Sapp ransomware belongs to the notorious Djvu/STOP malware family. The ransomware will encrypt all personal files, essentially taking them hostage. Because of this, it’s considered to be a very serious infection. For users who have backups of their files, file recovery will not be an issue as long as Sapp ransomware is deleted from the computer first. However, users with no backups may not be able to recover their files. The ransomware operators will try to sell the decryptors to victims for $980 but even paying comes with certain risks.
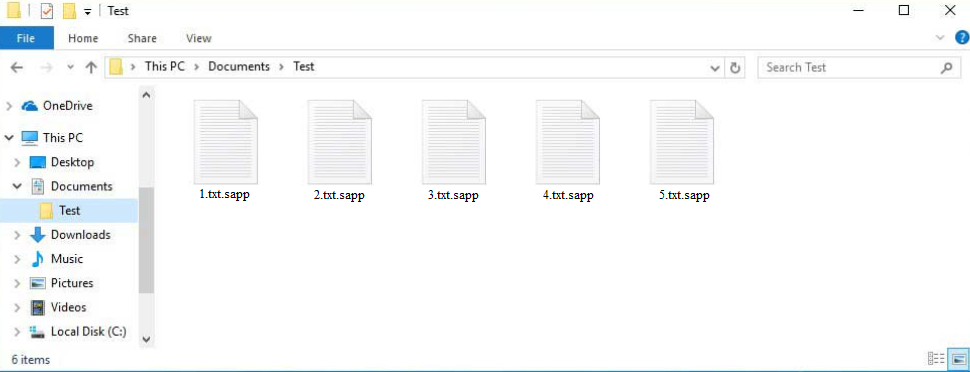
All ransomware versions from the Djvu/STOP family, including Sapp ransomware, are fundamentally the same. The malicious actors operating this ransomware have released hundreds of these infections but they can be differentiated by the extensions they add to encrypted files. This ransomware adds .sapp. For example, an encrypted text.txt file would become text.txt.sapp. Files with this extension will be unopenable until you use a specific decryptor on them. The files that are targeted the most are images, photos, videos, and documents because users are most willing to pay for them.
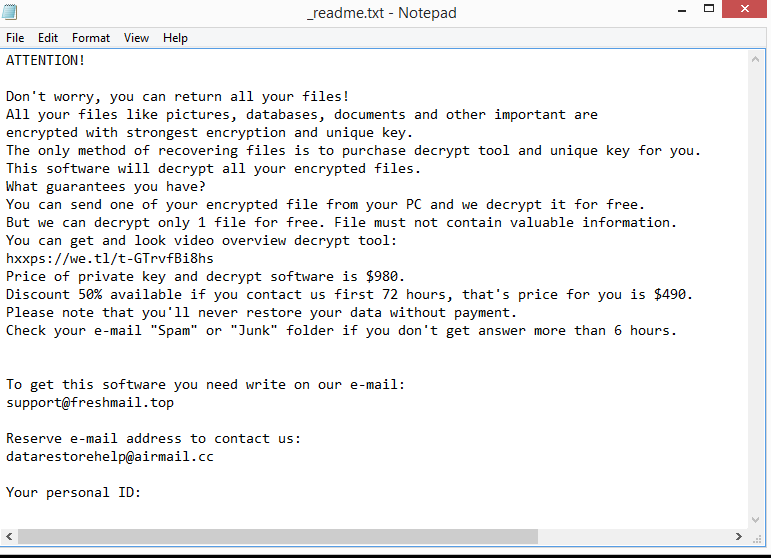
A _readme.txt ransom note with instructions on how to buy a decryptor will be dropped in folders that have encrypted files. According to the note, the decryptor costs $980 but there’s a 50% discount for victims who contact the cybercriminals within the first 72 hours. It’s debatable whether the claims of a discount are true, but there are several risks associated with paying. The most important thing to mention is that you are dealing with cyber criminals and that there are no guarantees that you will actually get the decryptor. It’s unlikely that the cybercriminals behind this ransomware will feel any kind of obligation to help you, even if you pay. Many users paid the ransoms in the past but did not receive their decryptors. The decision to pay or not is yours to make but you need to be aware of the risks that come with it.
File recovery shouldn’t be a problem for those who have backups. However, users must first remove Sapp ransomware from their computers. If the backup is accessed while the ransomware is still active, the backed-up files would also be encrypted. Files would be irreversibly lost if that happened. The safest and simplest way to delete Sapp ransomware is to use anti-malware software, and that is what we recommend doing. This will guarantee that your computer sustains no more harm and that the infection is completely eliminated.
Unfortunately, your options are very limited if you don’t have a backup. Waiting for a free Sapp ransomware decryptor to be released is one of the few options. Because this ransomware uses online keys to encrypt files, there is no free decryptor available at the moment. When ransomware uses online keys to encrypt files, the keys are unique to each victim. Without those keys, a decryptor is not very likely. It’s not impossible that the keys will eventually be released, so back up your encrypted files and occasionally check for a free Sapp ransomware decryptor.
How does ransomware spread
One of the most popular methods used by cybercriminals to spread malware is email attachments. Cybercriminals only need to buy email addresses from hacker forums, write a somewhat convincing email, and attach a malicious file to it, making it a relatively low-effort distribution method. Users’ computers become infected as soon as they open the malicious file. As long as those attached files remain unopened, the emails are not dangerous. Fortunately for users, malicious emails are frequently relatively simple to identify. The emails frequently contain several grammar and spelling mistakes. Senders often pretend to be from legitimate businesses, so the mistakes look very obvious and out of place. Grammar and spelling mistakes would make an email from a business whose services you use look very unprofessional.
Another red flag is when a sender who ought to know your name addresses you using words like “User,” “Member,” or “Customer”. You likely already noticed that emails from senders whose services you use always address you by name. It makes the email seem more personal.
Lastly, it’s worth mentioning that some malicious emails may be much more sophisticated. Thus, it’s recommended to scan all email attachments with anti-virus software or VirusTotal before opening them.
Additionally, torrents are also used to spread malware. Most torrent users are already aware of this but torrent sites are often quite poorly moderated, which allows malicious actors to upload torrents with malware in them. If users do not know how to recognize malicious torrents, they can easily end up with malware. Most commonly, torrents for entertainment content (e.g. movies, TV series, video games) contain malware. Using torrents to pirate copyrighted content is also essentially theft.
How to remove Sapp ransomware
Anti-malware software should be used to remove Sapp ransomware from your computer because it’s a rather sophisticated infection. If you try to do it manually yourself, you could end up causing serious damage to your computer unless you know exactly what to do. It’s much easier, and safer to use anti-virus software. As soon as the anti-virus program has completely removed Sapp ransomware, you can connect to your backup and start recovering your files safely.
If you do not have a backup, your only option may be to wait for a free decryptor to be released. Unfortunately, it’s not certain when that would happen, or even if. However, if it does get released, it would be posted on NoMoreRansom.
Quick Menu
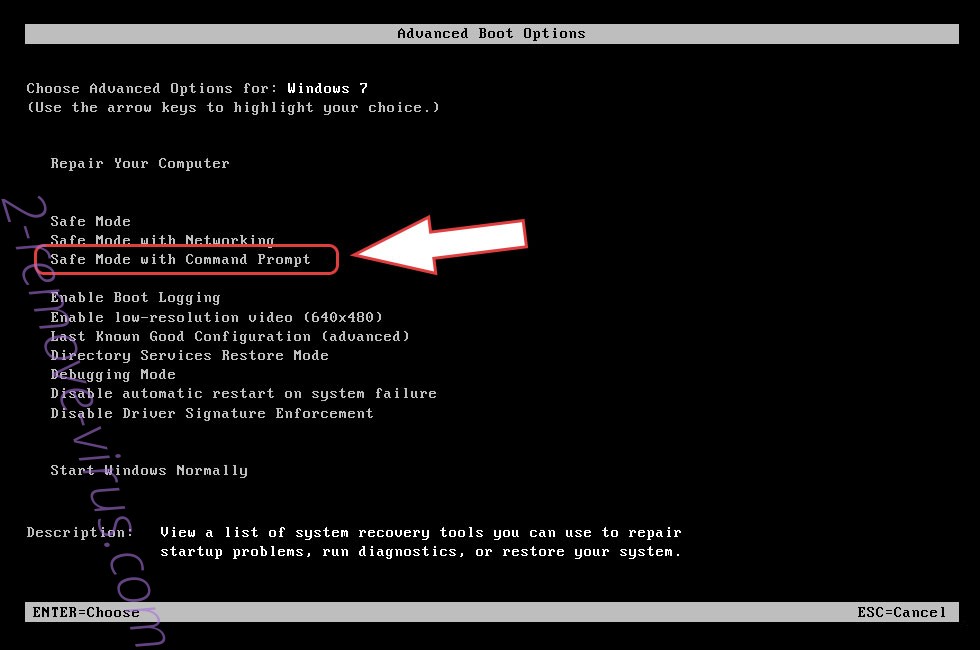
Step 1. Delete Sapp ransomware using Safe Mode with Networking.
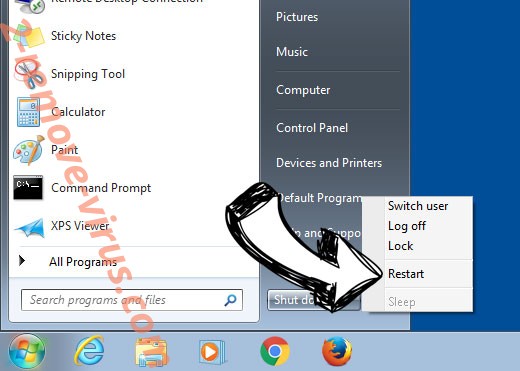
Remove Sapp ransomware from Windows 7/Windows Vista/Windows XP
- Click on Start and select Shutdown.
- Choose Restart and click OK.

- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove Sapp ransomware
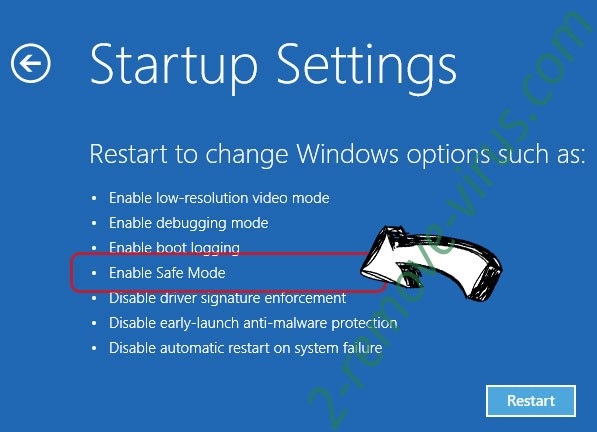
Remove Sapp ransomware from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.

- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete Sapp ransomware
Step 2. Restore Your Files using System Restore
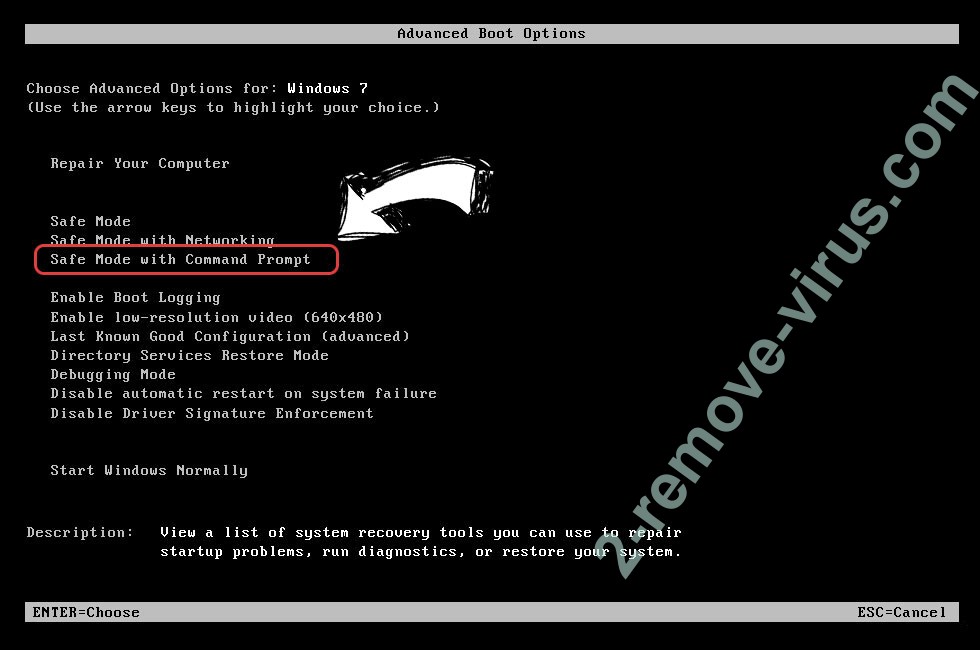
Delete Sapp ransomware from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

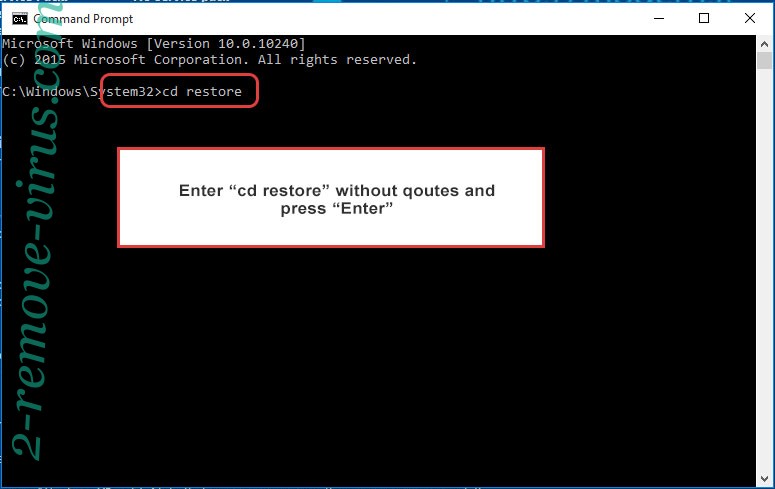
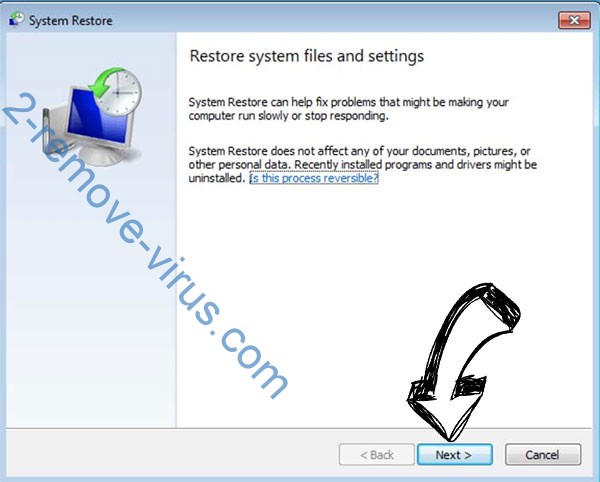
- Type in cd restore and tap Enter.

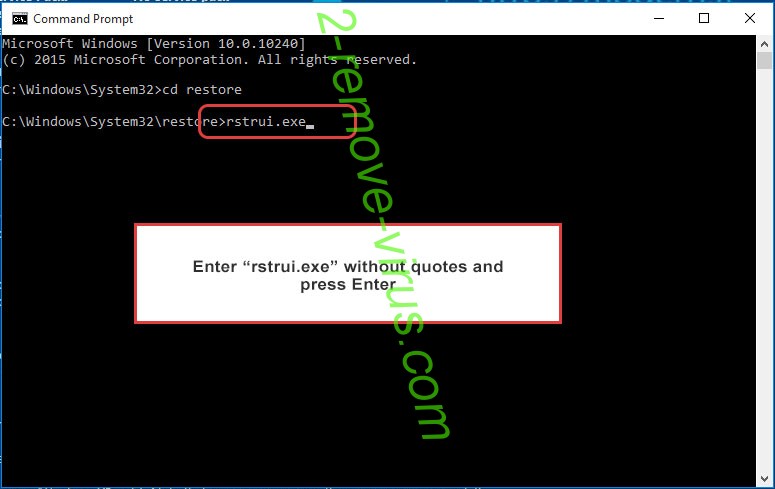
- Type in rstrui.exe and press Enter.

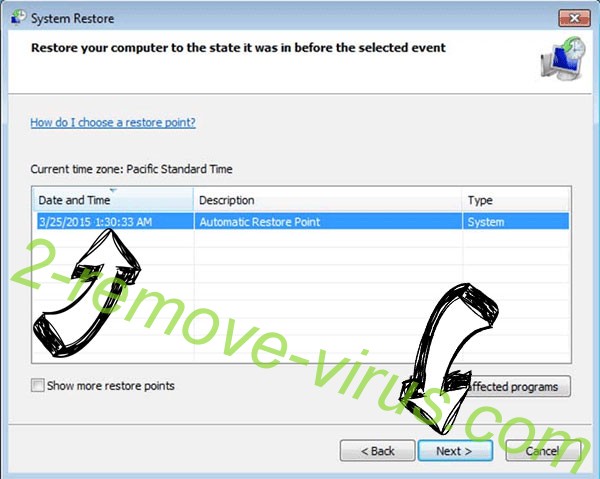
- Click Next in the new window and select the restore point prior to the infection.

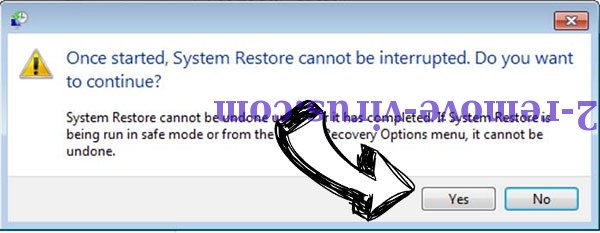
- Click Next again and click Yes to begin the system restore.

Delete Sapp ransomware from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.

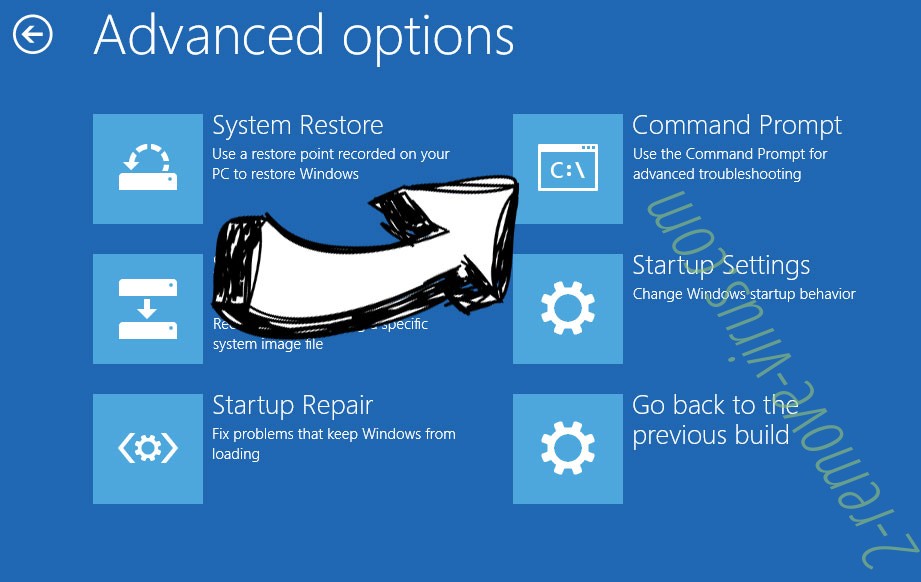
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

- Click Next and then click Yes to restore your system.

Offers
Download Removal Toolto scan for Sapp ransomwareUse our recommended removal tool to scan for Sapp ransomware. Trial version of provides detection of computer threats like Sapp ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.