njRat (also known as Bladabindi) is a remote access trojan (RAT) that essentially allows the operators complete access to an end user’s computer. It was first discovered almost a decade ago but it makes a major reemergence from time to time. It’s a very serious infection that has a wide range of capabilities, depending on what the main goal of the trojan operator is.

njRat is a remote access trojan, which essentially means it gives cybercriminals access to the infected device. It has a wide range of capabilities, including killing processes, changing the system registry, making recordings using the device’s camera and microphone, logging keystrokes, stealing passwords, changing/manipulating files, opening a remote shell, etc.
These types of trojans are designed to be as stealthy as possible in order to avoid detection, especially when no anti-virus software is present on the computer. This makes them especially dangerous infections. A trojan could hide on a computer for a very long time before users notice its presence.
The njRat trojan could be programmed to steal passwords and log keystrokes, and this is one of the most dangerous features. It could display fake windows when you’re trying to log in to some account, or it could simply log the keyboard strokes. Either way, passwords would be transferred to the cybercriminals operating the trojan. Stolen passwords often end up being sold on various hacker forums.
njRat could also essentially open a backdoor for other malicious infections to get in. For example, if you could download a ransomware infection that would encrypt all personal files and later demand money in exchange for a decryptor. The trojan could lie dormant until some cybercriminal buys access to infected devices to download ransomware onto them.
To summarise, remote access trojans like njRat are incredibly dangerous because they essentially give malicious actors control over an infected device. This could result in spying, stolen files/data, stolen passwords/other sensitive data, identity theft, additional malware infections, etc. Furthermore, the trojan may not exhibit any noticeable signs of being present in order to delay detection. And considering the stealthy methods it uses for infection, users may not notice its presence for a long time. This is why it’s important to have anti-virus programs installed.
How is njRat trojan distributed?
Remote access trojans like njRat can be distributed using many methods. It can be disguised as a fake update (e.g. Adobe Flash Player), or it can be spread through phishing and spam campaigns. In any case, an infection can be avoided in most cases if users have good browsing habits and learn to recognize malicious campaigns.
Malware is often distributed via emails. Cybercriminals use leaked email addresses to launch malicious spam campaigns. When someone opens a malicious email attachment, malware can initiate. These kinds of campaigns are incredibly common so users always need to be very careful with unsolicited emails from unknown senders. But such emails are usually easy to recognize unless they target someone specific. In most cases, one of the biggest giveaways of a malicious email is grammar/spelling mistakes. Senders usually claim to be from know companies so the grammar/spelling mistakes are a dead giveaway. For example, if you receive an email from someone claiming to be the bank but the email itself is full of mistakes, it’s 100% a malicious email. Another sign of a malicious email is users being addressed with generic words like “User”, “Member”, and “Customer” when the sender should know their name. If, for example, you receive an email from a company whose service you use but you are addressed with a generic word, you are likely dealing with a malicious/spam email.
When someone is targeted specifically, the email would be much more sophisticated. It would not have any grammar/spelling mistakes, address the potential victim by name, as well as contain some details that would make the email seem more credible. Because of this, it’s important to scan all unsolicited email attachments with anti-virus software or at least VirusTotal before opening them.
Malware can also be distributed via fake downloads. njRat, in particular, was spread using a fake Adobe Flash Player update download. Certain high-risk websites (or hacked sites) often display fake alerts claiming you need to install an update. For most users, these fake updates are quite easy to recognize. We think it’s necessary to caution users that they should not download anything from ads. If an update is needed, the program itself would either do it automatically or prompt you via the program. You will never get an update alert in your browser unless it’s for your browser or some browser extension. You should also only download updates from official websites.
Lastly, trojans like njRat can also be spread through torrents. Torrents are a major malware hub, especially torrents for entertainment content like video games, movies, and TV series. Last year, njRat was discovered to spread via torrents for game installers. Torrent websites are quite often poorly moderated, and this allows malicious actors to upload torrents with malware. If you do not know how to recognize torrents with malware in them, you have a very serious risk of picking up a serious malware infection. And it may not be immediately obvious that malware is present on a computer.
njRat removal
njRat is a very sophisticated infection and should be removed using professional software. You may not even notice its presence without an anti-virus program. This is why it’s important to have one installed. At the very least, you should have Microsoft Defender enabled.
As we’ve already explained, njRat has a variety of features so depending on what it did on your device, you may need to take additional actions. As a precaution, you should change all your passwords because the trojan also has keystroke logging capabilities.
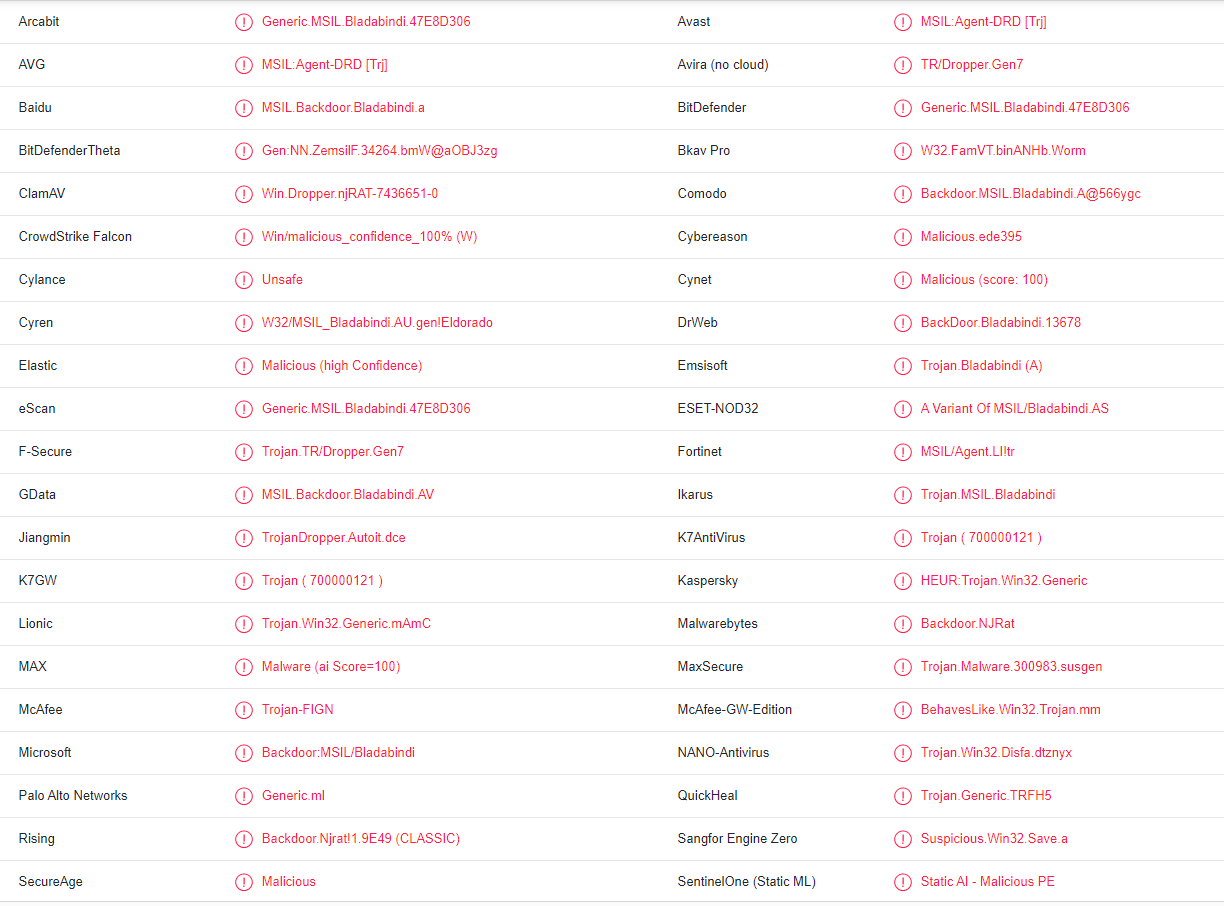
Files that are infected with njRat are detected by the majority of anti-virus programs:
- MSIL:Agent-DRD [Trj] by AVG/Avast
- Trojan-FIGN by McAfee
- Backdoor:MSIL/Bladabindi by Microsoft
- BKDR_BLADABI.SMC by TrendMicro
- Backdoor.NJRat by Malwarebytes
- HEUR:Trojan.Win32.Generic by Kaspersky
- A Variant Of MSIL/Bladabindi.AS by ESET
- Generic.MSIL.Bladabindi.47E8D306 by BitDefender
Offers
Download Removal Toolto scan for njRat trojanUse our recommended removal tool to scan for njRat trojan. Trial version of provides detection of computer threats like njRat trojan and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete njRat trojan using Safe Mode with Networking.
Remove njRat trojan from Windows 7/Windows Vista/Windows XP
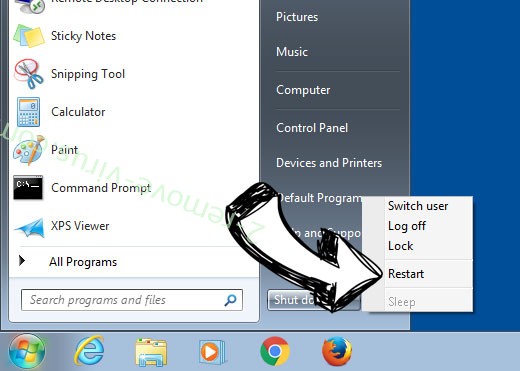
- Click on Start and select Shutdown.
- Choose Restart and click OK.

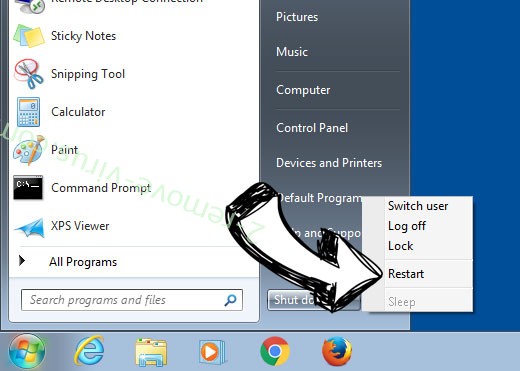
- Start tapping F8 when your PC starts loading.
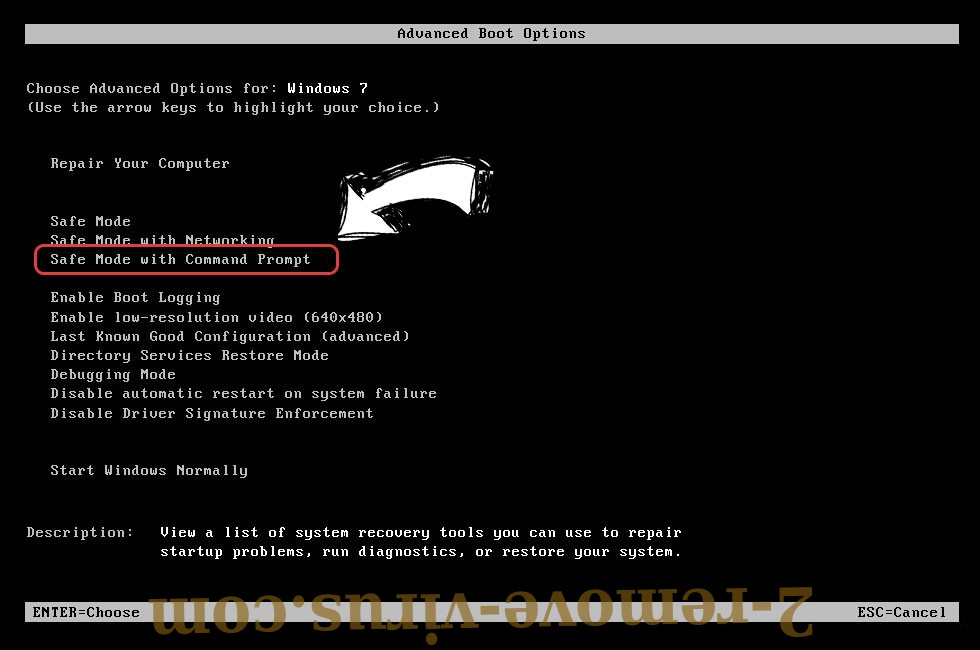
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove njRat trojan
Remove njRat trojan from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.


- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

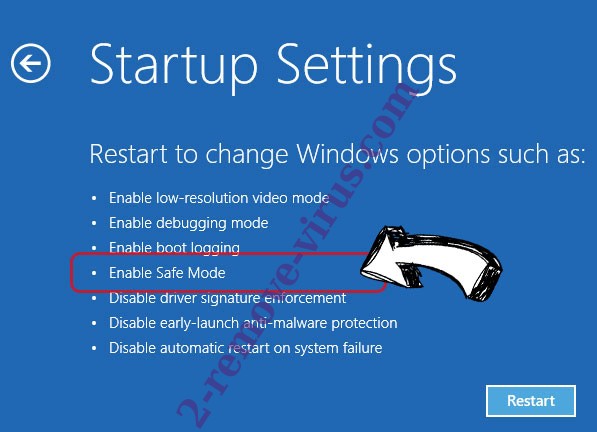
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete njRat trojan
Step 2. Restore Your Files using System Restore
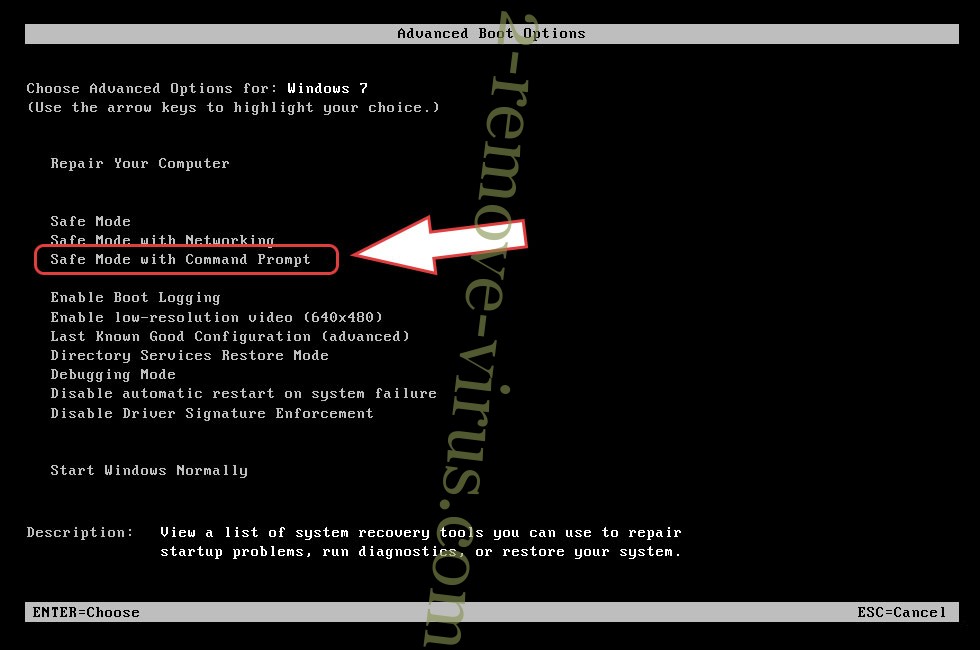
Delete njRat trojan from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
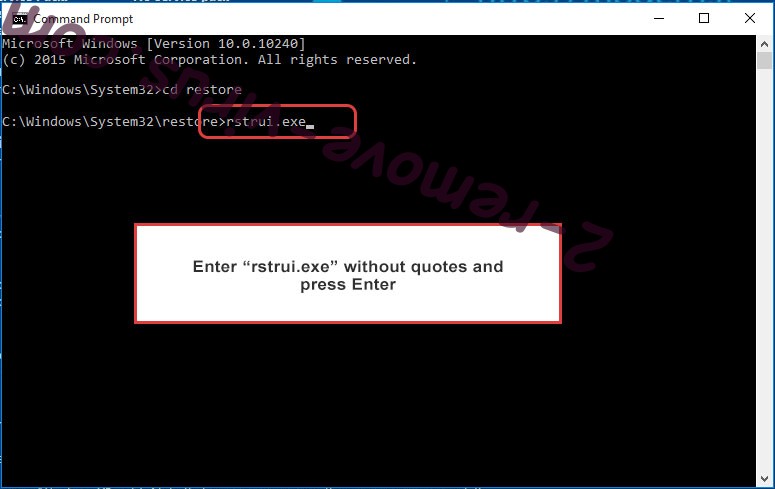
- Choose Command Prompt from the list.

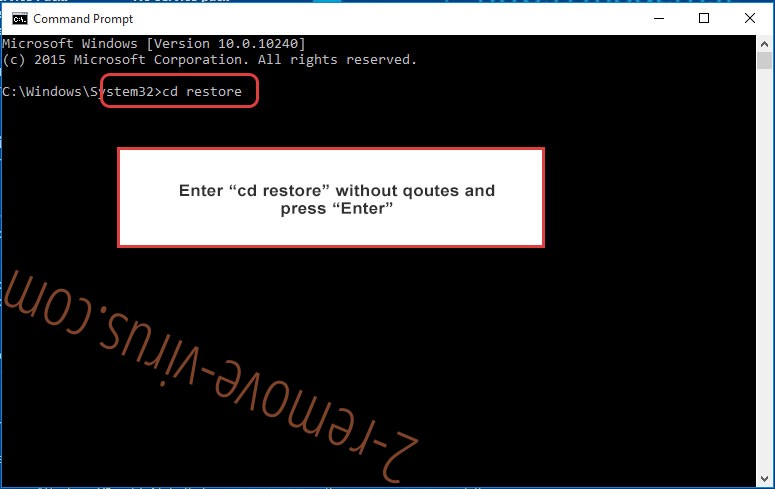
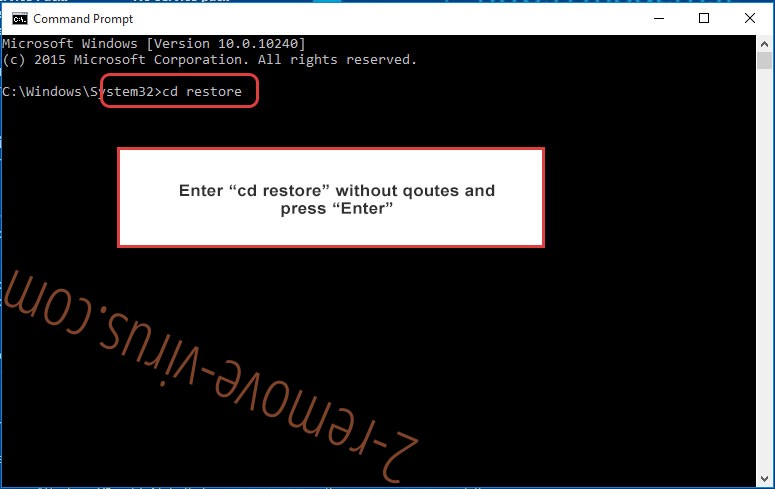
- Type in cd restore and tap Enter.

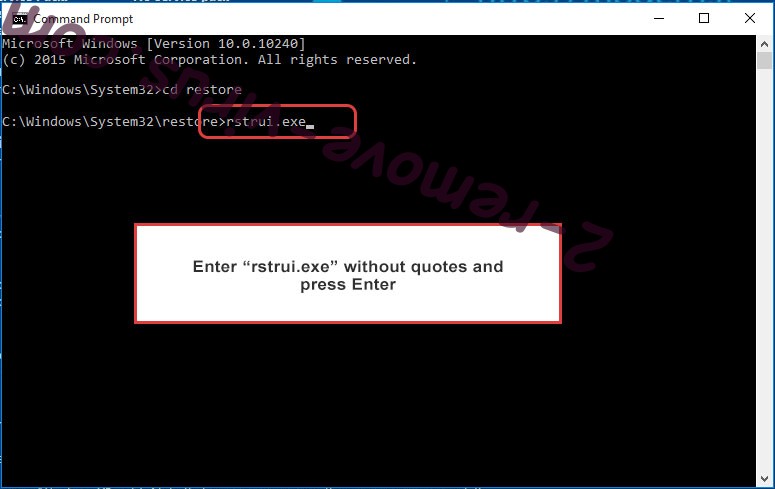
- Type in rstrui.exe and press Enter.

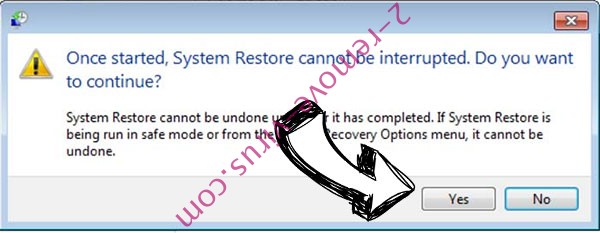
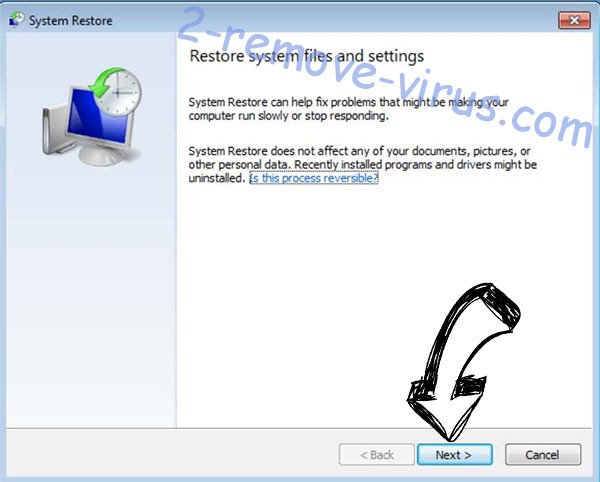
- Click Next in the new window and select the restore point prior to the infection.

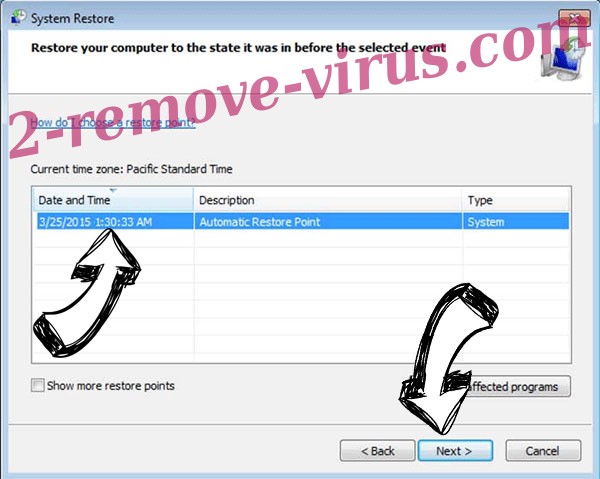
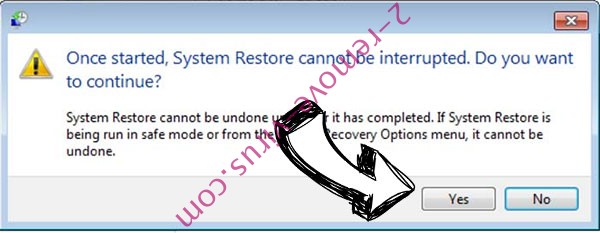
- Click Next again and click Yes to begin the system restore.

Delete njRat trojan from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.


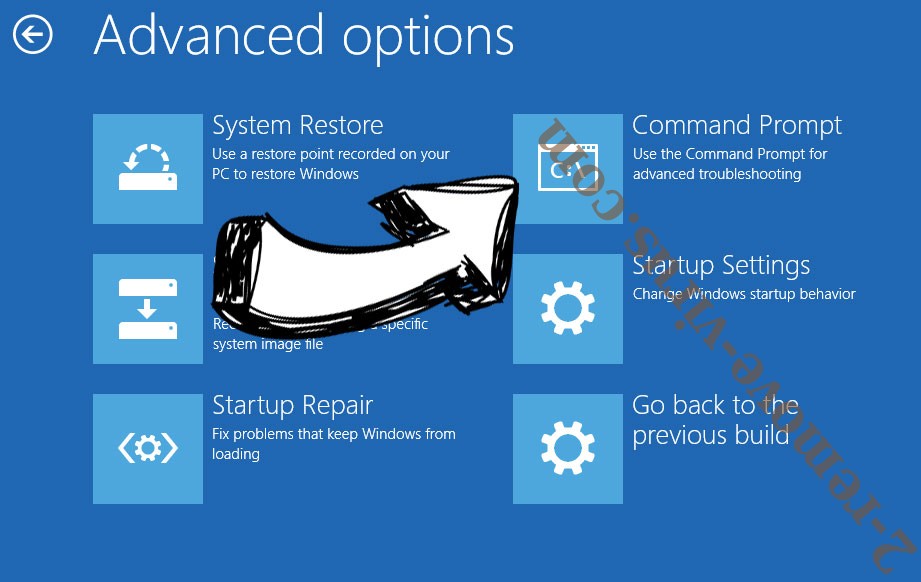
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

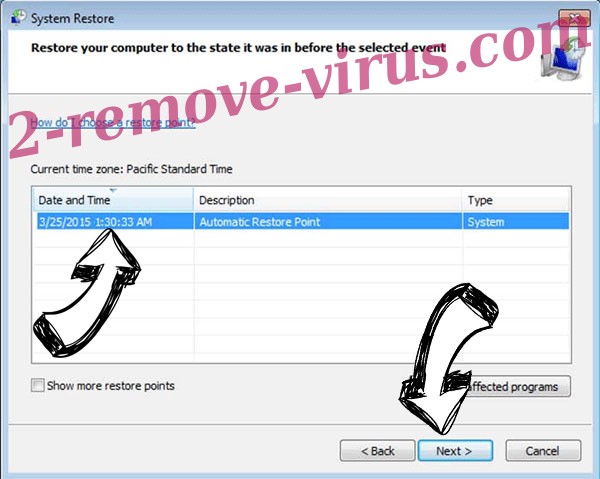
- Click Next and then click Yes to restore your system.

Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.