eshield.online is a browser hijacker targeting Mac computers
eshield.online browser hijacker is also known as a redirect virus, and mainly targets Mac devices. It should not be directly harmful, so the hijacker is not a severe infection. It’s not harmless, however, as it aims to generate traffic and profit and it’ll do that by redirecting you to suspicious pages. While hijackers use sly methods to install, they become very obvious soon after. You’ll notice your browser behaving in a strange way, search results will be a mixture of sponsored content and authentic results and you’ll be randomly redirected. However, since not everyone knows what specifically is a browser hijacker, they might not associate the bizarre behaviour with an infection. Just researching the symptoms/page redirected to with a search engine normally points users in the right direction.
You will notice changes made to your browser’s settings, in addition to the odd redirects. Your browser’s homepage and new tabs will be changed, and the hijacker will stop you from making any changes yourself. It is because they perform those changes that hijackers are able to redirect you.
We ought to say that hijackers can’t install by themselves as they are neither malware nor viruses. While users normally don’t notice this, but they install the hijackers themselves. The bundling method is usually used by pests like hijackers to install, meaning they’re added to free programs as added items and can install together with it. The next section of the article will explain how you could prevent these unnecessary installations.
While it might be a rather trivial infection, quick eshield.online uninstallation from your Mac is a good idea. In addition to you not being able to browse as normal, the hijacker will likely expose you to malicious programs, scams and other content that’s harmful to your computer.
How are hijackers spread
Browser hijackers install together with freeware, as we have mentioned above. This is called software bundling, and in simple terms it is attaching additional offers such as hijackers to known freeware. The dubious thing about this method is that the added offers are set to install with the free software but are hidden from users. You should not have any trouble with preventing these items from installing as long as you pay attention to how you install free software.
During free software installation, opting for Advanced (Custom) settings is important. The extra items won’t be made visible if you choose Default settings. Every item will be made visible in Advanced, and you shouldn’t have any trouble deselecting it. All you need to do is uncheck those boxes. Take into consideration that blocking installations takes much less time in comparison to removing infections that have been installed already. You will block many rubbish software from installing as long as you pay attention to how you install programs.
What does the hijacker do
You will see symptoms of a browser hijacker infection rather quickly as your Safari, Google Chrome or Mozilla Firefox browser will be hijacked, and you’ll be redirected. As soon as your browser is launched, you you will immediately be redirected to the hijacker’s promoted website since it has been set as your homepage. Not only your homepage, but modifications to your search engine will also be made. You will be redirected to a web page promoted by the hijacker and then displayed search results that have been altered whenever you carry out a search via the browser address bar. You may note that the results contain sponsored content that has little to do with what you searched for. In order to generate traffic and revenue, hijackers redirect users to those sponsored web pages. The weird redirects make hijackers possibly dangerous as well as irritating infections. Thus, do not engage with any sponsored content or advertisements until the hijacker is gone. You may be redirected to sponsored pages that might not necessarily be safe because hijackers don’t review whether they are secure. You may be led to a web page hosting malware, or one that’s trying to scam you. So even if hijackers are not directly harmful to the device, don’t keep them installed.
It should also be noted that browser hijackers have a tendency to spy on users, and gather various information related their searches, visited web pages, IP address and more. Hijackers rather commonly share that data with unknown third-parties, who use it for their own purposes.
To summarize, the hijacker did not ask for your explicit permission to install, made undesirable modifications to your browsers, started leading you to sponsored pages for revenue, and potentially subjected you to unreliable content. The sooner you remove eshield.online, the better.
eshield.online elimination
Using anti-spyware software for eshield.online deletion is what we advise. The anti-spyware program will guarantee successful threat elimination. Manual eshield.online elimination is not too hard either, if you understand how and make sure to remove all hijacker files. You’ll be able to restore your browser’s settings with no issues after you remove eshield.online.
Offers
Download Removal Toolto scan for eshield.onlineUse our recommended removal tool to scan for eshield.online. Trial version of provides detection of computer threats like eshield.online and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Uninstall eshield.online and related programs.
Remove eshield.online from Windows 8
Right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel choose Programs and Features and select to Uninstall a software.


Uninstall eshield.online from Windows 7
Click Start → Control Panel → Programs and Features → Uninstall a program.


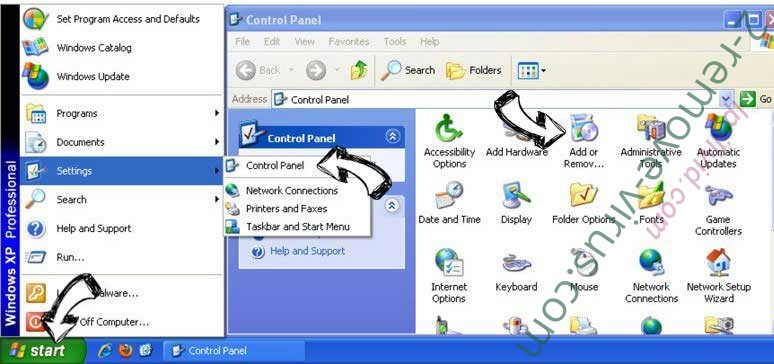
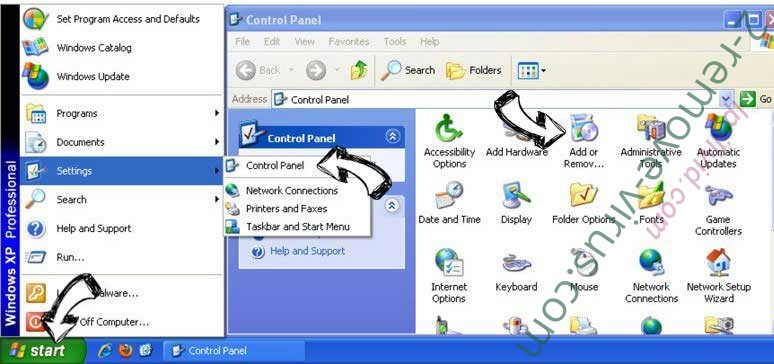
Delete eshield.online from Windows XP
Click Start → Settings → Control Panel. Locate and click → Add or Remove Programs.
Remove eshield.online from Mac OS X
Click Go button at the top left of the screen and select Applications. Select applications folder and look for eshield.online or any other suspicious software. Now right click on every of such entries and select Move to Trash, then right click the Trash icon and select Empty Trash.


Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
