What is CamuBot Trojan?
CamuBot Trojan is a highly dangerous piece of financial malware that is targeting Brazilian business-class bank customers. The malware attempts to camouflage itself as a supposedly mandatory bank security module, which is where its name CamuBot comes from. According to Security Intelligence, the Trojan first emerged in August 2018, and unlike the typical banking Trojan, CamuBot does not hide its deployment. Instead, it tricks the target into thinking it’s a security module for a bank, so people end up installing the Trojan themselves. This is a rather unusual infection method as it needs to target very specific people, who are hand-picked by the attackers. The hand-picked victims are contacted by phone and tricked into installing the malware. 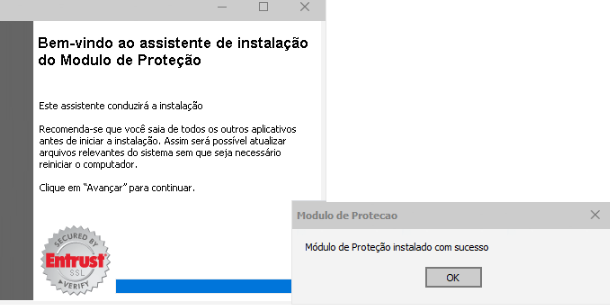
The attackers behind this malware campaign aim to trick business owners/employees into installing a banking Trojan, disguised as a security module for using online banking. The fake security module even has official logos and branding that will further convince potential victims that it’s legitimate. When the malware is installed, victims are then tricked into putting online banking credentials into a fake websites, which reveals those credentials to the attackers. The malware can even hijack one-time bank-generated passwords.
“The unique malware circumvents online banking authentication processes by installing a driver that will allow the remote sharing of authentication devices associated with victims’ computer. Once they trick victims into giving them remote access to authentication devices, they can hijack one-time bank-generated passwords and gain access to the victims’ online banking accounts to steal money,” Trend Micro disclose.
While the attack is highly sophisticated, it would be difficult to execute it successfully. People who have access to business online bank accounts should surely be trained in cybersecurity, thus it’s unlikely they would fall for the phishing phone calls used in these attacks. And even if attackers were successful in tricking the victims, most computers have anti-malware installed and it would detect and uninstall CamuBot Trojan immediately.
How are targets infected?
The attackers use a very unusual way of infecting victims, and that is phishing phone calls. Trend Micro reports that the attackers likely use social media, search engines and even the phone directory to look for targets (business employees or owners) who have access to online business banking. The targets would then be contacted by the attackers via phone, pretending to be bank employees, and directed to fake verification websites. The attackers would claim that the bank’s “security module” needs to updated, and potential victims would then be guided into downloading the supposed security module, which is actually disguised malware.
Victims would be advised to install the supposed ‘security module’ with a Windows administrator profile. If the victims fell for this phishing attempt, the installation will not cause suspicion as it has all the necessary bank logos and branding, making it seem fully legitimate. What the victim is actually installing is the CamuBot banking Trojan.
When the malware is successfully installed, a pop-up will appear and ask the victim to log in to his/her online bank account. The pop-up may look identical to the legitimate online banking site so the victim would not realize that they are giving away their online banking credentials to malicious actors.
Targets are likely hand-picked by attackers, and currently are strictly people residing in Brazil. Attackers would pick business owners or employees that they think would have access to online bank accounts. Attacks like this are why educating employees about cybersecurity is so important. All employees that have access to an online business bank account should be aware that banks would not call them this way and ask to install some kind of software. And if in doubt, people should drop the call and call the bank using its official numbers to inquire about this supposed update.
CamuBot Trojan removal
If anti-malware is installed on a computer that is trying to install the supposed ‘security module’, it should notify the user about it being malicious. This just goes to show how necessary anti-malware software is in some cases. When human error leads to a potentially serious situation, security software can help solve it. It would detect and delete CamuBot Trojan before it can actually do anything.
If you realize that you have recently received an unusual phone call asking to install something from someone claiming to be a bank employee, you might now need to remove CamuBot Trojan and contact your bank immediately.
According to VirusTotal, the malware is detected by 32 different anti-malware programs, some of which detect CamuBot as:
- TrojanSpy.Win32.CAMUBOT.A by Trend Micro;
- Trojan-Dropper.Win32.Agent.bjwcrp by Kaspersky;
- Trojan:Win32/Bitrep.A by Microsoft;
- Trojan.Dropper by Symantec;
- Artemis!684AAA16C9B5 by McAfee;
- Win32:Malware-gen by Avast and AVG.
Offers
Download Removal Toolto scan for CamuBot TrojanUse our recommended removal tool to scan for CamuBot Trojan. Trial version of provides detection of computer threats like CamuBot Trojan and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
