What is Helpme@freespeechmail.org?
Helpme@freespeechmail.org is a term used to refer to a ransomware application, which encrypts your files and demands that you pay a ransom fee for them. The reason the malicious program is named after an email address is because it is the email that you are required to contact in order to make the payment. Once it enters your computer and encrypts your data, it prompts you with a message stating that you need to purchase a decryption key in order to get your files back. Needless to say, there are no guarantees that the cyber criminals will follow through on their promises, even if you make the payment. We suggest that you terminate Helpme@freespeechmail.org right away.
Offers
Download Removal Toolto scan for Helpme@freespeechmail.orgUse our recommended removal tool to scan for Helpme@freespeechmail.org. Trial version of provides detection of computer threats like Helpme@freespeechmail.org and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
How does Helpme@freespeechmail.org work?
There are a few distribution methods used by the ransomware, however, it usually spreads through spam email attachments. When you open the malicious attachment, you infect your system. That is why it is important to be careful with emails from unknown senders. Do not believe various scams trying to convince you that you have won a lottery, or that a delivery is waiting for you, etc. The harmful threat may also get distributed with the help of bundled software. Make sure that you do not agree to any additional offers when installing free third party software, no matter what those offers may be.
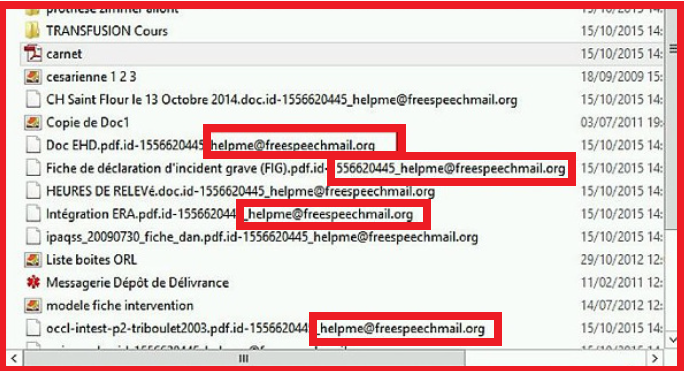
As soon as Helpme@freespeechmail.org enters your computer, it starts the file encryption process. The ransomware adds a unique ID and a Helpme@freespeechmail.org to their names. Once this process is completed, the malware presents you with a message claiming that the only way to get your files back is to pay 3 Bitcoins and then send the confirmation of the payment to the above mentioned email. Supposedly, you will then be provided with a decoder that will decrypt your files. The parasite also blocks your Internet access thus preventing you from looking for a solution online. It is clear that you should not waste your money on the cyber criminals. What you should do is delete Helpme@freespeechmail.org as soon as you can.
How to remove Helpme@freespeechmail.org?
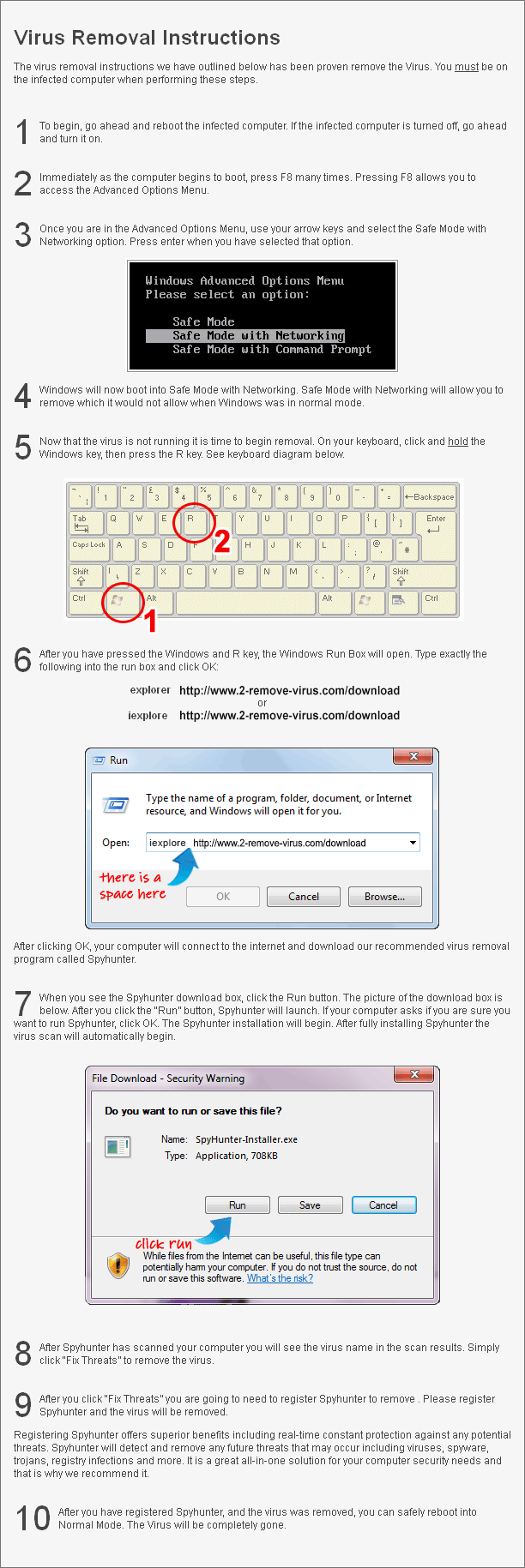
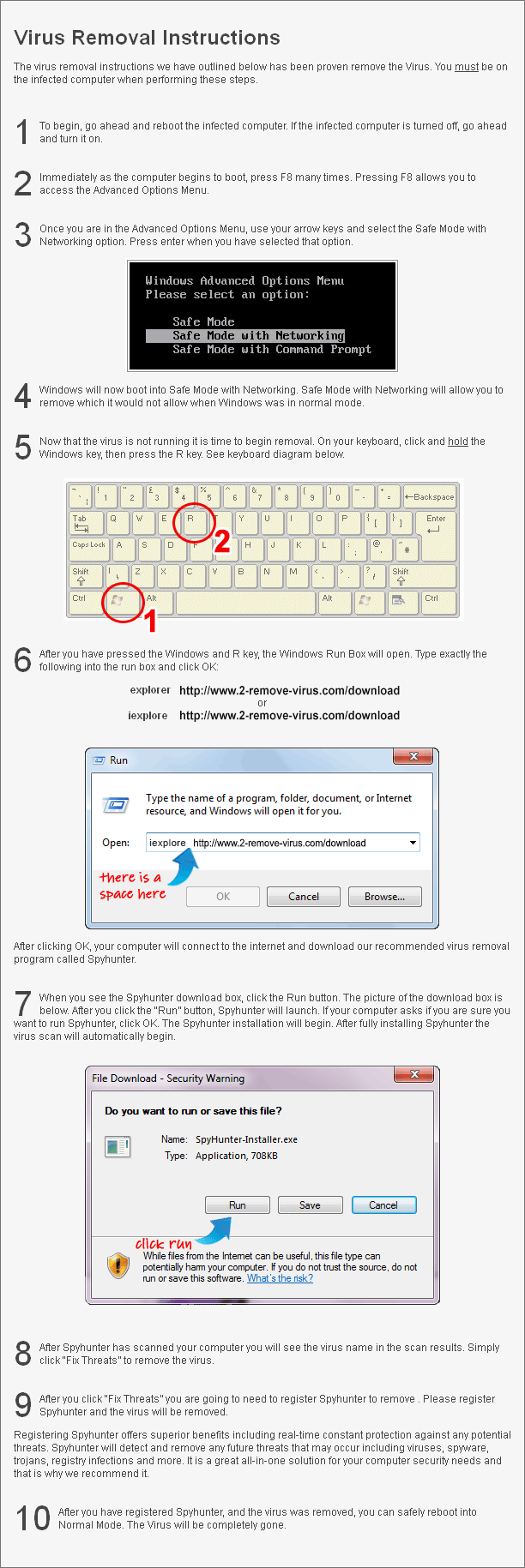
In order to delete Helpme@freespeechmail.org from your computer, you will have to use a powerful malware removal tool. You can download the anti-malware from our page. It will scan your system, detect all malicious files and programs and eliminate Helpme@freespeechmail.org along with them. In addition to Helpme@freespeechmail.org removal, you will also make sure that similar infections do not enter your system again. However, before you can download the utility and erase Helpme@freespeechmail.org, you will have to restart your PC in Safe Mode with Networking. As for your files, there are several ways you can get them back. You can restore them from backup, use Shadow Explorer, or implement one of the file decryption tools you can find online.
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.

You’ve said, infection is spreading usually via e-mail attachements. But this is very general statement. E-mail is primary only text, often with attachment. There is unusual to infect computer only by text (unfortunately, under windows not impossible). But attachment can be of arbitrary filetype. Can you tell me about type of attachment (is there document (i.e. ms doc(x) with macros) or executable file or etc.). Statement “infection via e-mail” is similar than “I’ve buy this on the internet”. I’am sure, there was not been oppenned any attachments of unknown sender’s e-mail, only normal filetypes from known people.
Hello Jan,
Very popular method of infection involves sending files which looks to be image files (such as GIFs or JPEGs) or word processor documents, but are in fact executable files. In Windows, this is particularly effective, since by default, extension are hidden from the user. For an attachment named look_at_this.JPG.EXE it would be displayed in the email client as look_at_this.JPG, appearing to be a JPG image file. A common method used to bypass antivirus checkers, is to include the virus in a ZIP archive, which the user must first unpack.
If you are infected with any of cryptolockers use this – https://noransom.kaspersky.com/
To prevent this kind infections I suggest to create a system restore point. If you have system restore points created on your computer, you may be able to restore previous versions of some encrypted files.