Lkfr ransomware belongs to the Djvu/STOP ransomware family. It’s file-encrypting malware that targets personal files, encrypts them, and demands payment for their recovery. It’s a dangerous piece of malware because file recovery is not always guaranteed.
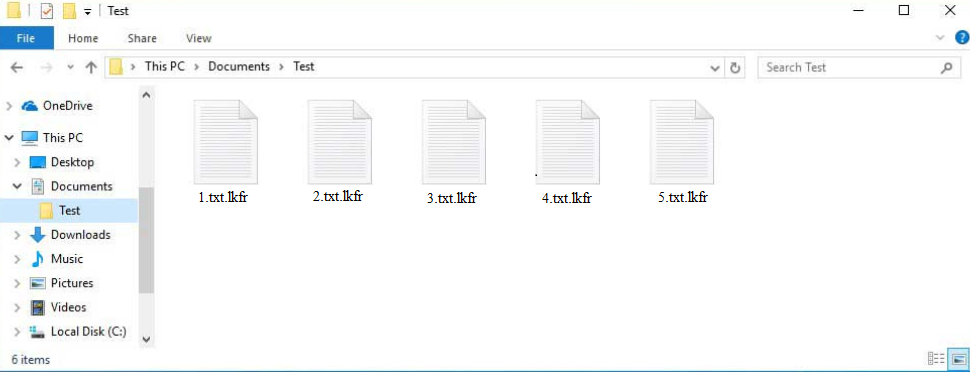
When the infected file is opened, the ransomware initiates and starts the encryption process. During the encryption process, the ransomware will display a fake Windows update window to distract users. In the meantime, it will encrypt all personal files, including photos, videos, documents, etc. Users can recognize which files have been affected by looking for the .lkfr extension. For example, a text.txt file would become text.txt.lkfr if encrypted.
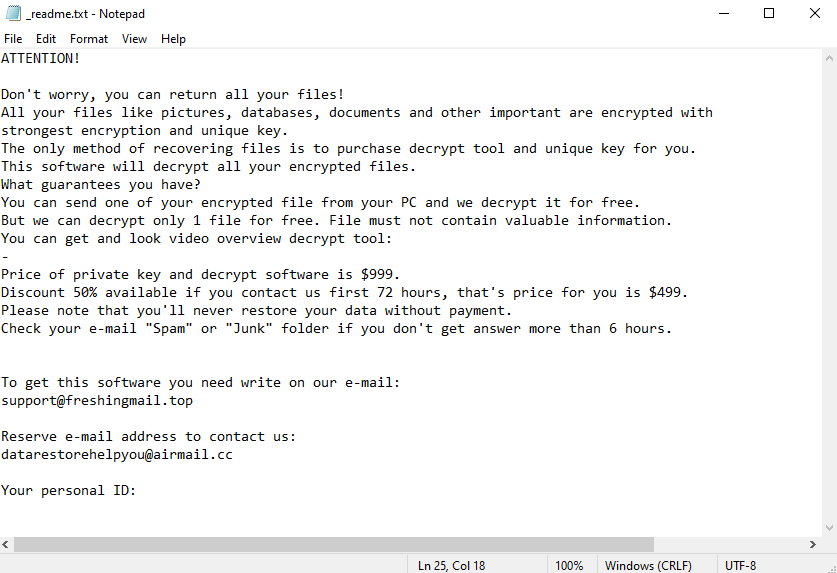
None of the encrypted files will be openable. To open them, they first need to be put through a decryptor. However, obtaining the decryptor will not be easy. The _readme.txt ransom note explains how users can buy it.
According to the note, a decryptor costs $999, to be paid in Bitcoin. However, there’s supposedly a 50% discount for users who contact the malware operators within the first 72 hours. The note also mentions that one file can be decrypted for free as long as it does not contain any important information.
Below is the full Lkfr ransomware ransom note:
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
–
Price of private key and decrypt software is $999.
Discount 50% available if you contact us first 72 hours, that’s price for you is $499.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
When it comes to ransomware, paying the ransom is never recommended. There are several reasons for this. First of all, paying does not guarantee a decryptor. Ransomware operators are cybercriminals, they do not operate like a business. Even if users pay, there is nothing to force them to send the decryptor. Many ransomware victims have paid for decryptors but failed to receive anything. It should also be mentioned that as long as users pay money, ransomware will thrive. Their money is used to support criminal activities.
File backup can be accessed as soon as users remove Lkfr ransomware from their computers. It’s strongly recommended to use a reliable anti-malware program instead of trying to delete Lkfr ransomware manually. Once the ransomware is fully removed, users can safely connect to their backup.
For users who have no backup, a free Lkfr ransomware decryptor developed by malware researchers is the only option. However, it’s not certain that such a decryptor will be released. If it does, it will be posted on NoMoreRansom. If a decryptor cannot be found there, it likely does not exist.
How does ransomware infect computers?
Like any other ransomware, Lkfr ransomware is distributed via methods like spam email attachments, torrents, malicious ads, etc. Because they’re less likely to engage in risky online behavior, users with good browsing habits tend to encounter malware much less compared to users with poor habits. Developing better habits is one of the best ways to avoid an infection.
Email attachments are one of the most common ways for ransomware distribution. Malicious files are attached to emails, and when they’re opened, the malware can initiate. Fortunately for users, malicious emails are not particularly difficult to recognize. They are disguised to look like emails sent by companies whose services users supposedly use. It could be a fake parcel delivery service, government agency, tax services, etc. The emails create a sense of urgency by claiming that the attached files are important documents that have sensitive information and need to be opened immediately. The emails may also be fake purchase notification emails. However, for one reason or another, they are usually full of grammar and spelling mistakes, which immediately give them away.
When users receive an unsolicited email with an attachment, they should always take note of how they are addressed. If it’s a legitimate email from a company whose services users use, users will be addressed by name. Malicious emails use generic words like User, Member, Customer, etc. because they target a large number of users with the same email.
It’s also worth mentioning that emails that target specific users will be much more sophisticated. They will address the user by name and contain specific information to make the email seem more credible. Thus, it’s always recommended to scan all unsolicited email attachments with anti-malware software or VirusTotal.
Torrents are also a popular way to spread malware like ransomware. Torrent sites are poorly moderated, which means that torrents with malware in them are often uploaded and stay up for a long time. It’s common to find malware in torrents for entertainment content, including in torrents for movies, TV series, and video games. We strongly discourage users from downloading copyrighted content using torrents because it’s not only content theft but also dangerous.
How to remove Lkfr ransomware
If you have a backup of your files, before you start file recovery, you need to remove Lkfr ransomware from your computer. We strongly recommend using a reliable anti-malware program to do this because ransomware is a complex infection. Unfortunately, removing the ransomware will not result in decrypted files because a specific Lkfr ransomware decryptor is necessary.
Once you remove Lkfr ransomware fully, you can access your backup and start recovering files. If you do not have a backup, your only option may be to wait for a free Lkfr ransomware to become available. Whether it will be released is not clear but if it does, it will be found on NoMoreRansom.
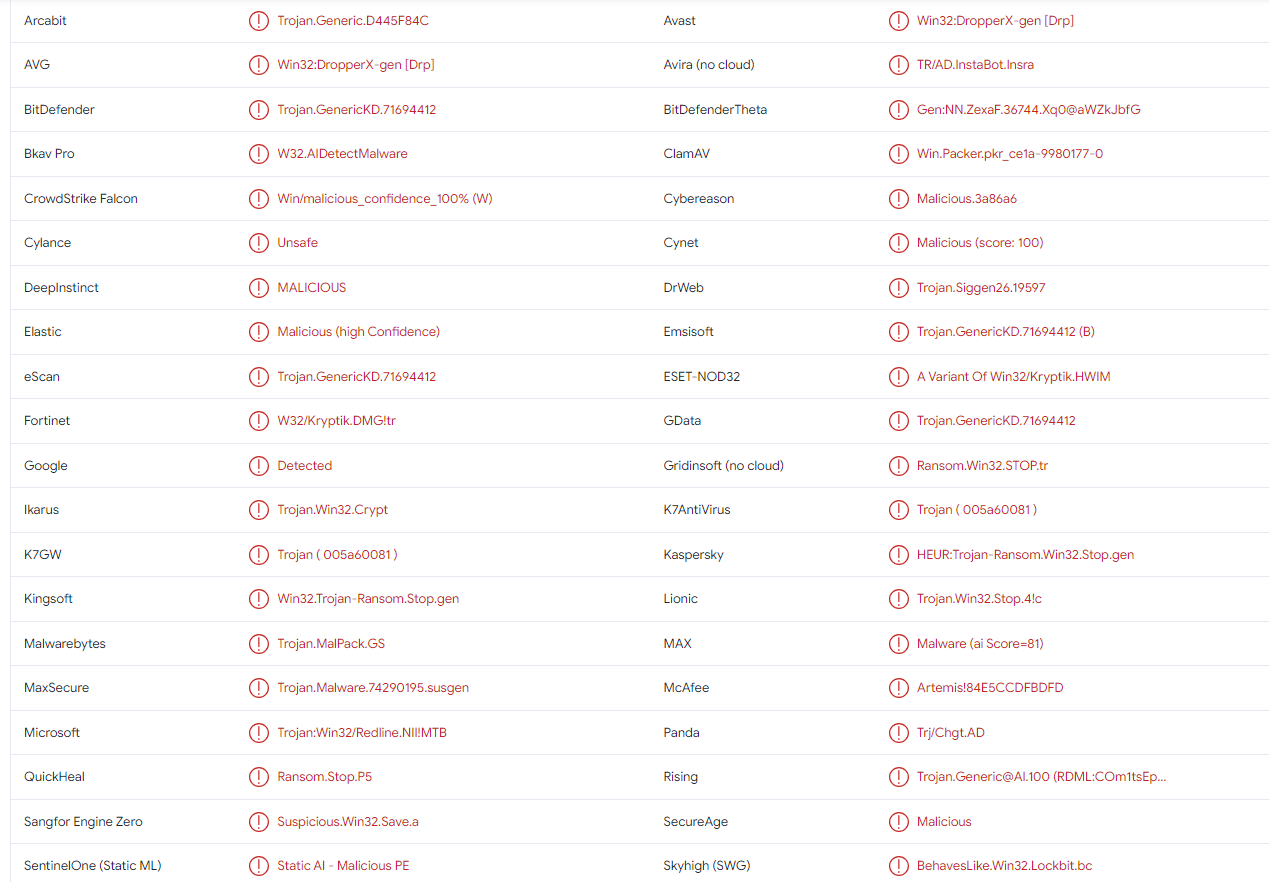
Lkfr ransomware is detected as:
- Win32:DropperX-gen [Drp] by AVG/Avast
- Trojan.GenericKD.71694412 by BitDefender
- Trojan.MalPack.GS by Malwarebytes
- Trojan:Win32/Redline.NII!MTB by Microsoft
- Trojan.Win32.PRIVATELOADER.YXEBSZ by TrendMicro
- Trojan.GenericKD.71694412 (B) by Emsisoft
- A Variant Of Win32/Kryptik.HWIM by ESET
- HEUR:Trojan-Ransom.Win32.Stop.gen by Kaspersky
- Artemis!84E5CCDFBDFD by McAfee
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.