About Telecrypt ransomware
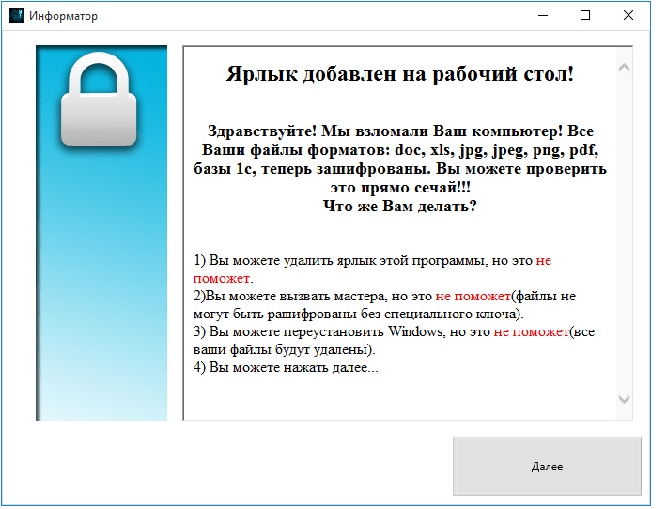
Telecrypt ransomware is yet another ransomware to add to the already big list of malicious viruses. If you infect your computer with it, it will encrypt your files and then demand that you pay to get them back. Researchers think that Telecrypt ransomware could be targeting Russian users as the ransom note it in Russian.
You could infect your computer if you open malicious email attachments, download fake software updates or use peer-to-peer networks (Torrents). Once it’s on your computer, it will use complex encryption algorithms to encrypt your files. You will be then asked to pay 5000 Rubles ($76) and they will supposedly send you a decryption key. Supposedly being the key word. We feel obligated to warn you that even if you pay, file restoration is not guaranteed. Many ransomware developers just take your money and give nothing back. Think carefully before you attempt to pay. Instead, we suggest you remove Telecrypt ransomware as soon as possible.
Why is Telecrypt ransomware so dangerous?
There are many ways in which Telecrypt ransomware could have reached your computer. The most probable one being spam email. If you get an email from an unknown sender that claims to be from a government organization or a company, and it puts pressure on you to open the file attachment, do not do so. Always double check the sender and the contents to ensure that what you are about to open is 100% safe. You might also encounter pop-ups that claim you need to update your software. Never download anything from these kinds of pop-ups. Only trust legitimate websites with downloads. And if you must use Torrents, at least make sure that what you are downloading does not contain ransomware.
When it downloads onto your computer, it will start file encryption. The interesting thing about Telecrypt ransomware is that it needs Internet to complete the process. It seems that Telecrypt ransomware can only encrypt .DOC; .DOCX; .XLS; .XLSX; .JPG; .JPEG; .PNG; .DT; .DBF; .CD; .PDF types of files. When the encryption process is complete, it might add the. Xcri file extension, or add nothing, depending on the version. In any case, Telecrypt ransomware will then generate a ransom note, explaining what has happened. The note is in Russian and explains that you need to pay the hackers $76 via Yandex.Money or Qiwi payment services to get a decryption key. This is rather unusual as most ransomware asks that you pay in Bitcoins to ensure anonymity. Even if it does not seem like a big amount of money, we don’t suggest paying. You might not get the decryption key and end up just supporting the future projects of the developers. Delete Telecrypt ransomware without mercy.
Telecrypt ransomware removal
You will need to purchase anti-malware software to remove Telecrypt ransomware from your computer. Manual Telecrypt ransomware removal is too complex for inexperienced users so we cannot recommend it. In order to delete Telecrypt ransomware, follow the instructions below.
Offers
Download Removal Toolto scan for Telecrypt ransomwareUse our recommended removal tool to scan for Telecrypt ransomware. Trial version of provides detection of computer threats like Telecrypt ransomware and assists in its removal for FREE. You can delete detected registry entries, files and processes yourself or purchase a full version.
More information about SpyWarrior and Uninstall Instructions. Please review SpyWarrior EULA and Privacy Policy. SpyWarrior scanner is free. If it detects a malware, purchase its full version to remove it.

WiperSoft Review Details WiperSoft (www.wipersoft.com) is a security tool that provides real-time security from potential threats. Nowadays, many users tend to download free software from the Intern ...
Download|more


Is MacKeeper a virus? MacKeeper is not a virus, nor is it a scam. While there are various opinions about the program on the Internet, a lot of the people who so notoriously hate the program have neve ...
Download|more


While the creators of MalwareBytes anti-malware have not been in this business for long time, they make up for it with their enthusiastic approach. Statistic from such websites like CNET shows that th ...
Download|more
Quick Menu
Step 1. Delete Telecrypt ransomware using Safe Mode with Networking.
Remove Telecrypt ransomware from Windows 7/Windows Vista/Windows XP
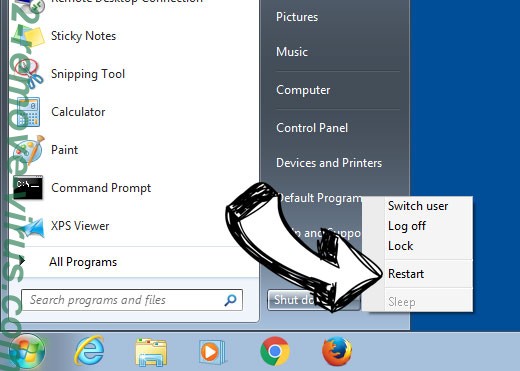
- Click on Start and select Shutdown.
- Choose Restart and click OK.

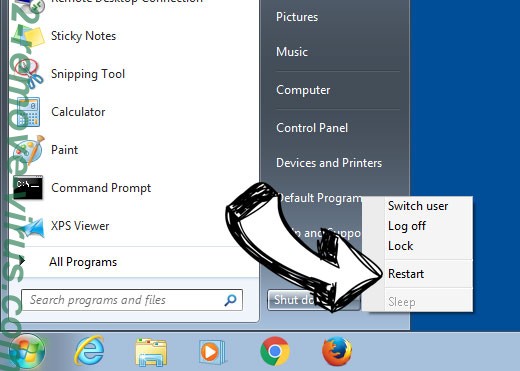
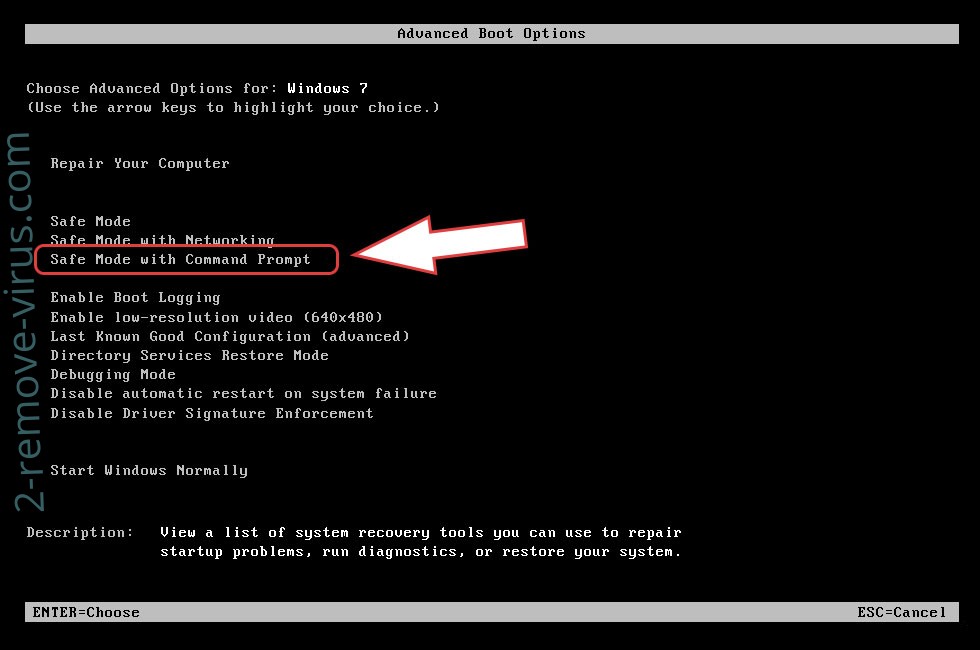
- Start tapping F8 when your PC starts loading.
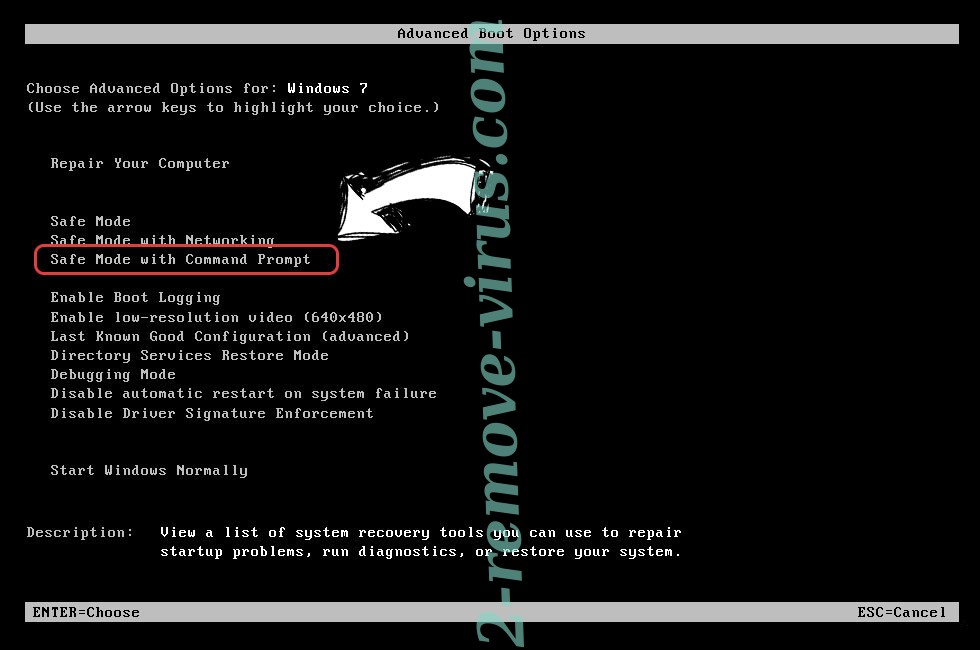
- Under Advanced Boot Options, choose Safe Mode with Networking.

- Open your browser and download the anti-malware utility.
- Use the utility to remove Telecrypt ransomware
Remove Telecrypt ransomware from Windows 8/Windows 10
- On the Windows login screen, press the Power button.
- Tap and hold Shift and select Restart.


- Go to Troubleshoot → Advanced options → Start Settings.
- Choose Enable Safe Mode or Safe Mode with Networking under Startup Settings.

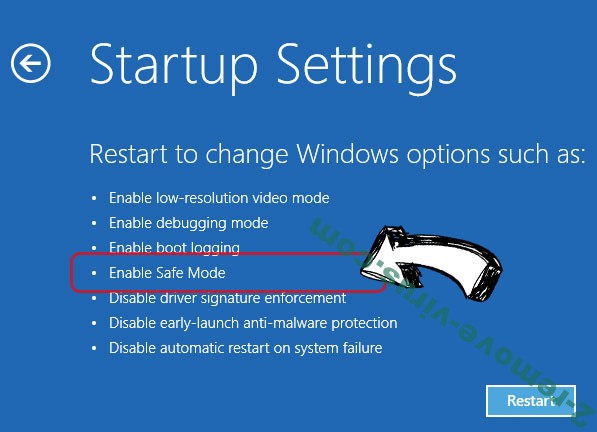
- Click Restart.
- Open your web browser and download the malware remover.
- Use the software to delete Telecrypt ransomware
Step 2. Restore Your Files using System Restore
Delete Telecrypt ransomware from Windows 7/Windows Vista/Windows XP
- Click Start and choose Shutdown.
- Select Restart and OK

- When your PC starts loading, press F8 repeatedly to open Advanced Boot Options
- Choose Command Prompt from the list.

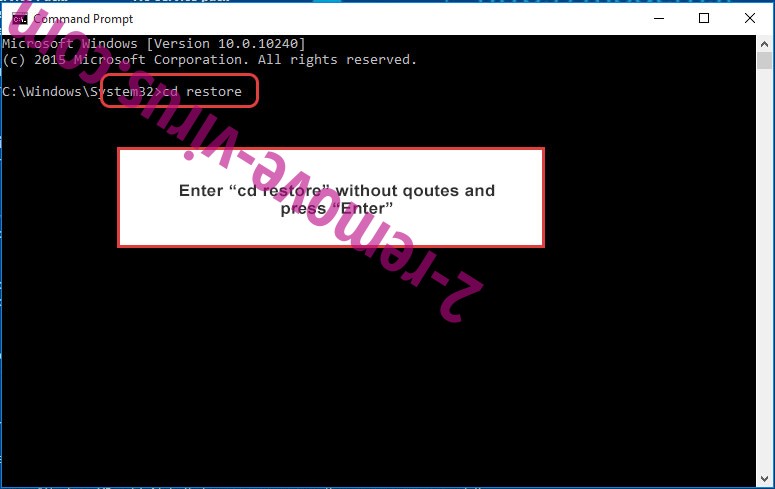
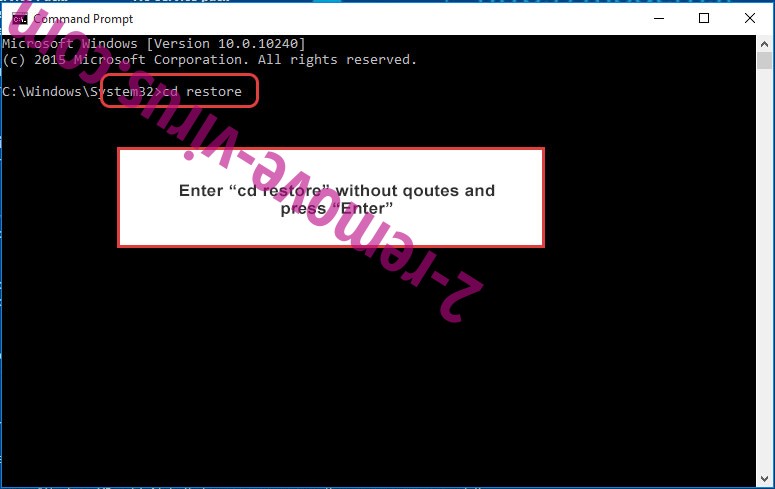
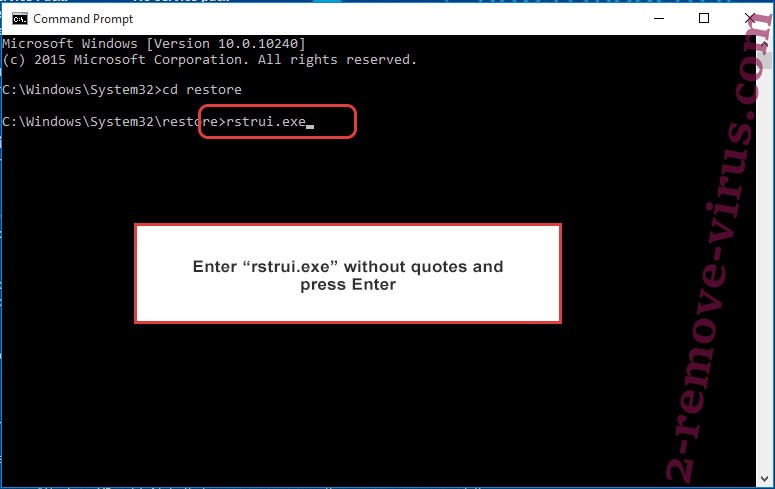
- Type in cd restore and tap Enter.

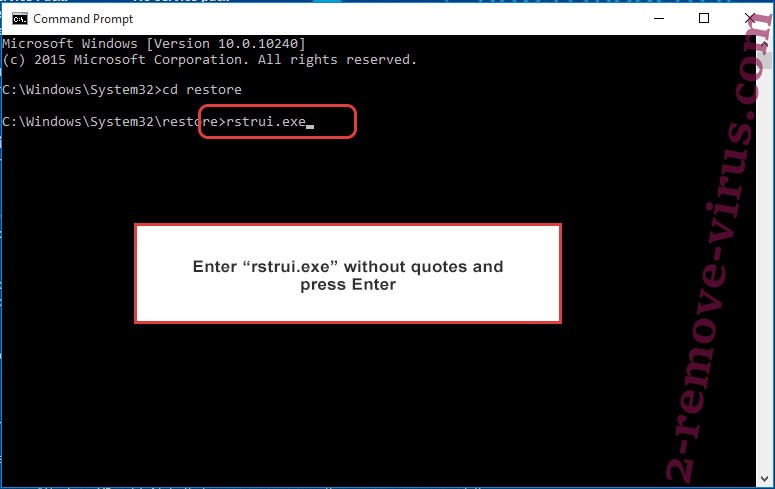
- Type in rstrui.exe and press Enter.

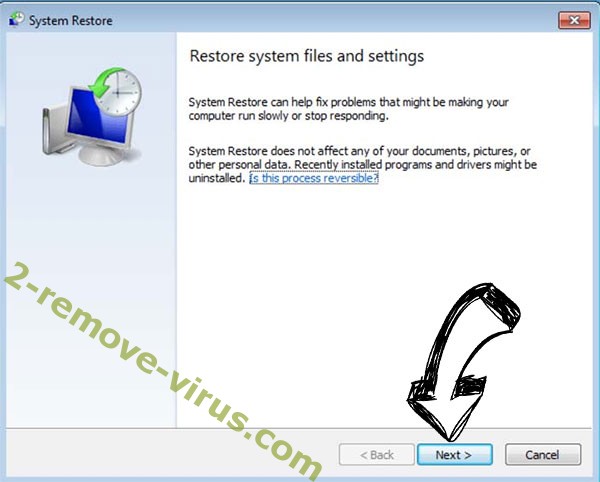
- Click Next in the new window and select the restore point prior to the infection.

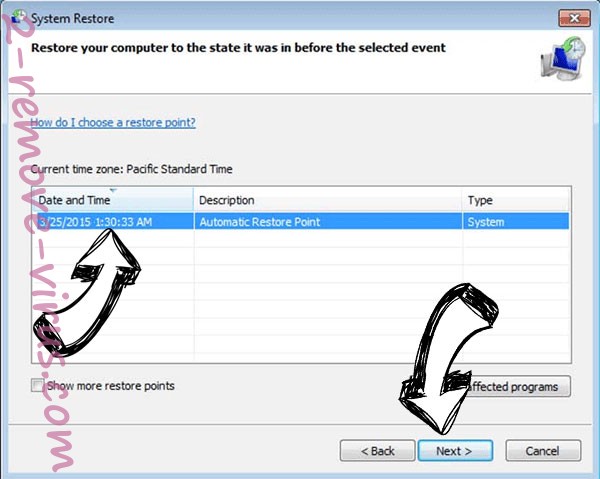
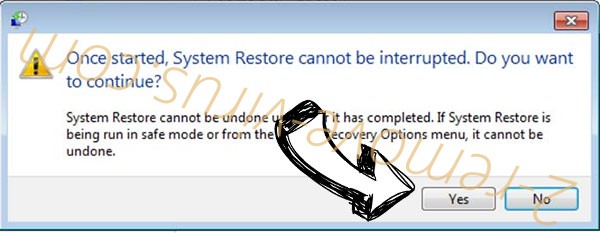
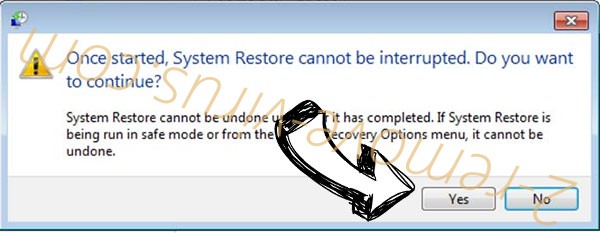
- Click Next again and click Yes to begin the system restore.

Delete Telecrypt ransomware from Windows 8/Windows 10
- Click the Power button on the Windows login screen.
- Press and hold Shift and click Restart.


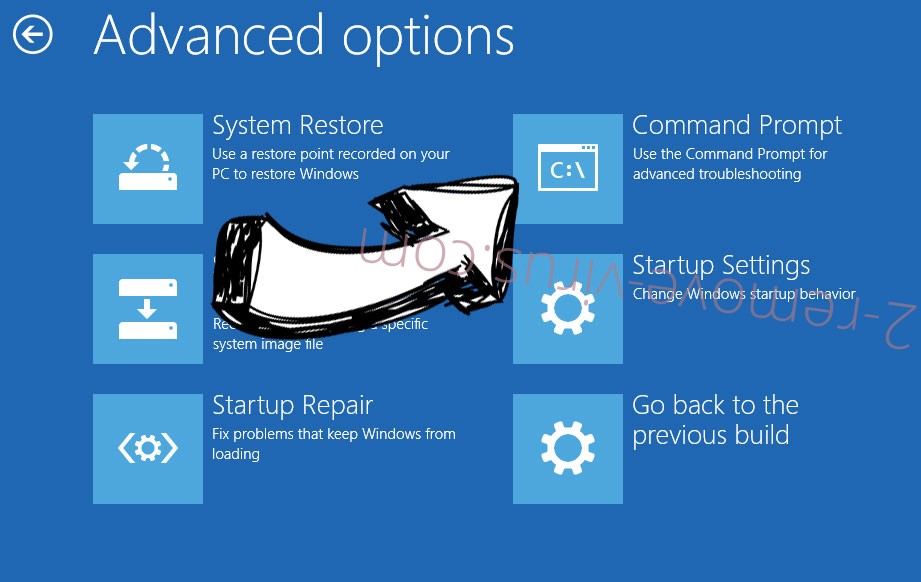
- Choose Troubleshoot and go to Advanced options.
- Select Command Prompt and click Restart.

- In Command Prompt, input cd restore and tap Enter.

- Type in rstrui.exe and tap Enter again.

- Click Next in the new System Restore window.

- Choose the restore point prior to the infection.

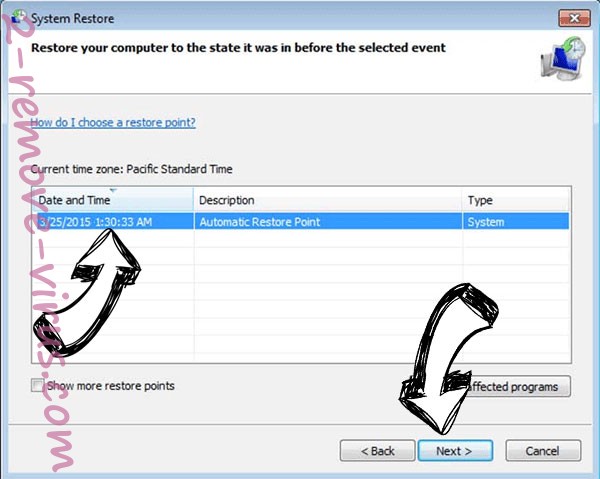
- Click Next and then click Yes to restore your system.

Site Disclaimer
2-remove-virus.com is not sponsored, owned, affiliated, or linked to malware developers or distributors that are referenced in this article. The article does not promote or endorse any type of malware. We aim at providing useful information that will help computer users to detect and eliminate the unwanted malicious programs from their computers. This can be done manually by following the instructions presented in the article or automatically by implementing the suggested anti-malware tools.
The article is only meant to be used for educational purposes. If you follow the instructions given in the article, you agree to be contracted by the disclaimer. We do not guarantee that the artcile will present you with a solution that removes the malign threats completely. Malware changes constantly, which is why, in some cases, it may be difficult to clean the computer fully by using only the manual removal instructions.
