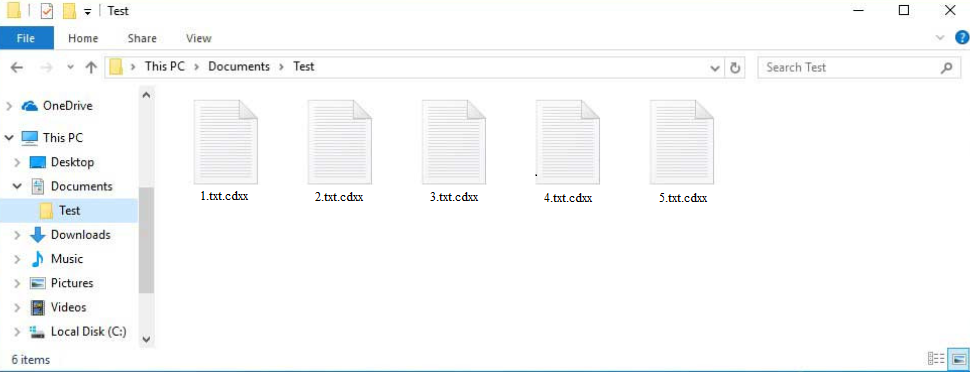
Cdxx ransomware is malware that encrypts files. The ransomware is part of the Djvu/STOP ransomware family and can be recognized by the .cdxx extension that gets added to encrypted files. It’s a very dangerous infection that could result in permanently lost personal files.
Cdxx ransomware aims to take your files hostage by encrypting them. It begins encrypting files as soon as the malicious file is initiated. All personal files will be targeted, including photos, videos, and documents. You will know immediately which files have been affected because they will be unopenable and have .cdxx added to them. For example, text.txt would become text.txt.cdxx if encrypted.
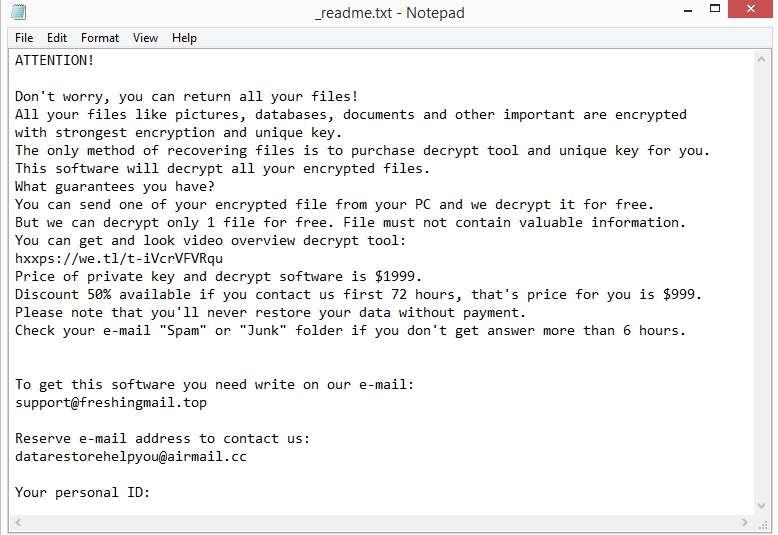
The ransomware will drop a _readme.txt ransom note in folders that have encrypted files. The note explains that files have been encrypted and how to acquire a decryptor. Unfortunately, the contents of the note are legitimate in the sense that file decryption is not possible unless you have a decryptor.
As explained in the note, malware operators are demanding $1,999 for a decryptor. Supposedly, there is a 50% discount for users who make contact within the first 72 hours, making the price for the decryptor $999. However, even if the discount part is true, paying the ransom is not recommended. First of all, you have no way of knowing that you’ll be sent a decryptor, you are dealing with cybercriminals after all. They can easily just take your money and not send you anything in return. it has happened to many ransomware victims in the past. Furthermore, your money would go towards future criminal activities, of which you could become a victim again. As long as users continue paying the ransom, ransomware will be a serious problem.
The contents of the _readme.txt ransom note are:
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted
with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-iVcrVFVRqu
Price of private key and decrypt software is $1999.
Discount 50% available if you contact us first 72 hours, that’s price for you is $999.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
If you have a backup of all your files, you should be able to recover them quite easily. However, before you access your backup, you need to remove Cdxx ransomware from your computer. We strongly recommend you use reliable anti-malware software instead of trying to delete Cdxx ransomware manually. Manual Cdxx ransomware removal could lead to further issues and even cause damage to your computer.
If you do not have a backup, your options are very limited. Or rather, the only option is to wait for a free Cdxx ransomware decryptor to be released. However, it’s not guaranteed that it will ever become available. There is a free Djvu/STOP ransomware by Emsisoft that you can try but it’s unlikely to work. For a free Cdxx ransomware decryptor to be developed, malware researchers need to have the online keys used for file encryption. Each victim has a unique key, which complicates the situation. However, if a decryptor does become available, it will be posted on NoMoreRansom. If you cannot find it on NoMoreRansom, you won’t find it anywhere else, especially not on some questionable forum.
How did ransomware enter your computer?
Cybercriminals usually distribute malware via methods like email, torrents, malicious ads, etc. Therefore, users with bad browsing habits are more likely to infect their devices with malware. Developing better online habits is one of the best ways to prevent future infections.
Ransomware is often found in email attachments. Cybercriminals use stolen email addresses to launch massive spam campaigns to target users with malware. Because the emails target a large number of users at the same time, they are very generic and usually easy to identify. First of all, senders claim to be from legitimate companies but the emails are often full of grammar/spelling mistakes. You will rarely see obvious mistakes in legitimate emails because they look unprofessional.
How an email addresses you can also help you determine whether it’s legitimate. If the sender claims to be someone whose services you use but they address you with generic words like User, Member, Customer, etc., it’s likely either spam or malicious. Legitimate emails from companies whose services you use will address you by name. Since malicious actors do not have access to personal information and they target many users at the same time, they have to use generic words.
Some malicious emails can be more sophisticated than others, which is why we always recommend scanning all unsolicited email attachments with anti-malware software or VirusTotal before opening them.
Malware also spreads via torrents. A lot of torrent sites are poorly regulated, which allows malicious actors to upload torrents with malware in them. Malware is often found in torrents for popular entertainment content, including movies, TV series, and video games. Using torrents to obtain copyrighted content is not only content theft but also dangerous for the computer.
Cdxx ransomware removal
We recommend you use anti-malware software to remove Cdxx ransomware from your computer. It’s a complex infection that requires a professional program to remove. Once the ransomware is gone, you can connect to your backup and start recovering your files.
If you do not have a backup, back up your encrypted files and occasionally check NoMoreRansom for a free Cdxx ransomware decryptor.
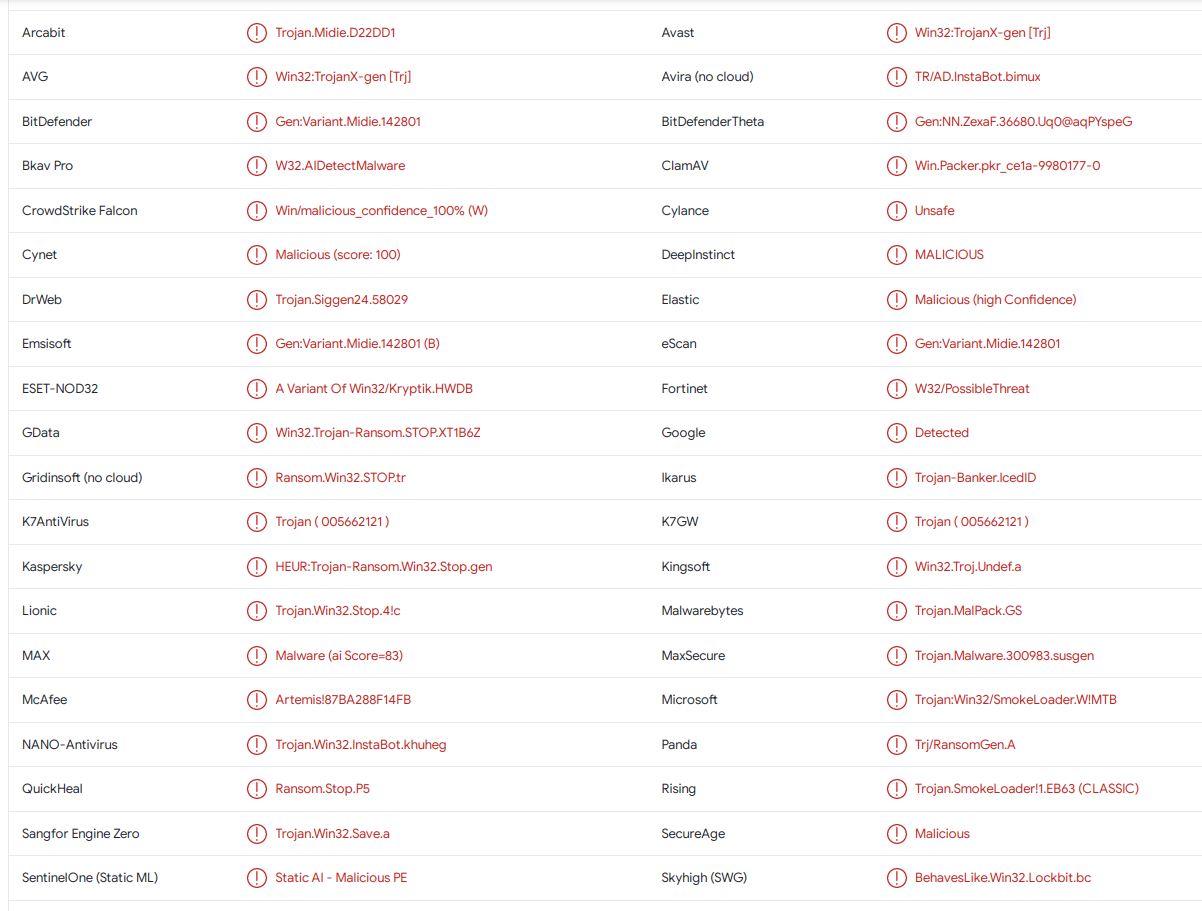
Cdxx ransomware is detected as:
- Win32:TrojanX-gen [Trj] by AVG/Avast
- A Variant Of Win32/Kryptik.HWDB by ESET
- HEUR:Trojan-Ransom.Win32.Stop.gen by Kaspersky
- Trojan.MalPack.GS by Malwarebytes
- Trojan:Win32/SmokeLoader.W!MTB by Microsoft
- Gen:Variant.Midie.142801 by BitDefender
Offers
Download Removal Toolto scan for Cdxx ransomwareUse our recommended removal tool to scan for Cdxx ransomware. Trial version of provides detection of computer threats like Cdxx ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.