Google, Oracle or Adobe)

- Leave the window.
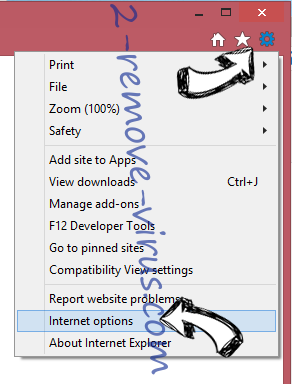
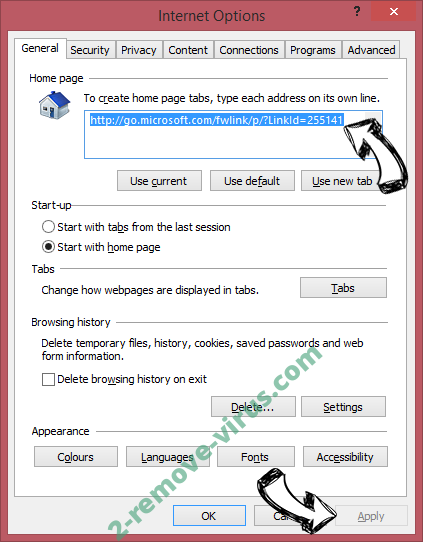
Change Internet Explorer homepage if it was changed by virus:
- Tap the gear icon (menu) on the top right corner of your browser and click Internet Options.

- In General Tab remove malicious URL and enter preferable domain name. Press Apply to save changes.

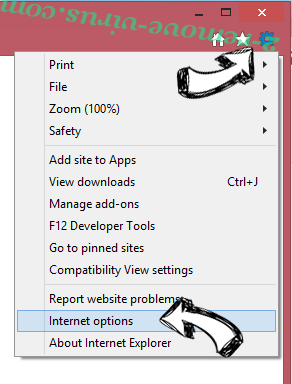
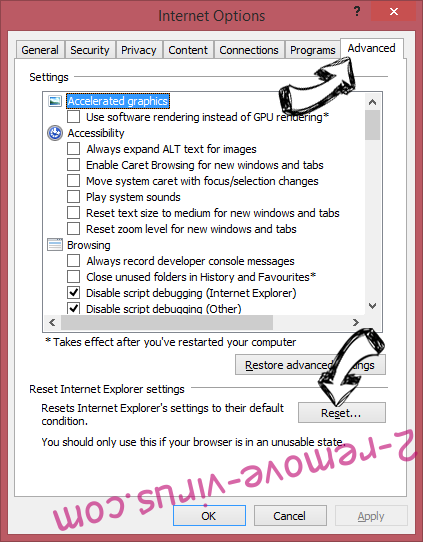
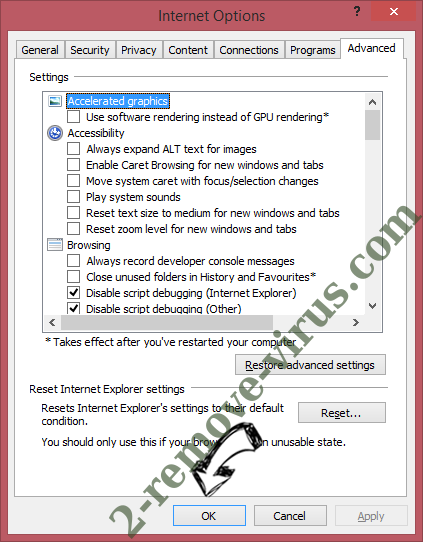
Reset your browser
- Click the Gear icon and move to Internet Options.

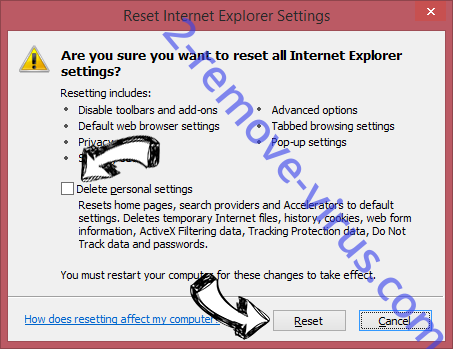
- Open the Advanced tab and press Reset.

- Choose Delete personal settings and pick Reset one more time.

- Tap Close and leave your browser.

- If you were unable to reset your browsers, employ a reputable anti-malware and scan your entire computer with it.
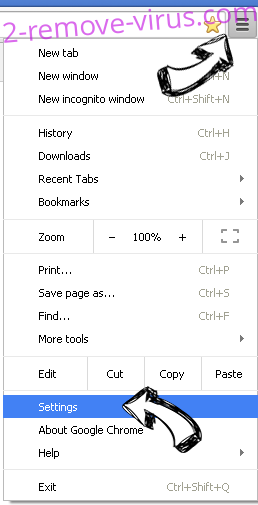
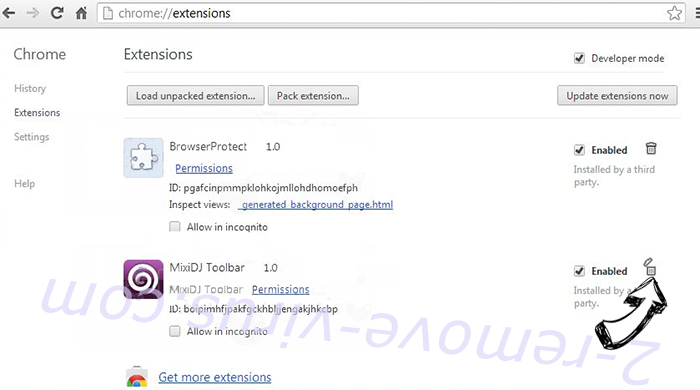
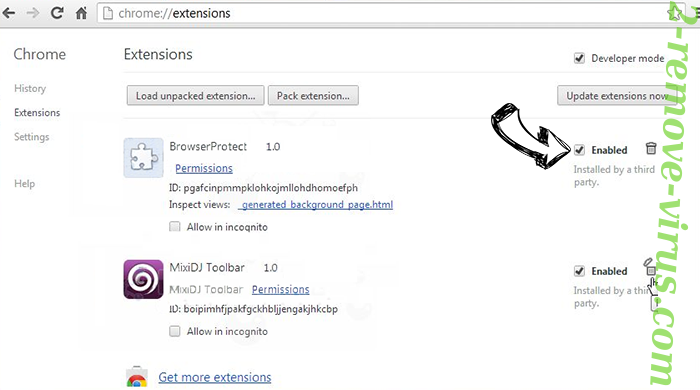
Erase charmsearching.com browser hijacker from Google Chrome
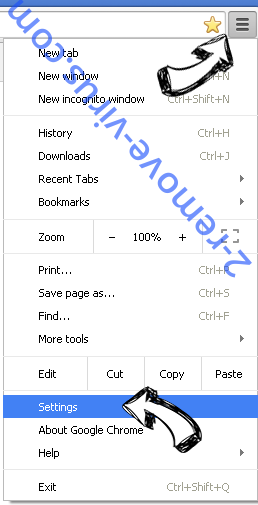
- Access menu (top right corner of the window) and pick Settings.

- Choose Extensions.

- Eliminate the suspicious extensions from the list by clicking the Trash bin next to them.

- If you are unsure which extensions to remove, you can disable them temporarily.

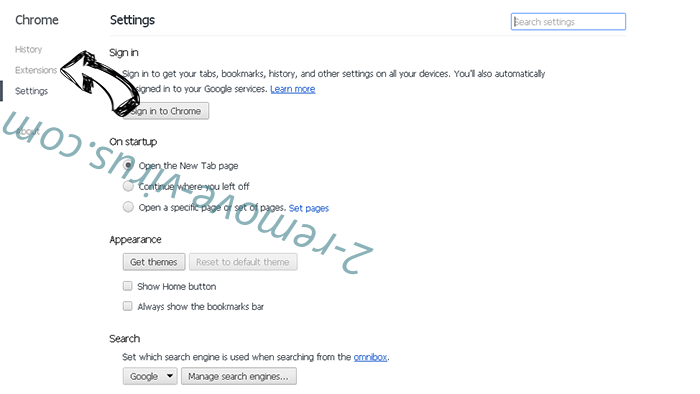
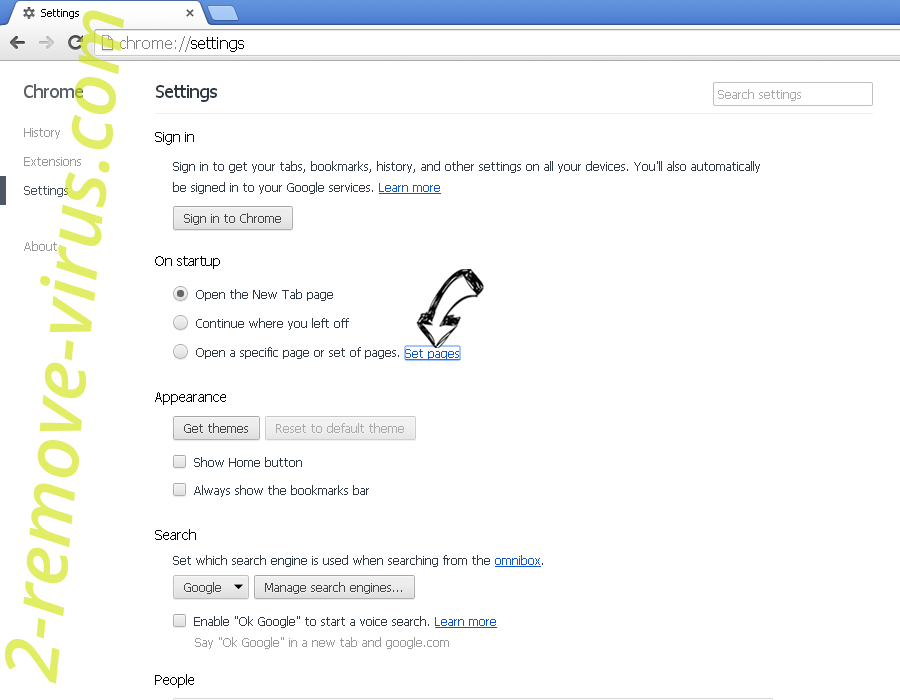
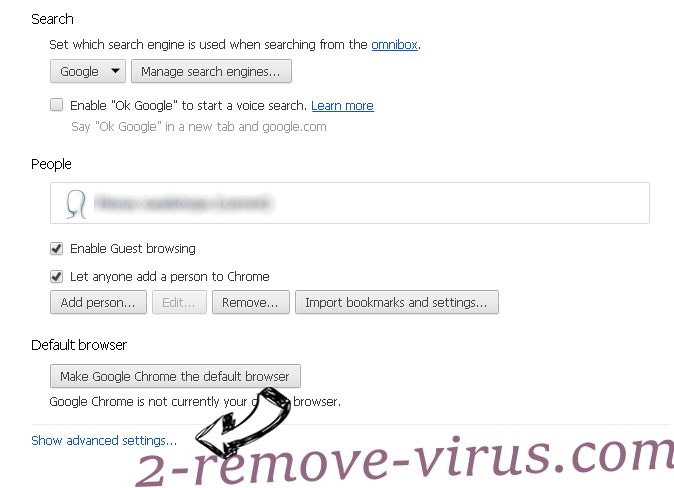
Reset Google Chrome homepage and default search engine if it was hijacker by virus
- Press on menu icon and click Settings.

- Look for the “Open a specific page” or “Set Pages” under “On start up” option and click on Set pages.

- In another window remove malicious search sites and enter the one that you want to use as your homepage.

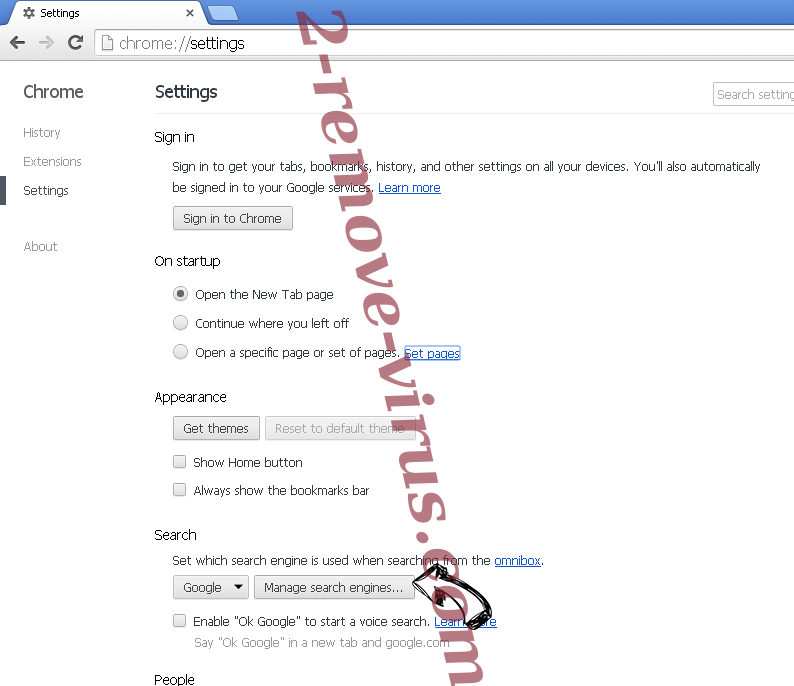
- Under the Search section choose Manage Search engines. When in Search Engines..., remove malicious search websites. You should leave only Google or your preferred search name.


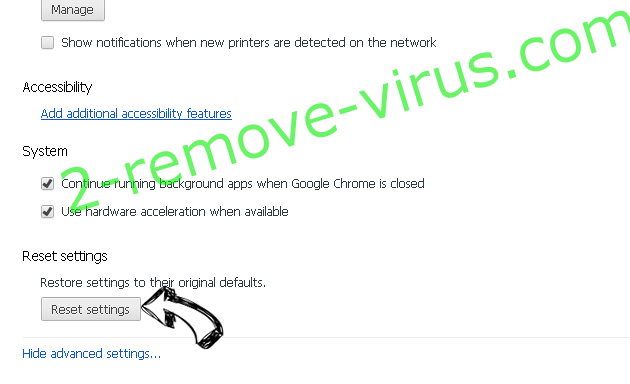
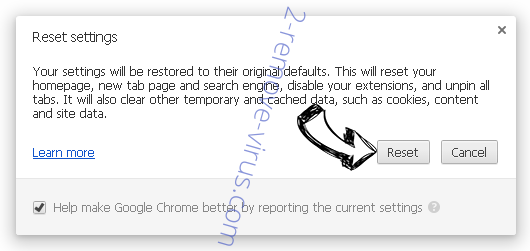
Reset your browser
- If the browser still does not work the way you prefer, you can reset its settings.
- Open menu and navigate to Settings.

- Press Reset button at the end of the page.

- Tap Reset button one more time in the confirmation box.

- If you cannot reset the settings, purchase a legitimate anti-malware and scan your PC.
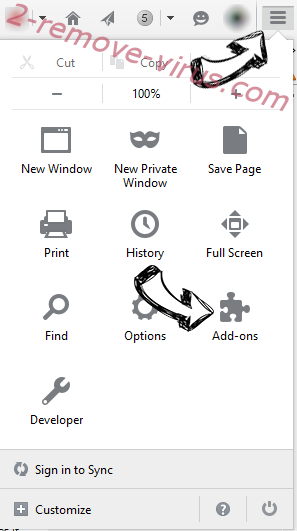
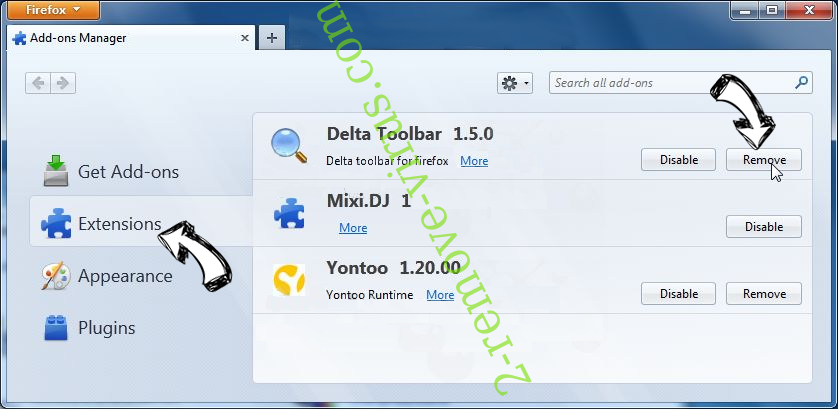
Remove charmsearching.com browser hijacker from Mozilla Firefox
- In the top right corner of the screen, press menu and choose Add-ons (or tap Ctrl+Shift+A simultaneously).

- Move to Extensions and Add-ons list and uninstall all suspicious and unknown entries.

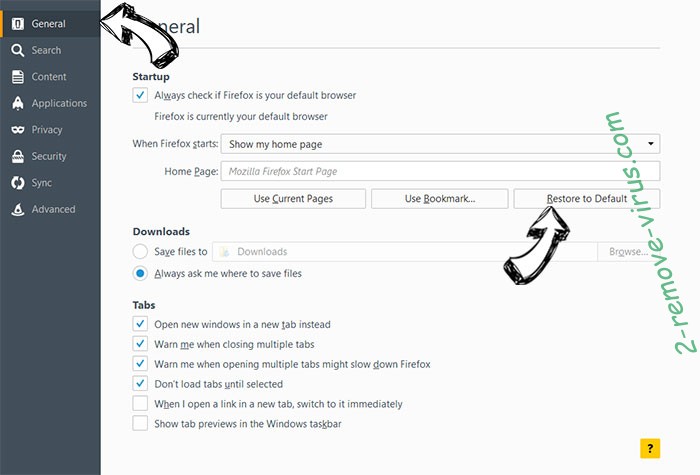
Change Mozilla Firefox homepage if it was changed by virus:
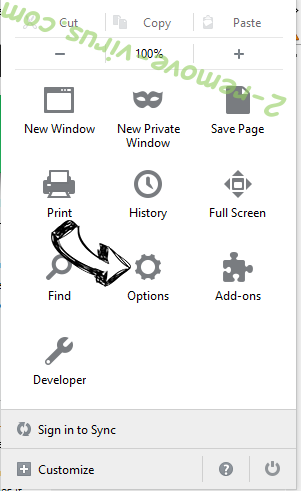
- Tap on the menu (top right corner), choose Options.

- On General tab delete malicious URL and enter preferable website or click Restore to default.

- Press OK to save these changes.
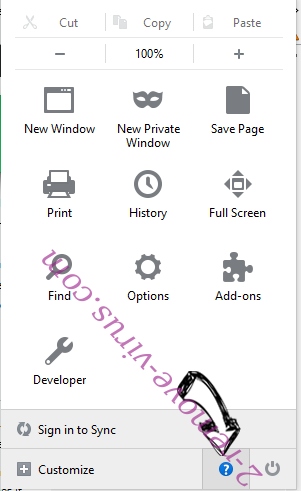
Reset your browser
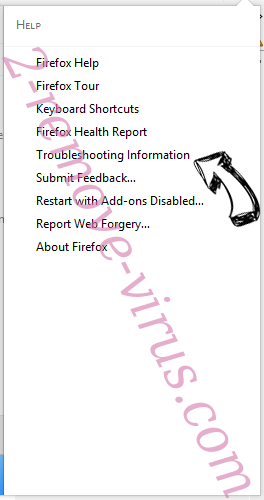
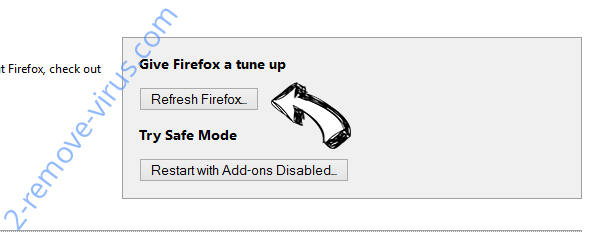
- Open the menu and tap Help button.

- Select Troubleshooting Information.

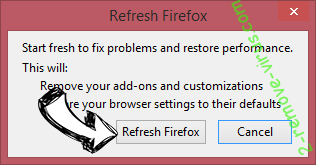
- Press Refresh Firefox.

- In the confirmation box, click Refresh Firefox once more.

- If you are unable to reset Mozilla Firefox, scan your entire computer with a trustworthy anti-malware.
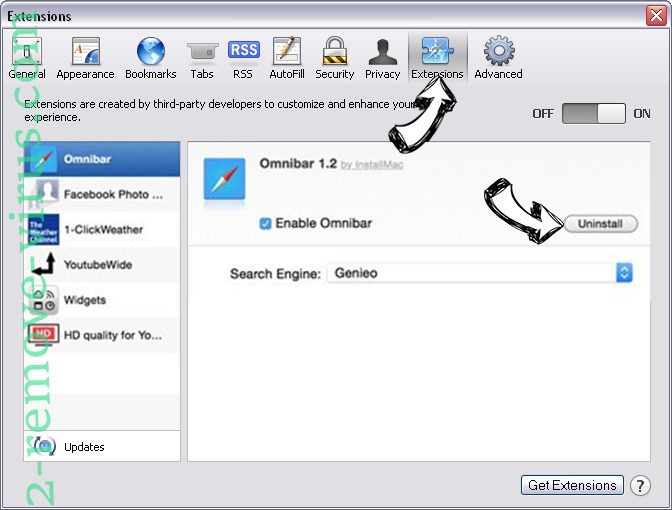
Uninstall charmsearching.com browser hijacker from Safari (Mac OS X)
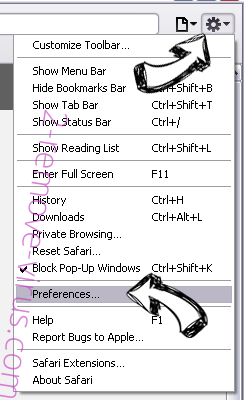
- Access the menu.
- Pick Preferences.

- Go to the Extensions Tab.

- Tap the Uninstall button next to the undesirable charmsearching.com browser hijacker and get rid of all the other unknown entries as well. If you are unsure whether the extension is reliable or not, simply uncheck the Enable box in order to disable it temporarily.
- Restart Safari.
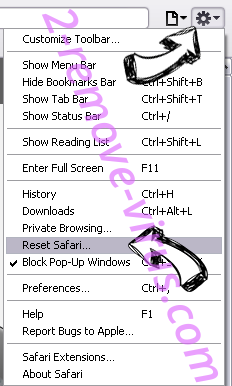
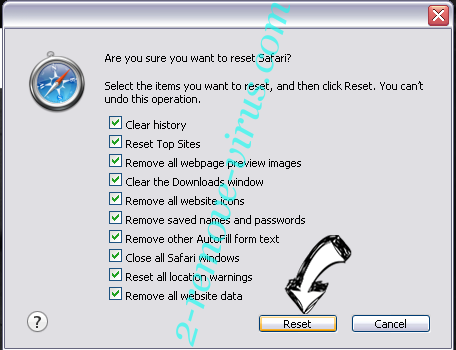
Reset your browser
- Tap the menu icon and choose Reset Safari.

- Pick the options which you want to reset (often all of them are preselected) and press Reset.

- If you cannot reset the browser, scan your whole PC with an authentic malware removal software.
Offers
Download Removal Toolto scan for charmsearching.com browser hijackerUse our recommended removal tool to scan for charmsearching.com browser hijacker. Trial version of provides detection of computer threats like charmsearching.com browser hijacker and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.