Gamezonenews.net Removal Instructions
Browser hijackers are becoming more and more prominent these days with so many of them popping up like mushrooms every week. We have recently come across another, relatively new, browser hijacker called Gamezonenews.net.
If you are reading this article, then you probably want to remove it as quickly as possible. However, we suggest that you take time to know more about this particular infection so that you would be able to deal with similar ones in the future, because if you are a frequent visitor of websites that distribute pirated software, then you are bound to encounter more of them further down the line.
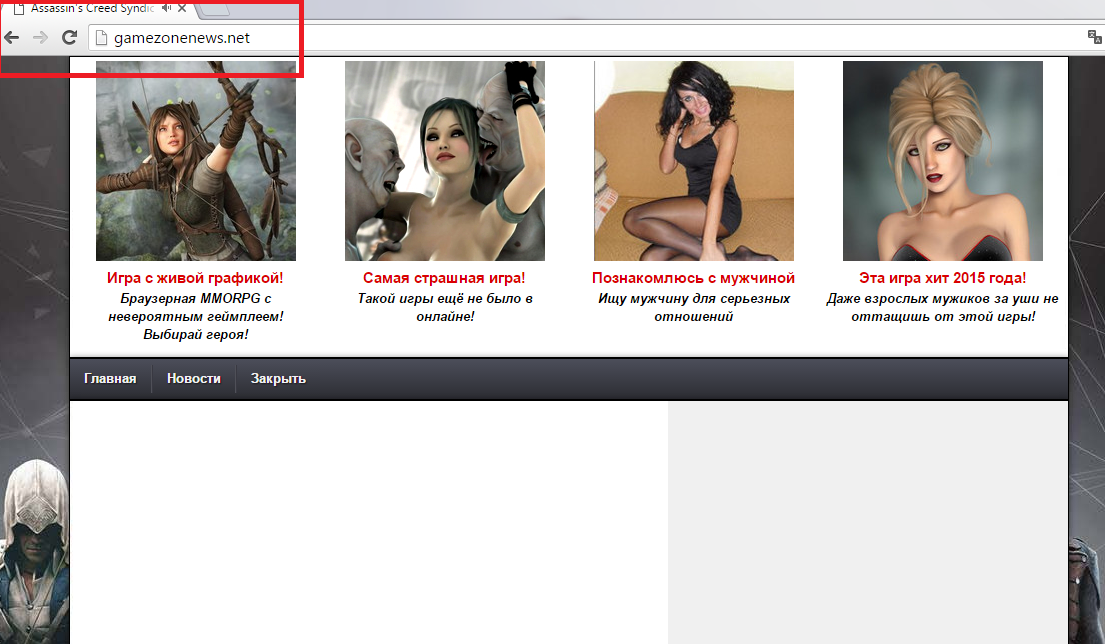 This hijacker will also be referred to as a search engine throughout this article. So this search engine was created in 2012 and is registered in Turkey. Its alleged current owner is Ahmet Kara. This hijacker has been created specifically for Turkish Internet surfers. It is not a particularly popular search engine, since it only receives approximately 900 visitors a day. So it is no surprise that it has morphed into a browser hijacker, because its main purpose is to generate money by displaying commercial advertisements on its main page. Gamezonenews.net probably infected your computer when you downloaded pirated software. It is mostly featured on Turkish websites, but people from neighboring countries get it as well. This hijacker does not ask users whether they want to replace their homepage with Gamezonenews.net, it just does that for them.
This hijacker will also be referred to as a search engine throughout this article. So this search engine was created in 2012 and is registered in Turkey. Its alleged current owner is Ahmet Kara. This hijacker has been created specifically for Turkish Internet surfers. It is not a particularly popular search engine, since it only receives approximately 900 visitors a day. So it is no surprise that it has morphed into a browser hijacker, because its main purpose is to generate money by displaying commercial advertisements on its main page. Gamezonenews.net probably infected your computer when you downloaded pirated software. It is mostly featured on Turkish websites, but people from neighboring countries get it as well. This hijacker does not ask users whether they want to replace their homepage with Gamezonenews.net, it just does that for them.
After you get rid of Gamezonenews.net, it may prove difficult for inexperienced users. You cannot reset your homepage by simply going to the browser settings and typing in a new address. This hijacker modifies the browser’s Target line which resets the homepage every time you reboot your PC. As if that was not enough, the installation wizard may install a randomly named process that will make sure to do the same. So the developers who created this hijacker made sure that whoever installs it will have a hard time removing it. Using Gamezonenews.net as a search engine is a frustrating endeavor, because it display unasked-for shortcuts and commercial advertisements. You will notice that it features a Google logo on the left. It is true that this hijacker uses Google as its search engine. So as a search engine it offers nothing unique to the end-user. We also have a suspicion that the website might collect information about your browsing habits for the purpose of selling it to third parties.
To remove Gamezonenews.net is not an impossible task. If it did not come with the additional process then it is a simple matter of fixing the Target line. But if it did come with the additional process then it will be a bit more challenging, since the process’s name is always random. Nevertheless, it should not be difficult to find it since it does not have a folder. In any case, we will provide you with instructions how to fix the Target line and where to look for this illusive process.
Remove Gamezonenews.net
Delete Gamezonenews.net from Windows 8 and Windows 8.1
- Navigate the mouse to the lower-left of the screen.
- Right-click the Windows logo and select Control Panel.
- Go to Uninstall a program.
- Find the program and Uninstall it.
Uninstall Gamezonenews.net from Windows Vista and Windows 7
- Navigate the mouse to the lower-left of the screen.
- Click the Start menu button and select Control Panel.
- Click Uninstall a Program.
- Find the unwanted application and Uninstall it.
Delete Gamezonenews.net from Windows XP
- Navigate the mouse to the lower-left of the screen.
- Click the Start menu button and select Control Panel.
- Click Add or Remove Programs.
- Find the application and Remove it.
Terminate Gamezonenews.net (process file)
- Open My Computer or Windows Explorer.
- Click Organize and select Folder and search options.
- Select the View tab and put the tick on Show hidden files, folders, and drives.
- Then copy and paste %PROGRAMFILES%, %PROGRAMFILES(x86)%, %APPDATA%, and %TEMP% separately in the address bar.
- Once you are in these particular folders find and delete any suspiciously named process (.exe) files.
- Empty your recycling bin.
Fix the browser’s Target line
- Right-click on Chrome, Firefox or Internet Explorer’s shortcut.
- Select Properties and open the Shortcut tab.
- Fix the modified Target line.
- Done.
Offers
Download Removal Toolto scan for Gamezonenews.netUse our recommended removal tool to scan for Gamezonenews.net. Trial version of provides detection of computer threats like Gamezonenews.net and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
