What is Trojan.Agent
You likely have a generic trojan infection inhabiting your device if your anti-virus software is identifying something named Trojan.Agent. We ought to point out that trojans aren’t small machine threats that should absolutely be taken seriously. If not eliminated, trojans could steal information, install other malware, and lead to a serious ransomware infection. 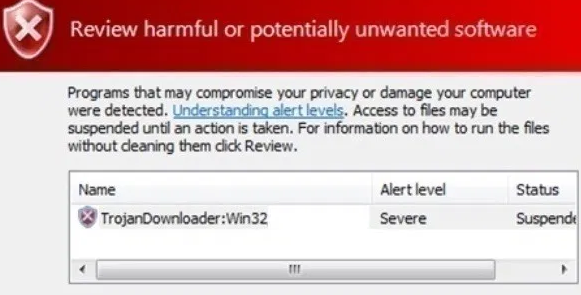
If Trojan.Agent is detected by your anti-malware application, you should deal with it as soon as possible, as it is harmful even if it is a generic trojan. Unless there is malware removal software, it would be pretty complex for you to notice the trojan. If the infection is not seen in time, it may steal your info, take your files for hostage or even delete them.
If you’re someone who opens spam emails, downloads pirated content, or enter dangerous web pages, that is how the trojan ended up on your computer. We suggest you change your browsing manners after Trojan.Agent removal if you believe they are the reason your machine got contaminated.
Trojan infection ways
You acquiring free copyrighted content through torrents might be why your machine is contaminated. We ought to note that torrent sites are not managed, and it is not hard for cyber crooks to mask their malware as episodes of a famous TV shows, film or other entertainment content.
Alternatively, the malicious software was added to a spam email which you opened. You’ll often see scammers who send those emails claiming to be from real, known companies in order to encourage the user to open the file. Those emails mostly request that you open the added file as otherwise you could be missing some supposedly crucial information. All it takes is for the malicious file to be opened, and the trojan can then start doing what it was designed to do.
How will Trojan.Agent affect the machine
Trojan.Agent is how virus removal applications like Kaspersky, ESET, Malwarebytes, TrendMicro, Windows Defender name generic trojans. As the identification name isn’t very informative, telling how your computer will be affected is difficult. Nevertheless, there are a few things that could occur, like taken data or files. Initially, you’re not likely to notice that something is wrong since it works in the background, and that is quite unsettling.
Trojans could also operate as backdoors for other infections, so more malware could be brought about by a trojan left ignored.
Trojan.Agent deletion
Since you’re reading about Trojan.Agent, you probably already have a malware removal application installed on your device. Even if it’s able to find it, it may struggle with Trojan.Agent uninstallation. If that’s the issue you have stumbled upon, you will either have to employ a different anti-malware program for Trojan.Agent elimination or do everything manually. Your anti-virus application may also be detecting something mistakenly, making Trojan.Agent a false detection.
Offers
Download Removal Toolto scan for Trojan.AgentUse our recommended removal tool to scan for Trojan.Agent. Trial version of provides detection of computer threats like Trojan.Agent and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
