What may be said about .Vpsh file extension
The ransomware known as .Vpsh file extension is classified as a serious threat, due to the possible damage it could cause. You You likely never encountered it before, and it could be particularly surprising to find out what it does. Ransomware can use powerful encryption algorithms for the encryption process, which stops you from accessing them any longer. Because data decryption isn’t possible in all cases, not to mention the time and effort it takes to get everything back in order, file encrypting malware is considered to be one of the most dangerous malicious program out there. 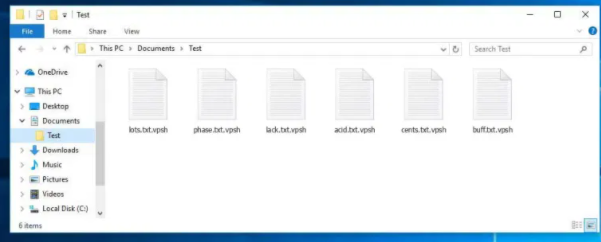
A decryptor will be offered to you by criminals but complying with the demands might not be the greatest idea. First of all, you might be just wasting your money because crooks don’t always recover files after payment. Do not expect cyber criminals to not just take your money and feel any obligation to assist you. In addition, by paying you’d be financing the projects (more ransomware and malware) of these cyber criminals. File encoding malicious program already costs $5 billion in loss to businesses in 2017, and that’s an estimation only. People are also becoming increasingly attracted to the business because the more victims pay the ransom, the more profitable it becomes. Consider investing that demanded money into backup instead because you could end up in a situation where you face file loss again. If backup was made before you got an infection, you can just fix .Vpsh file extension and proceed to unlock .Vpsh file extension files. And if you are unsure about how you managed to obtain the ransomware, its spread methods will be discussed further on in the report in the paragraph below.
.Vpsh file extension distribution methods
Email attachments, exploit kits and malicious downloads are the most frequent ransomware distribution methods. Because people are rather negligent when they open emails and download files, it’s usually not necessary for data encrypting malware spreaders to use more elaborate ways. Nevertheless, some ransomware can be distributed using more elaborate methods, which require more time and effort. Hackers do not have to do much, just write a simple email that less cautious people could fall for, add the contaminated file to the email and send it to hundreds of people, who might think the sender is someone legitimate. Those emails commonly mention money because that’s a delicate topic and users are more likely to be reckless when opening emails mentioning money. Hackers also prefer to pretend to be from Amazon, and warn possible victims that there has been some unusual activity in their account, which ought to immediately encourage a user to open the attachment. You need to look out for certain signs when dealing with emails if you want a clean device. It’s crucial that you check the sender to see whether they’re known to you and thus could be trusted. And if you do know them, double-check the email address to make sure it is actually them. Those malicious emails are also often full of grammar mistakes. Another typical characteristic is the lack of your name in the greeting, if a real company/sender were to email you, they would definitely know your name and use it instead of a general greeting, like Customer or Member. Weak spots on your device Out-of-date software may also be used to infect. A program comes with weak spots that can be exploited by data encrypting malicious software but they are regularly fixed by vendors. As has been shown by WannaCry, however, not everyone is that quick to install those updates for their programs. Because a lot of malicious software makes use of those weak spots it’s so critical that you regularly update your software. You can also make patches install automatically.
What does .Vpsh file extension do
Your data will be encrypted by ransomware as soon as it gets into your computer. Initially, it might not be obvious as to what is going on, but when you are unable to open your files, you’ll at least know something isn’t right. All encrypted files will have a weird file extension, which can help people find out the ransomware’s name. Your files could have been encoded using strong encryption algorithms, which might mean that you cannot decrypt them. A ransom note will explain what has happened to your files. The suggested a decryption tool will not come free, obviously. The note ought to display the price for a decryptor but if that isn’t the case, you’d have to use the provided email address to contact the criminals to find out how much the decryption software costs. Paying the ransom is not the suggested option for the reasons we have already mentioned above. Only consider that option as a last resort. It’s also somewhat probably that you’ve just forgotten that you have backed up your files. A free decryptor might also be an option. Malware researchers may sometimes release decryption programs for free, if the file encoding malicious software is crackable. Take that into consideration before you even think about giving into the requests. It would be a wiser idea to purchase backup with some of that money. If backup was created prior to infection, you can proceed to file recovery after you eliminate .Vpsh file extension virus. Now that you how how much damage this type of infection may cause, do your best to avoid it. Stick to legitimate download sources, pay attention to what type of email attachments you open, and make sure you keep your software updated at all times.
.Vpsh file extension removal
If the ransomware stays on your system, An anti-malware tool should be used to terminate it. It can be tricky to manually fix .Vpsh file extension virus because a mistake could lead to further harm. A malware removal program would be a smarter choice in this case. The software would not only help you deal with the threat, but it may also stop similar ones from getting in in the future. Find which anti-malware utility best suits what you require, install it and scan your device in order to identify the threat. Bear in mind that a malware removal utility is meant to get rid of the threat and not to help recover files. If the ransomware has been terminated completely, recover files from backup, and if you do not have it, start using it.
Offers
Download Removal Toolto scan for .Vpsh file extensionUse our recommended removal tool to scan for .Vpsh file extension. Trial version of provides detection of computer threats like .Vpsh file extension and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete .Vpsh file extension using Safe Mode with Networking.
Remove .Vpsh file extension from Windows 7/Windows Vista/Windows XP
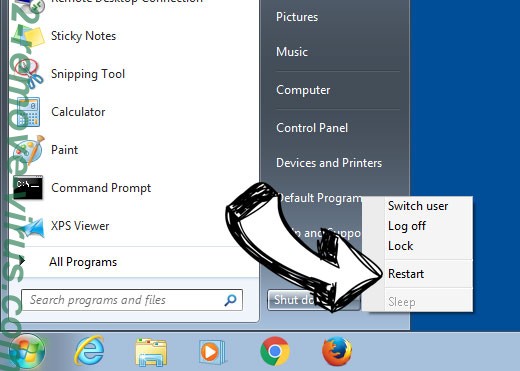
- Click on Start and select Shutdown.
- Choose Restart and click OK.

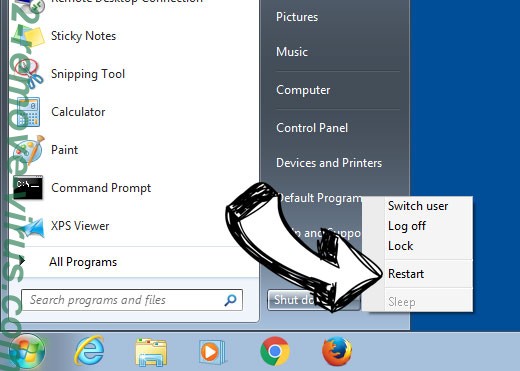
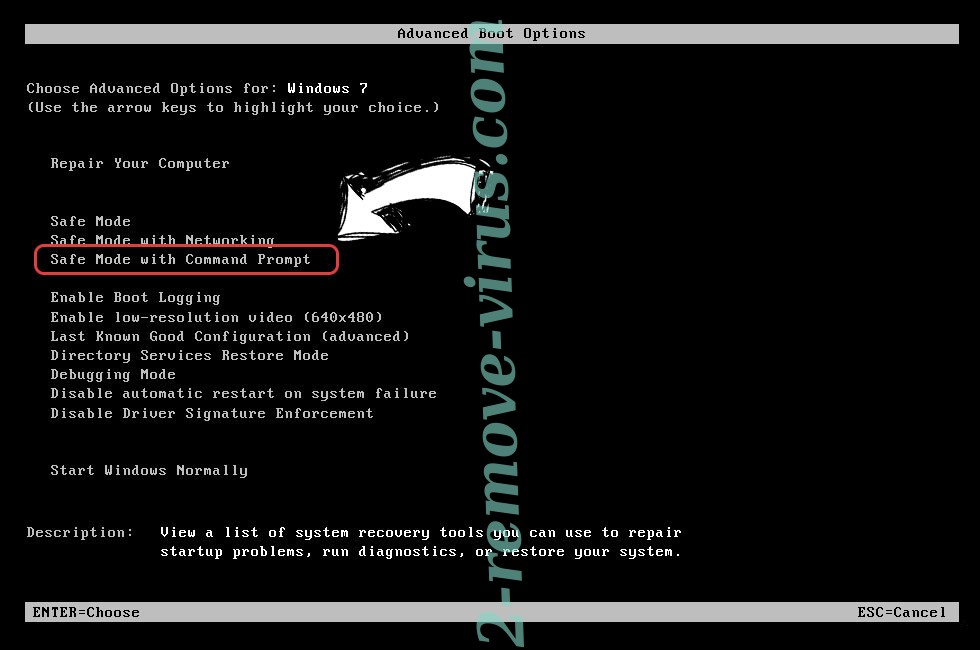
- Start tapping F8 when your PC starts loading.
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove .Vpsh file extension
Remove .Vpsh file extension from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.


- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

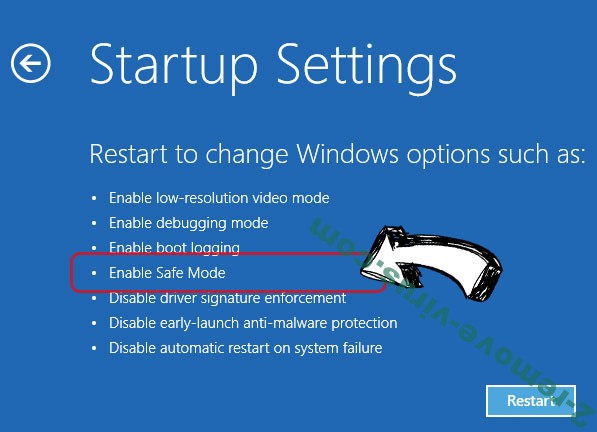
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete .Vpsh file extension
Step 2. Restore Your Files using System Restore
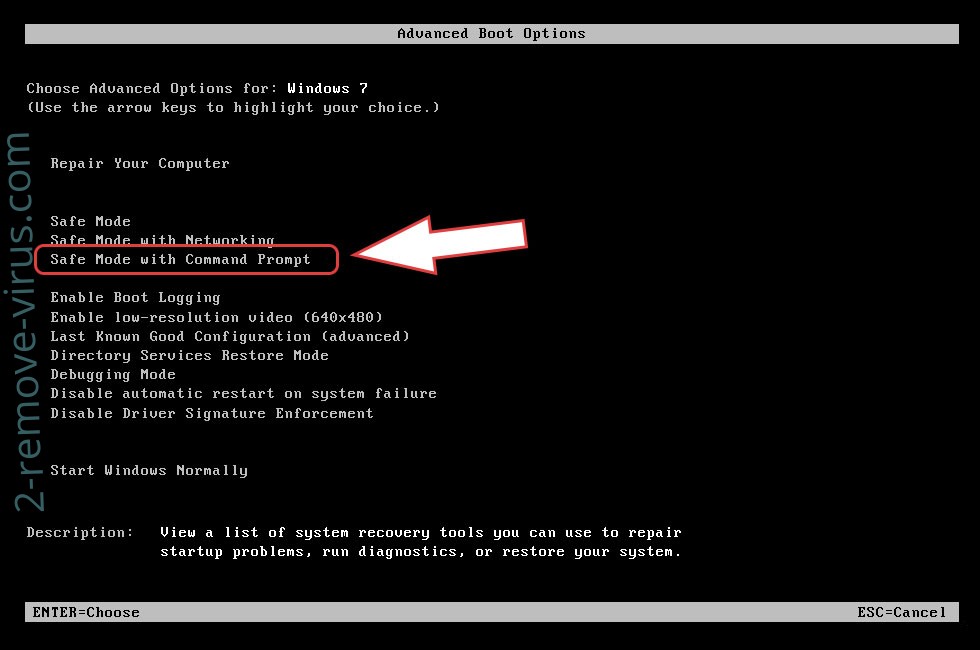
Delete .Vpsh file extension from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

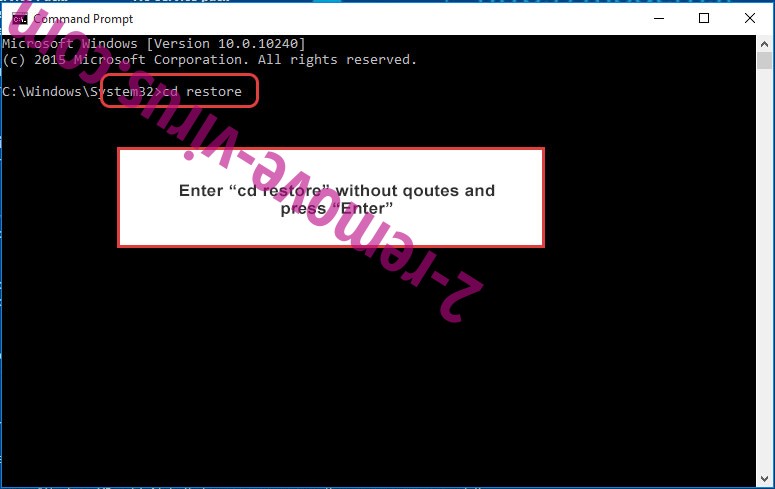
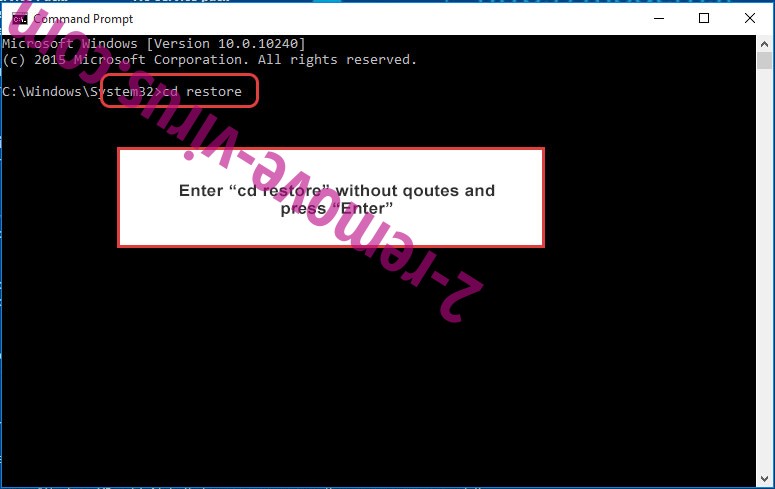
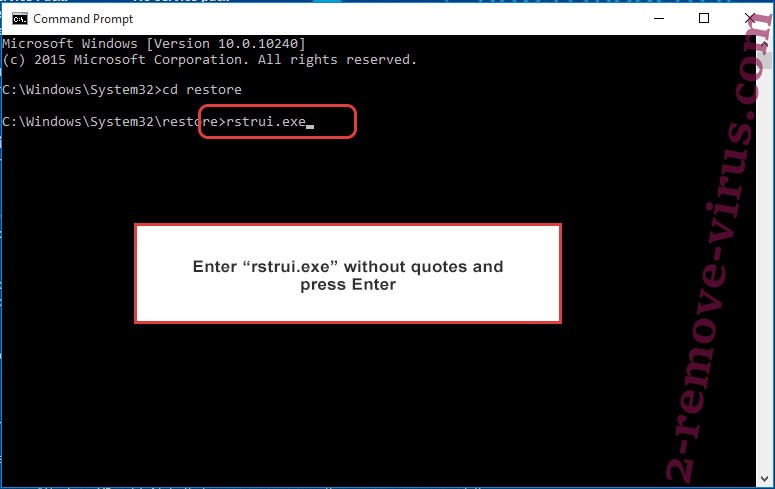
- Type in cd restore and tap Enter.

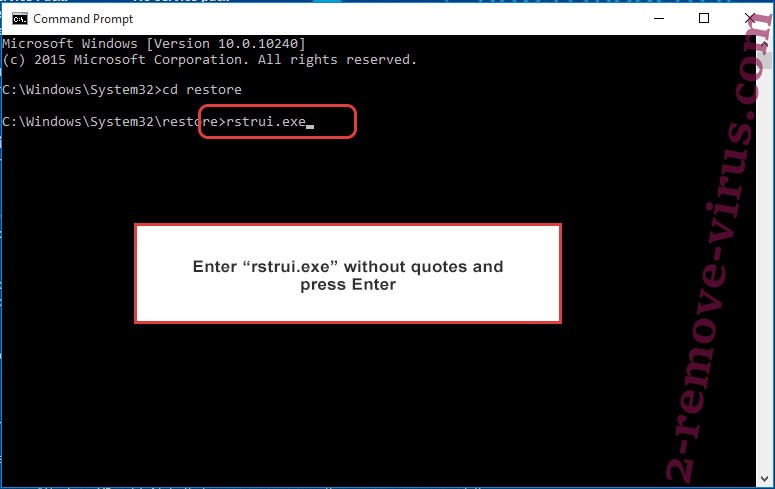
- Type in rstrui.exe and press Enter.

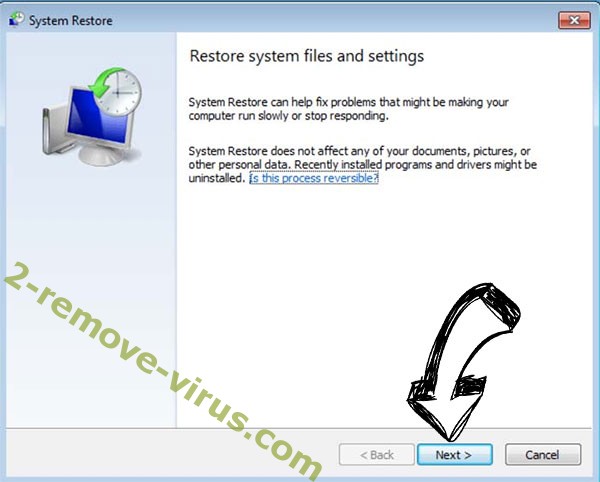
- Click Next in the new window and select the restore point prior to the infection.

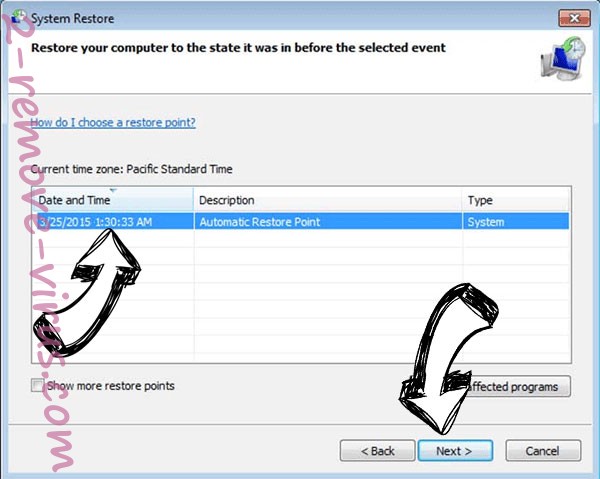
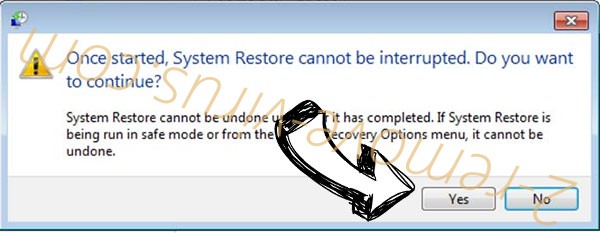
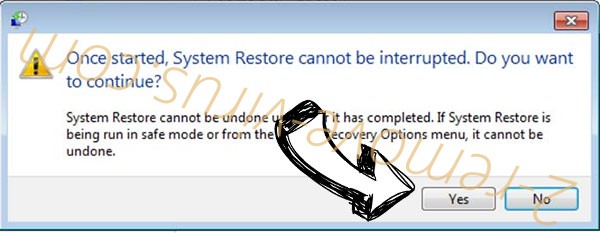
- Click Next again and click Yes to begin the system restore.

Delete .Vpsh file extension from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.


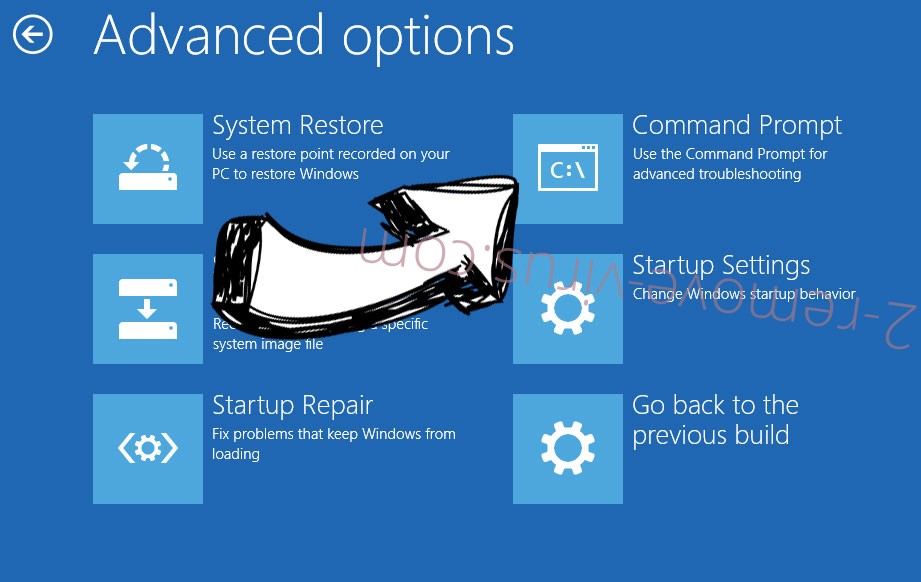
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

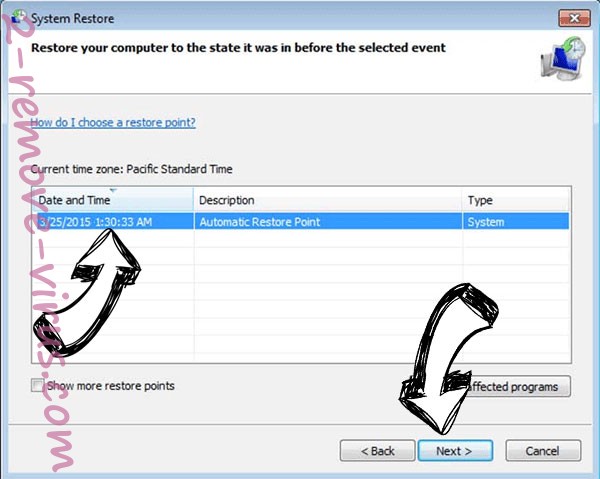
- Click Next and then click Yes to restore your system.

Incoming search terms:
Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
