About Systemdown@india.com
Systemdown@india.com is a ransomware type of virus that belongs to a big family of ransomwares. Systemdown@india.com spreads via spam emails and once victims download the ransomware, it proceeds to encrypt files. It a relatively new virus and there have been reports about it targeting business. When it encrypts files, it asks for money in order to restore them.
It is not known how much money the hackers want but presumably, when victims email the hackers, they will find out. We always recommend against paying when it comes ransomware because most hackers just ignore the victims after payment has been made. So in order to save you money and time, we recommend you remove Systemdown@india.com. If you have backup, you can restore your files only after you delete Systemdown@india.com.
How does Systemdown@india.com spread?
Ransomware usually spreads via spam emails. An infected file is attached to an email and sent to unsuspecting users. When users open that email and click on the attachment, they download the the virus onto their computer. Those emails usually end up in the spam folder but look rather official and legitimate. The email could claim that you need to open the attachment because it contains an important document, but do not be fooled. When you open spam emails, always make sure that what you are opening is safe. You can do so by double checking the sender and the contents using a reliable search engine. If someone else has gotten a similar email and ended up with ransomware, you have your answer.
What does Systemdown@india.com do?
Systemdown@india.com seems to use the RSA-2048 encryption algorithm, which means it creates two keys, a public and a private one. The public is used to encrypt files, the private – to decrypt. The private key is stored in a remote server and the victim needs to buy it from the hackers. Victims need to contact the hackers using email to find out how they can restore the files. Previous experience with ransomware shows that hackers very rarely give the decryption key to victims, so not matter what amount Systemdown@india.com developers ask for, you should not pay. You should not even contact them. Systemdown@india.com removal is your best option. After you delete Systemdown@india.com, you can get your files from backup, if you have it.
Systemdown@india.com removal
To erase Systemdown@india.com, you will need anti-malware software. Manually trying to remove Systemdown@india.com could have serious consequences for your computer, so we cannot recommend it. But anti-malware software should be able to help you get rid of Systemdown@india.com.
Offers
Download Removal Toolto scan for Systemdown@india.comUse our recommended removal tool to scan for Systemdown@india.com. Trial version of provides detection of computer threats like Systemdown@india.com and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete Systemdown@india.com using Safe Mode with Networking.
Remove Systemdown@india.com from Windows 7/Windows Vista/Windows XP
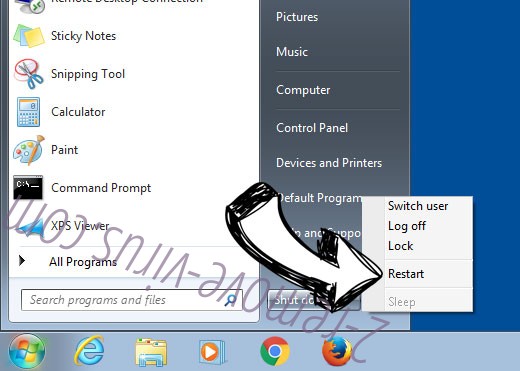
- Click on Start and select Shutdown.
- Choose Restart and click OK.

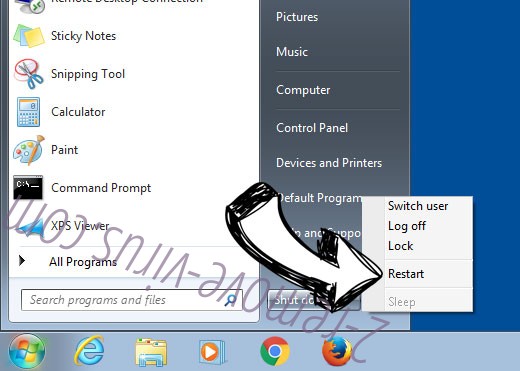
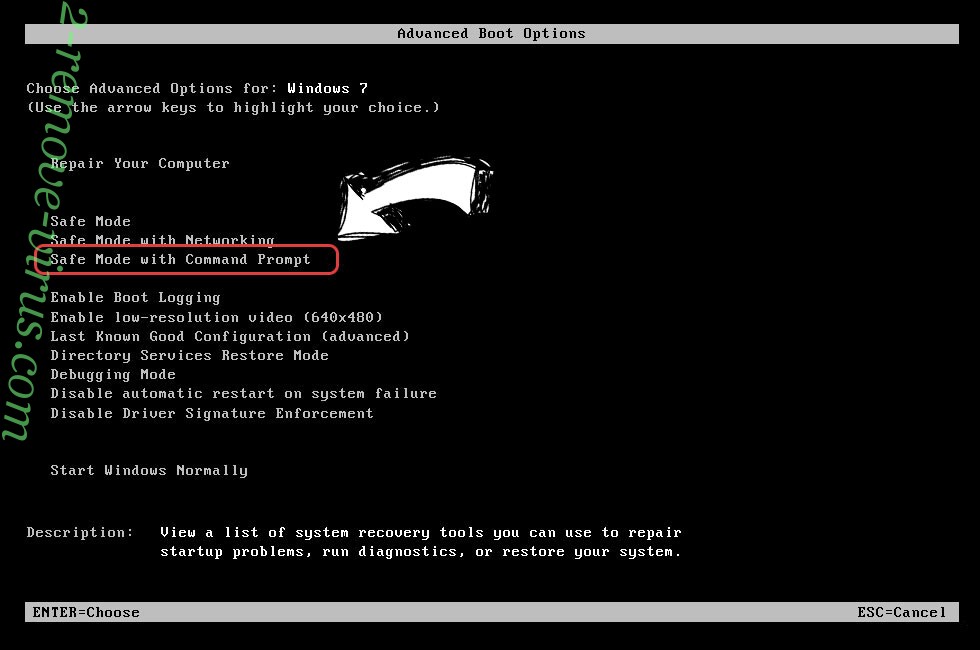
- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove Systemdown@india.com
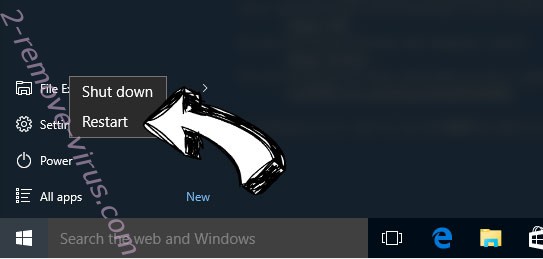
Remove Systemdown@india.com from Windows 8/Windows 10
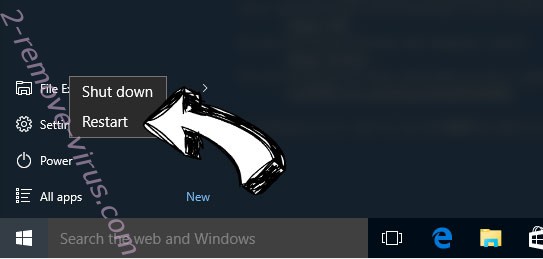
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.

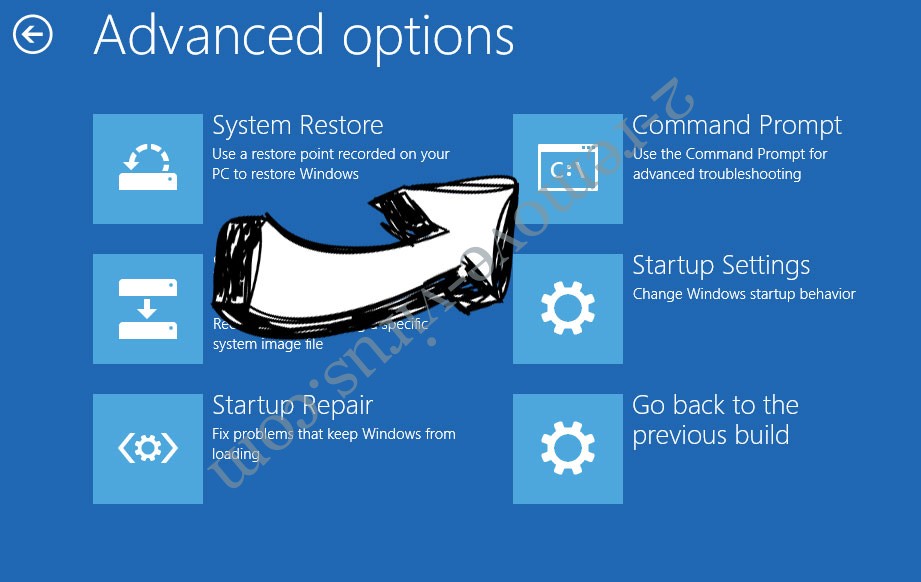
- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

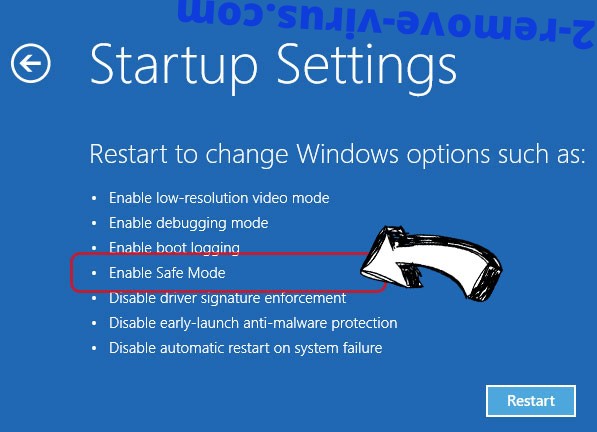
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete Systemdown@india.com
Step 2. Restore Your Files using System Restore
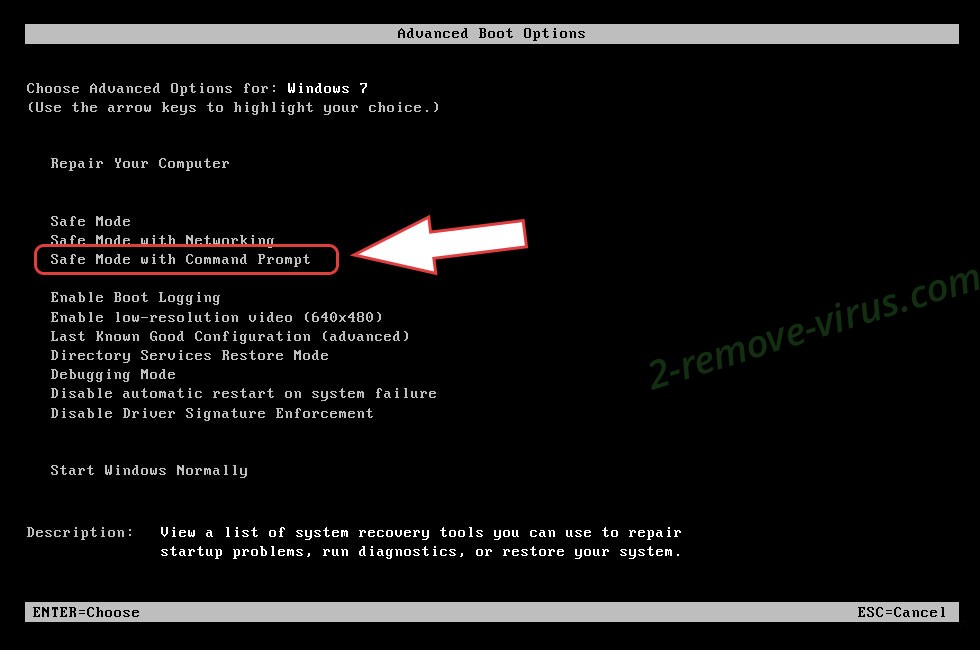
Delete Systemdown@india.com from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

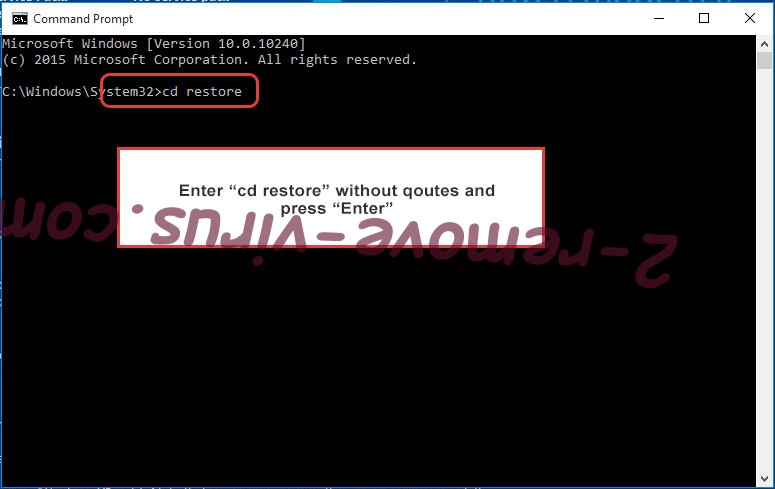
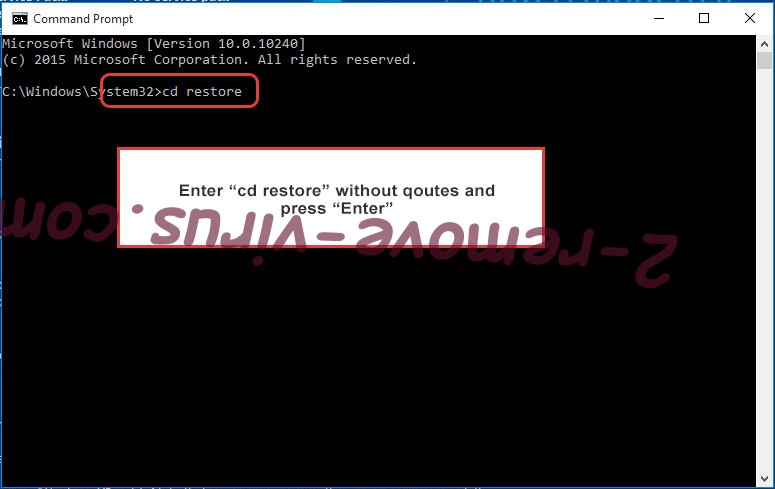
- Type in cd restore and tap Enter.

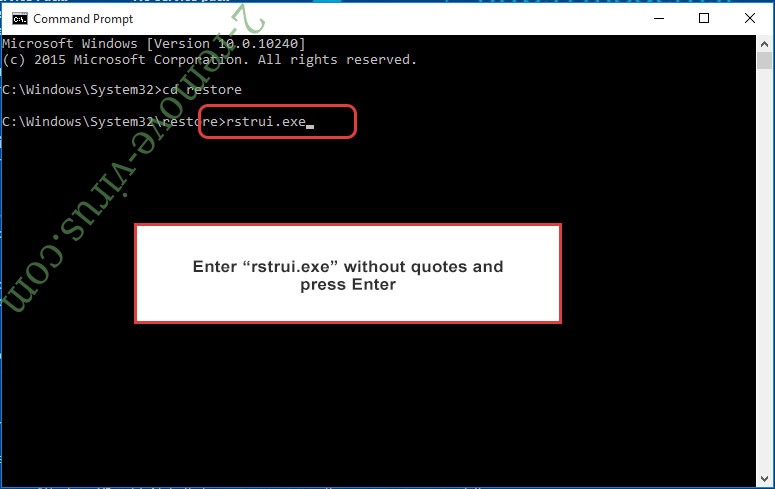
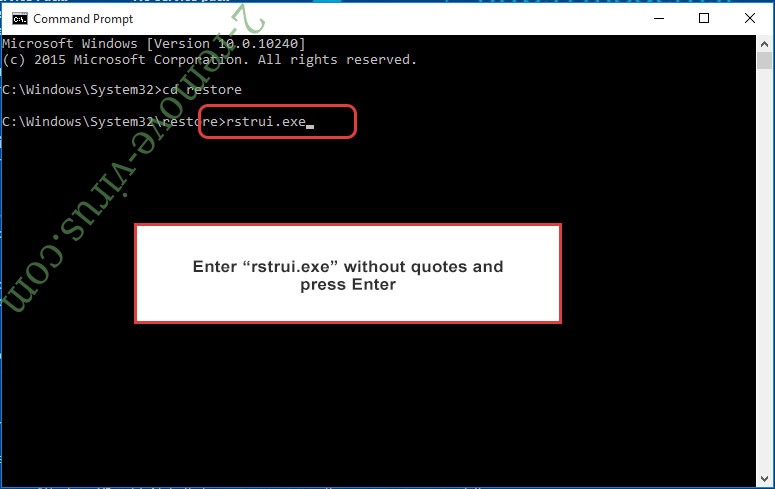
- Type in rstrui.exe and press Enter.

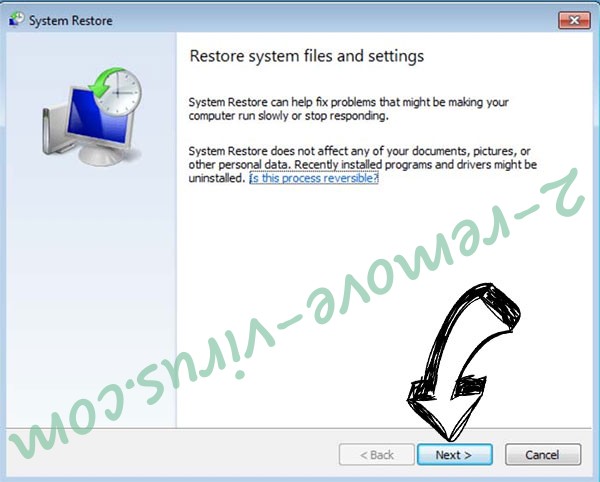
- Click Next in the new window and select the restore point prior to the infection.

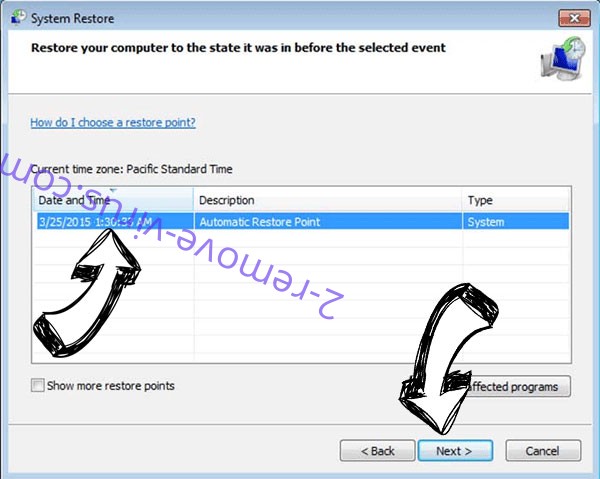
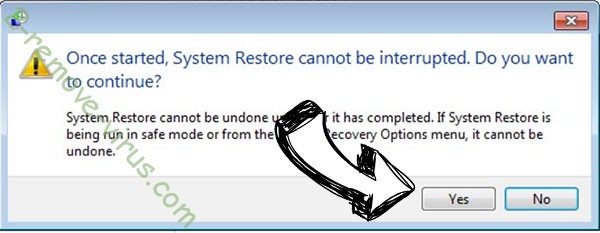
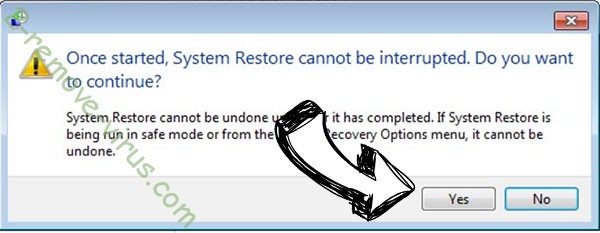
- Click Next again and click Yes to begin the system restore.

Delete Systemdown@india.com from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.

- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

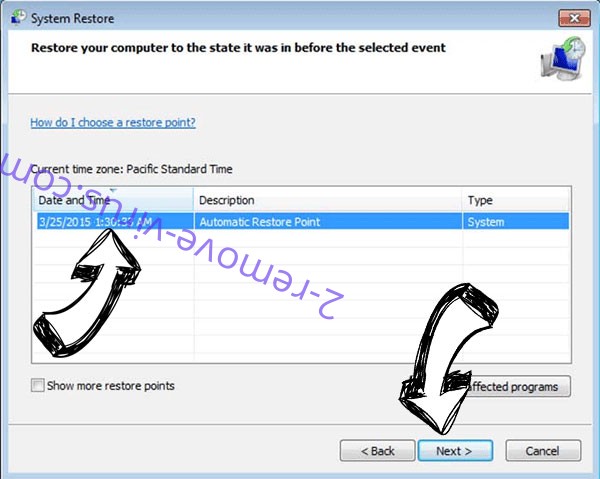
- Click Next and then click Yes to restore your system.

Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
