Win32/Ymacco is a serious malware infection, classified as a dropper malware that can allow other malicious programs to enter the computer. It shows signs of being present but anti-malware software is necessary to identify and remove Win32/Ymacco.
Win32/Ymacco is a trojan type of malware. Its main purpose is to open a backdoor for other malware to enter and redirect users to questionable websites. The former function is quite dangerous because it could result in dangerous malware entering the computer.
Trojans like Win32/Ymacco can stay on an unprotected computer for a long time, operating in the background until it needs to download other malware. The malicious software it downloads can vary from keyloggers to ransomware. But whatever it downloads, it will cause damage. Password-stealing trojans can steal highly sensitive information, while ransomware can permanently encrypt personal files.
While Win32/Ymacco is present, users may also get redirected to highly questionable websites in order to drive traffic to those sites. These redirects can happen completely randomly as you’re browsing. This can get quite annoying but at least it would signal that something is wrong.
Users without an active anti-malware program on the device can notice some signs of the trojan being present. One of the most obvious signs of malware’s presence is high CPU usage by an unknown process. A process associated with Win32/Ymacco is Uwgcset.exe. If you open Task Manager and there’s an unfamiliar process (such as Uwgcset.exe) at the top, and it’s using a lot of your computer’s resources, it could be a malicious process. You may also notice your computer suddenly lagging and programs crashing. These are usually the signs of a potential malware infection. If you notice anything strange, it’s a good idea to download an anti-malware program and perform a scan of the computer.
How did Win32/Ymacco enter your computer?
Trojans like Win32/Ymacco are distributed in several ways, including torrents, malicious email attachments, ads, etc. Users who have good browsing habits are much less likely to pick up infections like trojans and ransomware because they do not engage in risky behavior like opening random email attachments. One of the best defenses against malware infections is developing good habits.
Malicious actors often use emails to spread malware. They attach malware to emails and claim that the attachment needs to be opened immediately because it’s an important document. To convince users to open the files containing malware, senders claim to be from known companies/organizations. It’s common for malicious senders to pretend to be from government agencies, parcel delivery services, etc., emailing with time-sensitive business. Creating a sense of urgency is a known tactic used by cybercriminals to influence users.
Emails carrying malware are usually quite obvious. First of all, they are full of grammar/spelling mistakes. Senders pretend to be from legitimate companies/organizations but when the emails are full of mistakes, it becomes immediately obvious that something is not right. Another thing that often gives away malicious emails is how they address you. Because malicious actors target many users at the same time, they use generic words like User, Member, Customer, etc., to address users instead of using their names. Legitimate senders whose services you use will always address you by name because it makes the email seem more personal.
To avoid serious infections, we strongly recommend always scanning all email attachments with anti-virus software or VirusTotal before opening them.
Malware is also regularly found in torrents, especially in torrents for entertainment content such as movies, TV series, and video games. Torrent sites are often poorly regulated, which allows malicious actors to upload torrents with malware in them.
How to remove Win32/Ymacco
Win32/Ymacco is a serious malware infection that should be removed using an anti-malware program. Trojans are very complex, and manual removal could cause even more issues unless you know what you’re doing.
If your anti-malware program is detecting it, allow it to remove Win32/Ymacco immediately. It’s also possible that because Win32/Ymacco is a dropper trojan, additional malware could be detected on your computer. Depending on what type of malware is detected, you may need to take additional action, such as changing your passwords.
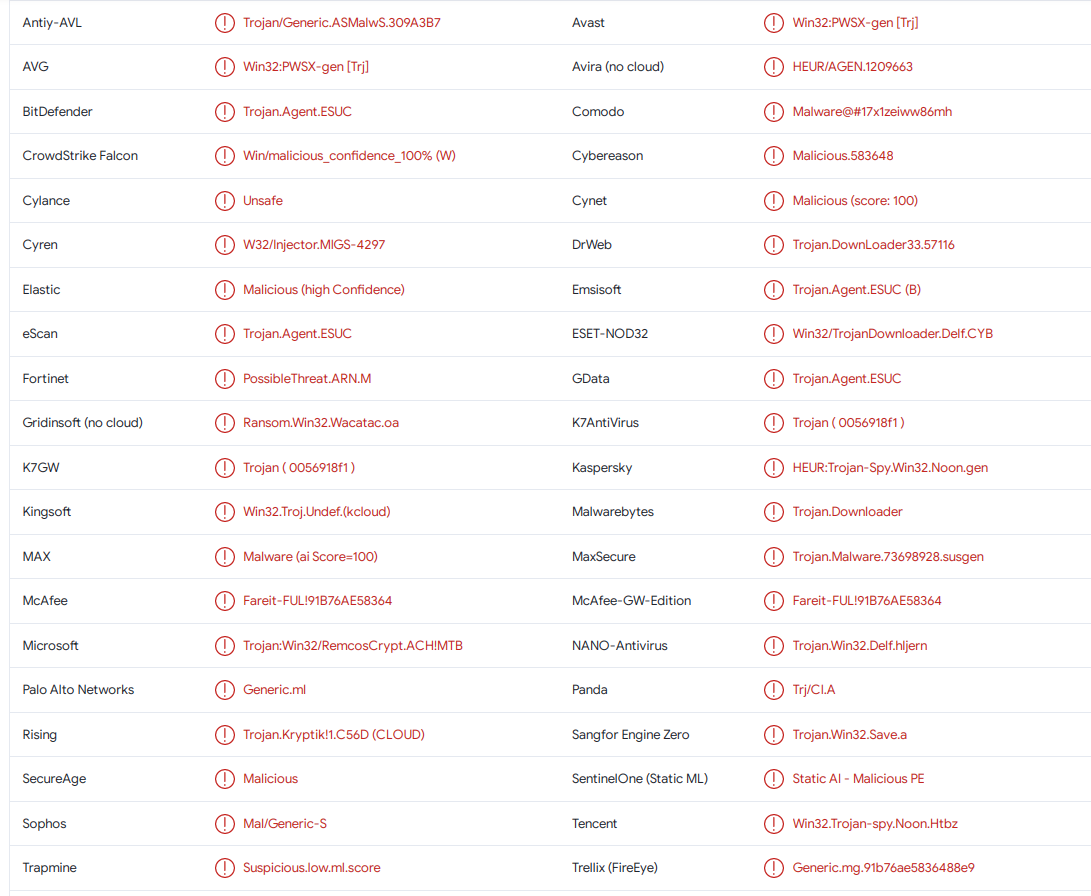
Win32/Ymacco is detected as:
- Win32:PWSX-gen [Trj] by AVG/Avast
- Trojan.Agent.ESUC by BitDefender
- Fareit-FUL!91B76AE58364 by McAfee
- Trojan:Win32/RemcosCrypt.ACH!MTB by Microsoft
- TROJ_GEN.R002C0DAM22 by TrendMicro
- Win32/TrojanDownloader.Delf.CYB by ESET
- HEUR:Trojan-Spy.Win32.Noon.gen by Kaspersky
- Trojan.Downloader by Malwarebytes
Offers
Download Removal Toolto scan for Win32/YmaccoUse our recommended removal tool to scan for Win32/Ymacco. Trial version of provides detection of computer threats like Win32/Ymacco and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.